Powerpoint Templates and Google slides for Vulnerability Mana
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Vulnerability management lifecycle diagram powerpoint image
Vulnerability management lifecycle diagram powerpoint imagePresenting vulnerability management lifecycle diagram powerpoint image. This is a vulnerability management lifecycle diagram powerpoint image. This is a four stage process. The stages in this process are discover, verify, remediate, report.
-
 Vulnerability management icons slide
Vulnerability management icons slidePresenting our premium Vulnerability Management Icons Slide set of slides with flexible icons. The icons are designed by our group of professionals. Add these Vulnerability Management Icons Slide to your presentation to make it visually appealing. Also, edit them according to your requirement. Download it and captive your audience.
-
 Vulnerability management whitepaper analyze root causes ppt slides role
Vulnerability management whitepaper analyze root causes ppt slides roleIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Analyze Root Causes Ppt Slides Role. This template helps you present information on four stages. You can also present information on Monitor Effect, Corrective Actions, Update Vulnerability Repository, Perform Root Cause Analysis, Develop Corrective Actions To Address Root Cause using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper categorize and prioritize vulnerabilities
Vulnerability management whitepaper categorize and prioritize vulnerabilitiesIntroducing Vulnerability Management Whitepaper Categorize And Prioritize Vulnerabilities to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Analyze Relevance, Determine Responsibility, Prioritize, Produce Wealth Information, Technology, using this template. Grab it now to reap its full benefits.
-
 Vulnerability management whitepaper conduct vulnerability assessment activities
Vulnerability management whitepaper conduct vulnerability assessment activitiesIntroducing Vulnerability Management Whitepaper Conduct Vulnerability Assessment Activities to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Execute Vulnerability Scans, Execute Vulnerability Assessments, Organizations, Physical Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
 Vulnerability management whitepaper define and document the plan ppt styles inspiration
Vulnerability management whitepaper define and document the plan ppt styles inspirationIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Define And Document The Plan Ppt Styles Inspiration. This template helps you present information on five stages. You can also present information on Build Vulnerability Management Team, Coordinate Risk Management, Define Standard Remediation Timelines, Define Vulnerabilities Should Documented, Define Periodic Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper define measures of effectiveness ppt styles portfolio
Vulnerability management whitepaper define measures of effectiveness ppt styles portfolioIntroducing Vulnerability Management Whitepaper Define Measures Of Effectiveness Ppt Styles Portfolio to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Identify End User Training, Train Practitioners, employee population, organizations, Roles and Responsibility, using this template. Grab it now to reap its full benefits.
-
 Vulnerability management whitepaper define the roles and responsibilities
Vulnerability management whitepaper define the roles and responsibilitiesIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Define The Roles And Responsibilities. This template helps you present information on three stages. You can also present information on Monitoring Roles, Remediation Roles, Authorization Roles, Team, Change Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper determine approved methods of vulnerability assessment
Vulnerability management whitepaper determine approved methods of vulnerability assessmentDeliver an outstanding presentation on the topic using this Vulnerability Management Whitepaper Determine Approved Methods Of Vulnerability Assessment. Dispense information and present a thorough explanation of Organization, Analysis, Vulnerability Assessment, Team, Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability management whitepaper determine effectiveness of vulnerability dispositions
Vulnerability management whitepaper determine effectiveness of vulnerability dispositionsIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Determine Effectiveness Of Vulnerability Dispositions. This template helps you present information on two stages. You can also present information on Evaluate Disposition Efforts, Update Vulnerability Repository, Repeat Disposition Process Necessary, Vulnerability Team, Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper determine the scope of vulnerability management
Vulnerability management whitepaper determine the scope of vulnerability managementIntroducing Vulnerability Management Whitepaper Determine The Scope Of Vulnerability Management to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Organization, Primarily Focused, Resource Constraints, The Operational Environment, using this template. Grab it now to reap its full benefits.
-
 Vulnerability management whitepaper determine tools aligned to the strategy
Vulnerability management whitepaper determine tools aligned to the strategyIntroducing Vulnerability Management Whitepaper Determine Tools Aligned To The Strategy to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Identify Candidate Tools, Test Tools, Publish Authorized Tool List, Define The Exception Process, Conduct Periodic Reviews, using this template. Grab it now to reap its full benefits.
-
 Vulnerability management whitepaper develop a plan revision process
Vulnerability management whitepaper develop a plan revision processIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Develop A Plan Revision Process. This template helps you present information on three stages. You can also present information on Review Changes, Update Toolset Necessary, Update Sources, Vulnerability Information, Primary Source Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper identify sources of vulnerability information
Vulnerability management whitepaper identify sources of vulnerability informationIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Identify Sources Of Vulnerability Information. This template helps you present information on one stages. You can also present information on Vulnerability Information, Organization, Vulnerability Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper manage exposure to discovered vulnerabilities
Vulnerability management whitepaper manage exposure to discovered vulnerabilitiesIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Manage Exposure To Discovered Vulnerabilities. This template helps you present information on one stages. You can also present information on Determine Disposition Methodology, Track To Resolution, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper need for vulnerability management
Vulnerability management whitepaper need for vulnerability managementPresent the topic in a bit more detail with this Vulnerability Management Whitepaper Need For Vulnerability Management. Use it as a tool for discussion and navigation on Preventative Approaches, Vulnerability Management, Continuous Monitoring Mandates, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability management whitepaper overview ppt styles deck
Vulnerability management whitepaper overview ppt styles deckIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Overview Ppt Styles Deck. This template helps you present information on five stages. You can also present information on Scoping Statement, Identify Stakeholders, Define Regulatory And Other Legal Requirements, Stakeholder Investments, Management Involvement using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper overview ppt styles file
Vulnerability management whitepaper overview ppt styles fileIntroducing Vulnerability Management Whitepaper Overview Ppt Styles File to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Management Strategy, List Identified Stakeholders, Establish Measures Improvement, Established Monitoring Program, using this template. Grab it now to reap its full benefits.
-
 Vulnerability management whitepaper overview ppt styles icon
Vulnerability management whitepaper overview ppt styles iconIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Overview Ppt Styles Icon. This template helps you present information on five stages. You can also present information on Vulnerability Management Plan, Vulnerability Management Process, List Sources Vulnerability Information, Definition Roles And Responsibilities, Approved Tools List using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper overview ppt styles rule
Vulnerability management whitepaper overview ppt styles ruleIntroducing Vulnerability Management Whitepaper Overview Ppt Styles Rule to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Management Strategy, List Stakeholders, Management Support, Budget Vulnerability Management, using this template. Grab it now to reap its full benefits.
-
 Vulnerability management whitepaper overview ppt styles style
Vulnerability management whitepaper overview ppt styles styleDeliver an outstanding presentation on the topic using this Vulnerability Management Whitepaper Overview Ppt Styles Style. Dispense information and present a thorough explanation of Security, Weakness, Technology, Vulnerability Management, Risk Management Program using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability management whitepaper quotes ppt slides outfit
Vulnerability management whitepaper quotes ppt slides outfitPresent the topic in a bit more detail with this Vulnerability Management Whitepaper Quotes Ppt Slides Outfit. Use it as a tool for discussion and navigation on Quotes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability management whitepaper table of content ppt slides portrait
Vulnerability management whitepaper table of content ppt slides portraitPresent the topic in a bit more detail with this Vulnerability Management Whitepaper Table Of Content Ppt Slides Portrait. Use it as a tool for discussion and navigation on Introduction, Develop Plan, Vulnerability Management, Assess And Improve, Capability, Define Vulnerability Analysis And Resolution Strategy, Implement Vulnerability Analysis And Resolution Capability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability management whitepaper vulnerability management model ppt styles designs
Vulnerability management whitepaper vulnerability management model ppt styles designsDeliver an outstanding presentation on the topic using this Vulnerability Management Whitepaper Vulnerability Management Model Ppt Styles Designs. Dispense information and present a thorough explanation of Non Existent, Scanning, Assessment And Compliance, Analysis And Prioritization, Attack Management, Business Risk Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Improve it security vulnerability security information event management dashboard
Improve it security vulnerability security information event management dashboardThis slide covers the SIEM dashboard which focuses on threat activity, log and event trend, log source, impacted hosts, log classification, Deliver an outstanding presentation on the topic using this Improve It Security Vulnerability Security Information Event Management Dashboard. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Improve it security with vulnerability event management dashboard snapshot
Improve it security with vulnerability event management dashboard snapshotThis slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Event Management Dashboard snapshot. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security information event management dashboard improve security vulnerability management
Security information event management dashboard improve security vulnerability managementThis slide covers the SIEM dashboard which focuses on server status, log sources, total logs, last log, collectors, log sources etc. Deliver an outstanding presentation on the topic using this Security Information Event Management Dashboard Improve Security Vulnerability Management. Dispense information and present a thorough explanation of Management, Dashboard, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Addressing asset security managing critical threat vulnerabilities and security threats
Addressing asset security managing critical threat vulnerabilities and security threatsThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Introducing Addressing Asset Security Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ownership, Location, Confidentiality, Integrity, using this template. Grab it now to reap its full benefits.
-
 Addressing critical business managing critical threat vulnerabilities and security threats
Addressing critical business managing critical threat vulnerabilities and security threatsThis slide provides details regarding business functions recovery as firm needs to retrieve the crucial information based on priorities in various departments and time taken to retrieve the information. Present the topic in a bit more detail with this Addressing Critical Business Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Department, Priorities, Allowable Downtime. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing cyber threats in managing critical threat vulnerabilities and security threats
Addressing cyber threats in managing critical threat vulnerabilities and security threatsThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Increase audience engagement and knowledge by dispensing information using Addressing Cyber Threats In Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Healthcare, Manufacturing, Government, Energy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing indicators associated managing critical threat vulnerabilities and security threats
Addressing indicators associated managing critical threat vulnerabilities and security threatsThis slide provides details regarding indicators associated to insider threats in terms of traits, demeanor and goals, etc. Introducing Addressing Indicators Associated Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Authentication Levels, Data Exfiltration, Traits, Demeanor, using this template. Grab it now to reap its full benefits.
-
 Addressing internal and external managing critical threat vulnerabilities and security threats
Addressing internal and external managing critical threat vulnerabilities and security threatsThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Increase audience engagement and knowledge by dispensing information using Addressing Internal And External Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on two stages. You can also present information on Targeted Intelligence, Malware Intelligence, Reputation Intelligence, External Sources, Internal Sources using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing natural calamities managing critical threat vulnerabilities and security threats
Addressing natural calamities managing critical threat vulnerabilities and security threatsThis slide provides details regarding natural calamities posing as threat to organization and threat management checklist during nature crisis. Deliver an outstanding presentation on the topic using this Addressing Natural Calamities Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Threat Management Checklist using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Addressing several financial managing critical threat vulnerabilities and security threats
Addressing several financial managing critical threat vulnerabilities and security threatsThis slide provides information regarding the various financial scenarios that pose a threat to firm profitability and determine signs of financial distress. Introducing Addressing Several Financial Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Insolvency Scenario, Currency Scenario, Unexpected Fluctuations, Bankruptcy, using this template. Grab it now to reap its full benefits.
-
 Addressing threat management critical threat vulnerabilities and security threats
Addressing threat management critical threat vulnerabilities and security threatsThe threat management team needs to have strong critical and creative thinking skills so that they become capable in taking key decisions without complete or conflicting information under immense tensed situations. The team will be trained by experts who will also use scenario based activities and costing will be per employee basis. Present the topic in a bit more detail with this Addressing Threat Management Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Hypotheticals, Workshops, Field Exercises. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing various ways to managing critical threat vulnerabilities and security threats
Addressing various ways to managing critical threat vulnerabilities and security threatsThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Increase audience engagement and knowledge by dispensing information using Addressing Various Ways To Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Management Policies, User Accounts, Active Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing ways to handling managing critical threat vulnerabilities and security threats
Addressing ways to handling managing critical threat vulnerabilities and security threatsThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Introducing Addressing Ways To Handling Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cash Requirement, Financial Statements, Overheads Analysis, Currency Hedging, using this template. Grab it now to reap its full benefits.
-
 Budget for effective threat managing critical threat vulnerabilities and security threats
Budget for effective threat managing critical threat vulnerabilities and security threatsFirm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Deliver an outstanding presentation on the topic using this Budget For Effective Threat Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Incident Management, Risk Management, Client Onboarding Process, Document Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparative assessment of managing critical threat vulnerabilities and security threats
Comparative assessment of managing critical threat vulnerabilities and security threatsThis slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Present the topic in a bit more detail with this Comparative Assessment Of Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Insider Threat, Social Engineering, Maintenance Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Contingency plan for cyber managing critical threat vulnerabilities and security threats
Contingency plan for cyber managing critical threat vulnerabilities and security threatsThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Introducing Contingency Plan For Cyber Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Contingency Solutions, Contingency Considerations, using this template. Grab it now to reap its full benefits.
-
 Current potential implications managing critical threat vulnerabilities and security threats
Current potential implications managing critical threat vulnerabilities and security threatsThis slide provides information regarding the potential implications concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Deliver an outstanding presentation on the topic using this Current Potential Implications Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Increase Security Threats, Employees using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Determine sequence phases for managing critical threat vulnerabilities and security threats
Determine sequence phases for managing critical threat vulnerabilities and security threatsThis slide provides details regarding sequence phases for threat attack by threat actor in terms of installation, command and control, actions and objectives, covering tracks. Increase audience engagement and knowledge by dispensing information using Determine Sequence Phases For Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Installation, Command And Control, Actions And Objectives, Covering Tracks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine several threat actors managing critical threat vulnerabilities and security threats
Determine several threat actors managing critical threat vulnerabilities and security threatsThis slide provides details regarding several threat actors profile such as cyber criminal and hacktivists and addressing them on parameters such as motive, intent, capability, action, target victim, etc. Deliver an outstanding presentation on the topic using this Determine Several Threat Actors Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Determine Several Threat Actors Profile using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Determine staff training schedule managing critical threat vulnerabilities and security threats
Determine staff training schedule managing critical threat vulnerabilities and security threatsThe employees will also require external training which will play important role in their development. The external training will be given by experts of various fields. This training will not be free, and charges will cost the firm per employee. Introducing Determine Staff Training Schedule Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Advanced Software Training, Training Module, using this template. Grab it now to reap its full benefits.
-
 Determine threat scenario managing critical threat vulnerabilities and security threats
Determine threat scenario managing critical threat vulnerabilities and security threatsThis slide provides details regarding threat scenario assessment by understanding various phases of threat actor attack on victim. Present the topic in a bit more detail with this Determine Threat Scenario Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Threat Campaign, Actions And Objectives, Covering Tracks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Different kinds of insider digital managing critical threat vulnerabilities and security threats
Different kinds of insider digital managing critical threat vulnerabilities and security threatsThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Introducing Different Kinds Of Insider Digital Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Third Party Insider, Malicious Insider, using this template. Grab it now to reap its full benefits.
-
 Ensuring collaboration among managing critical threat vulnerabilities and security threats
Ensuring collaboration among managing critical threat vulnerabilities and security threatsThis slide provides details regarding ensuring collaboration among various functional areas in order to minimize insider cyber threats. Increase audience engagement and knowledge by dispensing information using Ensuring Collaboration Among Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on ten stages. You can also present information on Human Resources, Procurement, Public Relations, Compliance, Legal using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ensuring vital records maintenance managing critical threat vulnerabilities and security threats
Ensuring vital records maintenance managing critical threat vulnerabilities and security threatsThis slide provides information regarding vital record maintenance in order to store crucial information and the location where these records are kept also details about the alternate backup location of the records and the other sources through which records can be retrieved. Introducing Ensuring Vital Records Maintenance Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Settlement Agreements, Primary Location, using this template. Grab it now to reap its full benefits.
-
 Evaluating financial practices in firm managing critical threat vulnerabilities and security threats
Evaluating financial practices in firm managing critical threat vulnerabilities and security threatsThe firm can track the financial performance by looking the financial practices it follows in order to avoid any early signs of financial distress. Deliver an outstanding presentation on the topic using this Evaluating Financial Practices In Firm Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Accounting, Short Term Expenses, Financial Statements using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Financial performance tracking managing critical threat vulnerabilities and security threats
Financial performance tracking managing critical threat vulnerabilities and security threatsThis slide presents the dashboard which will help firm in tracking the fiscal performance. This dashboard displays revenues and expenses trends and payment received analysis. Present the topic in a bit more detail with this Financial Performance Tracking Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Revenue And Expense Trends, Receivables Analysis. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 How financial risk can be controlled managing critical threat vulnerabilities and security threats
How financial risk can be controlled managing critical threat vulnerabilities and security threatsThis slide provides details regarding various ways through financial risks can be controlled by handling liquidity risk, foreign exchange risk and credit exchange risk. Increase audience engagement and knowledge by dispensing information using How Financial Risk Can Be Controlled Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on three stages. You can also present information on Liquidity Risk, Exchange Risk, Credit Exchange Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
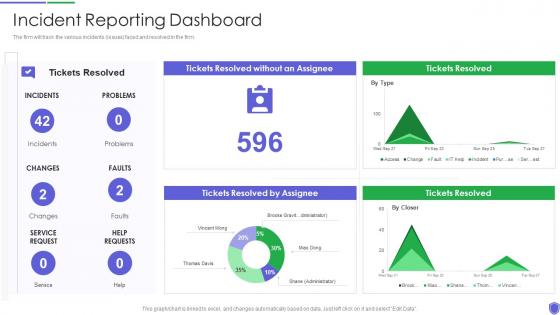 Incident reporting dashboard managing critical threat vulnerabilities and security threats
Incident reporting dashboard managing critical threat vulnerabilities and security threatsThe firm will track the various incidents issues faced and resolved in the firm. Present the topic in a bit more detail with this Incident Reporting Dashboard Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Incident Reporting Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Cyber Threats Management Dashboard
Vulnerability Administration At Workplace Cyber Threats Management DashboardThis slide portrays information regarding the dashboard that firm will use to manage cyber threats. The dashboard will provide clear picture of threats risks prevailing and how they are treated to technical engineers and board level executives. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Cyber Threats Management Dashboard. Dispense information and present a thorough explanation of Management, Dashboard, Portrays Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Third Party Cybersecurity Risks And Vulnerabilities Supplier Risk Management
Third Party Cybersecurity Risks And Vulnerabilities Supplier Risk ManagementThis slide showcases third party cybersecurity risks and vulnerabilities and their impact of functionality and operation. This template includes types such as data breaches, service disruption and compliance risk. Increase audience engagement and knowledge by dispensing information using Third Party Cybersecurity Risks And Vulnerabilities Supplier Risk Management. This template helps you present information on three stages. You can also present information on Data Breaches, Service Disruptions, Compliance Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How Incident Management Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
How Incident Management Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various ChatGPT use cases that can help organization in incident management and tackling cyber attacks. Its key elements are explore cyber attacks, decision support and post incident analysis Increase audience engagement and knowledge by dispensing information using How Incident Management Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on three stages. You can also present information on Explore Cyber Attacks, Decision Support, Post Incident Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 ChatGPT Opportunities For Vulnerability Assessment And Management Leveraging ChatGPT AI SS V
ChatGPT Opportunities For Vulnerability Assessment And Management Leveraging ChatGPT AI SS VIncrease audience engagement and knowledge by dispensing information using ChatGPT Opportunities For Vulnerability Assessment And Management Leveraging ChatGPT AI SS V This template helps you present information on Three stages. You can also present information on Security Tasks, Improved Efficiency, Identify New Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management Process
Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management ProcessThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Present the topic in a bit more detail with this Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Assets, Details, Comments. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process
Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management ProcessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Present the topic in a bit more detail with this Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Vulnerability, Threat, Threat Source. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Solutions To Overcome Challenges In Effective Vulnerability Management For SAP Systems
Solutions To Overcome Challenges In Effective Vulnerability Management For SAP SystemsThis slide depicts the resolutions to challenges in effective vulnerability management for SAP systems. The purpose of this template is to help the business ensure it can overcome these challenges through the use of given solutions. It includes challenges such as lack of resources and budgets, lack of visibility, etc. Introducing our Solutions To Overcome Challenges In Effective Vulnerability Management For SAP Systems set of slides. The topics discussed in these slides are Lack Of Resources And Budgets, Lack Of Visibility, Determining Start Point. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Network Vulnerabilities Management Key Metrics Dashboard Cybersecurity SS
Network Vulnerabilities Management Key Metrics Dashboard Cybersecurity SSThis dashboard tracks and manages the organizations network vulnerabilities. It includes KPIs such as data access vulnerabilities and exploitable vulnerabilities and a summary of vulnerabilities by severity.Deliver an outstanding presentation on the topic using this Network Vulnerabilities Management Key Metrics Dashboard Cybersecurity SS. Dispense information and present a thorough explanation of Unmitigated, Mitigated, Exploitable, Exploitable Hosts using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



