Powerpoint Templates and Google slides for Security Process
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Security of iot operations powerpoint slide rules
Security of iot operations powerpoint slide rulesPresenting security of iot operations powerpoint slide rules. This is a security of iot operations powerpoint slide rules. This is a one stage process. The stages in this process are security program, security configuration management, vulnerability scanning, application scanning, threat management, cloud assessment, authentication and privacy.
-
 Billing customer security e source control circular process with icon in centre
Billing customer security e source control circular process with icon in centrePresenting billing customer security e source control circular process with icon in centre. This is a billing customer security e source control circular process with icon in centre. This is a seven stage process. The stages in this process are billing process, billing procedure, billing cycle.
-
 Operating system memory process management security
Operating system memory process management securityPresenting this Operating System Memory Process Management Security PowerPoint presentation. Add charts and graphs for a wonderful representation of information. The PPT also supports the standard (4:3) and widescreen (16:9) aspect ratios. It is compatible with Google Slides. Convert this into popular images or document formats such as JPEG, PNG or PDF. High-quality graphics ensure that graphics quality is maintained at every stage of presentation.
-
 Hotel safety and security emergency process with 5 boxes
Hotel safety and security emergency process with 5 boxesPresenting hotel safety and security emergency process with 5 boxes. This is a hotel safety and security emergency process with 5 boxes. This is a five stage process. The stages in this process are hotel safety and security, guest house safety, lodge safety.
-
 Hotel safety and security procedures with converging arrows and boxes
Hotel safety and security procedures with converging arrows and boxesPresenting hotel safety and security procedures with converging arrows and boxes. This is a hotel safety and security procedures with converging arrows and boxes. This is a six stage process. The stages in this process are hotel safety and security, guest house safety, lodge safety.
-
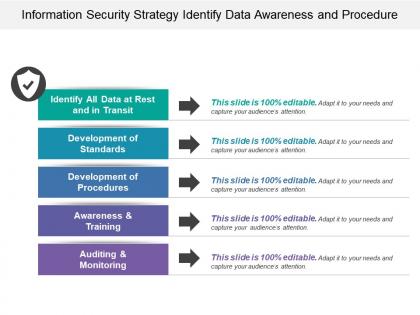 Information security strategy identify data awareness and procedure
Information security strategy identify data awareness and procedurePresenting this set of slides with name - Information Security Strategy Identify Data Awareness And Procedure. This is a five stage process. The stages in this process are Information Security Strategy, Information Security Plan, Information Protection Strategy.
-
 Business process automation standardise security collaboration consistency
Business process automation standardise security collaboration consistencyPresenting this set of slides with name - Business Process Automation Standardise Security Collaboration Consistency. This is a eight stage process. The stages in this process are Business Process Automation, Robotic Process Automation, Software Development.
-
 Infrastructure management defining application security and process
Infrastructure management defining application security and processPresenting this set of slides with name - Infrastructure Management Defining Application Security And Process. This is a seven stage process. The stages in this process are Infrastructure Management, Operation Management, Network Management.
-
 Skill matrix table identifying technical security and transaction processing
Skill matrix table identifying technical security and transaction processingPresenting this set of slides with name - Skill Matrix Table Identifying Technical Security And Transaction Processing. This is a three stage process. The stages in this process are Skill Matrix, Skill Mapping, Intelligence.
-
 Cloud governance define roles security policies and processes
Cloud governance define roles security policies and processesPresenting this set of slides with name - Cloud Governance Define Roles Security Policies And Processes. This is a five stage process. The stages in this process are Cloud Governance, Cloud Computing, Cloud Management.
-
 Pick pack inventory management reporting secure payment processing
Pick pack inventory management reporting secure payment processingPresenting this set of slides with name - Pick Pack Inventory Management Reporting Secure Payment Processing. This is an editable four stages graphic that deals with topics like Pick Pack, Inventory Management Reporting, Secure Payment Processing to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Major internet security technologies internet protocol stack stateful inspection
Major internet security technologies internet protocol stack stateful inspectionPresenting this set of slides with name - Major Internet Security Technologies Internet Protocol Stack Stateful Inspection. This is an editable four graphic that deals with topics like Major Internet Security Technologies, Internet Protocol Stack, Stateful Inspection to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security management integration directory process composer lifecycle management
Security management integration directory process composer lifecycle managementPresenting this set of slides with name - Security Management Integration Directory Process Composer Lifecycle Management. This is an editable three stages graphic that deals with topics like Security Management, Integration Directory, Process Composer, Lifecycle Management to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Management experience process control advanced training privacy security
Management experience process control advanced training privacy securityPresenting this set of slides with name - Management Experience Process Control Advanced Training Privacy Security. This is an editable four graphic that deals with topics like Management Experience, Process Control, Advanced Training, Privacy Security to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Insurance claim process cashless intimate submit documents security pay
Insurance claim process cashless intimate submit documents security payPresenting this set of slides with name - Insurance Claim Process Cashless Intimate Submit Documents Security Pay. This is a five stage process. The stages in this process are Insurance Claim Process, Insurance Claim Steps, Insurance Claim Procedure.
-
 Insurance claim process intimate submit document security pay
Insurance claim process intimate submit document security payPresenting this set of slides with name - Insurance Claim Process Intimate Submit Document Security Pay. This is a four stage process. The stages in this process are Insurance Claim Process, Insurance Claim Steps, Insurance Claim Procedure.
-
 Insurance claim process intimate submit documents security pay
Insurance claim process intimate submit documents security payPresenting this set of slides with name - Insurance Claim Process Intimate Submit Documents Security Pay. This is a four stage process. The stages in this process are Insurance Claim Process, Insurance Claim Steps, Insurance Claim Procedure.
-
 Secure application information visibility brand building process policy
Secure application information visibility brand building process policyPresenting this set of slides with name - Secure Application Information Visibility Brand Building Process Policy. This is an editable two stages graphic that deals with topics like Secure Application Information, Visibility Brand Building, Process Policy to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Process integration oversight security policy management corporate strategic plan
Process integration oversight security policy management corporate strategic planPresenting this set of slides with name - Process Integration Oversight Security Policy Management Corporate Strategic Plan. This is an editable three stages graphic that deals with topics like Process Integration Oversight, Security Policy Management, Corporate Strategic Plan to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Release roadmap swimlane include flow of process such as environment setup and security improvements
Release roadmap swimlane include flow of process such as environment setup and security improvementsPresenting this set of slides with name - Release Roadmap Swimlane Include Flow Of Process Such As Environment Setup And Security Improvements. This is a three stage process. The stages in this process are Release Swimlane, Launch Swimlane, Deliver Swimlane.
-
 Operational process operational planning maintaining supplying securing building
Operational process operational planning maintaining supplying securing buildingPresenting this set of slides with name - Operational Process Operational Planning Maintaining Supplying Securing Building. This is a five stage process. The stages in this process are Operational Planning, Maintaining, Supplying, Securing, Building.
-
 Intelligent process automation framework icons slide security ppt powerpoint presentation file
Intelligent process automation framework icons slide security ppt powerpoint presentation filePresenting this set of slides with name Intelligent Process Automation Framework Icons Slide Security Ppt Powerpoint Presentation File. The topics discussed in these slides are Technology, Communication, Knowledge, Planning, Marketing. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Intelligent process automation framework security a136 ppt powerpoint presentation layouts
Intelligent process automation framework security a136 ppt powerpoint presentation layoutsPresenting this set of slides with name Intelligent Process Automation Framework Security A136 Ppt Powerpoint Presentation Layouts. This is a five stage process. The stages in this process are Technology, Cognitive Agents, Planning, Strategy, Marketing. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Latest cyber security technology ppt powerpoint presentation gallery rules cpb
Latest cyber security technology ppt powerpoint presentation gallery rules cpbPresenting this set of slides with name Latest Cyber Security Technology Ppt Powerpoint Presentation Gallery Rules Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Latest Cyber Security Technology to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 External network security ppt powerpoint presentation slides rules cpb
External network security ppt powerpoint presentation slides rules cpbPresenting this set of slides with name External Network Security Ppt Powerpoint Presentation Slides Rules Cpb. This is an editable Powerpoint four stages graphic that deals with topics like External Network Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Investment process security analysis ppt powerpoint presentation icon background images cpb
Investment process security analysis ppt powerpoint presentation icon background images cpbPresenting this set of slides with name Investment Process Security Analysis Ppt Powerpoint Presentation Icon Background Images Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Investment Process Security Analysis to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Physical security management protocol ppt powerpoint presentation infographic cpb
Physical security management protocol ppt powerpoint presentation infographic cpbPresenting this set of slides with name Physical Security Management Protocol Ppt Powerpoint Presentation Infographic Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Physical Security Management Protocol to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Encryption security ppt powerpoint presentation icon rules cpb
Encryption security ppt powerpoint presentation icon rules cpbPresenting this set of slides with name Encryption Security Ppt Powerpoint Presentation Icon Rules Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Encryption Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information security risk assessment process ppt powerpoint presentation shapes cpb
Information security risk assessment process ppt powerpoint presentation shapes cpbPresenting this set of slides with name Information Security Risk Assessment Process Ppt Powerpoint Presentation Shapes Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Information Security Risk Assessment Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Network security fundamentals ppt powerpoint presentation show rules cpb
Network security fundamentals ppt powerpoint presentation show rules cpbPresenting this set of slides with name Network Security Fundamentals Ppt Powerpoint Presentation Show Rules Cpb. This is an editable Powerpoint seven stages graphic that deals with topics like Network Security Fundamentals to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security essentials ppt powerpoint presentation model rules cpb
Cyber security essentials ppt powerpoint presentation model rules cpbPresenting this set of slides with name Cyber Security Essentials Ppt Powerpoint Presentation Model Rules Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Cyber Security Essentials to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security log management process ppt powerpoint presentation professional graphics cpb
Security log management process ppt powerpoint presentation professional graphics cpbPresenting this set of slides with name Security Log Management Process Ppt Powerpoint Presentation Professional Graphics Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Security Log Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Standard security management process ppt powerpoint presentation pictures graphic images cpb
Standard security management process ppt powerpoint presentation pictures graphic images cpbPresenting this set of slides with name Standard Security Management Process Ppt Powerpoint Presentation Pictures Graphic Images Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Standard Security Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Process of security risk assessment and audit
Process of security risk assessment and auditPresenting this set of slides with name Process Of Security Risk Assessment And Audit. The topics discussed in these slides are Process Security, Risk Assessment, Audit. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Five yearly roadmap for securing business process management
Five yearly roadmap for securing business process managementPresenting our Five Yearly Roadmap For Securing Business Process Management PowerPoint Presentation Slide. This is a 100% editable and adaptable PPT slide. This layout allows you to modify the font, text, and image according to your unique requirements. The template can also be accessed with Google Slides. You can save it in different formats such as PDF or JPEG. High-quality graphics add to its benefits.
-
 Half yearly roadmap for securing business process management
Half yearly roadmap for securing business process managementPresenting Half Yearly Roadmap For Securing Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Quarterly roadmap for securing business process management
Quarterly roadmap for securing business process managementPresenting Quarterly Roadmap For Securing Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4:3 and 16:9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG
-
 Six months roadmap for securing business process management
Six months roadmap for securing business process managementPresenting Six Months Roadmap For Securing Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Three months roadmap for securing business process management
Three months roadmap for securing business process managementPresenting our Three Months Roadmap For Securing Business Process Management PowerPoint Presentation Slide. It is completely editable and adaptable according to requirements. Take advantage of this professionally created PPT design that allows you to add or edit any text, image, and graph to your presentation making it more attractive and educational. It can also be presented with a different color, font, font size, and font types. The entire shape and appearance of the objects can be changed in this PPT layout. This template also supports standard (4:3) and widescreen (16:9) format. It presents you with thousands of icons for your topic to choose from. This template is also compatible with Google Slides.
-
 Computer security trends information security ppt powerpoint presentation icon rules cpb
Computer security trends information security ppt powerpoint presentation icon rules cpbPresenting this set of slides with name Computer Security Trends Information Security Ppt Powerpoint Presentation Icon Rules Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Computer Security Trends Information Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information security management process ppt powerpoint presentation model cpb
Information security management process ppt powerpoint presentation model cpbPresenting this set of slides with name Information Security Management Process Ppt Powerpoint Presentation Model Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Information Security Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security audit procedures ppt powerpoint presentation infographics slides cpb
Cyber security audit procedures ppt powerpoint presentation infographics slides cpbPresenting this set of slides with name Cyber Security Audit Procedures Ppt Powerpoint Presentation Infographics Slides Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Cyber Security Audit Procedures to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security people process technology ppt powerpoint presentation file graphics template cpb
Cyber security people process technology ppt powerpoint presentation file graphics template cpbPresenting this set of slides with name Cyber Security People Process Technology Ppt Powerpoint Presentation File Graphics Template Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Cyber Security People Process Technology to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security people process technology framework
Cyber security people process technology frameworkPresenting this set of slides with name Cyber Security People Process Technology Framework. This is a six stage process. The stages in this process are Information Risk Management, Incident Response And Forensic Investigation, Architecture, Applications And Network Security, Threat And Vulnerability Assessment, Compliance And Awareness, Security Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Security vulnerability scanning ppt powerpoint presentation inspiration rules cpb
Security vulnerability scanning ppt powerpoint presentation inspiration rules cpbPresenting this set of slides with name Security Vulnerability Scanning Ppt Powerpoint Presentation Inspiration Rules Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Security Vulnerability Scanning to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Itil security management process ppt powerpoint presentation visual aids slides cpb
Itil security management process ppt powerpoint presentation visual aids slides cpbPresenting this set of slides with name ITIL Security Management Process Ppt Powerpoint Presentation Visual Aids Slides Cpb. This is an editable Powerpoint three stages graphic that deals with topics like ITIL Security Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Five year roadmap for secure business process management
Five year roadmap for secure business process managementPresenting Five Year Roadmap For Secure Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Half yearly roadmap for secure business process management
Half yearly roadmap for secure business process managementPresenting Half Yearly Roadmap For Secure Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Quarterly roadmap for secure business process management
Quarterly roadmap for secure business process managementPresenting Quarterly Roadmap For Secure Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Six months roadmap for secure business process management
Six months roadmap for secure business process managementPresenting Six Months Roadmap For Secure Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Three months roadmap for secure business process management
Three months roadmap for secure business process managementPresenting Three Months Roadmap For Secure Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Credit Card Payment Processing Security
Credit Card Payment Processing SecurityThis slide outline the basics of payment processing security to protect business operations and sensitive consumer data. It includes secure data storage, payment data encryption and payment data tokenization. Presenting our set of slides with Credit Card Payment Processing Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Secure Data Storage, Payment Data Encryption.
-
 Credit Card Security Processing Icon
Credit Card Security Processing IconIntroducing our Credit Card Security Processing Icon set of slides. The topics discussed in these slides are Credit Card Security Processing. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security Requirement In Credit Card Processing
Security Requirement In Credit Card ProcessingThis slide outline six goals and requirement that consider in PCI Payment Card Industry complaint for credit card processing. It includes the six key goals and payment card industry and data security standard requirements. Introducing our Security Requirement In Credit Card Processing set of slides. The topics discussed in these slides are Payment Card Industry, Security Standard Requirements. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Process To Formulate Cyber Security Communication Plan
Process To Formulate Cyber Security Communication PlanThis slide provides information to develop a cyber security communication plan effectively and efficiently. It includes elements such as formulate committee, identify scenarios, draft statement, rehearse plan and regulatory compliance. Introducing our premium set of slides with Process To Formulate Cyber Security Communication Plan Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Formulate Committee, Draft Statement, Rehearse, Plan, Regulatory Compliance So download instantly and tailor it with your information.
-
 Cloud Access Security Broker Working Process Ppt Ideas Grid
Cloud Access Security Broker Working Process Ppt Ideas GridThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Introducing Cloud Access Security Broker Working Process Ppt Ideas Grid. to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Discovery, Classification, Remediation, using this template. Grab it now to reap its full benefits.
-
 Security Process In Powerpoint And Google Slides Cpb
Security Process In Powerpoint And Google Slides CpbPresenting our Security Process In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Security Process. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Communication Plan Of Security Crisis Management Process
Communication Plan Of Security Crisis Management ProcessThis slide showcases flowchart depicting items considered when incident is reported. This template focuses son preparation of robust cybersecurity crisis management plan. It includes information related to notifying security team, classifying incidents, etc.Presenting our well structured Communication Plan Of Security Crisis Management Process. The topics discussed in this slide are Strengthening Continued, Implement Stronger Defences, Improve Incidents. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Security Action Plan Process
Cyber Security Action Plan ProcessThis slide illustrates action plan process of cyber security. It further consists steps such as system hygiene, plan development, create risk profile, evaluate and measure, minimize risk, cyber insurance, etc Introducing our premium set of slides with Cyber Security Action Plan Process. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Action, Security, Process. So download instantly and tailor it with your information.
-
 Information Security Program Action Plan Process
Information Security Program Action Plan ProcessThis slide represents action plan process for information security programs. It consists of steps such as make information security team, manage assets and inventory, evaluate risk, manage risk, create incident recovery plan, etc Introducing our Information Security Program Action Plan Process set of slides. The topics discussed in these slides are Security, Program, Process. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.




