Powerpoint Templates and Google slides for Security Model
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Firewall As A Service FWaaS Overview And Importance Cloud Security Model
Firewall As A Service FWaaS Overview And Importance Cloud Security ModelThis slide represents the overview and importance of firewall as a service. The purpose of this slide is to demonstrate the overview of cloud firewall, including its importance, services offered and top vendors such as Fortinet, Zscaler, Cisco, CheckPoint and so on. Increase audience engagement and knowledge by dispensing information using Firewall As A Service FWaaS Overview And Importance Cloud Security Model. This template helps you present information on two stages. You can also present information on Businesses, Providers, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall As A Service FWaaS Working And Security Features Cloud Security Model
Firewall As A Service FWaaS Working And Security Features Cloud Security ModelThis slide describes the working and security features of the firewall as a service. The purpose of this slide is to demonstrate the working of the firewall as a service, including its security features such as packet filtering, network monitoring, IPsec, SSL VPN support, DPI, and IP mapping. Introducing Firewall As A Service FWaaS Working And Security Features Cloud Security Model to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Packet, Internet, Network, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Cloud Security Model Ppt Background
Icons Slide For Cloud Security Model Ppt BackgroundIntroducing our well researched set of slides titled Icons Slide For Cloud Security Model Ppt Background. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Importance Of Software Defined Wide Area Network Cloud Security Model
Importance Of Software Defined Wide Area Network Cloud Security ModelThis slide talks about the need for SD WAN by comparing traditional WAN with SD WAN. The purpose of this slide is to demonstrate IT problems experienced with traditional wide area network and how SD WAN can address those problems. Present the topic in a bit more detail with this Importance Of Software Defined Wide Area Network Cloud Security Model. Use it as a tool for discussion and navigation on Problems, Solutions, Complexity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Introduction To Secure Access Service Edge SASE Cloud Security Model
Introduction To Secure Access Service Edge SASE Cloud Security ModelThis slide represents the introduction of SASE cloud security technology. The purpose of this slide is to demonstrate the core capabilities, benefits and key components of SASE. The key components include SD WAN, FWaaS, ZTNA, CASB, SWG, and unified management. Introducing Introduction To Secure Access Service Edge SASE Cloud Security Model to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Secure, Access, Service, using this template. Grab it now to reap its full benefits.
-
 Key Drivers For SASE Adoption Cloud Security Model
Key Drivers For SASE Adoption Cloud Security ModelThis slide outlines the critical drivers for secure access service edge adoption. This slide aims to demonstrate the key drivers that boost SASE adoption among different organizations, including cloud adoption, increased flexibility and agility, cost effective network traffic management, etc. Increase audience engagement and knowledge by dispensing information using Key Drivers For SASE Adoption Cloud Security Model. This template helps you present information on five stages. You can also present information on Adoption, Flexibility, Growth using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Pillars Of Cloud Access Security Broker Cloud Security Model
Pillars Of Cloud Access Security Broker Cloud Security ModelThis slide represents the four major pillars of cloud access security broker. The purpose of this slide is to showcase the main pillars of implementing a cloud access security broker. The pillars include compliance, visibility, threat protection, and data security. Introducing Pillars Of Cloud Access Security Broker Cloud Security Model to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Compliance, Visibility, Security, using this template. Grab it now to reap its full benefits.
-
 Roadmap To Implement Secure Access Service Edge Cloud Security Model
Roadmap To Implement Secure Access Service Edge Cloud Security ModelThis slide depicts the roadmap to implementing secure access service edge in an organization. The purpose of this slide is to demonstrate all the steps to be taken in the SASE implementation process, covering defining SASE objectives and needs, examining the environment and, discovering gaps, etc. Increase audience engagement and knowledge by dispensing information using Roadmap To Implement Secure Access Service Edge Cloud Security Model. This template helps you present information on seven stages. You can also present information on Objectives, Discover, Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
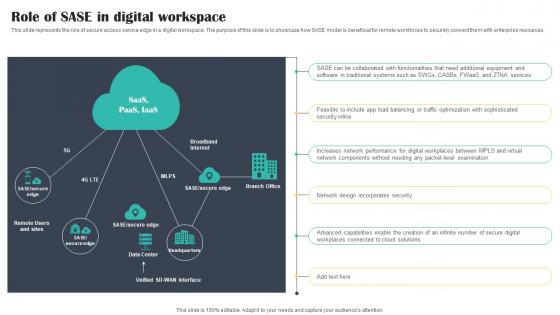 Role Of SASE In Digital Workspace Cloud Security Model
Role Of SASE In Digital Workspace Cloud Security ModelThis slide represents the role of secure access service edge in a digital workspace. The purpose of this slide is to showcase how SASE model is beneficial for remote workforces to securely connect them with enterprise resources. Introducing Role Of SASE In Digital Workspace Cloud Security Model to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Software, Optimization, Examination, using this template. Grab it now to reap its full benefits.
-
 SASE Identity Centric Architecture Overview Cloud Security Model
SASE Identity Centric Architecture Overview Cloud Security ModelThis slide outlines the overview of the centric architecture of the secure access service edge. The purpose of this slide is to demonstrate the various services executed by SASE architecture and components involved in this, such as enterprise data center, internet, internet edge, distributed edge, etc. Deliver an outstanding presentation on the topic using this SASE Identity Centric Architecture Overview Cloud Security Model. Dispense information and present a thorough explanation of Identity, Architecture, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SASE Vs SD WAN Vs SWGs Vs UTM Cloud Security Model
SASE Vs SD WAN Vs SWGs Vs UTM Cloud Security ModelThis slide demonstrates the difference between secure access service edge, software defined wide area network, secure web gateways, and unified threat management. The comparison is based on global connectivity, simplified management, optimized cloud access, multi layered protection, etc. Present the topic in a bit more detail with this SASE Vs SD WAN Vs SWGs Vs UTM Cloud Security Model. Use it as a tool for discussion and navigation on Management, Protection, Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Secure Access Service Edge Architecture Characteristics Cloud Security Model
Secure Access Service Edge Architecture Characteristics Cloud Security ModelThis slide represents the architectural characteristics of a secure access service edge. The purpose of this slide is to showcase the features of SASE architecture that include identity driven, cloud native, support for all edges, and global distribution. Increase audience engagement and knowledge by dispensing information using Secure Access Service Edge Architecture Characteristics Cloud Security Model. This template helps you present information on four stages. You can also present information on Identity, Native, Support using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Access Service Edge Implementation Steps Cloud Security Model
Secure Access Service Edge Implementation Steps Cloud Security ModelThis slide outlines the steps to implement a secure service edge in a business. The purpose of this slide is to demonstrate the various guidelines to consider while implementing the SASE model in an organization. The main steps include defining SASE goals and requirements, selecting the SD WAN backbone, incorporating zero trust solutions, etc. Introducing Secure Access Service Edge Implementation Steps Cloud Security Model to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Requirements, Solutions, Optimize, using this template. Grab it now to reap its full benefits.
-
 Secure Access Service Edge Importance Cloud Security Model
Secure Access Service Edge Importance Cloud Security ModelThis slide represents the importance of secure access service edge. This slides purpose is to demonstrate why businesses need the SASE model. The main reasons include scaling with business needs, encouraging work from anywhere environment, standing up for cyber threats, and offering a base for IoT adoption. Increase audience engagement and knowledge by dispensing information using Secure Access Service Edge Importance Cloud Security Model. This template helps you present information on four stages. You can also present information on Scales, Encourage, Evolution using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Access Service Edge SASE Architecture Cloud Security Model
Secure Access Service Edge SASE Architecture Cloud Security ModelThis slide represents the SASE architecture overview and its goals. The purpose of this slide is to demonstrate the secure access service edge architecture and its goals. The building blocks of SASE architecture include SWG, CASB, ZTNA, FWaaS, SD WAN, Thin Edge, and so on. Present the topic in a bit more detail with this Secure Access Service Edge SASE Architecture Cloud Security Model. Use it as a tool for discussion and navigation on Service, Secure, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Secure Access Service Edge Training Program Cloud Security Model
Secure Access Service Edge Training Program Cloud Security ModelThis slide represents the training program for the secure access service edge model. The purpose of this slide is to demonstrate the teams eligible for training, the modules to be covered during the training, the schedule and venue of the training. Deliver an outstanding presentation on the topic using this Secure Access Service Edge Training Program Cloud Security Model. Dispense information and present a thorough explanation of Access, Service, Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secure Access Service Edge Use Cases Cloud Security Model
Secure Access Service Edge Use Cases Cloud Security ModelThis slide represents the use cases of secure access service edge within an organization. The purpose of this slide is to demonstrate the various use cases of the SASE model, including rapid response to network demand, support for IoT and edge computing, VPN replacement, performance assurance and so on. Increase audience engagement and knowledge by dispensing information using Secure Access Service Edge Use Cases Cloud Security Model. This template helps you present information on six stages. You can also present information on Demand, Computing, Replacement using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Web Gateway SWG Functional Components Cloud Security Model
Secure Web Gateway SWG Functional Components Cloud Security ModelThis slide depicts the functional components of a secure web gateway, including their impact. The purpose of this slide is to demonstrate the required elements of SWG working. The main components include policy enforcement, data loss prevention, web proxy, malware detection, URL filtering, and so on. Present the topic in a bit more detail with this Secure Web Gateway SWG Functional Components Cloud Security Model. Use it as a tool for discussion and navigation on Components, Prevention, Inspection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Secure Web Gateway SWG Importance For Businesses Cloud Security Model
Secure Web Gateway SWG Importance For Businesses Cloud Security ModelThis slide outlines the importance of secure web gateways to businesses. The purpose of this slide is to demonstrate the need for SWGs for companies to protect their critical data and applications from malicious activities and actors. Increase audience engagement and knowledge by dispensing information using Secure Web Gateway SWG Importance For Businesses Cloud Security Model. This template helps you present information on six stages. You can also present information on Protecting, Corporations, Technologies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Web Gateway SWG Introduction And Features Cloud Security Model
Secure Web Gateway SWG Introduction And Features Cloud Security ModelThis slide describes the overview and features of the secure gateway. The purpose of this slide is to demonstrate the SWG and its benefits to businesses. The features include URL filtering, application control, data loss prevention, antivirus, and HTTPS inspection. Introducing Secure Web Gateway SWG Introduction And Features Cloud Security Model to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Problematic, Security, Protect, using this template. Grab it now to reap its full benefits.
-
 Secure Web Gateways SWG Setup And Working Cloud Security Model
Secure Web Gateways SWG Setup And Working Cloud Security ModelThis slide depicts the methods to setup the secure web gateways and their working. The purpose of this slide is to demonstrate the various ways in which organizations can install the SWGs. It also caters to the working and functions performed by SWGs to protect data and safe browsing on the internet. Increase audience engagement and knowledge by dispensing information using Secure Web Gateways SWG Setup And Working Cloud Security Model. This template helps you present information on eight stages. You can also present information on Implemented, Classifications, Programs using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Software Defined Wide Area Network SD WAN Introduction Cloud Security Model
Software Defined Wide Area Network SD WAN Introduction Cloud Security ModelThis slide represents the overview of SD WAN components of secure access service access. The purpose of this slide is to showcase the introduction and service components of SD WAN, including edge, orchestrator, and controller. Introducing Software Defined Wide Area Network SD WAN Introduction Cloud Security Model to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Network, Platform, Supervises, using this template. Grab it now to reap its full benefits.
-
 Timeline To Implement Cloud Access Security Broker Cloud Security Model
Timeline To Implement Cloud Access Security Broker Cloud Security ModelThis slide outlines the timeline to implement a cloud access security broker in a SASE model. The purpose of this slide is to demonstrate the different steps that would be taken by the business to deploy CASB and the steps include keeping a record of user activities, identifying risks from inside threats, and so on. Introducing Timeline To Implement Cloud Access Security Broker Cloud Security Model to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Activity, Identify, Removal, using this template. Grab it now to reap its full benefits.
-
 Timeline To Implement Secure Access Service Edge Cloud Security Model
Timeline To Implement Secure Access Service Edge Cloud Security ModelThis slide outlines the timeline to implement secure access service edge in an organization. The purpose of this slide is to demonstrate all the steps to be taken in the SASE implementation process, covering defining SASE objectives and needs, examining the environment and discovering gaps, etc. Increase audience engagement and knowledge by dispensing information using Timeline To Implement Secure Access Service Edge Cloud Security Model. This template helps you present information on seven stages. You can also present information on Objectives, Solutions, Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Traditional Networking Security Problems And SASE Solutions Cloud Security Model
Traditional Networking Security Problems And SASE Solutions Cloud Security ModelThis slide describes the traditional networking security problems and how SASE model can overcome those problems. The main problems include, remote access to on-premises resources, access to cloud resources, network access controls etc. Deliver an outstanding presentation on the topic using this Traditional Networking Security Problems And SASE Solutions Cloud Security Model. Dispense information and present a thorough explanation of Networking, Model, Solutions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Types Of Zero Trust Network Access ZTNA Models Cloud Security Model
Types Of Zero Trust Network Access ZTNA Models Cloud Security ModelThis slide describes the various types of zero trust network access models. The purpose of this slide is to demonstrate the various ZTNA models and core elements of ZTNA implementation. The model types include user protection, workload protection, and device protection. Increase audience engagement and knowledge by dispensing information using Types Of Zero Trust Network Access ZTNA Models Cloud Security Model. This template helps you present information on three stages. You can also present information on Change, Technologies, Knowledge using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Working Of Secure Access Service Edge Cloud Security Model
Working Of Secure Access Service Edge Cloud Security ModelThis slide represents the working of the secure access service edge model. The purpose of this slide is to demonstrate the working of the SASE model, comparing it to the traditional network security model. The components include cloud platforms, the internet, corporate network and so on. Present the topic in a bit more detail with this Working Of Secure Access Service Edge Cloud Security Model. Use it as a tool for discussion and navigation on Network, Security, Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Working Of Zero Trust Network Access Cloud Security Model
Working Of Zero Trust Network Access Cloud Security ModelThis slide outlines the working of zero trust network access. The purpose of this slide is to demonstrate the workflow of ZTNA, including the principles shared by all ZTNA architectures. The principles include no use of MPLS, hiding the IP addresses, securing devices, IDP and SSO platform, and so on. Deliver an outstanding presentation on the topic using this Working Of Zero Trust Network Access Cloud Security Model. Dispense information and present a thorough explanation of Working, Network, Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Zero Trust Network Access Vs Virtual Private Network Cloud Security Model
Zero Trust Network Access Vs Virtual Private Network Cloud Security ModelThis slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application level access. Present the topic in a bit more detail with this Zero Trust Network Access Vs Virtual Private Network Cloud Security Model. Use it as a tool for discussion and navigation on Workforce, Network, Private. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Zero Trust Network Access ZTNA Introduction Cloud Security Model
Zero Trust Network Access ZTNA Introduction Cloud Security ModelThis slide represents the overview of zero trust network access, including its architecture. The purpose of this slide is to demonstrate the overview and use cases of ZTNA. The primary use cases include authentication and access control and holistic control and visibility. Deliver an outstanding presentation on the topic using this Zero Trust Network Access ZTNA Introduction Cloud Security Model. Dispense information and present a thorough explanation of Network, Access, Introduction using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 ZTNA 1 0 Vs ZTNA 2 0 Cloud Security Model Ppt Pictures
ZTNA 1 0 Vs ZTNA 2 0 Cloud Security Model Ppt PicturesThis slide represents the comparison between zero trust network access versions 1.0 and 2.0. The purpose of this slide is to demonstrate the overview of both versions, including differences. It also includes the architecture of both versions of zero trust network access. Present the topic in a bit more detail with this ZTNA 1 0 Vs ZTNA 2 0 Cloud Security Model Ppt Pictures. Use it as a tool for discussion and navigation on Remote, Secures, Regulations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Analytics Solution Operating Model
Cyber Security Analytics Solution Operating ModelThe following slide highlights key points like threat intelligence, security information and event management, and analysis of user behavior to illustrate the cyber security analytics solution operating model. It helps organizations to proactively identify and respond to security threats, improving overall cybersecurity posture. Introducing our Cyber Security Analytics Solution Operating Model set of slides. The topics discussed in these slides are Intelligence, Data, Measures. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Sase Security Cloud Security Broker Implementation Models Ppt Show Graphics Tutorials
Sase Security Cloud Security Broker Implementation Models Ppt Show Graphics TutorialsThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out-of-band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Present the topic in a bit more detail with this Sase Security Cloud Security Broker Implementation Models Ppt Show Graphics Tutorials. Use it as a tool for discussion and navigation on Implementation, Technique, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Sase Security Types Of Zero Trust Network Access Ztna Models
Sase Security Types Of Zero Trust Network Access Ztna ModelsThis slide describes the various types of zero-trust network access models. The purpose of this slide is to demonstrate the various ZTNA models and core elements of ZTNA implementation. The model types include user protection, workload protection, and device protection. Deliver an outstanding presentation on the topic using this Sase Security Types Of Zero Trust Network Access Ztna Models. Dispense information and present a thorough explanation of Knowledge Conviction, Disruptive Technologies, Cultural Mindset Change using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Security Broker Implementation Models Secure Access Service Edge Sase
Cloud Security Broker Implementation Models Secure Access Service Edge SaseThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out-of-band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Increase audience engagement and knowledge by dispensing information using Cloud Security Broker Implementation Models Secure Access Service Edge Sase. This template helps you present information on three stages. You can also present information on Implementation, Applications, Inline Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Types Of Zero Trust Network Access Ztna Models Secure Access Service Edge Sase
Types Of Zero Trust Network Access Ztna Models Secure Access Service Edge SaseThis slide describes the various types of zero-trust network access models. The purpose of this slide is to demonstrate the various ZTNA models and core elements of ZTNA implementation. The model types include user protection, workload protection, and device protection. Deliver an outstanding presentation on the topic using this Types Of Zero Trust Network Access Ztna Models Secure Access Service Edge Sase. Dispense information and present a thorough explanation of Disruptive Technologies, Cultural Mindset Change, Knowledge Conviction using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS V
Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Present the topic in a bit more detail with this Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS V Use it as a tool for discussion and navigation on Employee Headcount, Average Employee Age, Gender Diversity Ratio This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategic Plan To Implement Key Access Security Control Models Strategy SS V
Strategic Plan To Implement Key Access Security Control Models Strategy SS VThis slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role-based access control and attributes based access control. Deliver an outstanding presentation on the topic using this Strategic Plan To Implement Key Access Security Control Models Strategy SS V Dispense information and present a thorough explanation of This slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role-based access control and attributes based access control, using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Strategic Plan To Implement Network Security Model To Effective Communication Strategy SS V
Strategic Plan To Implement Network Security Model To Effective Communication Strategy SS VThis slide represents the network security model for effective communication in the organization. It covers information regarding security threats, firewalls, virtual private networks, etc. Deliver an outstanding presentation on the topic using this Strategic Plan To Implement Network Security Model To Effective Communication Strategy SS V Dispense information and present a thorough explanation of Communication, Data Management, Marketing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Strategic Model For IoT Cyber Security Improving IoT Device Cybersecurity IoT SS
Strategic Model For IoT Cyber Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline strategic framework for Internet of Things IoT cyber security. Information covered in this slide is related to IoT security elements and major principles such as edge processing, device intelligence, messaging control, device initiated connections, etc. Deliver an outstanding presentation on the topic using this Strategic Model For IoT Cyber Security Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Elements, Security, Device using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Layered Defense Security Model For Enterprises
Layered Defense Security Model For EnterprisesThis slide highlights different layers of defence security model for organizations to manage security risk through multiple defensive strategies. It includes perimeter defence, host protection, application protection and data protection. Introducing our premium set of slides with Layered Defense Security Model For Enterprises. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Perimeter Defense, Host Protection, Application Protection. So download instantly and tailor it with your information.
-
 Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS V
Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS VThis slide represents key access security control models for organizations It includes discretionary access control, mandatory access control, role based access control and attributes based access control,Present the topic in a bit more detail with this Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS V Use it as a tool for discussion and navigation on Mandatory Access, Discretionary Access, Administrator Protected This template is free to edit as deemed fit for your organization Therefore download it now
-
 Network Security Model To Effective Comprehensive Guide For Deployment Strategy SS V
Network Security Model To Effective Comprehensive Guide For Deployment Strategy SS VThis slide represents the network security model for effective communication in the organization It covers information regarding security threats, firewalls, virtual private networks, etc Present the topic in a bit more detail with this Network Security Model To Effective Comprehensive Guide For Deployment Strategy SS V Use it as a tool for discussion and navigation on Protection Computer, Components Detect, Information Channel This template is free to edit as deemed fit for your organization Therefore download it now
-
 Cloud Access Security Broker Implementation Models SASE Network Security
Cloud Access Security Broker Implementation Models SASE Network SecurityThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out of band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Introducing Cloud Access Security Broker Implementation Models SASE Network Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Scanning, Forward, Reverse, using this template. Grab it now to reap its full benefits.
-
 SASE Network Security Types Of Zero Trust Network Access ZTNA Models
SASE Network Security Types Of Zero Trust Network Access ZTNA ModelsThis slide describes the various types of zero trust network access models. The purpose of this slide is to demonstrate the various ZTNA models and core elements of ZTNA implementation. The model types include user protection, workload protection, and device protection. Introducing SASE Network Security Types Of Zero Trust Network Access ZTNA Models to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Protection, Workload, Device, using this template. Grab it now to reap its full benefits.
-
 Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS V
Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS VThe following slide depicts blockchain attack identification workflow. It includes elements such as recording blockchain fingerprints, determining data breaches, aiming to deliver data to manufacturer, stealing and corrupting data, etc. Present the topic in a bit more detail with this Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Blockchain Fingerprints, Data Ownership, Data And Corrupt. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Business Model Investor Capital Pitch Deck For Pauboxs Secure Email Platform
Business Model Investor Capital Pitch Deck For Pauboxs Secure Email PlatformThis slide covers the business model canvas for email security software firm. It includes information about key partners, key activities, value proposition, key resources, distribution channels, customer relationships, customer segments, cost structure, revenue streams. Present the topic in a bit more detail with this Business Model Investor Capital Pitch Deck For Pauboxs Secure Email Platform Use it as a tool for discussion and navigation on Value Propositions, Customer Relationships, Customer Segments This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security And Trust Model Under SAP
Information Security And Trust Model Under SAPThis template depicts the data security and trust model under SAP. The purpose of this slide is to help the business ensure it protects its network and data through the implementation of information security and trust models. It includes elements such as audits and compliance, business resilience, etc. Presenting our set of slides with Information Security And Trust Model Under SAP. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Governance Policies, Audits And Compliance, Business Resilience.
-
 Requirements For Appropriate Cloud Security Model Next Generation CASB
Requirements For Appropriate Cloud Security Model Next Generation CASBThis slide outlines the different prerequisites organizations should consider when choosing a cloud security model and provider. The purpose of this slide is to showcase the various requirements a cloud security provider should possess, including visibility and threat detection, continuous compliance, data encryption and so on. Increase audience engagement and knowledge by dispensing information using Requirements For Appropriate Cloud Security Model Next Generation CASB This template helps you present information on five stages. You can also present information on Continuous Compliance, Data Encryption, Strong Authentication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Types Of Web Application Firewall Security Models
Firewall Network Security Types Of Web Application Firewall Security ModelsThis slide represents the various types of WAF security models. The purpose of this slide is to showcase the different models of WAF security models including the whitelist or negative security model, blacklist or positive security model, and hybrid security model. Present the topic in a bit more detail with this Firewall Network Security Types Of Web Application Firewall Security Models Use it as a tool for discussion and navigation on Black List Access Control, White List Access Control This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Firewall Network Security About WAF Overview Features And Security Models
Firewall Network Security About WAF Overview Features And Security ModelsThis slide outlines the overview of the Web Application Firewall system, its features, and security models. The purpose of this slide is to give an overview of Web Application Firewall, its architecture, characteristics, and security models such as whitelist, blacklist, and hybrid. Deliver an outstanding presentation on the topic using this Firewall Network Security About WAF Overview Features And Security Models Dispense information and present a thorough explanation of Security Models, Features using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SD WAN Model Benefits Of Secure Access Service Edge Sase
SD WAN Model Benefits Of Secure Access Service Edge SaseThis slide outlines the key benefits of secure access service edge. The purpose of this slide is to showcase the advantages of the SASE model, such as flexibility, cost savings, reduced complexity, increased performance, threat and data protection and increased network performance. Present the topic in a bit more detail with this SD WAN Model Benefits Of Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Data Protection, Increased Network Performance, Cost Savings, Secure Access Service Edge. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 SD WAN Model Best Practices To Implement Cloud Access Security Broker
SD WAN Model Best Practices To Implement Cloud Access Security BrokerThis slide represents the best practices for implementing a cloud access security broker within an organization. The purpose of this slide is to demonstrate the best practices and their possible impact on the overall business operations. The best practices include building visibility, forecasting risk and releasing CASB. Deliver an outstanding presentation on the topic using this SD WAN Model Best Practices To Implement Cloud Access Security Broker. Dispense information and present a thorough explanation of Network And Cloud Infrastructure Monitoring, Protection Against Risks, Specific Risk Prototypes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SD WAN Model Budget To Implement Secure Access Service Edge
SD WAN Model Budget To Implement Secure Access Service EdgeThis slide depicts the budget calculation for implementing a secure access service edge model in an organization. The purpose of this slide is to showcase the estimated and actual cost and variance for SASE model spending. The key components include SD-WAN, SWG, ZTNA, CASB, and FWaaS. Present the topic in a bit more detail with this SD WAN Model Budget To Implement Secure Access Service Edge. Use it as a tool for discussion and navigation on Secure Web Gateway, Cloud Access Security Broker, Zero Trust Network Access, Firewall As A Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 SD WAN Model Challenges With Traditional Network Security Approaches
SD WAN Model Challenges With Traditional Network Security ApproachesThis slide describes the challenges with traditional network security approaches. The purpose of this slide is to demonstrate the various challenges caused by conventional network security methods while backhauling traffic to data centers, including disjoint management, workload, slower cloud adoption, and so on. Deliver an outstanding presentation on the topic using this SD WAN Model Challenges With Traditional Network Security Approaches. Dispense information and present a thorough explanation of Challenges With Traditional Network, Security Approaches, Including Disjoint Management, Workload, Slower Cloud Adoption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SD WAN Model Checklist To Implement Secure Access Service Edge
SD WAN Model Checklist To Implement Secure Access Service EdgePresent the topic in a bit more detail with this SD WAN Model Checklist To Implement Secure Access Service Edge. Use it as a tool for discussion and navigation on Test And Troubleshoot, Incorporate Zero Trust Solutions, Goals And Requirements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 SD WAN Model Cloud Access Security Broker Casb Overview
SD WAN Model Cloud Access Security Broker Casb OverviewThis slide outlines the overview and benefits of cloud access security broker. The purpose of this slide is to demonstrate the benefits of CASB, such as risk visibility, threat prevention, granular cloud usage control, shadow IT assessment and management, and data loss prevention. Introducing SD WAN Model Cloud Access Security Broker Casb Overview to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Granular Cloud Usage Control, Data Loss Prevention, Cloud Access Security Broker, Risk Visibility, using this template. Grab it now to reap its full benefits.
-
 SD WAN Model Cloud Access Security Broker Implementation Models
SD WAN Model Cloud Access Security Broker Implementation ModelsThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out-of-band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Increase audience engagement and knowledge by dispensing information using SD WAN Model Cloud Access Security Broker Implementation Models. This template helps you present information on three stages. You can also present information on Cloud Access Security Broker, Api Scanning, Forward Proxy, Reverse Proxy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SD WAN Model Cloud Access Security Broker Use Cases
SD WAN Model Cloud Access Security Broker Use CasesThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Present the topic in a bit more detail with this SD WAN Model Cloud Access Security Broker Use Cases. Use it as a tool for discussion and navigation on Cloud Access Security Broker, Covering Protection Against Threats, Governing Usage, Securing Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 SD WAN Model Cloud Access Security Broker Working Process
SD WAN Model Cloud Access Security Broker Working ProcessThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Introducing SD WAN Model Cloud Access Security Broker Working Process to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Classification And Remediation, Control And Transparency Across Data, Risks In The Cloud, using this template. Grab it now to reap its full benefits.





