Powerpoint Templates and Google slides for Security Process
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Process security agency ppt powerpoint presentation icon professional cpb
Process security agency ppt powerpoint presentation icon professional cpbPresenting Process Security Agency Ppt Powerpoint Presentation Icon Professional Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Process Security Agency. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Electronic information security process of disaster recovery planning
Electronic information security process of disaster recovery planningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Increase audience engagement and knowledge by dispensing information using Electronic Information Security Process Of Disaster Recovery Planning. This template helps you present information on eight stages. You can also present information on Create Disaster, Recovery Team, Approval, Plan Testing, Forming Data Recovery Plan, Data Collection, Define Recovery Plans, Disaster Recovery Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social security retirement age ppt powerpoint presentation styles rules cpb
Social security retirement age ppt powerpoint presentation styles rules cpbPresenting our Social Security Retirement Age Ppt Powerpoint Presentation Styles Rules Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Three Major Steps Requirements Specification This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Ways for integrating security in application development process
Ways for integrating security in application development processIntroducing our premium set of slides with Ways For Integrating Security In Application Development Process. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Evaluation, Development Process, Applications. So download instantly and tailor it with your information.
-
 4 steps of rpa security for process automation improvement
4 steps of rpa security for process automation improvementPresenting our set of slides with 4 Steps Of RPA Security For Process Automation Improvement. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ensure Accountability, Protect Log Integrity, Enable Secure RPA Development.
-
 Network layer security protocols ppt powerpoint presentation pictures layout ideas cpb
Network layer security protocols ppt powerpoint presentation pictures layout ideas cpbPresenting our Network Layer Security Protocols Ppt Powerpoint Presentation Pictures Layout Ideas Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Network Layer Security Protocols This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Defining security threats effective information security risk management process
Defining security threats effective information security risk management processThis slide shows the categorization of information security threats. Categories covered are human error, natural disaster, software attacks and environmental control failures.Introducing Defining Security Threats Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Natural Disaster, Environmental Control Failures, Deliberate Software Attacks, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability information and event management logging process
Improve it security with vulnerability information and event management logging processThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Introducing Improve It Security With Vulnerability Information And Event Management Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Management, Process, using this template. Grab it now to reap its full benefits.
-
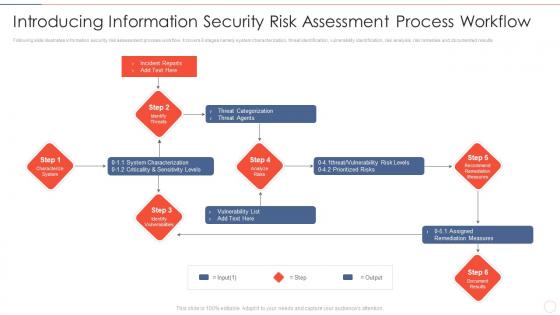 Effective information security introducing information security risk assessment process
Effective information security introducing information security risk assessment processFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results Increase audience engagement and knowledge by dispensing information using Effective Information Security Introducing Information Security Risk Assessment Process. This template helps you present information on six stages. You can also present information on Incident Reports, Threat Categorization, Vulnerability List, Assigned Remediation Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 6 step process to implement data availability security
6 step process to implement data availability securityThis slide represents 6 step process to implement data availability security illustrating simplified recording, on-site maintenance and online security, training, record disposal and plan. Presenting our set of slides with 6 Step Process To Implement Data Availability Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Management, Implement, Organization.
-
 Cyber threat security planning process with risk tolerance and threats
Cyber threat security planning process with risk tolerance and threatsThis following slide illustrates the cyber security threat program planning which include steps like identify key personnel, risk tolerance strategy and developing frequency. Presenting our set of slides with Cyber Threat Security Planning Process With Risk Tolerance And Threats. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Built Risk Tolerance, Identify And Document, Establish Governance.
-
 Network Security Process Of Disaster Recovery Planning
Network Security Process Of Disaster Recovery PlanningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Introducing Network Security Process Of Disaster Recovery Planning to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Operations, Processes, Assessment, Perform, using this template. Grab it now to reap its full benefits.
-
 Information Technology Security Process Of Disaster Recovery Planning
Information Technology Security Process Of Disaster Recovery PlanningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Introducing Information Technology Security Process Of Disaster Recovery Planning to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Process Of Disaster Recovery Planning, using this template. Grab it now to reap its full benefits.
-
 Computer Security Technical Assessment Process
Computer Security Technical Assessment ProcessThis slide signifies the technical assessment process on company security. It steps include identify, analyse, prioritize and monitoring. Introducing our premium set of slides with Computer Security Technical Assessment Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify, Analyse, Prioritize, Monitoring. So download instantly and tailor it with your information.
-
 Cyber Security Technical Assessment Process
Cyber Security Technical Assessment ProcessThis slide signifies the technical assessment process of cyber security. It include stages like identify, planning, execution, monitor and closure. Presenting our set of slides with Cyber Security Technical Assessment Process. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Execution, Closure, Planning, Monitor.
-
 Reverse Proxy It Process Of Secure Reverse Proxying
Reverse Proxy It Process Of Secure Reverse ProxyingThis slide depicts secure reverse proxying and how it can be established in three ways such as secure client to the proxy, secure proxy to the content server, and the secure client to proxy and secure proxy to a content server. Increase audience engagement and knowledge by dispensing information using Reverse Proxy It Process Of Secure Reverse Proxying. This template helps you present information on five stages. You can also present information on Process Of Secure Reverse Proxying using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Security Process Of Disaster Recovery Planning
Information Security Process Of Disaster Recovery PlanningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Increase audience engagement and knowledge by dispensing information using Information Security Process Of Disaster Recovery Planning. This template helps you present information on eight stages. You can also present information on Plan Testing, Approval, Prioritize Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Set Rules Configuration Network Security Ppt Powerpoint Presentation Gallery Pictures Cpb
Set Rules Configuration Network Security Ppt Powerpoint Presentation Gallery Pictures CpbPresenting our Set Rules Configuration Network Security Ppt Powerpoint Presentation Gallery Pictures Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Set Rules Configuration Network Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Secure Online Payment Processing Ppt Powerpoint Presentation Ideas Background Cpb
Secure Online Payment Processing Ppt Powerpoint Presentation Ideas Background CpbPresenting our Secure Online Payment Processing Ppt Powerpoint Presentation Ideas Background Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Secure Online Payment Processing. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Credit Card Processing Security Ppt Powerpoint Presentation Portfolio Brochure Cpb
Credit Card Processing Security Ppt Powerpoint Presentation Portfolio Brochure CpbPresenting our Credit Card Processing Security Ppt Powerpoint Presentation Portfolio Brochure Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Credit Card Processing Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Secure Loan Processing Ppt Powerpoint Presentation Show Skills Cpb
Secure Loan Processing Ppt Powerpoint Presentation Show Skills CpbPresenting Secure Loan Processing Ppt Powerpoint Presentation Show Skills Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Secure Loan Processing. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Secure Online Credit Card Processing Ppt Powerpoint Presentation File Backgrounds Cpb
Secure Online Credit Card Processing Ppt Powerpoint Presentation File Backgrounds CpbPresenting Secure Online Credit Card Processing Ppt Powerpoint Presentation File Backgrounds Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Secure Online Credit Card Processing. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Q70 Risk Management Framework For Information Security Incident Management Workflow Process
Q70 Risk Management Framework For Information Security Incident Management Workflow ProcessFollowing slide presents the incident management workflow of the firm. It covers five phases namely incident occurrence, team organizing, action taken, incident resolution and fail over report. Present the topic in a bit more detail with this Q70 Risk Management Framework For Information Security Incident Management Workflow Process. Use it as a tool for discussion and navigation on Incident Occurs, Team Takes Action, Auto Alerting, Fail Over Report, Organize Team, Incident Resolution. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Security Checklist Policies And Procedures Cloud Data Protection
Cloud Security Checklist Policies And Procedures Cloud Data ProtectionThis slide depicts the policies and procedures of the cloud security checklist. It also represents how it is essential to create new and update the current policies in an organization. Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Policies And Procedures Cloud Data Protection. This template helps you present information on five stages. You can also present information on Organization, On Boarding Employees, Cloud Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Pillars Of Cloud Security Process Based Security Cloud Data Protection
Pillars Of Cloud Security Process Based Security Cloud Data ProtectionThis slide represents the process-based security pillar of cloud security. It also shows how it works and what precautions does it take. Increase audience engagement and knowledge by dispensing information using Pillars Of Cloud Security Process Based Security Cloud Data Protection. This template helps you present information on four stages. You can also present information on Operational Security, Management, Operations using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Four Information Technology Security Processes
Four Information Technology Security ProcessesThis slide shows the four step by step processes used in information technology security. It includes penetration testing, VPN configuration, network security audit checklist and privileged password management. Presenting our set of slides with Four Information Technology Security Processes. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Penetration Testing, VPNConfiguration, Network Security Audit.
-
 Key Steps Of Saas Security Process
Key Steps Of Saas Security ProcessThe following slide depicts the SaaS security process to acknowledge the gap and have proactive approach. It mainly constitutes of three phases discover, monitor and protect. Presenting our set of slides with name Key Steps Of Saas Security Process. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ascertain Threats And Attacks, Encrypt Sensitive Data, Review Log Activities.
-
 Pillars Of Cloud Security Process Based Security Cloud Information Security
Pillars Of Cloud Security Process Based Security Cloud Information SecurityThis slide represents the process based security pillar of cloud security. It also shows how it works and what precautions does it take.Increase audience engagement and knowledge by dispensing information using Pillars Of Cloud Security Process Based Security Cloud Information Security This template helps you present information on four stages. You can also present information on Platform Customers, Different Locations, Adaptable Structure using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Domains That Will Be Addressed By Isms Iso 27001certification Process
Security Domains That Will Be Addressed By Isms Iso 27001certification ProcessThis slide portrays different security domains that will be addressed by ISMS. Domains covered are security policy, asset management, physical and environmental security, cryptography and human resource security. Introducing Security Domains That Will Be Addressed By Isms Iso 27001certification Process to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Security Policy, Human Resources Security, Access Control, using this template. Grab it now to reap its full benefits.
-
 Managed Security Service Threat Detection Process
Managed Security Service Threat Detection ProcessThe following slide highlights multistep process of managed security service to mitigate IT risks. It covers step such as operational readiness review, use cases, email notification, security analysis and event resolution. Introducing our premium set of slides with Managed Security Service Threat Detection Process. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Event Resolution, Operational Readiness Review, Email Notification, Security Analysis. So download instantly and tailor it with your information.
-
 Cyber Security Process For Cloud Services
Cyber Security Process For Cloud ServicesThe following slide highlights the cyber security process for cloud computing, cloud storage and cloud analytics storage. It depict identification, network security, data safety, application safety, monitoring and policy control to govern, protect and control the cloud services. Introducing our premium set of slides with name Cyber Security Process For Cloud Services. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network Security, Policy Control, Monitoring. So download instantly and tailor it with your information.
-
 Three Layers Of Cyber Security Management Process
Three Layers Of Cyber Security Management ProcessThe following slide highlights the three layers of cyber security management process which are dependent on people, process and technology, it helps company to manage cyber risks such as phishing attacks, data loss and exposed vulnerabilities. Presenting our set of slides with name Three Layers Of Cyber Security Management Process. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on People, Process, Technology.
-
 Steps To Ensure Robotic Process Automation Security Robotic Process Automation Types
Steps To Ensure Robotic Process Automation Security Robotic Process Automation TypesThis slide defines steps to ensure the security of robotic process automation, and it covers guarantee accountability for bot activities, protection from abuse, frauds, logs and bot development. Increase audience engagement and knowledge by dispensing information using Steps To Ensure Robotic Process Automation Security Robotic Process Automation Types. This template helps you present information on four stages. You can also present information on Process, Automation, Accountability using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 PCI Certification For Increasing Security Of Online Transactions Improving Financial Management Process
PCI Certification For Increasing Security Of Online Transactions Improving Financial Management ProcessThis slide depicts payment card industry PCI certification for increasing security of online transactions. It provides information about authorization, 2 way authentication, one time password OTP, repository, cyber attacks, compliance, data breach, etc. Increase audience engagement and knowledge by dispensing information using PCI Certification For Increasing Security Of Online Transactions Improving Financial Management Process. This template helps you present information on three stages. You can also present information on Before PCI Integration, PCI Integration, After Integration Impact using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Multistep Process Of Security Risk Acceptance
Multistep Process Of Security Risk AcceptanceThis slide shows multistep process of security risk acceptance which contains identifying risk, summarizing risk and risk acceptance and action. This can assist businesses in understanding the cause and effect of risks. Introducing our premium set of slides with Multistep Process Of Security Risk Acceptance. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identifying Risk, Summarizing Risk, Risk Acceptance Action. So download instantly and tailor it with your information.
-
 Cyber Security Risk Communication Process Framework
Cyber Security Risk Communication Process FrameworkThis slide showcases a model of risk communication process for cyber security. It includes identify issues, set goals, and objectives, community and constraints, stakeholder assessment, communication and engagement tools, implement strategy and evaluate and follow up. Introducing our premium set of slides with Cyber Security Risk Communication Process Framework. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Issue, Implement Strategy, Identify Messages. So download instantly and tailor it with your information.
-
 Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SS
Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SSThis slide showcases procedure that can help organization to implement mobile device management solution. Its key steps are current scenario assessment, policy development, choose solution etc. Increase audience engagement and knowledge by dispensing information using Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SS This template helps you present information on Five stages. You can also present information on Estimated Budget, Phase Duration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Process To Implement Mobile Vpn In Organization Mobile Device Security Cybersecurity SS
Process To Implement Mobile Vpn In Organization Mobile Device Security Cybersecurity SSThis slide showcases procedure that can help organization to implement VPN for mobile security. Its key steps are assessment, VPN technology selection, infrastructure setup etc. Introducing Process To Implement Mobile Vpn In Organization Mobile Device Security Cybersecurity SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Rating, Ideal, Softwares using this template. Grab it now to reap its full benefits.
-
 Process Phases For Application Security Assessment
Process Phases For Application Security AssessmentThis slide highlights the steps of application security assessment which include determining threats, identifying sensitive data, mapping application attacks, etc. Introducing our premium set of slides with Process Phases For Application Security Assessment Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Application Security, Statistical Representation So download instantly and tailor it with your information.
-
 Step By Step Process Of E Commerce Security
Step By Step Process Of E Commerce SecurityThis slide shows e-commerce transactions and data integrity through comprehensive multi-layer security measures. The steps are regular back of database, set up strong passwords, use malware softwwares,etc. Presenting our set of slides with Step By Step Process Of E Commerce Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Process, Ecommerce Security, Security Measures.
-
 Components Of Identity And Access Management Process Securing Systems With Identity
Components Of Identity And Access Management Process Securing Systems With IdentityThis slide discusses the Identity and Access Management components. The purpose of this slide is to highlight the various components, including the IAM framework, access and roles, IAM system function, centralized directory services, and so on. Introducing Components Of Identity And Access Management Process Securing Systems With Identity to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Iam Framework Purpose, Access And Roles, Iam System Functions using this template. Grab it now to reap its full benefits.
-
 Framework Of Identity And Access Management Process Securing Systems With Identity
Framework Of Identity And Access Management Process Securing Systems With IdentityThis slide discusses the Identity and Access Management framework. The purpose of this slide is to highlight the procedure that includes outlining how IAM architecture components work together, define user access to resources, and so on. Increase audience engagement and knowledge by dispensing information using Framework Of Identity And Access Management Process Securing Systems With Identity This template helps you present information on Eight stages. You can also present information on Employee Movements, Security Threat Reduction, Standard Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Functions Of Identity And Access Management Process Securing Systems With Identity
Functions Of Identity And Access Management Process Securing Systems With IdentityThis slide discusses the Identity and Access Management process functions. The purpose of this slide is to highlight the various functions, including identification in the system, roles in the design, assigning access levels, protecting sensitive data, and so on. Introducing Functions Of Identity And Access Management Process Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Identification In System, Roles In System using this template. Grab it now to reap its full benefits.
-
 Identity And Access Management Process In Workplace Securing Systems With Identity
Identity And Access Management Process In Workplace Securing Systems With IdentityThis slide discusses the Identity and Access Management process in the workplace. The purpose of this slide is to highlight the various usages of IAM in the workplace these include increasing the number of applications, managing identity data, and complex access scenarios. Increase audience engagement and knowledge by dispensing information using Identity And Access Management Process In Workplace Securing Systems With Identity This template helps you present information on Three stages. You can also present information on Increasing Number Of Applications, Managing Identity Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Parameters Of IAM Implementation Process Securing Systems With Identity
Key Parameters Of IAM Implementation Process Securing Systems With IdentityThis slide highlights the key function of the Identity and Access Management implementation process. The purpose of this slide is to explain the various parameters of IAM implementation these include identity lifecycle management, access control, authentication, and so on. Introducing Key Parameters Of IAM Implementation Process Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Authorization, Identity Governance using this template. Grab it now to reap its full benefits.
-
 Risk Associated With Identity And Access Management Process Securing Systems With Identity
Risk Associated With Identity And Access Management Process Securing Systems With IdentityThis slide outlines the potential hazards linked to the Identity and Access Management process. The purpose of this slide is to discuss the risks these include incorrectly defined roles and attributes, infrequent audits, and complex implementations. Introducing Risk Associated With Identity And Access Management Process Securing Systems With Identity to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Roles And Attributes, Infrequent Audits, Complex Implementations using this template. Grab it now to reap its full benefits.
-
 Streamlining Identity Management Process Within IAM Securing Systems With Identity
Streamlining Identity Management Process Within IAM Securing Systems With IdentityThis slide discusses the identity management of the Identity and Access Management process. The purpose of this slide is to explain identity management that relies on a combination of process, organizational structure, and enabling technologies. Introducing Streamlining Identity Management Process Within IAM Securing Systems With Identity to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Organization Structure, Processes, Technology using this template. Grab it now to reap its full benefits.
-
 Uniting Identity And Access Management Processes Securing Systems With Identity
Uniting Identity And Access Management Processes Securing Systems With IdentityThis slide discusses the Identity and Access Management uniting process. The purpose of this slide is to explain the Identity and Access Management unit, which involves users, access management, resources, identity management, and ID sources. Increase audience engagement and knowledge by dispensing information using Uniting Identity And Access Management Processes Securing Systems With Identity This template helps you present information on Four stages. You can also present information on Key Takeaways, Iam Market Size using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mobile Application Security Testing Process Mobile Security
Mobile Application Security Testing Process Mobile SecurityThis slide explains the mobile application security testing process which includes interaction and data handling and static analysis for weaknesses. Introducing Mobile Application Security Testing Process Mobile Security to increase your presentation threshold. Encompassed with Seven stages, this template is a great option to educate and entice your audience. Dispence information on Enable User Authentication, Cloud Backups using this template. Grab it now to reap its full benefits.
-
 Security Patch Management Process Lifecycle Mobile Security
Security Patch Management Process Lifecycle Mobile SecurityThis slide represents the patch management process lifecycle which include steps like standardize software versions, categorize assets and patches, etc. Introducing Security Patch Management Process Lifecycle Mobile Security to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Information Gathering, Exploitation using this template. Grab it now to reap its full benefits.
-
 Working Process Of Security Operations Center
Working Process Of Security Operations CenterThe below slide highlights the various steps involved in the working of security operations center that helps to safeguard sensitive data from cyber attacks. The major steps are asset discovery, behavioral monitoring, etc. Presenting our set of slides with name Working Process Of Security Operations Center. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Compliance Management, Incident Response, Alert Ranking.
-
 Hypertext Transfer Protocol Authentication In Web Security Solution
Hypertext Transfer Protocol Authentication In Web Security SolutionThis slide showcases the HTTP authentication in web security which include HTTP Basic Authentication, HTTP Digest Authentication, etc. Introducing Hypertext Transfer Protocol Authentication In Web Security Solution to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Http Basic Authentication, Http Digest Authentication, Https Client Authentication, Form Based Authentication, using this template. Grab it now to reap its full benefits.
-
 Steps For Security Configuration Management Process
Steps For Security Configuration Management ProcessThis slide depicts the process for security configuration management. Its objective is to harden the system to perform and control the tasks. This slide includes security requirement, identify, control, establish process, etc. Introducing our premium set of slides with name Steps For Security Configuration Management Process. Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify, Control, Develop And Adapt, Establish Process. So download instantly and tailor it with your information.
-
 Patch Management Process For IOT Device Security
Patch Management Process For IOT Device SecurityThe purpose of this slide is to ensure cybersecurity through compliance management and regular audits of network device patch management. It covers steps such as defining goals, conducting vulnerability scanning, managing patch compliance, etc. Presenting our set of slides with name Patch Management Process For IOT Device Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Evaluate Device Inventory, Embrace Automation, Test Patches.
-
 Security Patch Management Process Icon
Security Patch Management Process IconIntroducing our premium set of slides with name Security Patch Management Process Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security, Patch Management, Process. So download instantly and tailor it with your information.
-
 Software Security Patch Management Process
Software Security Patch Management ProcessThe purpose of this slide is to optimize software security through efficient patch management. It covers steps such as information retrieval, vulnerability scanning and patch testing. Presenting our set of slides with name Software Security Patch Management Process. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Retrieval, Vulnerability Scanning, Patch Testing.
-
 Web Security Upgradation Process Of Performing White Box Testing
Web Security Upgradation Process Of Performing White Box TestingThis slide highlights the steps for executing manual testing in software development such as document review, requirement analysis, etc. Introducing Web Security Upgradation Process Of Performing White Box Testing to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Process Of Performing White Box Testing, using this template. Grab it now to reap its full benefits.
-
 Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security Measures
Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security MeasuresThe slide depicts secure sockets layer SSL process to encrypt sensitive information between a webs browser and server. It include client web browser, websiteserver, SSL certificate etc. Introducing Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security Measures to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Client Check Certificate, Impact, Delivers Encrypted Content, using this template. Grab it now to reap its full benefits.
-
 Five Steps Process To Address Chatbot Security
Five Steps Process To Address Chatbot SecurityThis slide shows the processes organizations can use to improve or enhance the security of their chatbots. It includes stages such as assessment, minimizing data exposure, implementation, testing, and training. Introducing our premium set of slides with Five Steps Process To Address Chatbot Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Implement, Minimize Data Exposure, Test. So download instantly and tailor it with your information.
-
 Email Security Best Practices Components Of Email Account Security Process
Email Security Best Practices Components Of Email Account Security ProcessThis slide highlights the process of incorporating email security policies in an organization. The purpose of this slide is to illustrate the flow of email security implementation. The components are isolate, prevent, prepare, integrate, etc. Introducing Email Security Best Practices Components Of Email Account Security Process to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Prevent, Isolate, Respond, Prepare, Integrate, using this template. Grab it now to reap its full benefits.




