Powerpoint Templates and Google slides for Secure Systems
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Computer system security cyber attacks experienced by company in previous financial year
Computer system security cyber attacks experienced by company in previous financial yearThis slide shows the impact on the organizations financial condition due to cyber attacks in the past financial year 2021. Present the topic in a bit more detail with this Computer System Security Cyber Attacks Experienced By Company In Previous Financial Year. Use it as a tool for discussion and navigation on Cyber Attacks Experienced By Company In Previous Financial Year. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Computer system security prepare data backup for sensitive information
Computer system security prepare data backup for sensitive informationThis slide represents the preparation of data backup for sensitive information and how data backup should be created and stored within an organization. Introducing Computer System Security Prepare Data Backup For Sensitive Information to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Prepare Data Backup For Sensitive Information, using this template. Grab it now to reap its full benefits.
-
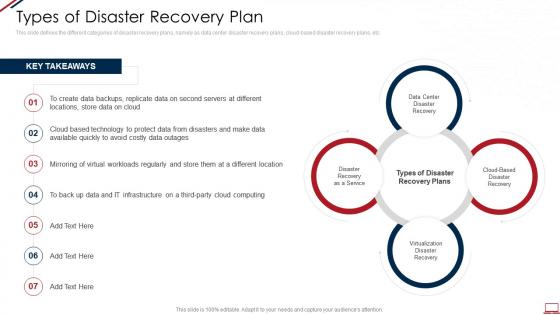 Computer system security types of disaster recovery plan
Computer system security types of disaster recovery planThis slide defines the different categories of disaster recovery plans, namely as data center disaster recovery plans, cloud-based disaster recovery plans, etc. Introducing Computer System Security Types Of Disaster Recovery Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Virtualization Disaster Recovery, Cloud Based Disaster Recovery, Data Center Disaster Recovery, Disaster Recovery As A Service, using this template. Grab it now to reap its full benefits.
-
 Table of contents for computer system security cont computer system security
Table of contents for computer system security cont computer system securityPresent the topic in a bit more detail with this Table Of Contents For Computer System Security Cont Computer System Security. Use it as a tool for discussion and navigation on Computer Security, Implementation, Roadmap Or Timeline, Business, Budget. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda for computer system security ppt powerpoint presentation slides visuals
Agenda for computer system security ppt powerpoint presentation slides visualsIntroducing Agenda For Computer System Security Ppt Powerpoint Presentation Slides Visuals to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity, Training, Strategies, Plan, Policies, using this template. Grab it now to reap its full benefits.
-
 Computer system security assessment matrix of cyber risks ppt grid
Computer system security assessment matrix of cyber risks ppt gridThis slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web or mobile applications, online payments, employee devices. Increase audience engagement and knowledge by dispensing information using Computer System Security Assessment Matrix Of Cyber Risks Ppt Grid. This template helps you present information on one stages. You can also present information on Industrial, Data Center, Multifamily, Retail, Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer system security comparison ppt powerpoint presentation slides visuals
Computer system security comparison ppt powerpoint presentation slides visualsIntroducing Computer System Security Comparison Ppt Powerpoint Presentation Slides Visuals to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Male Users, Female Users, using this template. Grab it now to reap its full benefits.
-
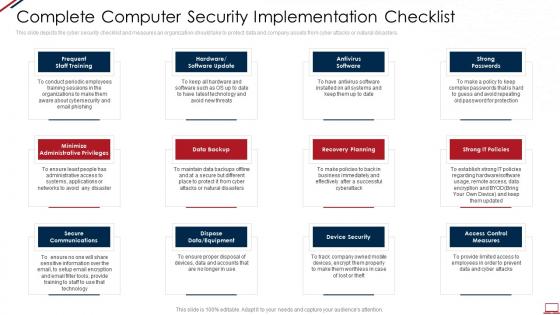 Computer system security complete computer security implementation checklist
Computer system security complete computer security implementation checklistThis slide depicts the cyber security checklist and measures an organization should take to protect data and company assets from cyber attacks or natural disasters. Increase audience engagement and knowledge by dispensing information using Computer System Security Complete Computer Security Implementation Checklist. This template helps you present information on twelve stages. You can also present information on Data Backup, Secure Communications, Recovery Planning, Strong Passwords, Device Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer system security compliance dashboard Snapshot of computer security
Computer system security compliance dashboard Snapshot of computer securityThis slide depicts the cyber security compliance report on how data and hardware are monitored in different categories such as standard, regulation, and asset type control. Present the topic in a bit more detail with this Computer System Security Compliance Dashboard Snapshot Of Computer Security. Use it as a tool for discussion and navigation on Asset Type Control, Control Issues By Standard, Control Issues By Regulation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Computer system security computer security awareness training for staff
Computer system security computer security awareness training for staffThis slide represents the cybersecurity awareness training program for staff, including the name of the participants and what modules would be covered under training daily. Deliver an outstanding presentation on the topic using this Computer System Security Computer Security Awareness Training For Staff. Dispense information and present a thorough explanation of Senior Executives, Project Managers, IT Teams, Front Line Staff, Developers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
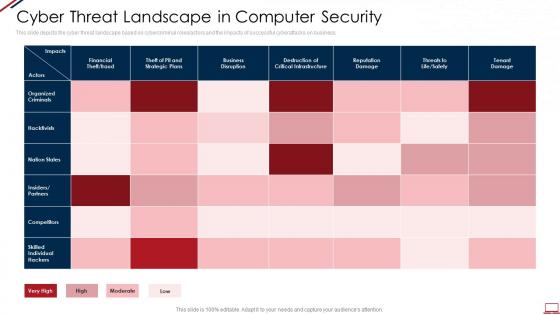 Computer system security cyber threat landscape in computer security
Computer system security cyber threat landscape in computer securityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Present the topic in a bit more detail with this Computer System Security Cyber Threat Landscape In Computer Security. Use it as a tool for discussion and navigation on Financial, Business, Tenant Damage, Organized Criminals, Competitors. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Computer system security dashboard snapshot for threat tracking in computer security
Computer system security dashboard snapshot for threat tracking in computer securityThis slide depicts the dashboard snapshot for threat tracking in cyber security by covering monthly threat status, current risk status, threat based on the role, threats by owners, risk by threats, and threat report. Deliver an outstanding presentation on the topic using this Computer System Security Dashboard For Threat Tracking In Computer Security. Dispense information and present a thorough explanation of Monthly Threat Status, Threats By Owners, Risk By Threats, Current Risk Status, Threats Based On Role using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Computer system security detail impact computer security plan can reduce the risk of data breach in organization
Computer system security detail impact computer security plan can reduce the risk of data breach in organizationThis slide represents the current status of the cyber attacks in an organization after implementing the cyber security model. Present the topic in a bit more detail with this Computer System Security Detail Impact Computer Security Plan Can Reduce The Risk Of Data Breach In Organization. Use it as a tool for discussion and navigation on System Misconfiguration, Network Intrusion, Automated Information Exfiltration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Computer system security highest number of malware attacks in departments
Computer system security highest number of malware attacks in departmentsThis slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2021 year. Present the topic in a bit more detail with this Computer System Security Highest Number Of Malware Attacks In Departments. Use it as a tool for discussion and navigation on Development Dept, Accounts Dept, HR Dept, Other, IT Dept. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
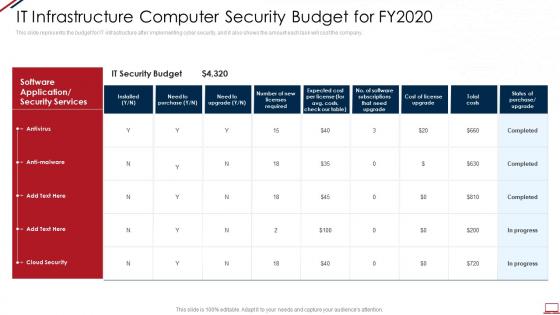 Computer system security it infrastructure computer security budget for fy2020
Computer system security it infrastructure computer security budget for fy2020This slide represents the budget for IT infrastructure after implementing cyber security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Computer System Security It Infrastructure Computer Security Budget For Fy2020. Use it as a tool for discussion and navigation on Cost, IT Security Budget, Software Application Or Security Services, Antivirus, Anti Malware. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Computer system security main steps of operational security
Computer system security main steps of operational securityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Introducing Computer System Security Main Steps Of Operational Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Assessment Of Risks, Analyze Security Holes And Vulnerabilities, Potential Threats, Sensitive Information, Implementation Of Appropriate Countermeasures, using this template. Grab it now to reap its full benefits.
-
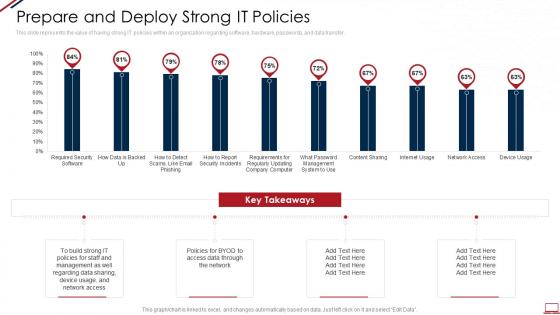 Computer system security prepare and deploy strong it policies
Computer system security prepare and deploy strong it policiesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Present the topic in a bit more detail with this Computer System Security Prepare And Deploy Strong It Policies. Use it as a tool for discussion and navigation on Prepare And Deploy Strong IT Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Computer system security problems faced by the organization
Computer system security problems faced by the organizationThis slide shows the organizations current situation through the total losses in millions experienced because of different cyberattacks. Deliver an outstanding presentation on the topic using this Computer System Security Problems Faced By The Organization. Dispense information and present a thorough explanation of Problems Faced By The Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Computer system security process of disaster recovery planning
Computer system security process of disaster recovery planningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Introducing Computer System Security Process Of Disaster Recovery Planning to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Plan Testing, Approval, Recovery Plans, Data Collection, Forming Data Recovery Plan, using this template. Grab it now to reap its full benefits.
-
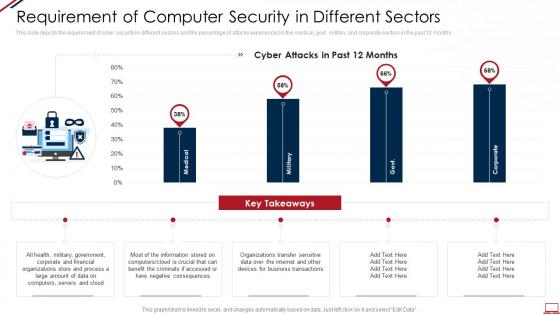 Computer system security requirement of computer security in different sectors
Computer system security requirement of computer security in different sectorsThis slide depicts the requirement of cyber security in different sectors and the percentage of attacks experienced in the medical, govt, military, and corporate sectors in the past 12 months. Present the topic in a bit more detail with this Computer System Security Requirement Of Computer Security In Different Sectors. Use it as a tool for discussion and navigation on Organizations, Process, Business. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Computer system security timeline for the implementation of computer security
Computer system security timeline for the implementation of computer securityThis slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Present the topic in a bit more detail with this Computer System Security Timeline For The Implementation Of Computer Security. Use it as a tool for discussion and navigation on Security, Risk Assessments, Perform. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Computer system security types of threats in computer security
Computer system security types of threats in computer securityThis slide depicts the main types of threats in cyber security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Increase audience engagement and knowledge by dispensing information using Computer System Security Types Of Threats In Computer Security. This template helps you present information on three stages. You can also present information on Cyber Crime, Cyber Terrorism, Cyber Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer system security what is computer security and how does it work
Computer system security what is computer security and how does it workThis slide defines the meaning of cyber security and how it helps to prevent data through different methods and techniques. Introducing Computer System Security What Is Computer Security And How Does It Work to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Techniques, Collective, Networks, Computer Systems, using this template. Grab it now to reap its full benefits.
-
 Table of contents for computer system security cont ppt powerpoint slides guide
Table of contents for computer system security cont ppt powerpoint slides guidePresent the topic in a bit more detail with this Table Of Contents For Computer System Security Cont Ppt Powerpoint Slides Guide. Use it as a tool for discussion and navigation on Organization, Mitigation, Implementation, Security, Planning. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security systems payment systems ppt powerpoint presentation infographic template format ideas cpb
Security systems payment systems ppt powerpoint presentation infographic template format ideas cpbPresenting our Security Systems Payment Systems Ppt Powerpoint Presentation Infographic Template Format Ideas Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Security Systems Payment Systems This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Best Business Security Camera System In Powerpoint And Google Slides Cpb
Best Business Security Camera System In Powerpoint And Google Slides CpbPresenting our Best Business Security Camera System In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Best Business Security Camera System This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 F1590 Zero Trust Network Access System Use Cases Zero Trust Security Model
F1590 Zero Trust Network Access System Use Cases Zero Trust Security ModelThis slide outlines multiple use cases of zero-trust network access systems. The purpose of this slide is to showcase the main use cases of the ZTNA model, which are replacing VPN and MPLS connections, internal firewall replacement, securing remote access to private apps, limiting user access, and so on. Present the topic in a bit more detail with this F1590 Zero Trust Network Access System Use Cases Zero Trust Security Model. Use it as a tool for discussion and navigation on Internal Firewall Replacement, Limiting User Access, Network Access Control Replacement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Integrating Security Principle With Dynamic System Development Method
Integrating Security Principle With Dynamic System Development MethodThis slide showcases incorporation of software security principles in DSDM model which helps in improving degree of project agility. It provides information regarding execution, functional model iteration, security design and security functional modulation. Introducing our Integrating Security Principle With Dynamic System Development Method set of slides. The topics discussed in these slides are Business Study, Integrating Security, Dynamic System Development. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security System Industry Growth In Powerpoint And Google Slides Cpb
Security System Industry Growth In Powerpoint And Google Slides CpbPresenting our Security System Industry Growth In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases two stages. It is useful to share insightful information on Security System Industry Growth This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Challenges And Solutions Associated With Security System
Challenges And Solutions Associated With Security SystemThis slide highlights security system challenges and solutions to overcome them. This further includes organization name, challenge and solutions such as server breach on main website of firm etc. Introducing our premium set of slides with Challenges And Solutions Associated With Security System. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Organization, Company, Security System. So download instantly and tailor it with your information.
-
 Cloud Cyber Security System Architecture
Cloud Cyber Security System ArchitectureThis slide showcases cyber security system architecture for business cloud data protection from hacks. This further includes key takeaways such as business having cloud misconfiguration that pose serious hazards. Introducing our Cloud Cyber Security System Architecture set of slides. The topics discussed in these slides are Emulated Components, Cyber Security, System Architecture. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Components Of Effective Enterprise Security System
Components Of Effective Enterprise Security SystemThis slide represents enterprise security system components for effectiveness. This further includes components such as security cameras, video monitoring, smartphone alerts, manage employee access. Presenting our set of slides with Components Of Effective Enterprise Security System. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Cameras, Video Monitoring, Smartphone Alerts.
-
 Global Cyber Security System Market Size Overview
Global Cyber Security System Market Size OverviewThis slide showcases market size overview for global cyber security system. This further includes key takeaways and data projection such as 175 billion dollars to 300 billion dollars by 2027 and about growth rate increase. Introducing our premium set of slides with Global Cyber Security System Market Size Overview. Ellicudate the one stage and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Global Cyber Security System, Market Size Overview. So download instantly and tailor it with your information.
-
 Host Intrusion Detection System For Security
Host Intrusion Detection System For SecurityThis slide highlights security benefits for host intrusion detection system. This further includes benefits such as evaluate traffic, threat intelligence and intrusion notification. Introducing our Host Intrusion Detection System For Security set of slides. The topics discussed in these slides are Evaluate Traffic, Threat Intelligence, Intrusion Notification. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 IOT Solution Components In Cyber Security System
IOT Solution Components In Cyber Security SystemThis slide highlights cyber security system components for IOT solutions. This includes secure device, secure communication, secured cloud and further includes messaging control and device integrated connections. Presenting our set of slides with IOT Solution Components In Cyber Security System. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Secure Device, Secure Communication, Secured Cloud.
-
 Strategies To Enhance Security System In Business
Strategies To Enhance Security System In BusinessThis slide highlights business security system enhancing key strategies. This further includes smart locks, alarm cameras and night safety platforms such as wireless alarms and improved access control. Introducing our premium set of slides with Strategies To Enhance Security System In Business. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Smart Locks, Alarm Cameras, Night Safety Platforms. So download instantly and tailor it with your information.
-
 Confidential Driven By Cloud And Security Initiatives Confidential Computing System Technology
Confidential Driven By Cloud And Security Initiatives Confidential Computing System TechnologyThis slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. Deliver an outstanding presentation on the topic using this Confidential Driven By Cloud And Security Initiatives Confidential Computing System Technology. Dispense information and present a thorough explanation of Confidential, Enterprise, Awareness using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Management System Workflow
Information Security Management System WorkflowThis slide represents the workflow that helps businesses to implement effective information security management system in organization. This workflow includes major phases , tasks and users responsible for each activity. Introducing our premium set of slides with Information Security Management System Workflow. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Develop ISMS, Document Policy Freme Work, Designate Internal Auditor. So download instantly and tailor it with your information.
-
 Roadmap To Implement Information Security Management System In Organization
Roadmap To Implement Information Security Management System In OrganizationThis slide represents roadmap that helps organizations implement system for information security management systems to protect sensitive data. It includes steps such as defining scope and objectives, identifying assets, recognizing risk, etc. Introducing our premium set of slides with Roadmap To Implement Information Security Management System In Organization. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Recognize Risk, Make Improvement, Identify Mitigation Measures. So download instantly and tailor it with your information.
-
 National Security Entry Exit Registration System In Powerpoint And Google Slides Cpb
National Security Entry Exit Registration System In Powerpoint And Google Slides CpbPresenting our National Security Entry Exit Registration System In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on National Security Entry Exit Registration System This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SS
Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SSThis slide exhibits IoT security best practices that help in addressing potential security weaknesses. It includes best practices such as network segmentation, IoT incident response plan, intrusion detection system, and patching and remediation. Increase audience engagement and knowledge by dispensing information using Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on four stages. You can also present information on Network Segmentation, Intrusion Detection System, Patching Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Digital Systems Engineering Creation Of Secure Networks Using Mbse Principles
Digital Systems Engineering Creation Of Secure Networks Using Mbse PrinciplesThe purpose of this slide is to explain how MBSE principles can be applied to create secure networks and align with the criteria and models of information security management systems. This slide also highlights the steps involved, such as plan, do, check, and act. Present the topic in a bit more detail with this Digital Systems Engineering Creation Of Secure Networks Using Mbse Principles. Use it as a tool for discussion and navigation on Techniques, Information, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Potential Threats Of Traditional Firewall Systems In Modern Network Security Firewall Virtualization
Potential Threats Of Traditional Firewall Systems In Modern Network Security Firewall VirtualizationThis slide highlights the various limitations of traditional firewall systems. The purpose of this slide is to outline the different issues of traditional firewalls. These include unable to prevent transfer of infected files, do not protect already compromised systems, etc. Deliver an outstanding presentation on the topic using this Potential Threats Of Traditional Firewall Systems In Modern Network Security Firewall Virtualization. Dispense information and present a thorough explanation of Harmful Websites, Non Technical Security, Security Rules using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Network Intrusion Prevention Cyber Security System
Network Intrusion Prevention Cyber Security SystemThis slide highlights the network intrusion prevention system cybersecurity. The purpose of this slide is to help ensure that suitable processes are undertaken during security incidents. It includes elements such as network perimeters, internet, LAN, etc. Introducing our Network Intrusion Prevention Cyber Security System set of slides. The topics discussed in these slides are Internet, Network Perimeter, Prevention Systems This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System
Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based SystemThis slide highlights the key functions within a cloud-based system in data security. The purpose of this slide is to outline the Process activities in a cloud-based system which include gathering, creating, retrieving data, etc. Introducing Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Tokenization Process Activities, Cloud Based System, Retrieving Data, using this template. Grab it now to reap its full benefits.
-
 Efficient Sales Processes With CRM Add Roles And Enable Security In CRM System CRP DK SS
Efficient Sales Processes With CRM Add Roles And Enable Security In CRM System CRP DK SSThis slide highlights the setting roles of new users and assigning roles, also highlights the enable security with field level and integration of lead generation with emails for contact management. Present the topic in a bit more detail with this Efficient Sales Processes With CRM Add Roles And Enable Security In CRM System CRP DK SS. Use it as a tool for discussion and navigation on Enable Security, Lead Generation, Emails For Contact Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 ATP Cyber Security System Process
ATP Cyber Security System ProcessThis slide showcases the ATP cyber security process. Its aim is to help define the target and identify the anomalies. This slide includes researching target, acquiring tools, detection of virus, strengthening the system, remove virus, etc. Presenting our set of slides with name ATP Cyber Security System Process. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Plan, Intrusion, Getting Out, Sub Zero.
-
 Securing Food Safety In Online Utilizing Food Delivery Management System
Securing Food Safety In Online Utilizing Food Delivery Management SystemThis slide covers utilizing food delivery management software to keep track of deliveries. It involves bill number, channel and estimated duration. Introducing Securing Food Safety In Online Utilizing Food Delivery Management System to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Bill Number, Channel, Customer Location, Estimated Duration, using this template. Grab it now to reap its full benefits.
-
 Physical Security System Protection Measures
Physical Security System Protection MeasuresThis slide showcases various layers that prevent unauthorized access and ensure security. The layers covered are deterrence, detection and access control. Presenting our set of slides with Physical Security System Protection Measures. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Deterrence, Detection, Access Control.
-
 Physical Security Systems To Enhance Data Safety
Physical Security Systems To Enhance Data SafetyThis slide showcases physical control systems to manage and safeguard crucial data. The systems covered are cable infrastructure, fire alarm, building management, etc. Introducing our premium set of slides with Physical Security Systems To Enhance Data Safety. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cable Infrastructure, Electronic Security Systems, Building Management. So download instantly and tailor it with your information.
-
 Data Analytics Importance In Identity And Access Management Securing Systems With Identity
Data Analytics Importance In Identity And Access Management Securing Systems With IdentityThis slide showcases the importance of Identity and Access Management based data analytics. The purpose of this slide is to explain the benefits, which are anomaly detection, account monitoring, policy violation detection, and so on. Increase audience engagement and knowledge by dispensing information using Data Analytics Importance In Identity And Access Management Securing Systems With Identity This template helps you present information on Five stages. You can also present information on Anomaly Detection, Identity Certification Campaigns using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Features Of Identity And Access Management Process Securing Systems With Identity
Features Of Identity And Access Management Process Securing Systems With IdentityThis slide discusses the Identity and Access Management features. The purpose of this slide is to explain the various features, including stored information authentication and authorization, external user registration, and so on. Present the topic in a bit more detail with this Features Of Identity And Access Management Process Securing Systems With Identity Use it as a tool for discussion and navigation on Stored Information, External User Registration This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Framework Of Identity And Access Management Process Securing Systems With Identity
Framework Of Identity And Access Management Process Securing Systems With IdentityThis slide discusses the Identity and Access Management framework. The purpose of this slide is to highlight the procedure that includes outlining how IAM architecture components work together, define user access to resources, and so on. Increase audience engagement and knowledge by dispensing information using Framework Of Identity And Access Management Process Securing Systems With Identity This template helps you present information on Eight stages. You can also present information on Employee Movements, Security Threat Reduction, Standard Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Historical Evolution Of Identity And Access Management Securing Systems With Identity
Historical Evolution Of Identity And Access Management Securing Systems With IdentityThis slide discusses the Identity and Access Management historical evolution. The purpose of this slide is to explain the historical background of IAM, including the historical roots of IAM, early IAM solutions, the role of tools, challenges with the directory, and so on. Introducing Historical Evolution Of Identity And Access Management Securing Systems With Identity to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Historical Roots Of Iam, Early Iam Solutions, Role Of Tools using this template. Grab it now to reap its full benefits.
-
 Identity And Access Management Introduction And Functions Securing Systems With Identity
Identity And Access Management Introduction And Functions Securing Systems With IdentityThis slide gives an overview of the Identity and Access Management process. The purpose of this slide is to explain the IAM and its functions in ensuring authentication, reporting, authorization, workflow, access management, and so on. Introducing Identity And Access Management Introduction And Functions Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Company Data And Resources, Streamline Workflows using this template. Grab it now to reap its full benefits.
-
 Steps To Implement Identity And Access Management In Enterprises Securing Systems With Identity
Steps To Implement Identity And Access Management In Enterprises Securing Systems With IdentityThis slide discusses the Identity and Access Management implementing process in enterprises. The purpose of this slide is to highlight the implementation process, including usage assessment, environment understanding, key IAM considerations, and so on. Introducing Steps To Implement Identity And Access Management In Enterprises Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Usage Assessment, Environment Understanding using this template. Grab it now to reap its full benefits.
-
 Steps To Implement Identity And Access Management Securing Systems With Identity
Steps To Implement Identity And Access Management Securing Systems With IdentityThis slide discusses the Identity and Access Management implementing program. The purpose of this slide is to highlight the implementation process of IAM, including scope identification, evaluating the right IAM approach, finding the best solution, and so on. Increase audience engagement and knowledge by dispensing information using Steps To Implement Identity And Access Management Securing Systems With Identity This template helps you present information on Six stages. You can also present information on Scope Identification, Define A Strategy, Assess Cost Factors using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Content For Securing Systems With Identity And Access Management
Table Of Content For Securing Systems With Identity And Access ManagementIncrease audience engagement and knowledge by dispensing information using Table Of Content For Securing Systems With Identity And Access Management This template helps you present information on One stages. You can also present information on Iam Overview, Training And Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Timeline To Implement Identity And Access Management Plan Securing Systems With Identity
Timeline To Implement Identity And Access Management Plan Securing Systems With IdentityThis slide shows the timeline for implementing the Identity and Access Management plan. The key steps include defining the project objective, identifying key stakeholders, determining compliance, integrating IAM with the existing system, etc. Introducing Timeline To Implement Identity And Access Management Plan Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Applications And Data, Public Cloud Platforms using this template. Grab it now to reap its full benefits.
-
 Best Practices For Secure Embedded Systems Mastering Embedded Systems Technology
Best Practices For Secure Embedded Systems Mastering Embedded Systems TechnologyThis slide showcases the best methods for developing secure embedded systems. The purpose of this slide is to showcase the best practices for building secure embedded systems, and these are securing boot, securing enclaves with Trusted Execution Environments TEE, implementing FOTA, etc. Present the topic in a bit more detail with this Best Practices For Secure Embedded Systems Mastering Embedded Systems Technology. Use it as a tool for discussion and navigation on Operating Systems In Market, Consumer Electronics, Industrial, Agriculture. This template is free to edit as deemed fit for your organization. Therefore download it now.




