Powerpoint Templates and Google slides for Secure Systems
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Flowchart For Security Orchestration And Automation System
Flowchart For Security Orchestration And Automation SystemThe following slide highlights conceptual security automation flowchart. It includes components such as SOAR platform, orchestration process, unification, automation, detection, analysis, respond, security tool etc. Introducing our Flowchart For Security Orchestration And Automation System set of slides. The topics discussed in these slides are Organization, Task, Provides, Capability, Requires. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Four Step Process Of Security Automation System
Four Step Process Of Security Automation SystemThe following slide highlights multistep process of security automation. The company can detect security breach after following steps such as investigating the steps of IT analyst, determining responsive action, eradication and closing the ticked Presenting our set of slides with name Four Step Process Of Security Automation System. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Investigating Steps, Security Analysts, Eradication.
-
 Multistep Security Automation System Checklist
Multistep Security Automation System ChecklistThe following slide highlights a comprehensive checklist for security automation. The checklist covers key points such as deciding the budget, selecting the right tools, deciding the tasks for automation etc. Presenting our set of slides with name Multistep Security Automation System Checklist. This exhibits information on one stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Multistep, Security Automation System, Checklist.
-
 Categorization Worksheet For System Components Security Incident Response Playbook
Categorization Worksheet For System Components Security Incident Response PlaybookThis slide illustrates categorization worksheet that can be used to categorize system components. It includes information about security system such as system name, its version, system location and other general information. Present the topic in a bit more detail with this Categorization Worksheet For System Components Security Incident Response Playbook. Use it as a tool for discussion and navigation on Categorization, Worksheet, Components. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Incident Response Playbook Asset Criticality Of Identified System Components
Security Incident Response Playbook Asset Criticality Of Identified System ComponentsMentioned slide demonstrates the asset criticality of identified system components. It includes information of system name, component used, impact rating, criticality rating and failure cost. Present the topic in a bit more detail with this Security Incident Response Playbook Asset Criticality Of Identified System Components. Use it as a tool for discussion and navigation on Identified, Components, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Corporate System Security Quality Assurance QA Matrix
Corporate System Security Quality Assurance QA MatrixThis slide covers quality assurance for corporate system security. It includes a matrix based on functional and customer requirements for security system such as no access to restricted sites, email tracking, confidential data protection, etc. Introducing our Corporate System Security Quality Assurance QA Matrix set of slides. The topics discussed in these slides are Email Tracking, Confidential Data Protected, Customer And Functional. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Canva Security Processes And Systems Canva Company Profile Ppt Summary Graphics Tutorials
Canva Security Processes And Systems Canva Company Profile Ppt Summary Graphics TutorialsThis slide highlights the Canva security systems encryption, data security, attack, monitoring, staged releases, secure development, account safety and in app permissions. Introducing Canva Security Processes And Systems Canva Company Profile Ppt Summary Graphics Tutorials to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Secure Development, Monitoring, Data Security, using this template. Grab it now to reap its full benefits.
-
 F542 It Ot Convergence Security Objectives Challenges Catalysts And Strategies Ot And It Modern Pi System
F542 It Ot Convergence Security Objectives Challenges Catalysts And Strategies Ot And It Modern Pi SystemThis slide covers objectives challenges catalysts and benefits of the Security in IT or OT convergence and Reduce systems cyberattack surface Increase audience engagement and knowledge by dispensing information using F542 It Ot Convergence Security Objectives Challenges Catalysts And Strategies Ot And It Modern Pi System. This template helps you present information on four stages. You can also present information on Resources, Requirements, Heterogeneous using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
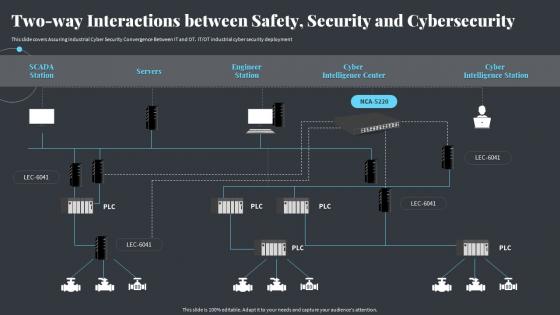 Two Way Interactions Between Safety Security And Cybersecurity Strategies Ot And It Modern Pi System
Two Way Interactions Between Safety Security And Cybersecurity Strategies Ot And It Modern Pi SystemThis slide covers Assuring Industrial Cyber Security Convergence Between IT and OT. IT or OT industrial cyber security deployment Deliver an outstanding presentation on the topic using this Two Way Interactions Between Safety Security And Cybersecurity Strategies Ot And It Modern Pi System. Dispense information and present a thorough explanation of Cybersecurity, Interactions, Intelligence Station using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IT Security Residual Risk Matrix With Risk Management Guide For Information Technology Systems
IT Security Residual Risk Matrix With Risk Management Guide For Information Technology SystemsThis slide highlights the information technology security residual risk matrix which includes asset, control topic, evaluation questions, response action and threat. Deliver an outstanding presentation on the topic using this IT Security Residual Risk Matrix With Risk Management Guide For Information Technology Systems. Dispense information and present a thorough explanation of Database Access, Evaluation Question, Response Action using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems
Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems. Use it as a tool for discussion and navigation on Threat Risk, Risk Mitigation Plan, Risk Owner. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Criteria And Control Measures For IT System Vulnerabilities
Security Criteria And Control Measures For IT System VulnerabilitiesThis slide highlights the security criteria for information technology system vulnerabilities with security area which includes management security, operational security and technical security. Introducing Security Criteria And Control Measures For IT System Vulnerabilities to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Security, Operational Security, Technical Security, using this template. Grab it now to reap its full benefits.
-
 Technical Security Control Model With Isk Management Guide For Information Technology Systems
Technical Security Control Model With Isk Management Guide For Information Technology SystemsThe following slide highlights the technical security control model which showcases different relationships and also includes supporting technical control function for protection and security. Deliver an outstanding presentation on the topic using this Technical Security Control Model With Isk Management Guide For Information Technology Systems. Dispense information and present a thorough explanation of Technical Security, Control Model, Supporting Technical, Control Function using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Importance Of Secure Ecommerce Payment Systems Analyzing And Implementing Management System
Importance Of Secure Ecommerce Payment Systems Analyzing And Implementing Management SystemThis slide represents the importance of payment gateways in facilitating systemized payment methods and providing consumers with fast and flexible way for making payments. It includes benefits of ecommerce payment systems such as meets digital needs, customer retention, security etc. Deliver an outstanding presentation on the topic using this Importance Of Secure Ecommerce Payment Systems Analyzing And Implementing Management System. Dispense information and present a thorough explanation of Customer Retention, Security, Multiple Payment Modes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Financial Burden To Company From It Security Breaches Risk Assessment Of It Systems
Financial Burden To Company From It Security Breaches Risk Assessment Of It SystemsThis slide highlights the financial burden of information technology security breaches which includes professional services, lost business opportunities, down time from multiple offices with losses. Deliver an outstanding presentation on the topic using this Financial Burden To Company From It Security Breaches Risk Assessment Of It Systems. Dispense information and present a thorough explanation of Professional Services, Lost Business Opportunities, Financial using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 It Security Residual Risk Matrix With Response Actions Risk Assessment Of It Systems
It Security Residual Risk Matrix With Response Actions Risk Assessment Of It SystemsThis slide highlights the information technology security residual risk matrix which includes asset, control topic, evaluation questions, response action and threat. Deliver an outstanding presentation on the topic using this It Security Residual Risk Matrix With Response Actions Risk Assessment Of It Systems. Dispense information and present a thorough explanation of Information, Technology, Evaluation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems
Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems. Use it as a tool for discussion and navigation on Mitigation Plan, Prioritized, Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Assessment Of It Systems Detection And Prevention Of Management Security Controls
Risk Assessment Of It Systems Detection And Prevention Of Management Security ControlsThe following slide highlights the management security controls which includes preventive management security controls showcasing IT security polices and guidelines with detection management security controls. Present the topic in a bit more detail with this Risk Assessment Of It Systems Detection And Prevention Of Management Security Controls. Use it as a tool for discussion and navigation on Prevention, Management, Security Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
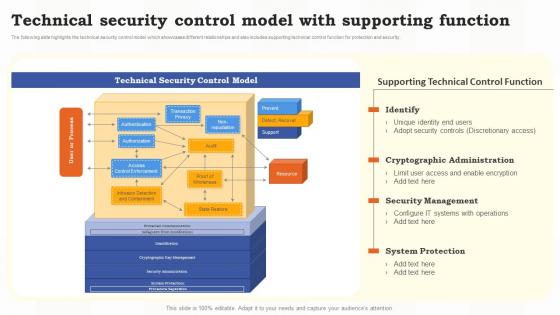 Technical Security Control Model With Supporting Function Risk Assessment Of It Systems
Technical Security Control Model With Supporting Function Risk Assessment Of It SystemsThe following slide highlights the technical security control model which showcases different relationships and also includes supporting technical control function for protection and security. Deliver an outstanding presentation on the topic using this Technical Security Control Model With Supporting Function Risk Assessment Of It Systems. Dispense information and present a thorough explanation of Technical, Security Management, System Protection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Automation Integrates Tools Systems And Processes Security Automation In Information Technology
Security Automation Integrates Tools Systems And Processes Security Automation In Information TechnologyThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Increase audience engagement and knowledge by dispensing information using Security Automation Integrates Tools Systems And Processes Security Automation In Information Technology. This template helps you present information on eight stages. You can also present information on Automation, Integrates, Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
 Risk Assessment Of It Systems Security Criteria And Control Measures For It System Vulnerabilities
Risk Assessment Of It Systems Security Criteria And Control Measures For It System VulnerabilitiesThis slide highlights the security criteria for information technology system vulnerabilities with security area which includes management security, operational security and technical security. Deliver an outstanding presentation on the topic using this Risk Assessment Of It Systems Security Criteria And Control Measures For It System Vulnerabilities. Dispense information and present a thorough explanation of Management Security, Operational Security, Technical Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Automation Integrates Tools Systems And Security Automation To Investigate And Remediate Cyberthreats
Security Automation Integrates Tools Systems And Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Increase audience engagement and knowledge by dispensing information using Security Automation Integrates Tools Systems And Security Automation To Investigate And Remediate Cyberthreats. This template helps you present information on eight stages. You can also present information on Automation, Processes, System Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 F638 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your Skillset
F638 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your SkillsetThis slide covers CISSP certification details such as what is the CISSP, how to become certified, how to prepare for CISSP and why to get CISSP certifications Deliver an outstanding presentation on the topic using this F638 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your Skillset. Dispense information and present a thorough explanation of Certification, Security Professional, Information Systems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 F639 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your Skillset
F639 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your SkillsetThis slide covers information about CISSP Examination such as weight of each domain in exams, prep courses details, qualification details etc. Present the topic in a bit more detail with this F639 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your Skillset. Use it as a tool for discussion and navigation on Examination, Information, Professional. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security Operations
Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security OperationsThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Present the topic in a bit more detail with this Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Security Automation, Integrates, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Evaluating IT System Security Using Swot Analysis Conducting Security Awareness
Evaluating IT System Security Using Swot Analysis Conducting Security AwarenessThe purpose of this slide is to outline the strength, weakness, opportunities and threat SWOT evaluation of organization cyber security. Organization can detect the potential risks and opportunities in the cyber security using SWOT model. Introducing Evaluating IT System Security Using Swot Analysis Conducting Security Awareness to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strengths, Weaknesses, Opportunities, Threats, using this template. Grab it now to reap its full benefits.
-
 F645 It Certifications To Expand Your Skillset Certified Information Systems Security Professional
F645 It Certifications To Expand Your Skillset Certified Information Systems Security ProfessionalThis slide covers CISSP certification information about salary and job responsibilities and CISSP certification salary ranges by job etc. Deliver an outstanding presentation on the topic using this F645 It Certifications To Expand Your Skillset Certified Information Systems Security Professional. Dispense information and present a thorough explanation of Information, Professional, Responsibilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key Members Of Financial Security Department Developing Anti Money Laundering And Monitoring System
Key Members Of Financial Security Department Developing Anti Money Laundering And Monitoring SystemThe following slide highlights key members of financial security department . It provides information about chief financial officer CFO, compliance auditor, senior analyst, customer support manager, operations manager, etc. Increase audience engagement and knowledge by dispensing information using Key Members Of Financial Security Department Developing Anti Money Laundering And Monitoring System. This template helps you present information on seven stages. You can also present information on Financial Security Department, Executive Officer, Transaction Monitoring using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Major Roles And Responsibilities Of Financial Security Developing Anti Money Laundering And Monitoring System
Major Roles And Responsibilities Of Financial Security Developing Anti Money Laundering And Monitoring SystemThe following slide Major roles and responsibilities of financial security department . It includes information about risk level determination, laws and regulations, team training, operational compliance, automatic workflows, red flags, etc. Present the topic in a bit more detail with this Major Roles And Responsibilities Of Financial Security Developing Anti Money Laundering And Monitoring System. Use it as a tool for discussion and navigation on Responsibilities, Financial, Operational Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Evaluating It System Security Using Swot Analysis Developing Cyber Security Awareness Training Program
Evaluating It System Security Using Swot Analysis Developing Cyber Security Awareness Training ProgramThe purpose of this slide is to outline the strength, weakness, opportunities and threat SWOT evaluation of organization cyber security. Organization can detect the potential risks and opportunities in the cyber security using SWOT model. Introducing Evaluating It System Security Using Swot Analysis Developing Cyber Security Awareness Training Program to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strengths, Weaknesses, Opportunities, Threats, using this template. Grab it now to reap its full benefits.
-
 Access Control In Secured Database Management System
Access Control In Secured Database Management SystemThis slide represents the block diagram representing the access control in secured database management system. It includes details related to database and security administrator, authorization system, database schemas, application programs etc. Presenting our well structured Access Control In Secured Database Management System. The topics discussed in this slide are Access Control, Secured Database, Management System. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cost Home Security System In Powerpoint And Google Slides Cpb
Cost Home Security System In Powerpoint And Google Slides CpbPresenting Cost Home Security System In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cost Home Security System. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cps Security And Privacy Life Cycle Next Generation Computing Systems Ppt Show Graphics Design
Cps Security And Privacy Life Cycle Next Generation Computing Systems Ppt Show Graphics DesignThis slide depicts the cyber-physical systems security and privacy life cycle, including its phases from 1 to 6, along with the tasks performed in each phase. Present the topic in a bit more detail with this Cps Security And Privacy Life Cycle Next Generation Computing Systems Ppt Show Graphics Design. Use it as a tool for discussion and navigation on Performance, Operational, Capability . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Safety And Security Objectives In Cyber Physical Systems Next Generation Computing Systems
Safety And Security Objectives In Cyber Physical Systems Next Generation Computing SystemsThis slide represents cyber-physical systems safety and security objectives, including confidentiality, integrity, availability, authenticity, and robustness. Present the topic in a bit more detail with this Safety And Security Objectives In Cyber Physical Systems Next Generation Computing Systems. Use it as a tool for discussion and navigation on Confidentiality, Availability, Authenticity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Strategic Planning Process For Cps Next Generation Computing Systems
Security Strategic Planning Process For Cps Next Generation Computing SystemsThis slide represents the security strategic planning process for CPS, including business strategy, technology roadmap, vision statement environment trends, current state assessment, and so on. Present the topic in a bit more detail with this Security Strategic Planning Process For Cps Next Generation Computing Systems. Use it as a tool for discussion and navigation on Strategic, Planning, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Steps For Cps Security Strategy Plan Next Generation Computing Systems Ppt Show Design Inspiration
Steps For Cps Security Strategy Plan Next Generation Computing Systems Ppt Show Design InspirationThis slide depicts the steps for the CPS security strategy plan, including recognizing the risks and assessing the current business situation, creating a goal and doing a gap analysis, etc. Present the topic in a bit more detail with this Steps For Cps Security Strategy Plan Next Generation Computing Systems Ppt Show Design Inspiration. Use it as a tool for discussion and navigation on Communicate, Implementation, Continuous Monitoring. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 30 60 90 Days Plan Information System Security And Risk Administration Plan Ppt Styles Ideas
30 60 90 Days Plan Information System Security And Risk Administration Plan Ppt Styles IdeasIntroducing 30 60 90 Days Plan Information System Security And Risk Administration Plan Ppt Styles Ideas to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Days Plan, using this template. Grab it now to reap its full benefits.
-
 About Us Information System Security And Risk Administration Plan Ppt Styles Gallery
About Us Information System Security And Risk Administration Plan Ppt Styles GalleryIncrease audience engagement and knowledge by dispensing information using About Us Information System Security And Risk Administration Plan Ppt Styles Gallery. This template helps you present information on three stages. You can also present information on Target Audiences, Creative, Value Clients using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda For Information System Security And Risk Administration Plan Ppt Styles Model
Agenda For Information System Security And Risk Administration Plan Ppt Styles ModelIntroducing Agenda For Information System Security And Risk Administration Plan Ppt Styles Model to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Information System Security, Current Information Security, Information Security Risks, using this template. Grab it now to reap its full benefits.
-
 Analysing The Impact Of Security Threats Information System Security And Risk Administration Plan
Analysing The Impact Of Security Threats Information System Security And Risk Administration PlanIncrease audience engagement and knowledge by dispensing information using Analysing The Impact Of Security Threats Information System Security And Risk Administration Plan. This template helps you present information on one stages. You can also present information on Security Threats, Malware, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Analysing The Impact On Assets Information Breach Information System Security And Risk Administration
Analysing The Impact On Assets Information Breach Information System Security And Risk AdministrationThis slide showcases impact of information breach on different assets which can help organization in formulating risk monitoring policy. Its key components are criterion, criterion weight and information assets. Deliver an outstanding presentation on the topic using this Analysing The Impact On Assets Information Breach Information System Security And Risk Administration. Dispense information and present a thorough explanation of Cost To Protect, Sales Records, Products Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Assigning Criticality Rating To Assets Information System Security And Risk Administration Plan
Assigning Criticality Rating To Assets Information System Security And Risk Administration PlanThis slide showcases criticality rating that can be allocation to assets for identifying critical assets. Its key elements are asst, failure cost, failure impact and criticality rating. Deliver an outstanding presentation on the topic using this Assigning Criticality Rating To Assets Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Failure Cost, Criticality Rating, Product Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Budget For Information Security Risk Management Information System Security And Risk Administration
Budget For Information Security Risk Management Information System Security And Risk AdministrationThis slide showcases budget that can should be allocated for different information security risk management activities. It provides information about employees training, software implementation, risk monitoring and data backup. Introducing Budget For Information Security Risk Management Information System Security And Risk Administration to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Training Of Employees, Software Implementation, Risk Monitoring, using this template. Grab it now to reap its full benefits.
-
 Cyber Attacks Faced By Different Departments Information System Security And Risk Administration Plan
Cyber Attacks Faced By Different Departments Information System Security And Risk Administration PlanThis slide showcases information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks. Present the topic in a bit more detail with this Cyber Attacks Faced By Different Departments Information System Security And Risk Administration Plan. Use it as a tool for discussion and navigation on It Department, Marketing Department, Operations Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Financial Impact Of Information Security Attacks Information System Security And Risk Administration Plan
Financial Impact Of Information Security Attacks Information System Security And Risk Administration PlanThis slide showcases financial impact of different cyber security attacks on organizations. Its key elements are business disruption, information loss, revenue loss, equipment damage and total cost by attack type. Introducing Financial Impact Of Information Security Attacks Information System Security And Risk Administration Plan to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering, Web Based Attacks, Stolen Devices, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Information System Security And Risk Administration Plan Ppt Styles Summary
Icons Slide For Information System Security And Risk Administration Plan Ppt Styles SummaryDeliver an outstanding presentation on the topic using this Icons Slide For Information System Security And Risk Administration Plan Ppt Styles Summary. Dispense information and present a thorough explanation of Icons Slide using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identifying Employees For Information Security Training Information System Security And Risk Administration
Identifying Employees For Information Security Training Information System Security And Risk AdministrationThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner. Present the topic in a bit more detail with this Identifying Employees For Information Security Training Information System Security And Risk Administration. Use it as a tool for discussion and navigation on Threat Scanning, Malware Detection, Report Formulation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security And Risk Management User Spending By Segment Information System Security And Risk
Information Security And Risk Management User Spending By Segment Information System Security And RiskThis slide showcases expenses done by organization in different segments of information security and risk management. Key segments include application security, cloud security, data security, identify access management, infrastructure protection, integrated risk management, security services etc. Present the topic in a bit more detail with this Information Security And Risk Management User Spending By Segment Information System Security And Risk. Use it as a tool for discussion and navigation on Marketing Segment, Network Security Equipment, Integrated Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information System Security And Risk Administration Plan Checklist For Information Security Risk
Information System Security And Risk Administration Plan Checklist For Information Security RiskThis slide showcases checklist that can help to ensure formulate and implementing data security risk management program in organization. Its key components are activity, assigned to and status. Deliver an outstanding presentation on the topic using this Information System Security And Risk Administration Plan Checklist For Information Security Risk. Dispense information and present a thorough explanation of Process To Tackle Risks, Identify Vulnerabilities, Formulating Risk Management Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 KPIS To Measure Information Security Risk Information System Security And Risk Administration Plan
KPIS To Measure Information Security Risk Information System Security And Risk Administration PlanThis slide showcases KPIs that can help organization to measure the impact of cybersecurity risk management programme. It showcases estimated figures before and after implementation of plan. Deliver an outstanding presentation on the topic using this KPIS To Measure Information Security Risk Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Intrusion Attempts, Risk Management Programme, Cost Per Incident using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Matrix For Threat Solution And Risk Management Information System Security And Risk Administration Plan
Matrix For Threat Solution And Risk Management Information System Security And Risk Administration PlanThis slide showcases matrix that can help organization to formulate solutions for different types of information security attacks. It can help organization to mitigate the risks and safeguard information in case of any attack. Deliver an outstanding presentation on the topic using this Matrix For Threat Solution And Risk Management Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Monitor Database Activity, Validate Database Protocols, Capture Detailed Transactions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Meet Our Team Information System Security And Risk Administration Plan Ppt Styles Visual Aids
Meet Our Team Information System Security And Risk Administration Plan Ppt Styles Visual AidsIntroducing Meet Our Team Information System Security And Risk Administration Plan Ppt Styles Visual Aids to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Meet Our Team, using this template. Grab it now to reap its full benefits.
-
 Information System Security And Risk Administration Plan Gap Assessment Of Organization Information Security
Information System Security And Risk Administration Plan Gap Assessment Of Organization Information SecurityThis slide showcases gap assessment of information security capabilities of organization. It also provides solutions to tackle the problems faced by company like frequent malware attacks and lack of awareness among employees. Present the topic in a bit more detail with this Information System Security And Risk Administration Plan Gap Assessment Of Organization Information Security. Use it as a tool for discussion and navigation on Corporate Security Programme, Low Cost Ransomware Tools, Vulnerabilities In Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information System Security And Risk Administration Plan Identifying Information Security Threats And Impact
Information System Security And Risk Administration Plan Identifying Information Security Threats And ImpactThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization. Increase audience engagement and knowledge by dispensing information using Information System Security And Risk Administration Plan Identifying Information Security Threats And Impact. This template helps you present information on one stages. You can also present information on Employee Sabotage, Physical Infrastructure Loss, Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information System Security And Risk Administration Plan Information Security Attacks Faced By Organization
Information System Security And Risk Administration Plan Information Security Attacks Faced By OrganizationThis slide showcases most common information attacks faced by organization. It includes malware, phishing, man in the middle attack, SQL injection, zero day exploit and DNS attack. Increase audience engagement and knowledge by dispensing information using Information System Security And Risk Administration Plan Information Security Attacks Faced By Organization. This template helps you present information on six stages. You can also present information on Sql Injection, Zero Day Exploit, Phishing Attack Accounts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat Level
Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat LevelThis slide showcases assessment matrix to identify risk associated with different class of information assets. It calculates severity of risk on the basis of threat and vulnerability level. Present the topic in a bit more detail with this Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat Level. Use it as a tool for discussion and navigation on Treat Level, Vulnerability Level, Risk Assessment Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information System Security And Risk Administration Plan Roles And Responsibilities Of Risk Management Team
Information System Security And Risk Administration Plan Roles And Responsibilities Of Risk Management TeamThis slide showcases responsibilities of major employees involved in information security risk management team. Key roles are information security manager, risk management officer and chief information officer. Introducing Information System Security And Risk Administration Plan Roles And Responsibilities Of Risk Management Team to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information Security Manager, Risk Management Officer, Chief Information Officer, using this template. Grab it now to reap its full benefits.
-
 Information System Security And Risk Administration Current Information And Data Security Capabilities Of Firm
Information System Security And Risk Administration Current Information And Data Security Capabilities Of FirmThis slide showcases current capabilities of organization regarding information and data security. Its key component are risk management functions, required standard rating and actual standard rating. Deliver an outstanding presentation on the topic using this Information System Security And Risk Administration Current Information And Data Security Capabilities Of Firm. Dispense information and present a thorough explanation of Risk Management Functions, Required Standard Rating, Actual Standard Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Current Information Security Issues Faced By Information System Security And Risk Administration
Current Information Security Issues Faced By Information System Security And Risk AdministrationIncrease audience engagement and knowledge by dispensing information using Current Information Security Issues Faced By Information System Security And Risk Administration. This template helps you present information on four stages. You can also present information on Untrained Employees, Frequent Data Breaches, Complex Risk Management Policy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
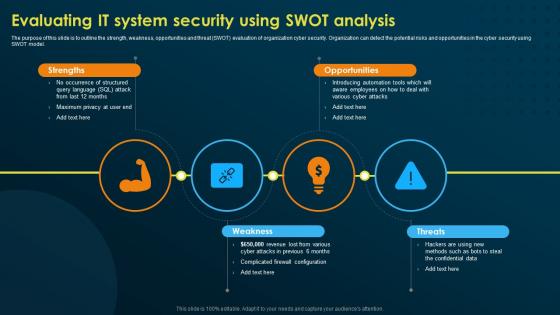 Evaluating It System Security Using Swot Analysis Implementing Security Awareness Training
Evaluating It System Security Using Swot Analysis Implementing Security Awareness TrainingThe purpose of this slide is to outline the strength, weakness, opportunities and threat SWOT evaluation of organization cyber security. Organization can detect the potential risks and opportunities in the cyber security using SWOT model. Increase audience engagement and knowledge by dispensing information using Evaluating It System Security Using Swot Analysis Implementing Security Awareness Training. This template helps you present information on four stages. You can also present information on Strengths, Opportunities, Weakness, Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.





