Powerpoint Templates and Google slides for Prevents Attacks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Types Of Attacks Prevented By Cloud Cryptography Cloud Cryptography
Types Of Attacks Prevented By Cloud Cryptography Cloud CryptographyThis purpose of this slide is to explain how cloud cryptography can help prevent several types of attacks that can compromise the confidentiality, integrity, and availability of data in cloud environments. These include Man-in-the-middle MitM attacks, data breaches, insider attacks, etc. Increase audience engagement and knowledge by dispensing information using Types Of Attacks Prevented By Cloud Cryptography Cloud Cryptography. This template helps you present information on four stages. You can also present information on Data Breaches, Insider Attacks, Denial Of Service using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks Management
Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks ManagementThe following slide illustrates some best practices to execute preventive actions for cyber attacks. It includes elements such as train employees, updating systems and software, developing incident response plan, backing up data, maintaining compliance etc. Increase audience engagement and knowledge by dispensing information using Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks Management. This template helps you present information on six stages. You can also present information on Train Employees, Maintain Compliance, Develop Incident Response Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Techniques To Prevent Eclipse Attack And Secure Funds Hands On Blockchain Security Risk BCT SS V
Techniques To Prevent Eclipse Attack And Secure Funds Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some methods to minimize the adverse impact of eclipse attack on blockchain network and facilitate security features. It includes elements such as random node selection, deterministic node selection, increased node connections, new node restrictions, etc. Introducing Techniques To Prevent Eclipse Attack And Secure Funds Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Random Node Selection, Deterministic Node Selection, New Node Restrictions, using this template. Grab it now to reap its full benefits.
-
 Ways To Prevent Blockchain Routing Attacks Hands On Blockchain Security Risk BCT SS V
Ways To Prevent Blockchain Routing Attacks Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some methods to minimize blockchain routing attacks to safeguard network from wrong routing table. It includes elements such as strong passwords, updating firmware, managing access control lists, monitoring logs, etc. Increase audience engagement and knowledge by dispensing information using Ways To Prevent Blockchain Routing Attacks Hands On Blockchain Security Risk BCT SS V. This template helps you present information on four stages. You can also present information on Strong Passwords, Update Firmware, Monitor using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V
Blockchain And Cybersecurity Techniques To Prevent Eclipse Attack And Secure Funds BCT SS VThe following slide illustrates some methods to minimize the adverse impact of eclipse attack on blockchain network and facilitate security features. It includes elements such as random node selection, deterministic node selection, increased node connections, new node restrictions, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V This template helps you present information on Four stages. You can also present information on Increased Node Connections, Deterministic Node Selection, New Node Restrictions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Ways To Prevent Blockchain Routing Attacks BCT SS V
Blockchain And Cybersecurity Ways To Prevent Blockchain Routing Attacks BCT SS VThe following slide illustrates some methods to minimize blockchain routing attacks to safeguard network from wrong routing table. It includes elements such as strong passwords, updating firmware, managing access control lists, monitoring logs, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Ways To Prevent Blockchain Routing Attacks BCT SS V This template helps you present information on Four stages. You can also present information on Strong Passwords, Update Firmware, Manage Access Control List using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Practices For Preventing Social Engineering Attacks
Best Practices For Preventing Social Engineering AttacksThe purpose of this slide is to emphasize how best practices for preventing social engineering attacks bolster security through awareness, education, and technical measures. Presenting our set of slides with Best Practices For Preventing Social Engineering Attacks. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Password Security, Penetration Testing, Employee Training.
-
 Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V
Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS VThe following slide illustrates some methods to minimize the adverse impact of eclipse attack on blockchain network and facilitate security features. It includes elements such as random node selection, deterministic node selection, increased node connections, new node restrictions, etc. Introducing Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Mining Capability, Mining Capabilities, Much Faster Rate using this template. Grab it now to reap its full benefits.
-
 Cyber Threats In Blockchain Ways To Prevent Blockchain Routing Attacks BCT SS V
Cyber Threats In Blockchain Ways To Prevent Blockchain Routing Attacks BCT SS VThe following slide illustrates some methods to minimize blockchain routing attacks to safeguard network from wrong routing table. It includes elements such as strong passwords, updating firmware, managing access control lists, monitoring logs, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Ways To Prevent Blockchain Routing Attacks BCT SS V This template helps you present information on Four stages. You can also present information on Blockchain Routing Attacks, Strong Passwords, Manage Access Control List using this PPT design. This layout is completely editable so personaize it now
-
 5G Cybersecurity Icon For Preventing Digital Attacks
5G Cybersecurity Icon For Preventing Digital AttacksIntroducing our 5G Cybersecurity Icon For Preventing Digital Attacks set of slides. The topics discussed in these slides are Preventing, Digital, Cybersecurity. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Best Practices To Prevent Cyber Attacks Implementing Cyber Risk Management Process
Best Practices To Prevent Cyber Attacks Implementing Cyber Risk Management ProcessThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti-virus, preventing to open suspicious emails, keeping systems up-to date etc. Introducing Best Practices To Prevent Cyber Attacks Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Utilize Anti Virus, Prevent Opening Suspicious, Leverage Firewalls, using this template. Grab it now to reap its full benefits.
-
 Ransomware In Digital Age Crypto Ransomware Attack Overview And Prevention
Ransomware In Digital Age Crypto Ransomware Attack Overview And PreventionThis slide highlights the type of ransomware attack, crypto or encrypting . The purpose of this slide is to explain the infection techniques and discuss prevention measures, such as installing antivirus software and enabling two-factor authentication. Increase audience engagement and knowledge by dispensing information using Ransomware In Digital Age Crypto Ransomware Attack Overview And Prevention. This template helps you present information on six stages. You can also present information on Crypto Ransomware Attack, Installing Antivirus Software, Infection Techniques using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ransomware In Digital Age Locker Ransomware Attack Overview And Prevention
Ransomware In Digital Age Locker Ransomware Attack Overview And PreventionThis slide highlights the type of ransomware attack, Locker. The purpose of this slide is to explain the infection techniques used by attackers and discussed prevention measures, such as be cautious when browsing the internet, always down. Increase audience engagement and knowledge by dispensing information using Ransomware In Digital Age Locker Ransomware Attack Overview And Prevention. This template helps you present information on five stages. You can also present information on Spam Email, Ransom Paid Through Cryptocurrency, Victim Computer Locked, Attachment Downloaded using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ransomware In Digital Age Mobile Ransomware Attack Overview And Prevention
Ransomware In Digital Age Mobile Ransomware Attack Overview And PreventionThis slide highlights the type of ransomware attack, Mobile. The purpose of this slide is to explain the infection methods used by attackers and discussed prevention measures, such as use add blocker, enable auto update of software and don not use unsecure website. Introducing Ransomware In Digital Age Mobile Ransomware Attack Overview And Prevention to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Install Antivirus Software, Avoid Clicking On Suspicious Links, Developing Malware, Infect Mobile Devices, using this template. Grab it now to reap its full benefits.
-
 Ransomware In Digital Age RACI Matrix For Ransomware Attacks Prevention Strategy
Ransomware In Digital Age RACI Matrix For Ransomware Attacks Prevention StrategyThis slide showcases a RACI matrix for the ransomware prevention plan, outlining the appropriate roles and steps to be taken during a ransomware attack. It includes tasks such as incident registration, conduct initial triage, and classification assignment etc. Present the topic in a bit more detail with this Ransomware In Digital Age RACI Matrix For Ransomware Attacks Prevention Strategy. Use it as a tool for discussion and navigation on Ransomware Attacks, Prevention Strategy, Classification Assignment, Conduct Initial Triage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ransomware In Digital Age Ransomware Attack Prevention Tools And Software
Ransomware In Digital Age Ransomware Attack Prevention Tools And SoftwareThis slide highlights the best tools and software for preventing ransomware attacks, which involve anti-ransomware software and tools like Bitdefender Antivirus Plus and Kaspersky anti-ransomware tool. These powerful tools have the potential to effectively halt ransomware attacks. Deliver an outstanding presentation on the topic using this Ransomware In Digital Age Ransomware Attack Prevention Tools And Software. Dispense information and present a thorough explanation of Bitdefender Antivirus Plus, Kaspersky Anti Ransomware Tool, Malwarebytes Anti Malware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ransomware In Digital Age Scareware Ransomware Attack Overview And Prevention
Ransomware In Digital Age Scareware Ransomware Attack Overview And PreventionThis slide presents the type of ransomware attack, Scareware. The purpose of this slide is to explain the infection mechanism used by attackers and discussed prevention measures, such as installing pop-up blocker and enabling two-way authentication. Deliver an outstanding presentation on the topic using this Ransomware In Digital Age Scareware Ransomware Attack Overview And Prevention. Dispense information and present a thorough explanation of Prevention Measures, Infection Mechanism, Scareware Ransomware Attack using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SAP Security Measures To Prevent Cyber Attacks
SAP Security Measures To Prevent Cyber AttacksPresenting our set of slides with SAP Security Measures To Prevent Cyber Attacks. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on SAP Security, Measures To Prevent, Cyber Attacks.
-
 Firewall Network Security Firewall Features To Effectively Prevent Cyber Attacks
Firewall Network Security Firewall Features To Effectively Prevent Cyber AttacksThis slide outlines the primary characteristics a firewall should have to prevent cyber attacks on a network. The purpose of this slide is to showcase the different features that a firewall should possess, including scalable performance, unified security management, threat prevention, and so on. Introducing Firewall Network Security Firewall Features To Effectively Prevent Cyber Attacks to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on URL Categories By Traffic, Traffic Source IP, Traffic Desintation IP using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Security Measures To Prevent Phishing Attacks
Ethical Hacking And Network Security Security Measures To Prevent Phishing AttacksThis slide represents the security measures to prevent phishing attacks, such as using the spam filter, updating security software regularly, utilization of multi-factor authentication, and so on. Introducing Ethical Hacking And Network Security Security Measures To Prevent Phishing Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Phishing Attacks, Spam Filter, Updating Security Software Regularly, Utilization Of Multi Factor Authentication, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Infrastructure Icon To Prevent Malware Attacks
Cybersecurity Infrastructure Icon To Prevent Malware AttacksIntroducing our premium set of slides with Cybersecurity Infrastructure Icon To Prevent Malware Attacks Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cybersecurity Infrastructure, Icon To Prevent, Malware Attacks So download instantly and tailor it with your information.
-
 Tips To Prevent Social Engineering Attacks
Tips To Prevent Social Engineering AttacksThe purpose of this slide is to highlight how tips for preventing social engineering attacks empower individuals and organizations to recognize, resist, and mitigate threats, enhancing cybersecurity. Introducing our premium set of slides with Tips To Prevent Social Engineering Attacks. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Email Security, Authentication Practices, Beware Of Offers. So download instantly and tailor it with your information.
-
 Agenda For Social Engineering Attacks Prevention For Businesses
Agenda For Social Engineering Attacks Prevention For BusinessesIntroducing Agenda For Social Engineering Attacks Prevention For Businesses to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering Attack, Prevention For Businesses, Social Engineering Lifecycle, Social Engineering Techniques, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Social Engineering Attacks Prevention For Businesses
Icons Slide For Social Engineering Attacks Prevention For BusinessesPresenting our well crafted Icons Slide For Social Engineering Attacks Prevention For Businesses set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
 Social Engineering Attacks Overview And Types Social Engineering Attacks Prevention
Social Engineering Attacks Overview And Types Social Engineering Attacks PreventionThis slide discusses about social engineering process of manipulating victims to provide access to their confidential information. This slide also outlines the types of social engineering attacks, such as phishing, pretexting, baiting, tailgating, impersonation, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Overview And Types Social Engineering Attacks Prevention. This template helps you present information on five stages. You can also present information on Quid Pro Quo Attack, Watering Hole Attack, Tailgating, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention 30 60 90 Days Plan To Implement Social Engineering
Social Engineering Attacks Prevention 30 60 90 Days Plan To Implement Social EngineeringThis slide represents 30-60-90 plan to protect companies and their employees from social engineering attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Introducing Social Engineering Attacks Prevention 30 60 90 Days Plan To Implement Social Engineering to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Simulation Test, Implement Continuous Monitoring, Third Party Risk Assessment, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention About Anti Phishing Solutions Types And Benefits
Social Engineering Attacks Prevention About Anti Phishing Solutions Types And BenefitsThis slide highlights the services available for social engineering prevention, such as browser-based, email-based and API-based. This slide also outlines the benefits of these services. These include risk identification, damage control, zero-trust security, etc. Present the topic in a bit more detail with this Social Engineering Attacks Prevention About Anti Phishing Solutions Types And Benefits. Use it as a tool for discussion and navigation on Reduce Cybersecurity Attacks, Zero Trust Security, Deliver Operational Efficiency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Attacks Prevention Best Practices For Social Engineering Awareness Campaign
Social Engineering Attacks Prevention Best Practices For Social Engineering Awareness CampaignThis slide talks about the measures for successful social engineering awareness campaign. These include recognize phish, train staff while keeping their individual needs in mind, action-oriented employee engagement, plan constant training sessions, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Best Practices For Social Engineering Awareness Campaign. This template helps you present information on six stages. You can also present information on Plan Constant Training Sessions, Evaluate Training Outcomes, Consumable Tidbits Of Knowledge, Action Oriented Employee Engagement using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Business Benefits Of Comprehensive Training Programs
Social Engineering Attacks Prevention Business Benefits Of Comprehensive Training ProgramsThis slide outlines the benefits of comprehensive training programs in organizations. These include align with company database, instructional library, auto-enrolment service, inform about real risks, track and evaluate and plan a year ahead. Introducing Social Engineering Attacks Prevention Business Benefits Of Comprehensive Training Programs to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Track And Evaluate, Instructional Library, Comprehensive Training Programs, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Checklist To Secure Organizations From Social Engineering
Social Engineering Attacks Prevention Checklist To Secure Organizations From Social EngineeringThis slide outlines the steps to be taken to protect the organization and its employees from social engineering attacks. The key approaches include provide staff training, update software, enable MFA and spam filters, implement real-time monitoring and develop an incident plan. Present the topic in a bit more detail with this Social Engineering Attacks Prevention Checklist To Secure Organizations From Social Engineering. Use it as a tool for discussion and navigation on Provide Staff Training, Multi Factor Authentication, Develop An Incident Response Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Attacks Prevention Common Attack Vectors For Social Engineering
Social Engineering Attacks Prevention Common Attack Vectors For Social EngineeringThis slide outlines the different components which result in successful social engineering attacks. These are software vulnerabilities, compromised credentials, weak passwords, malicious employees, poor encryption, ransomware, phishing, etc. Introducing Social Engineering Attacks Prevention Common Attack Vectors For Social Engineering to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Software Vulnerabilities, Compromised Credentials, Malicious Employees, Weak Passwords, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Comparison Of Different Anti-Phishing Solutions Providers
Social Engineering Attacks Prevention Comparison Of Different Anti-Phishing Solutions ProvidersThis slide compares the different anti-phishing solutions available in the market. It highlights the type of support provided, price and rating of various solutions. This slide also outlines the final service selection and the reasons supporting it. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Comparison Of Different Anti-Phishing Solutions Providers. Dispense information and present a thorough explanation of Anti Phishing Solutions, Final Service Selection, Reasons Supporting, Abnormal Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Attacks Prevention Components Of Social Engineering Life Cycle
Social Engineering Attacks Prevention Components Of Social Engineering Life CycleThis slide represents the life cycle of the social engineering process. The main steps included are ground preparation for the attack, deceiving the victim to achieve a foothold, collecting the data over time, and closing the interaction without any suspicion. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Components Of Social Engineering Life Cycle. This template helps you present information on four stages. You can also present information on Ground Preparation For Attack, Collecting The Information, Social Engineering Life Cycle, Taking Control Of The Conversation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Different Types Of Social Engineering Attacks
Social Engineering Attacks Prevention Different Types Of Social Engineering AttacksThis slide represents the different types of social engineering attacks based on technology and human interaction. These two types are further divided into components such as mobile-based, computer-based, voice-based, physical mode, etc. Introducing Social Engineering Attacks Prevention Different Types Of Social Engineering Attacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering Attacks, Physical Mode, Technology And Human Interaction, Email Phishing, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention For Businesses For Table Of Contents
Social Engineering Attacks Prevention For Businesses For Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention For Businesses For Table Of Contents. This template helps you present information on one stages. You can also present information on Resources And Training, Awareness Training Program, Training Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Human Based Social Engineering Attacks
Social Engineering Attacks Prevention Human Based Social Engineering AttacksThis slide discusses the different human-based techniques used by social engineering scammers. These attacks include impersonation, tailgating, baiting, pretexting, quid pro quo attacks, reverse social engineering and dumpster diving. Present the topic in a bit more detail with this Social Engineering Attacks Prevention Human Based Social Engineering Attacks. Use it as a tool for discussion and navigation on Reverse Social Engineering, Dumpster Diving, Social Engineering Attacks, Fraudulent Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Attacks Prevention Important Traits Of Social Engineering Attacks
Social Engineering Attacks Prevention Important Traits Of Social Engineering AttacksThe purpose of this slide is to outline the significant traits of a social engineering scam. The main points discussed in this slide are urgency, believability, trust, and heightened emotions such as fear, excitement, curiosity, sadness, guilt, etc. Introducing Social Engineering Attacks Prevention Important Traits Of Social Engineering Attacks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Time Sensitive Opportunities, Believability, Heightened Emotions, Manipulated Emotions, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Main Goals Of Social Engineering Attackers
Social Engineering Attacks Prevention Main Goals Of Social Engineering AttackersThis slide highlights the motive of the scammers behind the social engineering attacks. The two primary goals discussed in this slide are disruption and theft. This slide also outlines several examples, such as ransomware, phishing attacks, impersonation, etc. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Main Goals Of Social Engineering Attackers. Dispense information and present a thorough explanation of Social Engineering Attackers, Phishing Attacks, Distributed Denial Of Service, Aims To Corrupt Data Or Systems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Attacks Prevention Ontological Model Of Social Engineering Attack
Social Engineering Attacks Prevention Ontological Model Of Social Engineering AttackThe purpose of this slide is to represent the model of a social engineering attack which consists of several components. The major points depicted in this slide are social engineer, medium, goal, target, compliance principles, techniques, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Ontological Model Of Social Engineering Attack. This template helps you present information on six stages. You can also present information on Direct Communication, Bidirectional Communication, Unidirectional Communication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Red Flags Of A Social Engineering Attack
Social Engineering Attacks Prevention Red Flags Of A Social Engineering AttackThis slide highlights the signs of a social engineering attack. The purpose of this slide is to outline the various symptoms of cyber attack, such as strange messages from a friend, arouse emotions, create a sense of urgency, tempting offers, etc. Introducing Social Engineering Attacks Prevention Red Flags Of A Social Engineering Attack to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering Attack, Arouse Emotions, Arouse Emotions Like Fear, Arouse Emotions, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Resources And Training Provided To Employees In Organization
Social Engineering Attacks Prevention Resources And Training Provided To Employees In OrganizationThis slide demonstrates the resources and training that can be provided by companies to their staff. These include employee training, check to see if you have already been breached, be aware of the various phishing attacks, invest in security education, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Resources And Training Provided To Employees In Organization. This template helps you present information on five stages. You can also present information on Invest In Security Education, Invest In Password, Employee Training, Phishing Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Roadmap To Implement Social Engineering Prevention Strategies
Social Engineering Attacks Prevention Roadmap To Implement Social Engineering Prevention StrategiesThis slide represents the roadmap to prevent social engineering attacks in organizations. The key steps include conduct a baseline security assessment, employee training, implement technical controls, establish policies and procedures, etc. Introducing Social Engineering Attacks Prevention Roadmap To Implement Social Engineering Prevention Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Establish Policies And Procedures, Implement Technical Controls, Social Engineering Prevention Strategies, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Sciences Involved In Targeting Humans In Modern Social
Social Engineering Attacks Prevention Sciences Involved In Targeting Humans In Modern SocialThis slide highlights the key sciences involved in the process of modern social engineering. These are psychology, pedagogy, cognitive sciences, psychiatry, marketing, communication sciences, philosophy, normative processes, organizational sociology, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Sciences Involved In Targeting Humans In Modern Social. This template helps you present information on thirteen stages. You can also present information on Modern Social Engineering, Psychology, Pedagogy, Cognitive Sciences, Psychiatry, Marketing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Social Engineering Awareness Training Program For Employees
Social Engineering Attacks Prevention Social Engineering Awareness Training Program For EmployeesThis slide represents the training program for employees which will help them to prevent various cyber security scams in business. The purpose of this slide is to outline the mode, venue and schedule for the different training programs. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Social Engineering Awareness Training Program For Employees. Dispense information and present a thorough explanation of Social Engineering Awareness, Training Program For Employees, Training Programs, Cyber Security Scams using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Attacks Prevention Social Engineering Classification Chart Overview
Social Engineering Attacks Prevention Social Engineering Classification Chart OverviewIntroducing Social Engineering Attacks Prevention Social Engineering Classification Chart Overview to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering, Ingratiation, Instant Messaging, Waste Threats Management, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Social Engineering Methods Used By Attackers
Social Engineering Attacks Prevention Social Engineering Methods Used By AttackersThis slide demonstrates the popular procedures for conducting social engineering scams. These methods of performing social engineering attacks are phone calls, in-person interactions, tailgating, persuasion through third-party applications, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Social Engineering Methods Used By Attackers. This template helps you present information on four stages. You can also present information on Guide Them To Phishing Websites, Attackers Call Targets, Scammers Act As Employees, Fictitious Positions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Social Engineering Prevention Strategies For Safe Network Use
Social Engineering Attacks Prevention Social Engineering Prevention Strategies For Safe Network UseThis slide represents the protective measures for users to practice safe networking. The best practices mentioned in this slide are restrict others from connecting to primary wi-fi network, use a VPN, security of network-connected devices, etc. Introducing Social Engineering Attacks Prevention Social Engineering Prevention Strategies For Safe Network Use to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Practice Safe Networking, Primary Wifi Network, Security Of Network Connected Devices, Social Engineering Prevention Strategies, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Step By Step Process Of Social Engineering Awareness Program
Social Engineering Attacks Prevention Step By Step Process Of Social Engineering Awareness ProgramThis slide demonstrates the working of cyber security awareness training programs for organizations. These include start with employee training, make fictitious cyber attack campaigns, reinforce the awareness training and track progress and upgrade. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Step By Step Process Of Social Engineering Awareness Program. This template helps you present information on four stages. You can also present information on Awareness Training Program, Cyber Attack Campaigns, Start With Employee Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Technology Based Social Engineering Attacks
Social Engineering Attacks Prevention Technology Based Social Engineering AttacksThis slide discusses the different technology-based techniques used by social engineering scammers. These attacks include phishing, vishing, smishing, watering hole attacks, man-in-the-middle attacks, scareware and angler phishing. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Technology Based Social Engineering Attacks. Dispense information and present a thorough explanation of Watering Hole Attacks, Social Engineering Attacks, Angler Phishing, Fraudsters Fake Trusted Phone using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
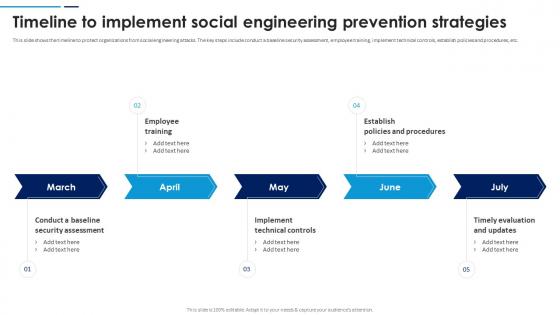 Social Engineering Attacks Prevention Timeline To Implement Social Engineering Prevention Strategies
Social Engineering Attacks Prevention Timeline To Implement Social Engineering Prevention StrategiesThis slide shows the timeline to protect organizations from social engineering attacks. The key steps include conduct a baseline security assessment, employee training, implement technical controls, establish policies and procedures, etc. Introducing Social Engineering Attacks Prevention Timeline To Implement Social Engineering Prevention Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Establish Policies And Procedures, Timely Evaluation And Updates, Implement Technical Controls, Employee Training, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Understanding Social Engineering Threat Landscape
Social Engineering Attacks Prevention Understanding Social Engineering Threat LandscapeThis slide shows the threat landscape for social engineering. The key components included are email, social media and the internet, trends, criminal groups, malicious insiders, and attack vectors such as physical on-site attacks, mobile, network, cloud, etc. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Understanding Social Engineering Threat Landscape. Dispense information and present a thorough explanation of Social Media And Internet, Social Engineering Threat Landscape, Search Result Poisoning using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Prevention Strategies For Safe Communication Social Engineering Attacks Prevention
Social Engineering Prevention Strategies For Safe Communication Social Engineering Attacks PreventionThis slide discusses several social engineering mitigation techniques. These include avoid clicking on links in emails and texts, use multi-factor authentication, select strong passwords, avoid sharing personal information, beware of internet friendships, etc. Introducing Social Engineering Prevention Strategies For Safe Communication Social Engineering Attacks Prevention to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering Prevention, Strategies For Safe Communication, Multi Factor Authentication, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Prevention Strategies For Safe Device Usage Social Engineering Attacks Prevention
Social Engineering Prevention Strategies For Safe Device Usage Social Engineering Attacks PreventionThe purpose of this slide is to represent the best practices for safe device usage. These safety measures include internet security software, never leave devices unsecured in public places, keep software updated and inspect all internet accounts. Increase audience engagement and knowledge by dispensing information using Social Engineering Prevention Strategies For Safe Device Usage Social Engineering Attacks Prevention. This template helps you present information on four stages. You can also present information on Internet Security Software, Keep Software Updated, Inspect All Internet Accounts, Devices Unsecured In Public using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Social Engineering Attacks Prevention For Businesses
Table Of Contents For Social Engineering Attacks Prevention For BusinessesIntroducing Table Of Contents For Social Engineering Attacks Prevention For Businesses to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Lifecycle And Process, Social Engineering Introduction, Attack Targets And Vectors, Statistics Of Social Engineering Scams, using this template. Grab it now to reap its full benefits.
-
 Techniques To Prevent Eclipse Attack And Secure Funds Guide For Blockchain BCT SS V
Techniques To Prevent Eclipse Attack And Secure Funds Guide For Blockchain BCT SS VThe following slide illustrates some methods to minimize the adverse impact of eclipse attack on blockchain network and facilitate security features. It includes elements such as random node selection, deterministic node selection, increased node connections, new node restrictions, etc. Introducing Techniques To Prevent Eclipse Attack And Secure Funds Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Random Node Selection, Deterministic Node Selection using this template. Grab it now to reap its full benefits.
-
 Ways To Prevent Blockchain Routing Attacks Guide For Blockchain BCT SS V
Ways To Prevent Blockchain Routing Attacks Guide For Blockchain BCT SS VThe following slide illustrates some methods to minimize blockchain routing attacks to safeguard network from wrong routing table. It includes elements such as strong passwords, updating firmware, managing access control lists, monitoring logs, etc. Increase audience engagement and knowledge by dispensing information using Ways To Prevent Blockchain Routing Attacks Guide For Blockchain BCT SS V This template helps you present information on four stages. You can also present information on Strong Passwords, Update Firmware, Monitor using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Practices To Prevent Cyber Attacks Cyber Risk Assessment
Best Practices To Prevent Cyber Attacks Cyber Risk AssessmentThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti-virus, preventing to open suspicious emails, keeping systems up-to date etc. Introducing Best Practices To Prevent Cyber Attacks Cyber Risk Assessment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Opening, Suspicious Emails, Leverage Firewalls using this template. Grab it now to reap its full benefits.
-
 Types Of Attacks Prevented By Data Encryption Encryption For Data Privacy In Digital Age It
Types Of Attacks Prevented By Data Encryption Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to highlight the major attacks avoided by utilizing data encryption techniques. These attacks are eavesdropping, sniffing, Man-in-the-Middle attacks, data breaches, data tampering or modification, and insider attacks. Deliver an outstanding presentation on the topic using this Types Of Attacks Prevented By Data Encryption Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Data Tampering, Data Breaches, Insider Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Best Practices To Prevent Cyber Attacks Creating Cyber Security Awareness
Best Practices To Prevent Cyber Attacks Creating Cyber Security AwarenessThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti-virus, preventing to open suspicious emails, keeping systems up-to date etc. Introducing Best Practices To Prevent Cyber Attacks Creating Cyber Security Awareness to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Opening Suspicious Emails, Leverage Firewalls using this template. Grab it now to reap its full benefits.
-
 Security Incident Icon To Prevent Cyber Attacks
Security Incident Icon To Prevent Cyber AttacksPresenting our set of slides with Security Incident Icon To Prevent Cyber Attacks. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Incident, Prevent Cyber Attacks.





