Powerpoint Templates and Google slides for Security Process
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 External network security ppt powerpoint presentation slides rules cpb
External network security ppt powerpoint presentation slides rules cpbPresenting this set of slides with name External Network Security Ppt Powerpoint Presentation Slides Rules Cpb. This is an editable Powerpoint four stages graphic that deals with topics like External Network Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Financial security rules and regulation document
Financial security rules and regulation documentPresenting this set of slides with name Financial Security Rules And Regulation Document. This is a one stage process. The stages in this process are Financial Security Rules And Regulation Document. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Proven process for secure operations icon
Proven process for secure operations iconPresenting our set of slides with name Proven Process For Secure Operations Icon. This exhibits information on one stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Process, Secure, Operations.
-
 Meta Data Organizational Securing Reporting Processing Development Monitoring
Meta Data Organizational Securing Reporting Processing Development MonitoringIf you require a professional template with great design, then this Meta Data Organizational Securing Reporting Processing Development Monitoring is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using twelve slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well-structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
 Security awareness program timeline cyber security phishing awareness training ppt rules
Security awareness program timeline cyber security phishing awareness training ppt rulesThis slide covers the security awareness implementation timeline for the organization cyber security training plan with conducting a simulated phishing exercise and system vendor risk assessment. Introducing Security Awareness Program Timeline Cyber Security Phishing Awareness Training Ppt Rules to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Security Awareness Program Timeline, using this template. Grab it now to reap its full benefits.
-
 The roi of security awareness training implementing security awareness program ppt rules
The roi of security awareness training implementing security awareness program ppt rulesThis slide covers the security awareness rate of interest calculations including typical cyber risk management factor for a trained, cyber conscious workforce. Increase audience engagement and knowledge by dispensing information using The Roi Of Security Awareness Training Implementing Security Awareness Program Ppt Rules. This template helps you present information on one stage. You can also present information on Costs From Routine Security Practices, Costs From Productivity Loss, Costs To Complete Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Estimated security management plan steps set up advanced security management plan ppt rules
Estimated security management plan steps set up advanced security management plan ppt rulesThis slide shows some of the estimated future IT Security Management Critical Success Factors of the company prior to the proactive measures taken by the company to mitigate security management problems and implementing an advanced Information Security Management System. Introducing Estimated Security Management Plan Steps Set Up Advanced Security Management Plan Ppt Rules to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Security Incidents Level, Intrusion Attempts, Security Implementation Duration, using this template. Grab it now to reap its full benefits.
-
 Agenda for cloud security cloud security it ppt rules
Agenda for cloud security cloud security it ppt rulesIncrease audience engagement and knowledge by dispensing information using Agenda For Cloud Security Cloud Security IT Ppt Rules. This template helps you present information on six stages. You can also present information on Agenda using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda of effective information security risk management process
Agenda of effective information security risk management processIncrease audience engagement and knowledge by dispensing information using Agenda Of Effective Information Security Risk Management Process. This template helps you present information on three stages. You can also present information on Agenda using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Checklist Policies And Procedures Cloud Information Security
Cloud Security Checklist Policies And Procedures Cloud Information SecurityThis slide depicts the policies and procedures of the cloud security checklist. It also represents how it is essential to create new and update the current policies in an organization.Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Policies And Procedures Cloud Information Security This template helps you present information on four stages. You can also present information on Measures Organization, Technologies Security, Latest Advanced using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Process Of Cyber Security Asset Management
Process Of Cyber Security Asset ManagementThe following slide highlights the process of cyber security asset management depicting four steps which include asset inventory, synchronization, security gaps and response to save assets and mitigate the risk in minimum time. Introducing our premium set of slides with name Process Of Cyber Security Asset Management. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Asset Inventory, Synchronization, Response, Security Gaps. So download instantly and tailor it with your information.
-
 Business Cyber Security Risk Assessment Process
Business Cyber Security Risk Assessment ProcessThe slide shows cyber threat detection and protection measures in order to eliminate the potential risks to the business. The steps include identifying, detecting, responding, protecting, and recovering. Presenting our set of slides with Business Cyber Security Risk Assessment Process. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Detect, Respond, Protect.
-
 Process For Information Security Risk Assessment Information Security Risk Management
Process For Information Security Risk Assessment Information Security Risk ManagementThis slide showcases process that can help organization to perform information security risk assessment. It can help to identify security threats and allocate vulnerability rating to information assets. Introducing Process For Information Security Risk Assessment Information Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Information Security Threats, Allocating Vulnerability, Risk Assessment, using this template. Grab it now to reap its full benefits.
-
 Five Step Process Of Safety And Security
Five Step Process Of Safety And SecurityThis slide shows the five stages process of safety and security. These stages are audit, plan, execute, monitor and repeat. Introducing our premium set of slides with Five Step Process Of Safety And Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Audit, Cyber Security Training, Quarterly Plan Review. So download instantly and tailor it with your information.
-
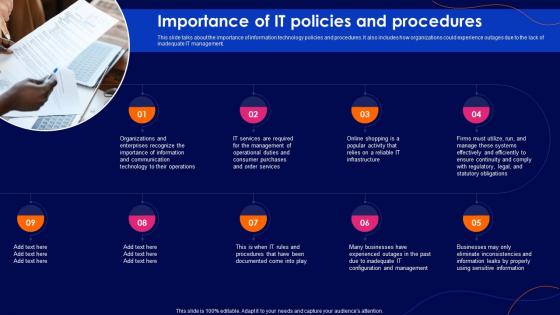 Cyber Security Policy Importance Of It Policies And Procedures
Cyber Security Policy Importance Of It Policies And ProceduresThis slide talks about the importance of information technology policies and procedures. It also includes how organizations could experience outages due to the lack of inadequate IT management. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Importance Of It Policies And Procedures. This template helps you present information on nine stages. You can also present information on Services, Operational, Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain Security Protocol List Icon
Blockchain Security Protocol List IconIntroducing our premium set of slides with Blockchain Security Protocol List Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Blockchain Security, Protocol List, Icon. So download instantly and tailor it with your information.
-
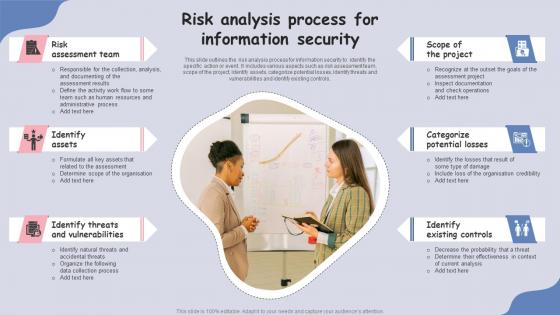 Risk Analysis Process For Information Security
Risk Analysis Process For Information SecurityThis slide outlines the risk analysis process for information security to identify the specific action or event. It includes various aspects such as risk assessment team, scope of the project, identify assets, categorize potential losses, identify threats and vulnerabilities and identify existing controls.Presenting our set of slides with Risk Analysis Process For Information Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Assessment Team, Identify Assets, Identify Threats.
-
 Strengthening Logistics Security With Patch Management Process
Strengthening Logistics Security With Patch Management ProcessFollowing slide showcases patch management process for enhancing logistics security. The purpose of this template is to help businesses foster secure operations, maintain continuity for activities and uphold customer trust. It includes elements such as long term protection, securing data integrity, etc.Presenting our set of slides with Strengthening Logistics Security With Patch Management Process. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vendor Security Collaboration, Response Preparation, Securing Data Integrity.
-
 Security Audit Procedure Icon To Verify Company Data Protection
Security Audit Procedure Icon To Verify Company Data ProtectionPresenting our set of slides with Security Audit Procedure Icon To Verify Company Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Audit Procedure, Verify Company, Data Protection.
-
 Fintech Cyber Security KYC Process
Fintech Cyber Security KYC ProcessThis slide showcases the fintech cyber security KYC process. Its aim is to identify the problems and verify the right customer to protect the data. This slide includes document verification, customer authentication, assess risk, enrolment facilitation, etc. Presenting our set of slides with name Fintech Cyber Security KYC Process. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Enrolment, Risk Assessment, Identity Verification Report.
-
 Home Selling Process For Securing Full Market Value
Home Selling Process For Securing Full Market ValueThe purpose of this slide is to outline the home selling process for securing full market value, covering the prepping of property, marketing, and negotiation tactics, due diligence, etc. Introducing Home Selling Process For Securing Full Market Value to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Market Prepping, Closing, Showings And Feedback using this template. Grab it now to reap its full benefits.


