Powerpoint Templates and Google slides for Security Process
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cycle Input Output Business Expansion Process Security Improvement Automation
Cycle Input Output Business Expansion Process Security Improvement AutomationIf you require a professional template with great design, then this Cycle Input Output Business Expansion Process Security Improvement Automation is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using twelve slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well-structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
 Seven petal secure authentication cloud communications process workflow
Seven petal secure authentication cloud communications process workflowIntroduce your topic and host expert discussion sessions with this Seven Petal Secure Authentication Cloud Communications Process Workflow. This template is designed using high-quality visuals, images, graphics, etc, that can be used to showcase your expertise. Different topics can be tackled using the seventeen slides included in this template. You can present each topic on a different slide to help your audience interpret the information more effectively. Apart from this, this PPT slideshow is available in two screen sizes, standard and widescreen making its delivery more impactful. This will not only help in presenting a birds-eye view of the topic but also keep your audience engaged. Since this PPT slideshow utilizes well-researched content, it induces strategic thinking and helps you convey your message in the best possible manner. The biggest feature of this design is that it comes with a host of editable features like color, font, background, etc. So, grab it now to deliver a unique presentation every time.
-
 Computer system security process of disaster recovery planning
Computer system security process of disaster recovery planningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Introducing Computer System Security Process Of Disaster Recovery Planning to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Plan Testing, Approval, Recovery Plans, Data Collection, Forming Data Recovery Plan, using this template. Grab it now to reap its full benefits.
-
 Data security it process of disaster recovery planning ppt slides download
Data security it process of disaster recovery planning ppt slides downloadThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Introducing Data Security IT Process Of Disaster Recovery Planning Ppt Slides Download to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Approval, Create Disaster, Recovery Team, Perform, Risk Analysis, Prioritize Procedures And Operations, Define Recovery Plans, using this template. Grab it now to reap its full benefits.
-
 Security guard services proposal specializing in ppt slides rules
Security guard services proposal specializing in ppt slides rulesIntroducing Security Guard Services Proposal Specializing In Ppt Slides Rules to increase your presentation threshold. Encompassed with twelve stages, this template is a great option to educate and entice your audience. Dispence information on Apartment Complexes, Construction Sites, Entertainment Facilities, Security Consulting, Investigations, Special Events, Communication Hotline, using this template. Grab it now to reap its full benefits.
-
 Risk Analysis Process In Cyber Security
Risk Analysis Process In Cyber SecurityThis slide outlines the risk analysis process for cyber security to effectively and efficiently protect their department assets. It includes key steps such as conduct risk assessment survey, identify risks, analyse risks, develop a risk management plan, implement risk management plan and monitor risks.Introducing our premium set of slides with Risk Analysis Process In Cyber Security. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Assessment Survey, Identify Risks, Analyze Risks. So download instantly and tailor it with your information.
-
 Common Issues Addressed By Security Patch Management Process
Common Issues Addressed By Security Patch Management ProcessFollowing slide highlights common problems tackled by security patch management process. The purpose of this slide is to build an organizations overall security position and maintain the integrity of its IT and operational environment. It includes factors such as data breaches, loss of productivity, etc.Presenting our set of slides with Common Issues Addressed By Security Patch Management Process. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Reputation Damage, Unintended System, Security Incidents.
-
 Effective Security Patch Management Process For Manufacturing Business
Effective Security Patch Management Process For Manufacturing BusinessThis slide showcases process of security patch management for manufacturing business. This template aims to help businesses integrate key components into a comprehensive security patch management process to maintain the stability of their operations. It includes phases such as vulnerability assessment, risk assessment, etc.Introducing our premium set of slides with Effective Security Patch Management Process For Manufacturing Business. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Vulnerability Assessment, Risk Assessment, Change Management. So download instantly and tailor it with your information.
-
 Ensuring Seamless Telecom Networks With Security Patch Management Process
Ensuring Seamless Telecom Networks With Security Patch Management ProcessFollowing slide highlights enabling of seamless telecom networks with security patch management process. The purpose of this template is to help businesses protect their networks to provide uninterrupted services and reliability of their offerings. It includes elements such as securing 5G network, etc.Introducing our premium set of slides with Ensuring Seamless Telecom Networks With Security Patch Management Process. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network Vulnerability, Network Performance, Response Planning. So download instantly and tailor it with your information.
-
 Importance Of Security Patch Management Process In Modern Business
Importance Of Security Patch Management Process In Modern BusinessFollowing slide highlights the necessity of security patch management process in business. The purpose of this template is to assist businesses in protecting their data from attacks and reduce unnecessary expenditures. It includes elements such as protection against cyberattacks, compliance with regulations, etc.Presenting our set of slides with Importance Of Security Patch Management Process In Modern Business. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Against Cyberattacks, Address Vulnerabilities, Maintain Compliance
-
 Reducing Downtime With Security Patch Management Process
Reducing Downtime With Security Patch Management ProcessFollowing slide showcases security patch management process for minimizing downtime. The purpose of this slide is to aid businesses in striking a balance between secure environment and smooth business operations for minimizing downtime. It includes steps such as patch testing, automated deployment, etc.Presenting our set of slides with Reducing Downtime With Security Patch Management Process. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Regular Maintenance, Performance Testing, Monitoring Alerting.
-
 Role Of Risk Assessment In Security Patch Management Process For Financial Software
Role Of Risk Assessment In Security Patch Management Process For Financial SoftwareFollowing slide highlights the importance of risk assessment in security patch management process. The purpose of this template is to help financial institutions allocate resources effectively and maintain the trust of regulatory bodies. It includes elements such as cost benefit analysis, contingency planning, etc.Introducing our premium set of slides with Role Of Risk Assessment In Security Patch Management Process For Financial Software. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Contingency Planning, Communication Transparency, Monitoring Auditing. So download instantly and tailor it with your information.
-
 Security Patch Management Process For Healthcare IT Systems
Security Patch Management Process For Healthcare IT SystemsFollowing slide showcases the healthcare industry security patch management process. The purpose of this slide is to help healthcare organizations in ensuring that their IT systems are patched safely and effectively. It includes steps such as define, identify and prioritize, etc.Presenting our set of slides with Security Patch Management Process For Healthcare IT Systems. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Roles Responsibilities, Ensure Introduced, Deployment Depends.
-
 Unique Security Patch Management Process For Online Retailers
Unique Security Patch Management Process For Online RetailersThis slide highlights the e commerce business security patch management process. The purpose of this slide is to help businesses in ensuring a smooth e commerce experience while maintaining industry standards. It includes steps such as regulatory focus, risk assessment, etc.Introducing our premium set of slides with Unique Security Patch Management Process For Online Retailers. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Automated Deployment, Effective Communication, Thorough Testing. So download instantly and tailor it with your information.
-
 4 Step Development Process For Big Data Analytics Security
4 Step Development Process For Big Data Analytics SecurityThis slide depicts the 4 step developmental process for big data analytics. The purpose of this slide is to help the business establish big data security analytics in an appropriate manner for safeguarding sensitive and important business information. It includes steps such as classification, encryption, etc. Presenting our set of slides with 4 Step Development Process For Big Data Analytics Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Classification, Data Encryption.
-
 Process For Creating Network Security Management Plan
Process For Creating Network Security Management PlanThis slide showcases the process of network security in business. The main purpose of this slide is to understand and maintain network security in the workplace. This includes understanding business models, identifying threats, developing IT security policies, etc.Introducing our premium set of slides with Process For Creating Network Security Management Plan. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Understanding Business, Identifying Threat, Maintain Security Future. So download instantly and tailor it with your information.
-
 Cloud Access Security Broker Working Process Cloud Security Model
Cloud Access Security Broker Working Process Cloud Security ModelThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Working Process Cloud Security Model. This template helps you present information on three stages. You can also present information on Discovery, Classification, Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Security Year Rules Jobs In Powerpoint And Google Slides Cpb
Social Security Year Rules Jobs In Powerpoint And Google Slides CpbPresenting our Social Security Year Rules Jobs In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Social Security Year Rules Jobs This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security Protocols Recovery Resolution Plan In Powerpoint And Google Slides Cpb
Security Protocols Recovery Resolution Plan In Powerpoint And Google Slides CpbPresenting Security Protocols Recovery Resolution Plan In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Protocols Recovery Resolution Plan. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 SASE Network Security Cloud Access Security Broker Working Process
SASE Network Security Cloud Access Security Broker Working ProcessThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Increase audience engagement and knowledge by dispensing information using SASE Network Security Cloud Access Security Broker Working Process. This template helps you present information on three stages. You can also present information on Discovery, Classification, Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Audit Process For Digital Ecosystem
Cyber Security Audit Process For Digital EcosystemThis slide elaborates on cybersecurity audit process and provides details about how to implement protection in a digital ecosystem. It includes elements such as build blueprint, audit frequently, etc. Presenting our set of slides with Cyber Security Audit Process For Digital Ecosystem. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Define Audit Purpose, Build Blueprint, Identify Evaluate Risk Management.
-
 Security Deposit Rules In Powerpoint And Google Slides Cpb
Security Deposit Rules In Powerpoint And Google Slides CpbPresenting our Security Deposit Rules In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Security Deposit Rules. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Overview And Workflow Process Of Eclipse Attack Hands On Blockchain Security Risk BCT SS V
Overview And Workflow Process Of Eclipse Attack Hands On Blockchain Security Risk BCT SS VThe following slide showcases the brief introduction of eclipse attack to have understanding of malicious node among peer-to peer network P2P. It includes elements such as how does and eclipse attack works, reconnecting with malicious node, exposure to information, etc. Introducing Overview And Workflow Process Of Eclipse Attack Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Enabled Attack, Achieve Control, Incoming And Outgoing, using this template. Grab it now to reap its full benefits.
-
 Overview And Working Process Of Ddos Attack Hands On Blockchain Security Risk BCT SS V
Overview And Working Process Of Ddos Attack Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of distributed denial of service DDOS attack to prevent user from leveraging key information. It includes elements such as hampering website with excessive internet traffic, minimizing website downtime, etc. Increase audience engagement and knowledge by dispensing information using Overview And Working Process Of Ddos Attack Hands On Blockchain Security Risk BCT SS V. This template helps you present information on four stages. You can also present information on Website Hostage, Close The Attack, Inability To Resolve using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 About Devsecops Model Workflow Process Devsecops Best Practices For Secure
About Devsecops Model Workflow Process Devsecops Best Practices For SecureThis slide gives an overview of the working procedure of DevSecOps. The purpose of this slide is to discuss the various steps involved in the DevSecOps working process, these include committing, analyzing, setting up the environment, testing, deploying, monitoring, and repeating. Introducing About Devsecops Model Workflow Process Devsecops Best Practices For Secure to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Devsecops Working Process, Analyzing, Testing, Deploying, Monitoring, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure Continuous Process Improvement In Devsecops
Devsecops Best Practices For Secure Continuous Process Improvement In DevsecopsThis slide discusses the DevSecOps program requirement for continuous improvement. The purpose of this slide is to explain the needs of the DevSecOps program for achieving efficiency, these include strategic goals, architecture operation, and program evaluation. Introducing Devsecops Best Practices For Secure Continuous Process Improvement In Devsecops to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Strategic Goals, Architecture And Operations, Program Evaluation, Devops Environment, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure Enabling Devsecops Implementation Through Process
Devsecops Best Practices For Secure Enabling Devsecops Implementation Through ProcessThis slide explains the process involved in DevSecOps implementation. The purpose of his slide is to discuss the process involving automate dev. and production environments, automate software testing, automate software deployment, automate monitoring and alerting, and so on. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Enabling Devsecops Implementation Through Process. This template helps you present information on eight stages. You can also present information on Devsecops Implementation, Production Environments, Automate Software Testing, Automate Software Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Devsecops Best Practices For Secure Key Processes Followed In Devsecops Model
Devsecops Best Practices For Secure Key Processes Followed In Devsecops ModelThis slide discusses the various processes followed in DevSecOps. The purpose of this slide is to highlight the processes, including code analysis, change management, compliance management, threat modelling and security training. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Key Processes Followed In Devsecops Model. This template helps you present information on five stages. You can also present information on Code Analysis, Change Management, Compliance Managements, Threat Modelling using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Devsecops Best Practices For Secure Success Criteria For Devsecops Model Process
Devsecops Best Practices For Secure Success Criteria For Devsecops Model ProcessThis slide highlights the success criteria followed for the DevSecOps process. The purpose of this slide is to discuss the various standards, including open collaboration to shared objectives, security at source, reinforcement and elevations through automation, and so on. Introducing Devsecops Best Practices For Secure Success Criteria For Devsecops Model Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Proactive Monitoring And Recursive, Reinforce And Elevate Through Automation, Security At Source, using this template. Grab it now to reap its full benefits.
-
 Sase Model Cloud Access Security Broker Working Process
Sase Model Cloud Access Security Broker Working ProcessThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Introducing Sase Model Cloud Access Security Broker Working Process to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Discovery, Classification, Remediation, using this template. Grab it now to reap its full benefits.
-
 Digital Signal Processing In Modern Important Factors To Contemplate Regarding DSP Security
Digital Signal Processing In Modern Important Factors To Contemplate Regarding DSP SecurityThis slide represents the important attributes to contemplate DSP security. The purpose of this slide is to highlight the factors of DSPO security such as data encryption, Access control, secure communication, etc. Increase audience engagement and knowledge by dispensing information using Digital Signal Processing In Modern Important Factors To Contemplate Regarding DSP Security. This template helps you present information on twelve stages. You can also present information on Firmware Security, Physical Security, Secure Communication, Data Encryption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Digital Signal Processing In Modern Major Security Aspects Digital Signal Processing Solve
Digital Signal Processing In Modern Major Security Aspects Digital Signal Processing SolveThis slide showcases the solution to major security aspects of Digital Signal Processing in modern communication systems. The purpose of this slide is to highlight the security aspects such as encryption and data security, audio and speech authentication, biometric security, etc. Introducing Digital Signal Processing In Modern Major Security Aspects Digital Signal Processing Solve to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Audio And Speech Authentication, Biometric Security, Encryption And Data Security, Network Security And Intrusion Detection, using this template. Grab it now to reap its full benefits.
-
 Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It
Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various features of Internet Protocol Security IPsec mechanism. The properties of IPsec include authentication, privacy, integrity, key management, tunnelling, flexibility and interoperability. Introducing Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Key Management, Interoperability, using this template. Grab it now to reap its full benefits.
-
 Workflow For Security Incident Management Process
Workflow For Security Incident Management ProcessThis slide depicts the information flow for threat incident management process. The purpose of this slide is to help the business ensure its incident management process is streamlined through the use of categorization, escalation, etc. Presenting our set of slides with Workflow For Security Incident Management Process. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identification, Categorization, Escalation.
-
 SD WAN Model Cloud Access Security Broker Working Process
SD WAN Model Cloud Access Security Broker Working ProcessThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Introducing SD WAN Model Cloud Access Security Broker Working Process to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Classification And Remediation, Control And Transparency Across Data, Risks In The Cloud, using this template. Grab it now to reap its full benefits.
-
 Firewall Network Security IP Internet Protocol Reputation Function In NGFW
Firewall Network Security IP Internet Protocol Reputation Function In NGFWThis slide outlines the overview of the IP Reputation function used in Next Generation Firewalls. The purpose of this slide is to introduce the Internet Protocol IP reputation, including its features and limitations. This function blocks network traffic based on the reputation score of Ips. Introducing Firewall Network Security IP Internet Protocol Reputation Function In NGFW to increase your presentation threshold. Encompassed with Eight stages, this template is a great option to educate and entice your audience. Dispence information on Policy Enforcement, Network Visibility, Streamlined Adaptability using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker Working Process Next Generation CASB
Cloud Access Security Broker Working Process Next Generation CASBThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Introducing Cloud Access Security Broker Working Process Next Generation CASB to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Working Process, Discovery, Classification, Remediation using this template. Grab it now to reap its full benefits.
-
 Cyber Security Awareness Facts And Statistics Implementing Cyber Risk Management Process
Cyber Security Awareness Facts And Statistics Implementing Cyber Risk Management ProcessThe following slide showcases some facts and figures to generate awareness about cyber-crimes. It includes elements such as hike in ransomware attacks, more employees are expected to be target of malware attacks, increasing cost of data breaches etc. Introducing Cyber Security Awareness Facts And Statistics Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering, Data Breaches, Mobile Malware Attacks, using this template. Grab it now to reap its full benefits.
-
 Critical Infrastructure Security Response Process
Critical Infrastructure Security Response ProcessThis slide represents the infrastructure security process for assessing preparedness. Its objective is to involve and study critical infrastructure and provide protection. This slide includes identification of infrastructure, assessment of vulnerabilities, prioritise, etc. Introducing our premium set of slides with Critical Infrastructure Security Response Process. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Infrastructure, Vulnerabilities, Prioritise. So download instantly and tailor it with your information.
-
 Process To Determine Adequate Cyber Security Control
Process To Determine Adequate Cyber Security ControlThis slide represents the process to identifying adequate cyber security control for business to prevent online threats and implement necessary steps. It includes various steps such as evaluate size of the company, identify scope of IT infrastructure, etc. Presenting our set of slides with Process To Determine Adequate Cyber Security Control This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify Scope Of It Infrastructure, Evaluate Size Of Company, Investment In Cyber Security
-
 Six Steps Process To Review Strategic Retirement Planning To Build Secure Future Fin SS
Six Steps Process To Review Strategic Retirement Planning To Build Secure Future Fin SSThis slide shows information about various stages which can be used by individuals to review retirement plan. These steps are schedule, gather relevant information, evaluate, consider changes, etc. Introducing Six Steps Process To Review Strategic Retirement Planning To Build Secure Future Fin SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Review Retirement Plan, Portfolio, Retirement Plan, using this template. Grab it now to reap its full benefits.
-
 Email Authentication And Security Working Process
Email Authentication And Security Working ProcessThis slide highlights the email authentication and security working process which includes sender establishes authentication rules, and sender configuration. Presenting our set of slides with Email Authentication And Security Working Process. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Email Infrastructure, Authentication Rules, Authentication Results.
-
 Primary Protocols Used In Email Security
Primary Protocols Used In Email SecurityThis slide is an overview of different protocols used in email security which includes simple mail transfer protocol secure and sender policy framework. Introducing our premium set of slides with Primary Protocols Used In Email Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Mail Transfer, Policy Framework, Layer Security. So download instantly and tailor it with your information.
-
 Log Management Process In Application Security
Log Management Process In Application SecurityThis slide showcases the introduction of log management in application security for decreasing the security threats. Increase audience engagement and knowledge by dispensing information using Log Management Process In Application Security. This template helps you present information on five stages. You can also present information on Handling Security Logs, Non Compliance Risks Attacks, Ensure Data Security, Log Management Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Process Phases Of Penetration Testing In Application Security
Process Phases Of Penetration Testing In Application SecurityThis slide highlights the steps for implementing penetration testing which include planning and reconnaissance, gaining access, etc. Introducing Process Phases Of Penetration Testing In Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Planning And Reconnaissance, Gaining Access, Maintaining Access, Analysis And WAF Configuration, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Overview And Process Of Tokenization In Data Security
Tokenization For Improved Data Security Overview And Process Of Tokenization In Data SecurityThis slide highlights the introduction and phases of tokenization in data security. The purpose of this slide is to showcase the overview and process such as various assets, verification of ownership, transfer to blockchain, etc. Introducing Tokenization For Improved Data Security Overview And Process Of Tokenization In Data Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Tokenization In Data Security, While Ensuring Security, Small And Midsize Enterprises, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System
Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based SystemThis slide highlights the key functions within a cloud-based system in data security. The purpose of this slide is to outline the Process activities in a cloud-based system which include gathering, creating, retrieving data, etc. Introducing Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Tokenization Process Activities, Cloud Based System, Retrieving Data, using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Process Of Implementing Cloud Native Application Security
Application Security Implementation Plan Process Of Implementing Cloud Native Application SecurityThis slide highlights the steps for deploying cloud-native application security which include understanding principles, risk assessment, etc. Introducing Application Security Implementation Plan Process Of Implementing Cloud Native Application Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Risk Assessment, Continuous Monitoring, Container Security, Implement Strong Access Controls, using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Working Process Of Effective Logging Implementation
Application Security Implementation Plan Working Process Of Effective Logging ImplementationThis slide outlines the steps for deploying effective logging which include assess requirements, select logging tool, defining logging standards, etc. Introducing Application Security Implementation Plan Working Process Of Effective Logging Implementation to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Ensure Security, Centralize Log Management, Define Logging Standards, Select Logging Tools, using this template. Grab it now to reap its full benefits.
-
 Web Application Security Testing Process Phases
Web Application Security Testing Process PhasesThis slide showcases the process phases of implementing web application security which include information gathering, planning analysis, etc. Introducing our premium set of slides with name Web Application Security Testing Process Phases. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Gathering, Vulnerability Detection, Reporting, Planning Analysis. So download instantly and tailor it with your information.
-
 Steps For Effective Triage Cyber Security Process
Steps For Effective Triage Cyber Security ProcessThis slide represents steps for effective triage process which assists security teams to focus on critical threats and allocate resources effectively., It includes steps for effective triage cyber security process such as identify, map and eradicate Introducing our premium set of slides with name Steps For Effective Triage Cyber Security Process Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Artifacts, Draw Event Timelines, System From Backup. So download instantly and tailor it with your information.
-
 Utilization Of Triage Cyber Security Process In It
Utilization Of Triage Cyber Security Process In ItThis slide represents utilization of triage cyber security process in IT which assists to handle large number of tickets and increases help desk efficiency. It includes utilization of triage cyber security process in IT such as IT operations, email, etc Presenting our set of slides with name Utilization Of Triage Cyber Security Process In It This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Software Testing, Agile Software Development, IT Operations
-
 Cyber Security Gap Analysis Process
Cyber Security Gap Analysis ProcessThis slide covers procedure for cyber security gap analysis such as establishing security goal, assembling skilled team, and gathering documentation to identify and address vulnerabilities and shortcomings in an organizations security measures to enhance overall resilience against cyber threats. Presenting our set of slides with name Cyber Security Gap Analysis Process. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Establish Security Goal, Assemble Skilled Team, Gather Necessary Documentation.
-
 ATP Cyber Security System Process
ATP Cyber Security System ProcessThis slide showcases the ATP cyber security process. Its aim is to help define the target and identify the anomalies. This slide includes researching target, acquiring tools, detection of virus, strengthening the system, remove virus, etc. Presenting our set of slides with name ATP Cyber Security System Process. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Plan, Intrusion, Getting Out, Sub Zero.
-
 Cloud Access Security Broker Working Process CASB Cloud Security
Cloud Access Security Broker Working Process CASB Cloud SecurityThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Working Process CASB Cloud Security. This template helps you present information on three stages. You can also present information on Cloud Access Security, Broker Working Process, Classification And Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
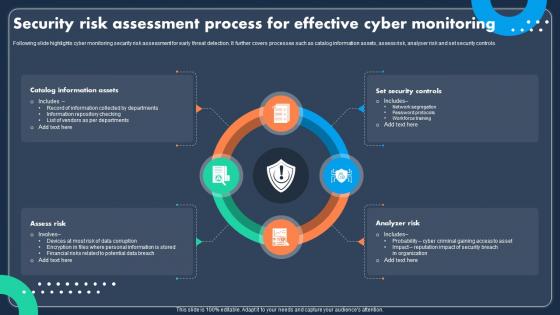 Security Risk Assessment Process For Effective Cyber Monitoring
Security Risk Assessment Process For Effective Cyber MonitoringFollowing slide highlights cyber monitoring security risk assessment for early threat detection. It further covers processes such as catalog information assets, assess risk, analyser risk and set security controls. Introducing our premium set of slides with Security Risk Assessment Process For Effective Cyber Monitoring Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Assets, Security Controls, Analyzer Risk. So download instantly and tailor it with your information.
-
 Securing Food Safety In Online Strategies To Improve Food Delivery Process In Restaurants
Securing Food Safety In Online Strategies To Improve Food Delivery Process In RestaurantsThis slide covers implementing strategies to enhance delivery efficiency such as prioritizing orders, creating counter for drivers and leveraging feedback from team. Introducing Securing Food Safety In Online Strategies To Improve Food Delivery Process In Restaurants to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Prioritize Orders, Create Counter For Delivery Partners, Assess Feedback From Team, using this template. Grab it now to reap its full benefits.
-
 Comanagement Of SIEM Cyber Security Process
Comanagement Of SIEM Cyber Security ProcessThis slide showcases the co management of SIEM cyber security process. Its aim is to list monitoring activities and manage services. This slide includes onboarding, build out, baseline, tune and monitor. Introducing our premium set of slides with name Comanagement Of SIEM Cyber Security Process. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Onboard, Build Out, Baseline. So download instantly and tailor it with your information.
-
 Physical Security Process Flow Chart
Physical Security Process Flow ChartThis slide showcases flow chart of physical security that includes determining need, identifying threats, elements of protection system, verification, testing and handing over. Presenting our set of slides with Physical Security Process Flow Chart. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Determine Security Need, Facility Characterization, Identify Potential Threats.
-
 Cyber Security Process In Industry 4 0 Icon
Cyber Security Process In Industry 4 0 IconPresenting our set of slides with Cyber Security Process In Industry 4 0 Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Process, Industry 4 0, Icon.



