Powerpoint Templates and Google slides for Security Process
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Billing customer security e source control circular process with icon in centre
Billing customer security e source control circular process with icon in centrePresenting billing customer security e source control circular process with icon in centre. This is a billing customer security e source control circular process with icon in centre. This is a seven stage process. The stages in this process are billing process, billing procedure, billing cycle.
-
 Operating system memory process management security
Operating system memory process management securityPresenting this Operating System Memory Process Management Security PowerPoint presentation. Add charts and graphs for a wonderful representation of information. The PPT also supports the standard (4:3) and widescreen (16:9) aspect ratios. It is compatible with Google Slides. Convert this into popular images or document formats such as JPEG, PNG or PDF. High-quality graphics ensure that graphics quality is maintained at every stage of presentation.
-
 Process integration oversight security policy management corporate strategic plan
Process integration oversight security policy management corporate strategic planPresenting this set of slides with name - Process Integration Oversight Security Policy Management Corporate Strategic Plan. This is an editable three stages graphic that deals with topics like Process Integration Oversight, Security Policy Management, Corporate Strategic Plan to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Latest cyber security technology ppt powerpoint presentation gallery rules cpb
Latest cyber security technology ppt powerpoint presentation gallery rules cpbPresenting this set of slides with name Latest Cyber Security Technology Ppt Powerpoint Presentation Gallery Rules Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Latest Cyber Security Technology to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Investment process security analysis ppt powerpoint presentation icon background images cpb
Investment process security analysis ppt powerpoint presentation icon background images cpbPresenting this set of slides with name Investment Process Security Analysis Ppt Powerpoint Presentation Icon Background Images Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Investment Process Security Analysis to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Physical security management protocol ppt powerpoint presentation infographic cpb
Physical security management protocol ppt powerpoint presentation infographic cpbPresenting this set of slides with name Physical Security Management Protocol Ppt Powerpoint Presentation Infographic Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Physical Security Management Protocol to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Encryption security ppt powerpoint presentation icon rules cpb
Encryption security ppt powerpoint presentation icon rules cpbPresenting this set of slides with name Encryption Security Ppt Powerpoint Presentation Icon Rules Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Encryption Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information security risk assessment process ppt powerpoint presentation shapes cpb
Information security risk assessment process ppt powerpoint presentation shapes cpbPresenting this set of slides with name Information Security Risk Assessment Process Ppt Powerpoint Presentation Shapes Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Information Security Risk Assessment Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security essentials ppt powerpoint presentation model rules cpb
Cyber security essentials ppt powerpoint presentation model rules cpbPresenting this set of slides with name Cyber Security Essentials Ppt Powerpoint Presentation Model Rules Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Cyber Security Essentials to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information security management process ppt powerpoint presentation model cpb
Information security management process ppt powerpoint presentation model cpbPresenting this set of slides with name Information Security Management Process Ppt Powerpoint Presentation Model Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Information Security Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security people process technology ppt powerpoint presentation file graphics template cpb
Cyber security people process technology ppt powerpoint presentation file graphics template cpbPresenting this set of slides with name Cyber Security People Process Technology Ppt Powerpoint Presentation File Graphics Template Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Cyber Security People Process Technology to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security people process technology framework
Cyber security people process technology frameworkPresenting this set of slides with name Cyber Security People Process Technology Framework. This is a six stage process. The stages in this process are Information Risk Management, Incident Response And Forensic Investigation, Architecture, Applications And Network Security, Threat And Vulnerability Assessment, Compliance And Awareness, Security Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Security problems cloud computing ppt powerpoint presentation gallery rules cpb
Security problems cloud computing ppt powerpoint presentation gallery rules cpbPresenting this set of slides with name Security Problems Cloud Computing Ppt Powerpoint Presentation Gallery Rules Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Security Problems Cloud Computing to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Itil security management process ppt powerpoint presentation visual aids slides cpb
Itil security management process ppt powerpoint presentation visual aids slides cpbPresenting this set of slides with name ITIL Security Management Process Ppt Powerpoint Presentation Visual Aids Slides Cpb. This is an editable Powerpoint three stages graphic that deals with topics like ITIL Security Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Process flow for cyber security service ppt powerpoint presentation files
Process flow for cyber security service ppt powerpoint presentation filesPresenting this set of slides with name Process Flow For Cyber Security Service Ppt Powerpoint Presentation Files. This is a three stage process. The stages in this process are Project Kickoff, Planning, Development And Implementation, Maintain And Train. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Security management process standard ppt powerpoint presentation summary cpb
Security management process standard ppt powerpoint presentation summary cpbPresenting this set of slides with name Security Management Process Standard Ppt Powerpoint Presentation Summary Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Security Management Process Standard to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Process flow for company online database security ppt gallery
Process flow for company online database security ppt galleryPresenting this set of slides with name Process Flow For Company Online Database Security Ppt Gallery. This is a four stage process. The stages in this process are Project Kickoff, Planning, Development And Implementation, Maintain And Train. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Application security management process ppt powerpoint graphics tutorials cpb
Application security management process ppt powerpoint graphics tutorials cpbPresenting this set of slides with name Application Security Management Process Ppt Powerpoint Graphics Tutorials Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Application Security Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Process flow for enterprise cyber safety and security services ppt gallery
Process flow for enterprise cyber safety and security services ppt galleryPresenting this set of slides with name Process Flow For Enterprise Cyber Safety And Security Services Ppt Gallery. This is a four stage process. The stages in this process are Project Kickoff, Planning, Development And Implementation, Maintain And Train. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cyber security process with identify and react
Cyber security process with identify and reactPresenting this set of slides with name Cyber Security Process With Identify And React. This is a four stage process. The stages in this process are Identify, Protect, Detect, React. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Multistep process for continuous system security
Multistep process for continuous system securityPresenting this set of slides with name Multistep Process For Continuous System Security. This is a four stage process. The stages in this process are Predict, Prevent, Detect, Respond. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Security implementation process with strategize and plan
Security implementation process with strategize and planPresenting this set of slides with name Security Implementation Process With Strategize And Plan. This is a three stage process. The stages in this process are Assess And Learn, Strategize And Plan, Implement And Support. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Step 1 2 3 of network security process
Step 1 2 3 of network security processPresenting our set of slides with name Step 1 2 3 Of Network Security Process. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Step 1 2 3 Network, Security, Process.
-
 Security incident management process ppt powerpoint presentation visual aids styles cpb
Security incident management process ppt powerpoint presentation visual aids styles cpbPresenting our Security Incident Management Process Ppt Powerpoint Presentation Visual Aids Styles Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Security Incident Management Process This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Four Step Process Of Security Automation System
Four Step Process Of Security Automation SystemThe following slide highlights multistep process of security automation. The company can detect security breach after following steps such as investigating the steps of IT analyst, determining responsive action, eradication and closing the ticked Presenting our set of slides with name Four Step Process Of Security Automation System. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Investigating Steps, Security Analysts, Eradication.
-
 Multistep Process For Automating Cloud Security Operations
Multistep Process For Automating Cloud Security OperationsThe following slide highlights four step process of cloud security automation. The various steps are container configure management, using infrastructure as code, automating asset tagging and vulnerability scanning where security analysts should implement automation. Introducing our premium set of slides with Multistep Process For Automating Cloud Security Operations. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Container Configure Management, Infrastructure As Code, Vulnerability Scanning. So download instantly and tailor it with your information.
-
 Bank Frauds Prevention Process With Cyber Security Program
Bank Frauds Prevention Process With Cyber Security ProgramThe slide illustrates a banking frauds mitigation process for client to reduce and prevent issues. Its key steps are establish governance structure, define culture shift, introduce staff training, improve payment process, implement technology controls and harden human firewall. Introducing our premium set of slides with Bank Frauds Prevention Process With Cyber Security Program. Elucidate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Introduce Staff Training, Implement Technology Controls, Improve Payment Process, Harden Human Firewall. So download instantly and tailor it with your information.
-
 Process Of Secure Reverse Proxying Reverse Proxy Load Balancer Ppt Formats
Process Of Secure Reverse Proxying Reverse Proxy Load Balancer Ppt FormatsThis slide depicts secure reverse proxying and how it can be established in three ways such as secure client to the proxy, secure proxy to the content server, and the secure client to proxy and secure proxy to a content server. Introducing Process Of Secure Reverse Proxying Reverse Proxy Load Balancer Ppt Formats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Secure Reverse, Proxy Server, Process, using this template. Grab it now to reap its full benefits.
-
 Business Security Management Four Stage Process
Business Security Management Four Stage ProcessThe purpose of this slide is to outline the risk management procedures in a business organization and to provide desired solutions. This includes four steps- monitor, identify, evaluate and treat. Presenting our set of slides with name Business Security Management Four Stage Process. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Evaluate, Treat, Monitor.
-
 Canva Security Processes And Systems Canva Company Profile Ppt Summary Graphics Tutorials
Canva Security Processes And Systems Canva Company Profile Ppt Summary Graphics TutorialsThis slide highlights the Canva security systems encryption, data security, attack, monitoring, staged releases, secure development, account safety and in app permissions. Introducing Canva Security Processes And Systems Canva Company Profile Ppt Summary Graphics Tutorials to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Secure Development, Monitoring, Data Security, using this template. Grab it now to reap its full benefits.
-
 Problem Management Process For Enhancing Cyber Security
Problem Management Process For Enhancing Cyber SecurityThis slide signifies increasing cyber security and IT through problem management process. It includes stages like detection, define, investigate, identify resolutions, implement and follow up Introducing our premium set of slides with Problem Management Process For Enhancing Cyber Security. Elucidate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Problem Detection, Define, Investigate, Identify Resolutions, Implement. So download instantly and tailor it with your information.
-
 Incident Management Process In Cyber Security
Incident Management Process In Cyber SecurityThis slide covers incident management process in cyber security. It involves steps such as engage team, identify incidents, assessment, investigation and documentation. Presenting our set of slides with name Incident Management Process In Cyber Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Incident Response Team, Monitoring And Evaluation, Investigation Or Resolving.
-
 Key Steps Cyber Security Incident Response Plan Process
Key Steps Cyber Security Incident Response Plan ProcessThis slide covers key steps cyber incident response plan process. It involves six stages such as preparation, detection, analysis, containment, eradication and recovery. Presenting our set of slides with name Key Steps Cyber Security Incident Response Plan Process. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Preparation, Detection, Containment, Eradication.
-
 Security Processes That Cant Be Automated Security Automation To Investigate And Remediate Cyberthreats
Security Processes That Cant Be Automated Security Automation To Investigate And Remediate CyberthreatsThe following slide highlights the three processes of the security which cannot be automated which includes threat modeling, penetration testing and bug bounty program. Introducing Security Processes That Cant Be Automated Security Automation To Investigate And Remediate Cyberthreats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Modeling, Penetration Testing, Bug Bounty , using this template. Grab it now to reap its full benefits.
-
 Why To Automate The It Security Process Security Automation To Investigate And Remediate Cyberthreats
Why To Automate The It Security Process Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Introducing Why To Automate The It Security Process Security Automation To Investigate And Remediate Cyberthreats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Better Threat Detection, Faster Containment, Improve Productivity, using this template. Grab it now to reap its full benefits.
-
 Security Automation Integrates Tools Systems And Processes Security Automation In Information Technology
Security Automation Integrates Tools Systems And Processes Security Automation In Information TechnologyThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Increase audience engagement and knowledge by dispensing information using Security Automation Integrates Tools Systems And Processes Security Automation In Information Technology. This template helps you present information on eight stages. You can also present information on Automation, Integrates, Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
 Why To Automate The It Security Process Security Automation In Information Technology
Why To Automate The It Security Process Security Automation In Information TechnologyThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Security Automation In Information Technology. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Reverse Proxy Server Process Of Secure Reverse Proxying Ppt Powerpoint Presentation Infographic Template Ideas
Reverse Proxy Server Process Of Secure Reverse Proxying Ppt Powerpoint Presentation Infographic Template IdeasThis slide depicts secure reverse proxying and how it can be established in three ways such as secure client to the proxy, secure proxy to the content server, and the secure client to proxy and secure proxy to a content server. Introducing Reverse Proxy Server Process Of Secure Reverse Proxying Ppt Powerpoint Presentation Infographic Template Ideas to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Secure Reverse Proxying, Safe Data Transmission, Secure Sockets, using this template. Grab it now to reap its full benefits.
-
 Why To Automate The It Security Process Enabling Automation In Cyber Security Operations
Why To Automate The It Security Process Enabling Automation In Cyber Security OperationsThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Enabling Automation In Cyber Security Operations. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Protocols In Powerpoint And Google Slides Cpb
Cyber Security Protocols In Powerpoint And Google Slides CpbPresenting our Cyber Security Protocols In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases nine stages. It is useful to share insightful information on Cyber Security Protocols This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Data Security Risk Management Response Process
Cyber Data Security Risk Management Response ProcessThis slide covers process to respond towards cyber data security risk. It includes steps such as preparation of incident response plan, detection of data compromises, analyse use of malicious tools, eradicate network threats, data recovery as the final step. Presenting our set of slides with name Cyber Data Security Risk Management Response Process. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Threats, Compromised Data, Data Compromises.
-
 Four Steps Of Cyber Security Data Breach Risk Process
Four Steps Of Cyber Security Data Breach Risk ProcessThis slide covers steps utilised to breach data. It includes stages such as probing, performing initial attack, expansion of attacks and data lifting. Introducing our premium set of slides with name Four Steps Of Cyber Security Data Breach Risk Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Initial Attack, Expanded Attack, Breach Risk Process. So download instantly and tailor it with your information.
-
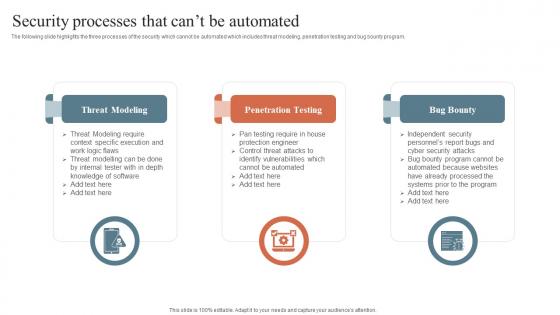 Security Processes That Cant Be Automated Security Orchestration Automation And Response Guide
Security Processes That Cant Be Automated Security Orchestration Automation And Response GuideThe following slide highlights the three processes of the security which cannot be automated which includes threat modeling, penetration testing and bug bounty program. Introducing Security Processes That Cant Be Automated Security Orchestration Automation And Response Guide to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Modeling, Penetration Testing, Bug Bounty, using this template. Grab it now to reap its full benefits.
-
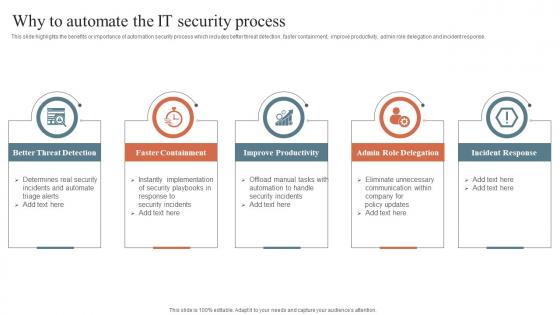 Why To Automate The It Security Process Security Orchestration Automation And Response Guide
Why To Automate The It Security Process Security Orchestration Automation And Response GuideThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Security Orchestration Automation And Response Guide. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Threat Modeling Process For Secure Data Assets
Threat Modeling Process For Secure Data AssetsThis slide shows threat modeling to protect business assets from risks. It contains two phases discovery and implementation that includes steps such as identify assets, analyze attack surface, attack vectors, analyze, prioritize and develop controls. Introducing our premium set of slides with name Threat Modeling Process For Secure Data Assets. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Hackers Path, Identified Assets, Threat Routes. So download instantly and tailor it with your information.
-
 Threat Modelling Process Of Cyber Security Program
Threat Modelling Process Of Cyber Security ProgramThis slide shows threat modelling process to identify gaps and improve efficiency of cyber security program. It contains five steps select digital asset, identify attack scenarios, evaluate existing controls, assess residual risks and construct business case. Presenting our set of slides with name Threat Modelling Process Of Cyber Security Program. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Threat Modelling, Cyber Security, Assess Residual Risk .
-
 Robotic Process Automation Security Steps
Robotic Process Automation Security StepsThis slide exhibits steps to ensure robotic process automation protection to prevent data leakage and fraud. It includes four steps ensure bot actions accountability, avoid fraud, protect log integrity and enable secure development. Presenting our set of slides with name Robotic Process Automation Security Steps. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Bot Actions Accountability, Avoid Fraud And Errors, Secure Log Integrity.
-
 Process For Information Security Risk Assessment Information System Security And Risk Administration Plan
Process For Information Security Risk Assessment Information System Security And Risk Administration PlanThis slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets. Increase audience engagement and knowledge by dispensing information using Process For Information Security Risk Assessment Information System Security And Risk Administration Plan. This template helps you present information on four stages. You can also present information on Security Threats, Information Assets, Risk Associated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Transformation Process Flow
Cyber Security Transformation Process FlowThis slide provides a cyber security process for transformation of business operations which can be used by managers for risk mitigation by resolving security issues. The steps relate to assessment of current cyber security posture, set objectives, implement strategies, train employees etc. Introducing our premium set of slides with Cyber Security Transformation Process Flow. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Set Objectives, Implement Strategies, Train Employees. So download instantly and tailor it with your information.
-
 Cyber Security Incident Response Process
Cyber Security Incident Response ProcessThis slide covers procedure of cyber security incident response. The purpose of this process is to examine the cyber threat and try to find the ways to mitigate the risk. It includes four steps such as identification and detection, containment, eradication and recovery and post recovery.Introducing our premium set of slides with Cyber Security Incident Response Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identification Detection, Eradication Recovery, Incident Manager. So download instantly and tailor it with your information.
-
 RPA Discovery Process Security Steps
RPA Discovery Process Security StepsFollowing slide exhibits steps for robotic process automation security. Purpose of this slide is to use business automation efficiently that prevents data leakage and fraud. It includes pointers such as bot actions accountability, avoid fraud, secure log integrity etc. Introducing our premium set of slides with RPA Discovery Process Security Steps. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Technical And Automations Tools, Analysis Structure, RPA Development. So download instantly and tailor it with your information.
-
 Blockchain Technology For Efficient Security Initiatives Protecting Recruitment Process
Blockchain Technology For Efficient Security Initiatives Protecting Recruitment ProcessThis slide showcases security initiatives which can help recruiters protect their sensitive information. It provides details about record keeping, secured storage, verification, decentralized info, etc. Increase audience engagement and knowledge by dispensing information using Blockchain Technology For Efficient Security Initiatives Protecting Recruitment Process. This template helps you present information on four stages. You can also present information on Candidate Information, Decentralized Job Listing, Candidate Qualifications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
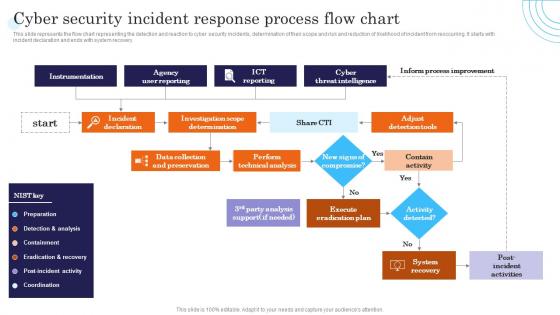 Cyber Security Incident Response Process Flow Chart Incident Response Strategies Deployment
Cyber Security Incident Response Process Flow Chart Incident Response Strategies DeploymentThis slide represents the flow chart representing the detection and reaction to cyber security incidents, determination of their scope and risk and reduction of likelihood of incident from reoccurring. It starts with incident declaration and ends with system recovery. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Response Process Flow Chart Incident Response Strategies Deployment. This template helps you present information on one stages. You can also present information on Instrumentation, Agency, Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Policy What Happens In The Absence Of It Policies And Procedures
Cyber Security Policy What Happens In The Absence Of It Policies And ProceduresThis slide represents the consequences of not having IT policies and procedures. Effects include disrupted and inconsistent operational duties, communication gaps between staff and employees, etc. Introducing Cyber Security Policy What Happens In The Absence Of It Policies And Procedures to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Procedures, Information, Corporations, using this template. Grab it now to reap its full benefits.
-
 SDN Security IT Implementation Process Of Software Defined Networking SDN
SDN Security IT Implementation Process Of Software Defined Networking SDNThis slide outlines the implementation process of software defined networking that includes creating a use case, forming a multi functional team, testing, and reviewing. The main implementation types of SDN are open SDN, SDN via APIs, and SDN via hypervisor based overlay network. Increase audience engagement and knowledge by dispensing information using SDN Security IT Implementation Process Of Software Defined Networking SDN. This template helps you present information on four stages. You can also present information on Process, Implementation, Software using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Photo Editing Company Profile Canva Security Processes And Systems CP SS V
Photo Editing Company Profile Canva Security Processes And Systems CP SS VThis slide highlights the Canva security systems encryption, data security, attack, monitoring, staged releases, secure development, account safety and in app permissions. Introducing Photo Editing Company Profile Canva Security Processes And Systems CP SS V to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Encryption, Processes, Systems, using this template. Grab it now to reap its full benefits.
-
 Process To Formulate Cyber Security Communication Plan
Process To Formulate Cyber Security Communication PlanThis slide provides information to develop a cyber security communication plan effectively and efficiently. It includes elements such as formulate committee, identify scenarios, draft statement, rehearse plan and regulatory compliance. Introducing our premium set of slides with Process To Formulate Cyber Security Communication Plan Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Formulate Committee, Draft Statement, Rehearse, Plan, Regulatory Compliance So download instantly and tailor it with your information.
-
 Security Process In Powerpoint And Google Slides Cpb
Security Process In Powerpoint And Google Slides CpbPresenting our Security Process In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Security Process. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Action Plan Process
Cyber Security Action Plan ProcessThis slide illustrates action plan process of cyber security. It further consists steps such as system hygiene, plan development, create risk profile, evaluate and measure, minimize risk, cyber insurance, etc Introducing our premium set of slides with Cyber Security Action Plan Process. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Action, Security, Process. So download instantly and tailor it with your information.
-
 Supply Chain Security Risk Management Process
Supply Chain Security Risk Management ProcessThis slide showcases process that can help organization to manage supply chain security risks. Its key steps are document risks, develop framework, monitor risk and regular review. Introducing our premium set of slides with Supply Chain Security Risk Management Process Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Document Risks, Develop Framework. So download instantly and tailor it with your information.




