Powerpoint Templates and Google slides for Threats.
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Various types of workplace violence and threats corporate security management
Various types of workplace violence and threats corporate security managementThis slide provides details regarding various types of workplace violence threats created by people in terms of stalking, physical assault, harassment or intimidation, etc. Increase audience engagement and knowledge by dispensing information using Various Types Of Workplace Violence And Threats Corporate Security Management. This template helps you present information on six stages. You can also present information on Threatening Behavior, Physical Assault, Property Damage, Harassment And Intimidation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Physical security threats ppt powerpoint presentation outline templates cpb
Physical security threats ppt powerpoint presentation outline templates cpbPresenting Physical Security Threats Ppt Powerpoint Presentation Outline Templates Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Physical Security Threats. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Threat drivers and emerging managing cyber risk in a digital age
Threat drivers and emerging managing cyber risk in a digital ageMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security. Introducing Threat Drivers And Emerging Managing Cyber Risk In A Digital Age to increase your presentation threshold. Encompassed with threee stages, this template is a great option to educate and entice your audience. Dispence information on Internet Of Things, Artificial Intelligence, Human Machine Interface, using this template. Grab it now to reap its full benefits.
-
 Threat vulnerability asset matrix managing cyber risk in a digital age
Threat vulnerability asset matrix managing cyber risk in a digital ageMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Threat Vulnerability Asset Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ai based automation of cyber threat security controls
Ai based automation of cyber threat security controlsThe following slide highlights the threat security controls which are integrated with artificial intelligence which includes RPA and ML. Introducing our AI Based Automation Of Cyber Threat Security Controls set of slides. The topics discussed in these slides are Cyber Threat Security, Automated Control Management, Control And Vulnerability Reporting. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Comparison of cyber threat security vendors with pricing and use case
Comparison of cyber threat security vendors with pricing and use caseMentioned slide highlights the cyber threat security vendors with uses cases, metrics, intelligence , cyber security and pricing. Presenting our well structured Comparison Of Cyber Threat Security Vendors With Pricing And Use Case. The topics discussed in this slide are Financial Services, Cyber Security, Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber security risk management framework for threat protection
Cyber security risk management framework for threat protectionThis slide highlights the cyber security risk management framework which include third party risk management, IT risk assessment and security center operations. Presenting our set of slides with Cyber Security Risk Management Framework For Threat Protection. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Governance, Security Assessment, Independent Audit.
-
 Cyber security threat management system
Cyber security threat management systemThe following slide illustrates the cyber security threat management system which includes threat containment, logging and traceability management. Introducing our Cyber Security Threat Management System set of slides. The topics discussed in these slides are Threat Containment And Remediation, Identify Management, Application Visibility And Control. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber threat approaches for security protection
Cyber threat approaches for security protectionThe following slide highlights the cyber threat approaches which include traditional and artificial intelligence based approaches to counter threats. Presenting our well structured Cyber Threat Approaches For Security Protection. The topics discussed in this slide are Cybersecurity Threat, Social Engineering, Traditional Approach. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber threat hunting program with process and tools
Cyber threat hunting program with process and toolsThe following slide highlights the cyber threat hunting program including people, process and with four different levels to minimize risks and threats. Introducing our Cyber Threat Hunting Program With Process And Tools set of slides. The topics discussed in these slides are Cyber Threat Hunting, Cyber Security Tool, Cyber Threat Training. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber threat icon indicating malware attack
Cyber threat icon indicating malware attackIntroducing our premium set of slides with Cyber Threat Icon Indicating Malware Attack. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Icon Indicating Malware Attack. So download instantly and tailor it with your information.
-
 Cyber threat intelligence services for enterprise security
Cyber threat intelligence services for enterprise securityThis slide highlights the services of cyber threat intelligence with incident management, cyber analytics, and vulnerability management and infrastructure management. Presenting our set of slides with Cyber Threat Intelligence Services For Enterprise Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Infrastructure Management, Vulnerability Management, Cyber Analytics.
-
 Cyber threat report with risk indicator and affected systems
Cyber threat report with risk indicator and affected systemsPresenting our well structured Cyber Threat Report With Risk Indicator And Affected Systems. The topics discussed in this slide are Risk Level, Risk Indication, Potential Affected Systems. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber threat security company users and protection
Cyber threat security company users and protectionThe following slide highlights the cyber threat security companies with its users retailers, BFSI, large scale enterprises, protection and pricing. Introducing our Cyber Threat Security Company Users And Protection set of slides. The topics discussed in these slides are Pricing, Company, Users. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber threat security icon to capture sensitive information
Cyber threat security icon to capture sensitive informationIntroducing our premium set of slides with Cyber Threat Security Icon To Capture Sensitive Information. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Security Icon To Capture Sensitive Information. So download instantly and tailor it with your information.
-
 Cyber threat security maturity model with protection levels
Cyber threat security maturity model with protection levelsThe following slide illustrates the model of cyber threat security which includes secure, defend, contain, monitor and manage levels. Presenting our well structured Cyber Threat Security Maturity Model With Protection Levels. The topics discussed in this slide are Security Management Technology, Threat Management Platform, Threat Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber threat security planning process with risk tolerance and threats
Cyber threat security planning process with risk tolerance and threatsThis following slide illustrates the cyber security threat program planning which include steps like identify key personnel, risk tolerance strategy and developing frequency. Presenting our set of slides with Cyber Threat Security Planning Process With Risk Tolerance And Threats. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Built Risk Tolerance, Identify And Document, Establish Governance.
-
 Cyber threat security planning with educate and retest stage
Cyber threat security planning with educate and retest stageThe following slide highlights the cyber threat security planning to minimize threats in organizations. It include six stages to deploy cyber threat to organization. Introducing our premium set of slides with Cyber Threat Security Planning With Educate And Retest Stage. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Deploy, Retest, Educate. So download instantly and tailor it with your information.
-
 Cyber threat strategies for security protection
Cyber threat strategies for security protectionThis slide highlights the cyber threat strategies that include risk assessment, phishing program, software protocols and end point protection. Presenting our set of slides with Cyber Threat Strategies For Security Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Program, Software Protocols, End Point Protection.
-
 Key cyber security threat to organizations
Key cyber security threat to organizationsThis slide displays different types of cyber security threats which impacts organization negatively. It include malware, emotet, phishing and SQL injection. Introducing our premium set of slides with Key Cyber Security Threat To Organizations. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Malware, Phishing, SQL Injection. So download instantly and tailor it with your information.
-
 Roadmap for developing cyber threat program
Roadmap for developing cyber threat programThe following slide highlights the cyber threat security roadmap which include three phases for managing the threats in organization. Presenting our set of slides with Roadmap For Developing Cyber Threat Program. This exhibits information on nine stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implement And Integrate, Risk Assessment, Identify Vulnerabilities.
-
 Validated online lifecycle threat ppt powerpoint presentation inspiration portfolio cpb
Validated online lifecycle threat ppt powerpoint presentation inspiration portfolio cpbPresenting our Validated Online Lifecycle Threat Ppt Powerpoint Presentation Inspiration Portfolio Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Validated Online Lifecycle Threat. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Weakness threat difference ppt powerpoint presentation layouts ideas cpb
Weakness threat difference ppt powerpoint presentation layouts ideas cpbPresenting our Weakness Threat Difference Ppt Powerpoint Presentation Layouts Ideas Cpb PowerPoint template design. This PowerPoint slide showcases nine stages. It is useful to share insightful information on Weakness Threat Difference . This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence Framework
Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence FrameworkThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations.Present the topic in a bit more detail with this Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence Framework Use it as a tool for discussion and navigation on Local Area Network, Mainframe Systems, Distributes Systems This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 How Firm Handle Various Insider Threats At Workplace Enabling It Intelligence Framework
How Firm Handle Various Insider Threats At Workplace Enabling It Intelligence FrameworkThis slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc.Introducing How Firm Handle Various Insider Threats At Workplace Enabling It Intelligence Framework to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Employee Training, Develop Threat Hunting Team, Implement User Behavioral Analytics using this template. Grab it now to reap its full benefits.
-
 Risk Based Methodology To Cyber Threat Drivers And Emerging Technologies Impact On Cyber Security
Risk Based Methodology To Cyber Threat Drivers And Emerging Technologies Impact On Cyber SecurityMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security.Increase audience engagement and knowledge by dispensing information using Risk Based Methodology To Cyber Risk Based Methodology To Cyber Threat Drivers And Emerging Technologies Impact On Cyber Security security This template helps you present information on one stage. You can also present information on Artificial Intelligence, Human Machine Interface, Internet Of Things using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Online Threats Drawbacks Ppt Powerpoint Presentation Show Graphics Example Cpb
Online Threats Drawbacks Ppt Powerpoint Presentation Show Graphics Example CpbPresenting Online Threats Drawbacks Ppt Powerpoint Presentation Show Graphics Example Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Online Threats Drawbacks. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Security threat assessment ppt powerpoint presentation diagram ppt cpb
Security threat assessment ppt powerpoint presentation diagram ppt cpbPresenting Security Threat Assessment Ppt Powerpoint Presentation Diagram Ppt Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Threat Assessment. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Risk threat vulnerability ppt powerpoint presentation portfolio graphics design cpb
Risk threat vulnerability ppt powerpoint presentation portfolio graphics design cpbPresenting our Risk Threat Vulnerability Ppt Powerpoint Presentation Portfolio Graphics Design Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Risk Threat Vulnerability. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Management threats ppt powerpoint presentation pictures clipart cpb
Management threats ppt powerpoint presentation pictures clipart cpbPresenting our Management Threats Ppt Powerpoint Presentation Pictures Clipart Cpb PowerPoint template design. This PowerPoint slide showcases seven stages. It is useful to share insightful information on Management Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Environmental management issues pharmaceutical company pharmaceutical company swot analysis threats
Environmental management issues pharmaceutical company pharmaceutical company swot analysis threatsThis slide shows the various threats related to pharmaceutical company such as high level of competition, suppliers, regulations on international trade and many more. Introducing Environmental Management Issues Pharmaceutical Company Pharmaceutical Company Swot Analysis Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Pharmaceutical, Analysis, Threats, using this template. Grab it now to reap its full benefits.
-
 Cyberterrorism it checklist to deal with cyber terrorism threats ppt slides templates
Cyberterrorism it checklist to deal with cyber terrorism threats ppt slides templatesThis slide represents the checklist to deal with cyber terrorism threats which involve 24 7 monitoring, employee training, keeping software updated. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Checklist To Deal With Cyber Terrorism Threats Ppt Slides Templates. This template helps you present information on one stages. You can also present information on Incident Response Plan, Limited Access Privileges, Evaluating Risk Third Party Vendor, Cyber Security Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Critical security threats ppt powerpoint presentation model mockup cpb
Critical security threats ppt powerpoint presentation model mockup cpbPresenting our Critical Security Threats Ppt Powerpoint Presentation Model Mockup Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Critical Security Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Real time analysis of security alerts threat intelligence services
Real time analysis of security alerts threat intelligence servicesThis slide covers the threat intelligence services such as global intelligence, local intelligence, and other effective threat detection services. Increase audience engagement and knowledge by dispensing information using Real Time Analysis Of Security Alerts Threat Intelligence Services. This template helps you present information on three stages. You can also present information on Global Intelligence, Local Intelligence, Other Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Successful siem strategies for audit and compliance threat intelligence services
Successful siem strategies for audit and compliance threat intelligence servicesThis slide covers the threat intelligence services such as global intelligence, local intelligence, and other effective threat detection services. Increase audience engagement and knowledge by dispensing information using Successful Siem Strategies For Audit And Compliance Threat Intelligence Services. This template helps you present information on three stages. You can also present information on Local Intelligence, Global Intelligence, Other Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Internet Threats Cybercrime Ppt Powerpoint Presentation Pictures Cpb
Internet Threats Cybercrime Ppt Powerpoint Presentation Pictures CpbPresenting Internet Threats Cybercrime Ppt Powerpoint Presentation Pictures Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Internet Threats Cybercrime. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Threat Mitigation Plan Ppt Powerpoint Presentation File Templates Cpb
Threat Mitigation Plan Ppt Powerpoint Presentation File Templates CpbPresenting Threat Mitigation Plan Ppt Powerpoint Presentation File Templates Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Threat Mitigation Plan. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Digital Transformation In A Banking Financial Analysis Threats Related To The Banking Company
Digital Transformation In A Banking Financial Analysis Threats Related To The Banking CompanyThis slides shows the various threats related to the banking company which includes legal and political framework, high competition, etc. Introducing Digital Transformation In A Banking Financial Analysis Threats Related To The Banking Company to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Political Framework, High Competition, Developing Economies, using this template. Grab it now to reap its full benefits.
-
 Agenda for advanced security monitoring plan to remove cybersecurity threat and data infraction
Agenda for advanced security monitoring plan to remove cybersecurity threat and data infractionIncrease audience engagement and knowledge by dispensing information using Agenda For Advanced Security Monitoring Plan To Remove Cybersecurity Threat And Data Infraction. This template helps you present information on seven stages. You can also present information on Agenda using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons slide for advanced security monitoring plan to remove cybersecurity threat and data infraction
Icons slide for advanced security monitoring plan to remove cybersecurity threat and data infractionIntroducing our well researched set of slides titled Icons Slide For Advanced Security Monitoring Plan To Remove Cybersecurity Threat And Data Infraction. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Table of contents advanced security monitoring plan to remove cybersecurity threat and data infraction
Table of contents advanced security monitoring plan to remove cybersecurity threat and data infractionPresent the topic in a bit more detail with this Table Of Contents Advanced Security Monitoring Plan To Remove Cybersecurity Threat And Data Infraction. Use it as a tool for discussion and navigation on Cybersecurity Monitoring Tools To Be Implemented, Essential Elements Of Security Monitoring Plan, Cybersecurity Monitoring Best Practices To Be Followed By The Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Common Methods Used To Threaten Information Security
Information Security Common Methods Used To Threaten Information SecurityThis slide depicts the standard methods used to threaten cyber-security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Deliver an outstanding presentation on the topic using this Information Security Common Methods Used To Threaten Information Security. Dispense information and present a thorough explanation of Information, Security, Common using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Cyber Threat Landscape In Information Security
Information Security Cyber Threat Landscape In Information SecurityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Present the topic in a bit more detail with this Information Security Cyber Threat Landscape In Information Security. Use it as a tool for discussion and navigation on Landscape, Information, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Latest Threats In Information Security
Information Security Latest Threats In Information SecurityThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Introducing Information Security Latest Threats In Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Latest Threats In Information Security, using this template. Grab it now to reap its full benefits.
-
 Types Of Threats In Information Security
Types Of Threats In Information SecurityThis slide depicts the main types of threats in cyber security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Increase audience engagement and knowledge by dispensing information using Types Of Threats In Information Security. This template helps you present information on three stages. You can also present information on Cyber Crime, Cyber Terrorism, Cyber Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix
Information Security Program Cybersecurity Management Threat Vulnerability Asset MatrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat Drivers And Emerging Technologies Impact On Cyber Security
Threat Drivers And Emerging Technologies Impact On Cyber SecurityMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security. Increase audience engagement and knowledge by dispensing information using Threat Drivers And Emerging Technologies Impact On Cyber Security. This template helps you present information on four stages. You can also present information on Infrastructure, Artificial Intelligence, Technologies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risk Management Framework For Information Security Threat Identification And Vulnerability
Risk Management Framework For Information Security Threat Identification And VulnerabilityFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security Threat Identification And Vulnerability. Dispense information and present a thorough explanation of Communication And Network, Database, Failure To Segment Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cybersecurity Risk Management Framework Mitigation Plan For Resolving Encountered Threat
Cybersecurity Risk Management Framework Mitigation Plan For Resolving Encountered ThreatMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Mitigation Plan For Resolving Encountered Threat. Dispense information and present a thorough explanation of Security Breach, Data Backup Team, Asset Manager, Operational Downtime using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
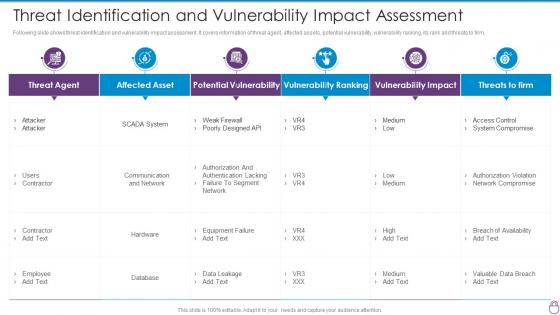 Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact
Cybersecurity Risk Management Framework Threat Identification And Vulnerability ImpactFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact. Dispense information and present a thorough explanation of Threat Agent, Affected Asset, Potential Vulnerability, Vulnerability Ranking, Vulnerability Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SWOT Analysis Threats Related To The Banking Company Digitalization In Retail Banking Company
SWOT Analysis Threats Related To The Banking Company Digitalization In Retail Banking CompanyThis slides shows the various threats related to the banking company which includes legal and political framework, high competition, etc.Increase audience engagement and knowledge by dispensing information using SWOT Analysis Threats Related To The Banking Company Digitalization In Retail Banking Company This template helps you present information on four stages. You can also present information on Legal And Political Framework, High Competition, Risks Impacting Developing Economies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber
Threat Vulnerability Asset Matrix Risk Based Methodology To CyberMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Social Engineering, Ranked Critical Resources, Present IT Safeguards This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber Security
Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber SecurityMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security.Increase audience engagement and knowledge by dispensing information using Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber Security This template helps you present information on one stage. You can also present information on Internet Of Things, Artificial Intelligence, Human Machine Interface using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security
Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber SecurityMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on System Redundancy, Incident Response Plan, Security Policy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Contingency Plan For Threat Handling In Building Business Analytics Architecture
Contingency Plan For Threat Handling In Building Business Analytics ArchitectureThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Present the topic in a bit more detail with this Contingency Plan For Threat Handling In Building Business Analytics Architecture. Use it as a tool for discussion and navigation on Contingency Solutions, Contingency Considerations, Local Area Network, Wide Area Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 How Firm Handle Various Insider Threats At Workplace Building Business Analytics Architecture
How Firm Handle Various Insider Threats At Workplace Building Business Analytics ArchitectureThis slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc. Increase audience engagement and knowledge by dispensing information using How Firm Handle Various Insider Threats At Workplace Building Business Analytics Architecture. This template helps you present information on two stages. You can also present information on Employee Training, IT Security And HR Coordination, Develop Threat Hunting Team, Implement User Behavioral Analytics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementation Latest Technologies SWOT Analysis Threats Related Banking Company
Implementation Latest Technologies SWOT Analysis Threats Related Banking CompanyThis slides shows the various threats related to the banking company which includes legal and political framework, high competition, etc. Introducing Implementation Latest Technologies SWOT Analysis Threats Related Banking Company to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Legal And Political Framework, High Competition, Impacting Developing Economies, Threat, using this template. Grab it now to reap its full benefits.
-
 Unlocking Business Infrastructure Capabilities Contingency Plan For Threat Handling In Security Centre
Unlocking Business Infrastructure Capabilities Contingency Plan For Threat Handling In Security CentreThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an outstanding presentation on the topic using this Unlocking Business Infrastructure Capabilities Contingency Plan For Threat Handling In Security Centre. Dispense information and present a thorough explanation of Contingency Plan For Threat Handling In Security Centre using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Unlocking Business Infrastructure Capabilities How Firm Handle Various Insider Threats At Workplace
Unlocking Business Infrastructure Capabilities How Firm Handle Various Insider Threats At WorkplaceThis slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc. Present the topic in a bit more detail with this Unlocking Business Infrastructure Capabilities How Firm Handle Various Insider Threats At Workplace. Use it as a tool for discussion and navigation on Coordination, Workplace, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing various ways to handle insider cyber threat management for organization critical
Addressing various ways to handle insider cyber threat management for organization criticalThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Introducing Addressing Various Ways To Handle Insider Cyber Threat Management For Organization Critical to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Periodic Risk Assessment, Networks And Individuals, Amount Of Privilege, using this template. Grab it now to reap its full benefits.





