Powerpoint Templates and Google slides for Vulnerability Mana
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
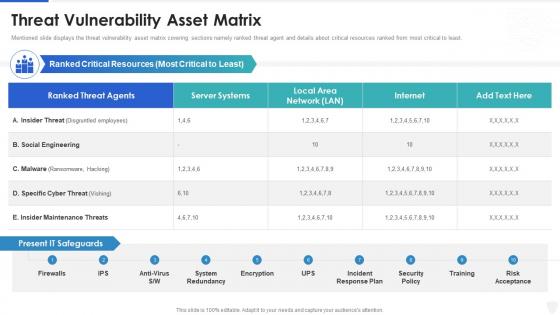 Cybersecurity and digital business risk management threat vulnerability asset matrix
Cybersecurity and digital business risk management threat vulnerability asset matrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Cybersecurity And Digital Business Risk Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enterprise vulnerability management analyze root causes
Enterprise vulnerability management analyze root causesIntroducing Enterprise Vulnerability Management Analyze Root Causes to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Perform Root Cause Analysis, Develop Corrective Actions, Update The Vulnerability, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management categorize and prioritize vulnerabilities
Enterprise vulnerability management categorize and prioritize vulnerabilitiesIntroducing Enterprise Vulnerability Management Categorize And Prioritize Vulnerabilities to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Analyze For Relevance, Determine Responsibility, Prioritize, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management conduct vulnerability assessment activities
Enterprise vulnerability management conduct vulnerability assessment activitiesIntroducing Enterprise Vulnerability Management Conduct Vulnerability Assessment Activities to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Execute Vulnerability Scans, Execute Vulnerability Assessments, Capabilities Of The Organizations, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management content
Enterprise vulnerability management contentPresent the topic in a bit more detail with this Enterprise Vulnerability Management Content Use it as a tool for discussion and navigation on Introduction, Resolution Strategy, Vulnerability Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise vulnerability management define and document the plan
Enterprise vulnerability management define and document the planIntroducing Enterprise Vulnerability Management Define And Document The Plan to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Coordinate With Risk Management, Standard Remediation Timelines, Vulnerabilities Should, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management define measures of effectiveness
Enterprise vulnerability management define measures of effectivenessIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Define Measures Of Effectiveness. This template helps you present information on two stages. You can also present information on Identify End User Training, Train Practitioners, Define Training Requirements using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise vulnerability management define the roles and responsibilities
Enterprise vulnerability management define the roles and responsibilitiesIntroducing Enterprise Vulnerability Management Define The Roles And Responsibilities to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Monitoring Roles, Remediation Roles, Authorization Roles, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management determine approved methods of vulnerability assessment
Enterprise vulnerability management determine approved methods of vulnerability assessmentIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Determine Approved Methods Of Vulnerability Assessment. This template helps you present information on four stages. You can also present information on Required By Regulation, Operational Requirements, Determine The Legal Implications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise vulnerability management determine effectiveness of vulnerability dispositions
Enterprise vulnerability management determine effectiveness of vulnerability dispositionsIntroducing Enterprise Vulnerability Management Determine Effectiveness Of Vulnerability Dispositions to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Evaluate Disposition Efforts, Update Vulnerability Repository, Repeat Disposition, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management determine the state of the program
Enterprise vulnerability management determine the state of the programIntroducing Enterprise Vulnerability Management Determine The State Of The Program to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Relevant Stakeholders, Appropriate Work Products, Process Provides, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management key features of siem software
Improve it security with vulnerability management key features of siem softwareThis slide provides the details about our companys SIEM key features such as automated reports, log collection and classification, high scalability, security automation, etc. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Key Features Of Siem Software. This template helps you present information on seven stages. You can also present information on Comprehensive, Compliance, Classification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve it security with vulnerability management log management services
Improve it security with vulnerability management log management servicesThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Introducing Improve It Security With Vulnerability Management Log Management Services to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Collection And Normalization, Search Speed, Real Time Analysis, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management logging sources
Improve it security with vulnerability management logging sourcesThis slide covers the logging sources for SIEM which uses different devices such as security, network, servers, and applications. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Logging Sources. This template helps you present information on four stages. You can also present information on Security Devices, Network Devices, Servers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve it security with vulnerability management need for siem software company
Improve it security with vulnerability management need for siem software companyThis slide covers the need for the SIEM software which focuses on detecting incidents, compliance regulations, and incident management Introducing Improve It Security With Vulnerability Management Need For Siem Software Company to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Detecting Incidents, Compliance With Regulations, Efficient Incident Management, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management next evolution of siem software
Improve it security with vulnerability management next evolution of siem softwareThis slide focuses on the upcoming evolution of SIEM software which covers SIEM foundation, threat intelligence, user entity and behavior analytics, network traffic analysis, endpoint monitoring, and SOAR. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Next Evolution Of Siem Software. This template helps you present information on six stages. You can also present information on Foundation, Threat Intelligence, Analytics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve it security with vulnerability management organization siem log flow
Improve it security with vulnerability management organization siem log flowThis slide covers the companys log flow and understand how the data is gathered, security alerts are notified to the clients. Introducing Improve It Security With Vulnerability Management Organization Siem Log Flow to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Our Organization Siem Log Flow, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management our siem companys milestones
Improve it security with vulnerability management our siem companys milestonesThis slide provides the milestones of our company such as foundation year, revenue generation, profitability, etc. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Our Siem Companys Milestones. This template helps you present information on six stages. You can also present information on Our Siem Companys Milestones using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve it security with vulnerability management security intelligence services
Improve it security with vulnerability management security intelligence servicesThis slide covers the security intelligence services such as cyber threat intelligence, incident and response management, cyber analytics, vulnerability management, etc. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Security Intelligence Services. Dispense information and present a thorough explanation of Management, Analytics, Infrastructure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Improve it security with vulnerability management siem architecture
Improve it security with vulnerability management siem architecturePresent the topic in a bit more detail with this Improve It Security With Vulnerability Management Siem Architecture. Use it as a tool for discussion and navigation on Vulnerability Scans, Operating Systems, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Exhaustive Contingency Plan With Impact And Vulnerabilities Project Management Bundle
Exhaustive Contingency Plan With Impact And Vulnerabilities Project Management BundleThe following slide displays the contingency plan of the organization for various risks and hazards that are associated to the project, the provided highlights the nature of hazard, the further actions and the responsible team member for plan execution. Deliver an outstanding presentation on the topic using this Exhaustive Contingency Plan With Impact And Vulnerabilities Project Management Bundle. Dispense information and present a thorough explanation of Transportation System, Raw Materials, Personnel, Facility, Utilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Analysis For Effective Threat Management In Vulnerability Administration At Workplace
Impact Analysis For Effective Threat Management In Vulnerability Administration At WorkplaceThis slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Present the topic in a bit more detail with this Impact Analysis For Effective Threat Management In Vulnerability Administration At Workplace. Use it as a tool for discussion and navigation on Management, Workplace, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Threat Management Action Plan Vulnerability Administration At Workplace
Threat Management Action Plan Vulnerability Administration At WorkplaceThe threat management action plan will help in keeping the track of various potential threats that are existing in the firm. The person responsible in handling the threats will keep track of the duration in which threat is resolved. Deliver an outstanding presentation on the topic using this Threat Management Action Plan Vulnerability Administration At Workplace. Dispense information and present a thorough explanation of Threat Management Action Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Administration At Workplace Budget For Effective Threat Management At Workplace
Vulnerability Administration At Workplace Budget For Effective Threat Management At WorkplaceFirm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Budget For Effective Threat Management At Workplace. Dispense information and present a thorough explanation of Management, Workplace, Implementation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Administration At Workplace Impact Analysis Of Successful Management Implementation
Vulnerability Administration At Workplace Impact Analysis Of Successful Management ImplementationThis slide depicts the impact of successful implementation of threat management in terms improved incident management and customer satisfaction and depicts that how much the focus area has been improved from the previous state. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Impact Analysis Of Successful Management Implementation. Use it as a tool for discussion and navigation on Analysis, Management, Implementation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Selecting Secured Threat Management Software
Vulnerability Administration At Workplace Selecting Secured Threat Management SoftwareThis slide will help firm in choosing the suitable automated threat management software which is to handle existing security and privacy issues and predict upcoming threats. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Selecting Secured Threat Management Software. Use it as a tool for discussion and navigation on Management, Software, Workflows. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Technological Assessment Current Management Capabilities
Vulnerability Administration At Workplace Technological Assessment Current Management CapabilitiesThis slide provides details regarding present management capabilities assessment based on several parameters such as incidents and service requests handling rate, service failure rate, customer satisfaction score, etc. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Technological Assessment Current Management Capabilities. Use it as a tool for discussion and navigation on Technological, Assessment, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Threat Management Action Plan
Vulnerability Administration At Workplace Threat Management Action Planthem. The person responsible in handling the threat will keep track of the threat resolve duration and will check whether the threat is treated or not. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Threat Management Action Plan. Use it as a tool for discussion and navigation on Threat Management Action Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Threat Management Team Training Schedule
Vulnerability Administration At Workplace Threat Management Team Training ScheduleThe threat management team needs to have strong critical and creative thinking skills so that they become capable in taking key decisions without complete or conflicting information under immense tensed situations. The team will be trained by experts who will also use scenario based activities and costing will be per employee basis. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Threat Management Team Training Schedule. Dispense information and present a thorough explanation of Management, Schedule, Employee using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information Security
Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information SecurityThis slide showcases assessment matrix to identify risk associated with different class of information assists. It calculates severity of risk on the basis of threat and vulnerability level Present the topic in a bit more detail with this Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Assessment, Vulnerability, Associated. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information Security
Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information SecurityThis slide showcases table for allocating vulnerability rating to different class of information assets. It shows information about severity, vulnerability score and description Present the topic in a bit more detail with this Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Identification, Information, Vulnerability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Acceptance Checklist With Vulnerability Management
Risk Acceptance Checklist With Vulnerability ManagementThis slide showcases risk acceptance checklist which can be referred by IT management to accept or mitigate vulnerabilities with least amount of loss. It includes information about risks, date of occurrence, vulnerability level, next follow up, etc. Introducing our Risk Acceptance Checklist With Vulnerability Management set of slides. The topics discussed in these slides are Risk Acceptance, Checklist, Vulnerability Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 IT Risk Management Strategies IT Vulnerabilities With Threat Source And Action
IT Risk Management Strategies IT Vulnerabilities With Threat Source And ActionThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this IT Risk Management Strategies IT Vulnerabilities With Threat Source And Action. Use it as a tool for discussion and navigation on Vulnerabilities, Threat Source, Threat Action. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise Risk Management IT Vulnerabilities With Threat Source And Action
Enterprise Risk Management IT Vulnerabilities With Threat Source And ActionThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this Enterprise Risk Management IT Vulnerabilities With Threat Source And Action. Use it as a tool for discussion and navigation on Vulnerabilities, Threat Source, Threat Action. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk Management
Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk ManagementThis slide showcases assessment matrix to identify risk associate with different class of information assets. It calculates severity of risk on the basis of threat and vulnerability level. Deliver an outstanding presentation on the topic using this Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk Management. Dispense information and present a thorough explanation of Risk Assessment Matrix, Vulnerability Level, Threat Level using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat Identification And Vulnerability Assessment Information Security Risk Management
Threat Identification And Vulnerability Assessment Information Security Risk ManagementThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Present the topic in a bit more detail with this Threat Identification And Vulnerability Assessment Information Security Risk Management. Use it as a tool for discussion and navigation on Threat Identification, Vulnerability Assessment, Risk Identification. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 Vulnerability Rating For Risk Identification Information Security Risk Management
Vulnerability Rating For Risk Identification Information Security Risk ManagementThis slide showcases table for allocating vulnerability rating to different class of information assets. Its shows information about severity, vulnerability score and description. Present the topic in a bit more detail with this Vulnerability Rating For Risk Identification Information Security Risk Management. Use it as a tool for discussion and navigation on Vulnerability Score, Risk Identification, Severity. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 Four Pillars Of Vulnerability Management Program
Four Pillars Of Vulnerability Management ProgramThis slide defines the pillars of vulnerability management program framework. It includes information related to discovery, identification, reporting and response. Presenting our set of slides with Four Pillars Of Vulnerability Management Program. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identification, Reporting And Prioritization, Response And Remediation.
-
 Key Elements Of Vulnerability Management Program
Key Elements Of Vulnerability Management ProgramThis slide defines the main elements of vulnerability management program. It includes information related to assessment, management tools, integration and agility. Presenting our set of slides with Key Elements Of Vulnerability Management Program. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vulnerability Assessment, Vulnerability Management Tools, Integration And Alignment .
-
 Technological Components For Vulnerability Management Program
Technological Components For Vulnerability Management ProgramThis slide defines the technological components used for creating vulnerability management programs. It includes information related to assessment, process, software development, automation and reporting. Presenting our set of slides with Technological Components For Vulnerability Management Program. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vulnerability Assessment, Reporting, Systematic Process.
-
 Threat And Vulnerability Management Model To Measure Program Maturity
Threat And Vulnerability Management Model To Measure Program MaturityThis slide defines the vulnerability management model adopted to measure the maturity of program. It includes information related to different levels from scanning to risk management. Introducing our premium set of slides with Threat And Vulnerability Management Model To Measure Program Maturity. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Non Existent, Scanning, Assessment. So download instantly and tailor it with your information.
-
 Threats And Vulnerability Management Program Process
Threats And Vulnerability Management Program ProcessThis slide defines the functions and process adopted by the threats and vulnerability management program. It includes information related to identifying, evaluating, treating and reporting vulnerabilities. Presenting our set of slides with Threats And Vulnerability Management Program Process. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identifying Vulnerabilities, Treating Vulnerabilities, Evaluating Vulnerabilities.
-
 Vulnerability Management Program And Security Services
Vulnerability Management Program And Security ServicesThis slide defines the vulnerability management program and security services based on risk. It includes information related to integrating, assessment planning, analysis and sustainability. Presenting our set of slides with Vulnerability Management Program And Security Services. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Assessment Planning, Analysis And Reporting, Sustainability.
-
 Cybersecurity Risk Analysis And Management Plan Risk Assessment Matrix With Vulnerability And Threat
Cybersecurity Risk Analysis And Management Plan Risk Assessment Matrix With Vulnerability And ThreatThis slide showcases assessment matrix to identify risk associated with different class of information assets. It calculates severity of risk on the basis of threat and vulnerability level Deliver an outstanding presentation on the topic using this Cybersecurity Risk Analysis And Management Plan Risk Assessment Matrix With Vulnerability And Threat. Dispense information and present a thorough explanation of Assessment, Vulnerability, Threat Level using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management Plan
Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating Deliver an outstanding presentation on the topic using this Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Identification, Assessment, Vulnerability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management Plan
Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management PlanThis slide showcases table for allocating vulnerability rating to different class of information assets. Its shows information about severity, vulnerability score and description Deliver an outstanding presentation on the topic using this Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Vulnerability, Identification, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enterprise Vulnerability Management Assessment Model
Enterprise Vulnerability Management Assessment ModelThis slide showcases the enterprise vulnerability management assessment model that routinely checks the network for flaws, provides risk insights, and aids in immediately closing the loop on vulnerability management. It also includes stages such as asset discovery, scanning, remediation, assessment, etc. Presenting our set of slides with Enterprise Vulnerability Management Assessment Model. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Enterprise, Vulnerability, Management Assessment.
-
 Enterprise Vulnerability Management Process Flow Chart
Enterprise Vulnerability Management Process Flow ChartThis slide showcases the enterprise vulnerability management assessment model that routinely checks the network for flaws, provides risk insights, and aids in immediately closing the loop on vulnerability management. It also includes stages such as asset discovery, scanning, remediation, assessment, etc. Introducing our Enterprise Vulnerability Management Process Flow Chart set of slides. The topics discussed in these slides are Enterprise, Vulnerability, Management Process. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Key Features Of Enterprise Vulnerability Management
Key Features Of Enterprise Vulnerability ManagementThis slide showcases enterprise vulnerability management features that converts a typical VM programme into risk based vulnerability management, allowing enterprises to avoid breaches . It also includes features such as vulnerability assessment, high risk software audit, patch management, etc. Introducing our premium set of slides with Key Features Of Enterprise Vulnerability Management. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Vulnerability Assessment, Security Configuration Management, Active Port Audit. So download instantly and tailor it with your information.
-
 Open Source Enterprise Vulnerability Management Software Tools
Open Source Enterprise Vulnerability Management Software ToolsThis slide showcases open source enterprise vulnerability management software tools that aids companies in securing their networks by locating and repairing flaws. It also includes descriptions regarding tools such as triviy, metasploit, openscap, etc. Presenting our set of slides with Open Source Enterprise Vulnerability Management Software Tools. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Enterprise, Vulnerability, Management Software Tools.
-
 Stages In Enterprise Vulnerability Management Life Cycle
Stages In Enterprise Vulnerability Management Life CycleThis slide showcase stages in the enterprise vulnerability management life cycle to make it possible for enterprises to detect vulnerabilities in their computer system security, rank assets. It also includes steps such as discovering, prioritizing assets, assessing, reporting, remediating, etc. Introducing our premium set of slides with Stages In Enterprise Vulnerability Management Life Cycle. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Discover, Prioritize Assets, Assess. So download instantly and tailor it with your information.
-
 Steps For Enterprise Vulnerability Management Program
Steps For Enterprise Vulnerability Management ProgramThis slide showcases steps for enterprise vulnerability management that check for vulnerabilities as they are introduced into the environment since conditions can change very quickly. It also includes identifying vulnerabilities, evaluating vulnerabilities, treating and reporting, etc. Presenting our set of slides with Steps For Enterprise Vulnerability Management Program. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify Vulnerabilities, Evaluating Vulnerabilities, Reporting Vulnerabilities.
-
 Tips For A Better Enterprise Vulnerability Management Program
Tips For A Better Enterprise Vulnerability Management ProgramThis slide showcases tips for enterprise vulnerability management to provide businesses with a framework for handling these risks on a large scale while more quickly identifying weaknesses throughout the system. It also includes comprehensive scans, accelerating processes, addressing weaknesses, etc. Introducing our premium set of slides with Tips For A Better Enterprise Vulnerability Management Program. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Conduct Comprehensive Scans, Continually Assess Vulnerabilities, Accelerate Process. So download instantly and tailor it with your information.
-
 Tools Enterprise Vulnerability Management In The Organization
Tools Enterprise Vulnerability Management In The OrganizationThis slide showcases tools for enterprise vulnerability management helps businesses secure their networks by identifying and fixing issues. It also includes tools such as nessus professional,nexpose community edition, openvas, manageengine vulnerability manager plus, etc. Presenting our set of slides with Tools Enterprise Vulnerability Management In The Organization. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Manageengine, Vulnerability Manager Plus, Nessus Professional.
-
 Top Metrics For Enterprise Vulnerability Management
Top Metrics For Enterprise Vulnerability ManagementThis slide showcases enterprise vulnerability management metrics that are used to evaluate how well vulnerability management VM program is works. It also includes measures such as detection, meantime in resolving, scanner coverage, etc. Introducing our premium set of slides with Top Metrics For Enterprise Vulnerability Management. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Mean Time To Detect, Scanner Coverage, Average Window Exposure. So download instantly and tailor it with your information.
-
 Risk Based Vulnerability Management Software In Powerpoint And Google Slides Cpb
Risk Based Vulnerability Management Software In Powerpoint And Google Slides CpbPresenting Risk Based Vulnerability Management Software In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Risk Based Vulnerability Management Software. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Key Steps Involved In Vulnerability Management Process Flow
Key Steps Involved In Vulnerability Management Process FlowThe purpose of this slide is to represent procedure followed to manage identified vulnerability. It includes various stages such as performing vulnerability scan, measuring vulnerability risk, prioritizing and addressing vulnerabilities and continuous vulnerability management. Presenting our set of slides with Key Steps Involved In Vulnerability Management Process Flow. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Perform Vulnerability Scan, Measure Vulnerability Risk, Continuous Vulnerability Management.
-
 Process Flow For Vulnerability Management In Startup Business
Process Flow For Vulnerability Management In Startup BusinessThe purpose of this slide is to showcase key steps involved in managing vulnerabilities in startup business. It includes stages such as assessing IT environment, prioritizing vulnerabilities, taking action, verifying action, reporting and improving. Introducing our premium set of slides with Process Flow For Vulnerability Management In Startup Business. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Prioritize Vulnerabilities, Take Action, Verify Action, Report And Improve. So download instantly and tailor it with your information.
-
 Vulnerability Management Maturity Model Process Flow
Vulnerability Management Maturity Model Process FlowThe purpose of this slide is to showcase vulnerability handling maturity model flow chart. It includes various stages such as scanning, assessment, analysis and prioritization, business-risk management and attack management. Presenting our set of slides with Vulnerability Management Maturity Model Process Flow. This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Scanning, Assessment, Attack Management.
-
 Vulnerability Management Process Flow For IT Organization
Vulnerability Management Process Flow For IT OrganizationThis slide represents procedure to handle and resolve vulnerability in an IT company. It includes various stages, such as identifying, evaluating, remediating, verifying, and reporting. Introducing our premium set of slides with Vulnerability Management Process Flow For IT Organization. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify, Evaluate, Remediate, Verify. So download instantly and tailor it with your information.




