Powerpoint Templates and Google slides for It Threat
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyberterrorism it types of trojans misused in cyber terrorism ppt slides tips
Cyberterrorism it types of trojans misused in cyber terrorism ppt slides tipsThis slide describes the types of trojans misused in cyber terrorism, such as downloader trojan, spyware, backdoor trojan, and rootkit trojans. Introducing Cyberterrorism IT Types Of Trojans Misused In Cyber Terrorism Ppt Slides Tips to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Downloader Trojan, Backdoor Trojan, Spyware, Rootkit Trojans, using this template. Grab it now to reap its full benefits.
-
 Table of contents for cyber terrorism cyberterrorism it ppt slides tools
Table of contents for cyber terrorism cyberterrorism it ppt slides toolsPresent the topic in a bit more detail with this Table Of Contents For Cyber Terrorism Cyberterrorism IT Ppt Slides Tools. Use it as a tool for discussion and navigation on Current Scenario Company, Elements Cyber Terrorism, Preventive Measures, Against Cyber Terrorism Tools, Steps To Mitigate Cyber Terrorism, Tools Misused Cyber Terrorism, Current Situation Around Globe. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Improve it security with vulnerability management threat intelligence services
Improve it security with vulnerability management threat intelligence servicesThis slide covers the threat intelligence services such as global intelligence, local intelligence, and other effective threat detection services. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Threat Intelligence Services. This template helps you present information on three stages. You can also present information on Global Intelligence, Local Intelligence, Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine phases of threat attack disrupting it project safety enhancing overall project security it
Determine phases of threat attack disrupting it project safety enhancing overall project security itThis slide provides information regarding various phases for threat attack disrupting IT project safety in terms of reconnaissance, weaponization, delivery and exploitation. Introducing Determine Phases Of Threat Attack Disrupting It Project Safety Enhancing Overall Project Security It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reconnaissance, Weaponization, Exploitation, using this template. Grab it now to reap its full benefits.
-
 Enhancing overall project security it addressing various threats affecting it project safety
Enhancing overall project security it addressing various threats affecting it project safetyThis slide provides information regarding various IT threats existing at workplace disrupting IT project safety such as general and criminal IT threats. Deliver an outstanding presentation on the topic using this Enhancing Overall Project Security It Addressing Various Threats Affecting It Project Safety. Dispense information and present a thorough explanation of Service, Operations, Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enhancing overall project security it comparative assessment of various threat agents affecting
Enhancing overall project security it comparative assessment of various threat agents affectingThis slide provides information regarding comparative assessment of different threat agents impacting IT project safety comparing on various parameters such as data loss impact, skills required to handle threat, etc. Present the topic in a bit more detail with this Enhancing Overall Project Security It Comparative Assessment Of Various Threat Agents Affecting. Use it as a tool for discussion and navigation on Assessment, Operations, Maintenance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enhancing overall project security it contingency plan for managing threats to ensure
Enhancing overall project security it contingency plan for managing threats to ensureThis slide provides information regarding contingency plan for managing threats to ensure IT project safety with aid of technical equipment ensuring contingency plans. Deliver an outstanding presentation on the topic using this Enhancing Overall Project Security It Contingency Plan For Managing Threats To Ensure. Dispense information and present a thorough explanation of Contingency Plan For Managing Threats To Ensure IT Project Safety using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enhancing overall project security it determine phases of threat attack disrupting project safety contd
Enhancing overall project security it determine phases of threat attack disrupting project safety contdThis slide provides information regarding various phases for threat attack disrupting IT project safety in terms of installation, command and control, actions and objectives, covering tracks. Introducing Enhancing Overall Project Security It Determine Phases Of Threat Attack Disrupting Project Safety Contd to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Command And Control, Actions And Objectives, Covering Tracks, using this template. Grab it now to reap its full benefits.
-
 Insider Threat Discovery Flowchart Of It Company
Insider Threat Discovery Flowchart Of It CompanyThis slide shows information technology company flowchart indicating insider threat discovery. It provides information such as user request for service, authentication check, starting session, role based access control RBAC, permission checks, etc. Presenting our set of slides with name Insider Threat Discovery Flowchart Of It Company. This exhibits information on one stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Application Service, End Session, Start Session, Allow Access, Terminate Session.
-
 Most Effective It Security Tools For Protection Against Insider Threat
Most Effective It Security Tools For Protection Against Insider ThreatThis slide shows most effective IT security tools for protection against insider threats. It provides information about data loss prevention DLP, user and entity behavior UEBA, identity and access management IAM and security information and event management SIEM Introducing our premium set of slides with Most Effective It Security Tools For Protection Against Insider Threat. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Loss Prevention, User Entity Behavior, Identity Access Management. So download instantly and tailor it with your information.
-
 IT Risk Management Strategies Classification Of IT Risks With Threats
IT Risk Management Strategies Classification Of IT Risks With ThreatsThis slide highlights the classification of information technology risks which includes technology, security, political and legal, personnel, and infrastructure with key threats. Present the topic in a bit more detail with this IT Risk Management Strategies Classification Of IT Risks With Threats. Use it as a tool for discussion and navigation on Technology, Security, Political And Legal. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IT Security Threat Mitigation Strategies
IT Security Threat Mitigation StrategiesThe slide covers strategies to prevent IT security threats for reducing overall impact of risks or attacks on business. It includes four strategies such as risk assessment, network access control, incident response plan and regular network traffic monitoring Introducing our premium set of slides with IT Security Threat Mitigation Strategies. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk Assessment, Network Access Controls, Incident Response Plan, Regular Network Traffic Monitoring. So download instantly and tailor it with your information.
-
 IT Risk Management Strategies Information Technology Risks Form Human Threat Source
IT Risk Management Strategies Information Technology Risks Form Human Threat SourceThis slide highlights the IT risks form human threat source which includes hacker, computer criminal, terrorist, insiders and industrial espionage with threat description and threat actions. Present the topic in a bit more detail with this IT Risk Management Strategies Information Technology Risks Form Human Threat Source. Use it as a tool for discussion and navigation on Computer Criminal, Terrorist, Industrial Espionage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IT Risk Management Strategies IT Vulnerabilities With Threat Source And Action
IT Risk Management Strategies IT Vulnerabilities With Threat Source And ActionThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this IT Risk Management Strategies IT Vulnerabilities With Threat Source And Action. Use it as a tool for discussion and navigation on Vulnerabilities, Threat Source, Threat Action. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation Plan
IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation PlanThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Increase audience engagement and knowledge by dispensing information using IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation Plan. This template helps you present information on one stages. You can also present information on Threat, Risk, Risk Priority, Risk Reduction Timeline using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise Risk Management Classification Of IT Risks With Threats
Enterprise Risk Management Classification Of IT Risks With ThreatsThis slide highlights the classification of information technology risks which includes technology, security, political and legal, personnel, and infrastructure with key threats. Present the topic in a bit more detail with this Enterprise Risk Management Classification Of IT Risks With Threats. Use it as a tool for discussion and navigation on Technology, Security, Political And Legal. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise Risk Management IT Vulnerabilities With Threat Source And Action
Enterprise Risk Management IT Vulnerabilities With Threat Source And ActionThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this Enterprise Risk Management IT Vulnerabilities With Threat Source And Action. Use it as a tool for discussion and navigation on Vulnerabilities, Threat Source, Threat Action. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Classification Of IT Risks With Threats Risk Management Guide For Information Technology Systems
Classification Of IT Risks With Threats Risk Management Guide For Information Technology SystemsThis slide highlights the classification of information technology risks which includes technology, security, political and legal, personnel, and infrastructure with key threats. Present the topic in a bit more detail with this Classification Of IT Risks With Threats Risk Management Guide For Information Technology Systems. Use it as a tool for discussion and navigation on Technology, Security, Political And Legal. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology Systems
IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology SystemsThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology Systems. Use it as a tool for discussion and navigation on Vulnerabilities, Threat Source, Threat Action. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
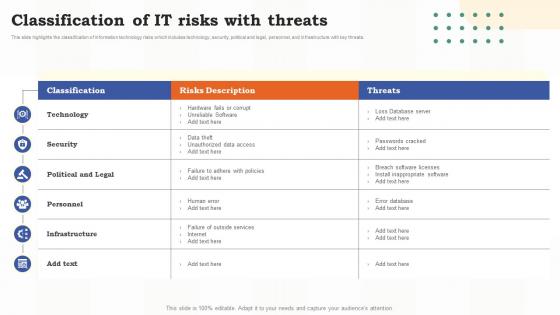 Classification Of It Risks With Threats Risk Assessment Of It Systems Ppt Slides Backgrounds
Classification Of It Risks With Threats Risk Assessment Of It Systems Ppt Slides BackgroundsThis slide highlights the classification of information technology risks which includes technology, security, political and legal, personnel, and infrastructure with key threats. Present the topic in a bit more detail with this Classification Of It Risks With Threats Risk Assessment Of It Systems Ppt Slides Backgrounds. Use it as a tool for discussion and navigation on Technology, Political And Legal, Infrastructure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Technology Risks Form Human Threat Source Risk Assessment Of It Systems
Information Technology Risks Form Human Threat Source Risk Assessment Of It SystemsThis slide highlights the IT risks form human threat source which includes hacker, computer criminal, terrorist, insiders and industrial espionage with threat description and threat actions. Present the topic in a bit more detail with this Information Technology Risks Form Human Threat Source Risk Assessment Of It Systems. Use it as a tool for discussion and navigation on Information, Technology, Source. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It Vulnerabilities With Threat Source And Action Risk Assessment Of It Systems Ppt Slides Introduction
It Vulnerabilities With Threat Source And Action Risk Assessment Of It Systems Ppt Slides IntroductionThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this It Vulnerabilities With Threat Source And Action Risk Assessment Of It Systems Ppt Slides Introduction. Use it as a tool for discussion and navigation on Vulnerabilities, Source, Information Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems
Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems. Use it as a tool for discussion and navigation on Mitigation Plan, Prioritized, Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It Security Threat And Weakness Analysis
It Security Threat And Weakness AnalysisThe following slide highlights the IT security assessment to verify the safety status of assets and networks. It includes elements such as threats, weakness, impact and level of risk, current and proposed controls etc. Introducing our premium set of slides with It Security Threat And Weakness Analysis. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk, Threats, Weakness. So download instantly and tailor it with your information.
-
 It threat intelligence ppt powerpoint presentation ideas images cpb
It threat intelligence ppt powerpoint presentation ideas images cpbPresenting this set of slides with name IT Threat Intelligence Ppt Powerpoint Presentation Ideas Images Cpb. This is an editable Powerpoint three stages graphic that deals with topics like IT Threat Intelligence to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Risk Management Plan To Manage Cyber Threats Guide To Build It Strategy Plan For Organizational Growth
Risk Management Plan To Manage Cyber Threats Guide To Build It Strategy Plan For Organizational GrowthThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Deliver an outstanding presentation on the topic using this Risk Management Plan To Manage Cyber Threats Guide To Build It Strategy Plan For Organizational Growth. Dispense information and present a thorough explanation of Management, Information, Vulnerability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Addressing Threat Management Team Training Schedule Managing IT Threats At Workplace Overview
Addressing Threat Management Team Training Schedule Managing IT Threats At Workplace OverviewThe threat management team needs to have strong critical and creative thinking skills so that they become capable in taking key decisions without complete or conflicting information under immense tensed situations. The team will be trained by experts who will also use scenario based activities and costing will be per employee basis. Present the topic in a bit more detail with this Addressing Threat Management Team Training Schedule Managing IT Threats At Workplace Overview. Use it as a tool for discussion and navigation on Description, Audience, Frequency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Best Practices To Ensure Cybersecurity At Workplace Managing IT Threats At Workplace Overview
Best Practices To Ensure Cybersecurity At Workplace Managing IT Threats At Workplace OverviewThis slide provides details regarding best practices to enable cybersecurity at workplace in terms of data backup, enable compliance, phishing simulations, employees training, etc. Introducing Best Practices To Ensure Cybersecurity At Workplace Managing IT Threats At Workplace Overview to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Develop, Security, using this template. Grab it now to reap its full benefits.
-
 Budget For Effective Threat Management At Workplace Managing IT Threats At Workplace Overview
Budget For Effective Threat Management At Workplace Managing IT Threats At Workplace OverviewFirm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Present the topic in a bit more detail with this Budget For Effective Threat Management At Workplace Managing IT Threats At Workplace Overview. Use it as a tool for discussion and navigation on Software, Duration, Implementation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity Roadmap To Track Activities Across Firm Managing IT Threats At Workplace Overview
Cybersecurity Roadmap To Track Activities Across Firm Managing IT Threats At Workplace OverviewThis slide provides details regarding roadmap to track cybersecurity activities across firm on monthly basis in terms of security and compliance, backups, staff training. Deliver an outstanding presentation on the topic using this Cybersecurity Roadmap To Track Activities Across Firm Managing IT Threats At Workplace Overview. Dispense information and present a thorough explanation of Security, Backups, Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Determine Staff Training Schedule For Skills Enhancement Managing IT Threats At Workplace Overview
Determine Staff Training Schedule For Skills Enhancement Managing IT Threats At Workplace OverviewThe employees will also require external training which will play important role in their development. The external training will be given by experts of various fields. This training will not be free, and charges will cost the firm per employee. Deliver an outstanding presentation on the topic using this Determine Staff Training Schedule For Skills Enhancement Managing IT Threats At Workplace Overview. Dispense information and present a thorough explanation of Packages, Training, Enhancement using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Determine Threat Management Team Structure Managing IT Threats At Workplace Overview
Determine Threat Management Team Structure Managing IT Threats At Workplace OverviewThe threat management team generally comprise of senior management personnel that have authority and resources to accelerate the company s internal incident response. They will be responsible in managing human impacts both employees and community, company reputation, share values, and corporate assets. Introducing Determine Threat Management Team Structure Managing IT Threats At Workplace Overview to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Determine, Threat Management, Team Structure, using this template. Grab it now to reap its full benefits.
-
 Enable Cybersecurity Compliance At Organization Managing IT Threats At Workplace Overview
Enable Cybersecurity Compliance At Organization Managing IT Threats At Workplace OverviewThis slide provides details regarding role of cybersecurity compliance at workplace. The importance of the security compliance include management of user trust, enhance business efficiency, secure brand reputation, etc. Increase audience engagement and knowledge by dispensing information using Enable Cybersecurity Compliance At Organization Managing IT Threats At Workplace Overview. This template helps you present information on eight stages. You can also present information on Cybersecurity, Confidentiality, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Highlighting Ongoing Cybersecurity Trends Across Globe Managing IT Threats At Workplace Overview
Highlighting Ongoing Cybersecurity Trends Across Globe Managing IT Threats At Workplace OverviewThis slide provides details regarding cybersecurity trends existing across globe in terms of rise in automotive hacking, IoT with 5G, cloud platform as potential vulnerable, etc. Introducing Highlighting Ongoing Cybersecurity Trends Across Globe Managing IT Threats At Workplace Overview to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Automotive, Artificial, Potential, using this template. Grab it now to reap its full benefits.
-
 Impact Analysis For Effective Threat Management In Securing Managing IT Threats At Workplace Overview
Impact Analysis For Effective Threat Management In Securing Managing IT Threats At Workplace OverviewThis slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Present the topic in a bit more detail with this Impact Analysis For Effective Threat Management In Securing Managing IT Threats At Workplace Overview. Use it as a tool for discussion and navigation on Analysis, Threat Management, Securing Workplace. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Analysis Of Successful Threat Management Implementation Managing IT Threats At Workplace Overview
Impact Analysis Of Successful Threat Management Implementation Managing IT Threats At Workplace OverviewThis slide depicts the impact of successful implementation of threat management in terms improved incident management and customer satisfaction and depicts that how much the focus area has been improved from the previous state. Introducing Impact Analysis Of Successful Threat Management Implementation Managing IT Threats At Workplace Overview to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Management, Incident, Satisfaction, using this template. Grab it now to reap its full benefits.
-
 Selecting Secured Threat Management Software Managing IT Threats At Workplace Overview
Selecting Secured Threat Management Software Managing IT Threats At Workplace OverviewThis slide will help firm in choosing the suitable automated threat management software which is to handle existing security and privacy issues and predict upcoming threats. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Deliver an outstanding presentation on the topic using this Selecting Secured Threat Management Software Managing IT Threats At Workplace Overview. Dispense information and present a thorough explanation of Secured, Management, Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Management Capabilities Managing It Threats At Workplace Overview Technological Assessment Of Firm Current
Management Capabilities Managing It Threats At Workplace Overview Technological Assessment Of Firm CurrentThis slide provides details regarding present management capabilities assessment based on several parameters such as incidents and service requests handling rate, service failure rate, customer satisfaction score, etc. Present the topic in a bit more detail with this Management Capabilities Managing It Threats At Workplace Overview Technological Assessment Of Firm Current. Use it as a tool for discussion and navigation on Management, Capabilities, Technological. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents Managing It Threats At Workplace Overview
Table Of Contents Managing It Threats At Workplace OverviewIntroducing Table Of Contents Managing It Threats At Workplace Overview to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Threat, Leveraging, Budget, using this template. Grab it now to reap its full benefits.
-
 Major Threats That Creates Obstacles Amazon Business Strategy Understanding Its Core Competencies
Major Threats That Creates Obstacles Amazon Business Strategy Understanding Its Core CompetenciesThis slide provides information regarding SWOT analysis technique utilized by Amazon to evaluate its competitive positioning. The slide highlighting threats faced by Amazon causing potential issues in terms of data and online privacy risk, aggressive pricing strategies, etc. Deliver an outstanding presentation on the topic using this Major Threats That Creates Obstacles Amazon Business Strategy Understanding Its Core Competencies. Dispense information and present a thorough explanation of Growth, Legislations, Strategies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Strategic Initiatives Playbook IT Risk Management Framework To Manage Security Threats
Strategic Initiatives Playbook IT Risk Management Framework To Manage Security ThreatsThis slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Deliver an outstanding presentation on the topic using this Strategic Initiatives Playbook IT Risk Management Framework To Manage Security Threats. Dispense information and present a thorough explanation of IT Risk Management, Framework To Manage, Security Threats, Platform Upgradation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IT Risk Management Framework To Manage Security Threats IT Cost Optimization And Management Strategy SS
IT Risk Management Framework To Manage Security Threats IT Cost Optimization And Management Strategy SSThis slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Present the topic in a bit more detail with this IT Risk Management Framework To Manage Security Threats IT Cost Optimization And Management Strategy SS. Use it as a tool for discussion and navigation on Implement Control Environment, Implement Security Processes, Enterprise Security Program. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Management Plan To Manage Cyber Threats IT Cost Optimization And Management Strategy SS
Risk Management Plan To Manage Cyber Threats IT Cost Optimization And Management Strategy SSThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Deliver an outstanding presentation on the topic using this Risk Management Plan To Manage Cyber Threats IT Cost Optimization And Management Strategy SS. Dispense information and present a thorough explanation of Threat, Vulnerability, Cyber Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IT Risk Management Framework To Manage Security Threats Develop Business Aligned IT Strategy
IT Risk Management Framework To Manage Security Threats Develop Business Aligned IT StrategyThis slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Increase audience engagement and knowledge by dispensing information using IT Risk Management Framework To Manage Security Threats Develop Business Aligned IT Strategy. This template helps you present information on three stages. You can also present information on Enterprise Security Program, Control Environment, Security Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risk Management Plan To Manage Cyber Threats Develop Business Aligned IT Strategy
Risk Management Plan To Manage Cyber Threats Develop Business Aligned IT StrategyThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Deliver an outstanding presentation on the topic using this Risk Management Plan To Manage Cyber Threats Develop Business Aligned IT Strategy. Dispense information and present a thorough explanation of Vulnerability, Likelihood, Control Initiative, Natural Disaster using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Strategic Framework To Manage IT Risk Management Framework To Manage Security Threats Strategy SS
Strategic Framework To Manage IT Risk Management Framework To Manage Security Threats Strategy SSThis slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy. Deliver an outstanding presentation on the topic using this Strategic Framework To Manage IT Risk Management Framework To Manage Security Threats Strategy SS. Dispense information and present a thorough explanation of Implement Enterprise Security Program, Implement Control Environment, Implement Security Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Strategic Framework To Manage IT Risk Management Plan To Manage Cyber Threats Strategy SS
Strategic Framework To Manage IT Risk Management Plan To Manage Cyber Threats Strategy SSThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Strategic Framework To Manage IT Risk Management Plan To Manage Cyber Threats Strategy SS. Use it as a tool for discussion and navigation on Risk Management Plan, Manage Cyber Threats, Vulnerability, Control Initiative. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Management Plan To Manage Cyber Threats Comprehensive Plan To Ensure It And Business
Risk Management Plan To Manage Cyber Threats Comprehensive Plan To Ensure It And BusinessThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Risk Management Plan To Manage Cyber Threats Comprehensive Plan To Ensure It And Business. Use it as a tool for discussion and navigation on Management, Information, Vulnerability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Essential Initiatives To Safeguard Various It Threats Risk Management Plan
Essential Initiatives To Safeguard Various It Threats Risk Management PlanThis slide provides information regarding several IT threats risk management plan including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Essential Initiatives To Safeguard Various It Threats Risk Management Plan. Use it as a tool for discussion and navigation on Malicious Human Attack, Vulnerability, It Threats, Risk Management Plan This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IT Strategy Planning Guide IT Risk Management Framework To Manage Security Threats Strategy SS V
IT Strategy Planning Guide IT Risk Management Framework To Manage Security Threats Strategy SS VThis slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Deliver an outstanding presentation on the topic using this IT Strategy Planning Guide IT Risk Management Framework To Manage Security Threats Strategy SS V. Dispense information and present a thorough explanation of IT Risk Management, Framework To Manage, Security Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IT Strategy Planning Guide Risk Management Plan To Manage Cyber Threats Strategy SS V
IT Strategy Planning Guide Risk Management Plan To Manage Cyber Threats Strategy SS VThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this IT Strategy Planning Guide Risk Management Plan To Manage Cyber Threats Strategy SS V. Use it as a tool for discussion and navigation on Risk Management Plan, Manage Cyber Threats, Natural Disaster, Website Resources Unavailability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Management Plan To Manage Cyber Threats Blueprint Develop Information It Roadmap Strategy Ss
Risk Management Plan To Manage Cyber Threats Blueprint Develop Information It Roadmap Strategy SsThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Risk Management Plan To Manage Cyber Threats Blueprint Develop Information It Roadmap Strategy Ss. Use it as a tool for discussion and navigation on Management, Information, Vulnerability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Communication Plan To Mitigate Multiple Threat In It Sector
Communication Plan To Mitigate Multiple Threat In It SectorFollowing slide illustrates communication plan to control various risk to achieve business objectives without any disruption and chaos. The plan includes types of risk, owner, channel, mitigation measures and risk level to combat business related risks. Presenting our well structured Communication Plan To Mitigate Multiple Threat In It Sector. The topics discussed in this slide are Risk Level, Channel, Owner. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Risk Management Plan To Manage Cyber Threats Strategic Initiatives To Boost IT Strategy SS V
Risk Management Plan To Manage Cyber Threats Strategic Initiatives To Boost IT Strategy SS VThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Increase audience engagement and knowledge by dispensing information using Risk Management Plan To Manage Cyber Threats Strategic Initiatives To Boost IT Strategy SS V. This template helps you present information on seven stages. You can also present information on Plan, Management, Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 IT Risk Management Framework To Manage Security Threats Definitive Guide To Manage Strategy SS V
IT Risk Management Framework To Manage Security Threats Definitive Guide To Manage Strategy SS VThis slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Introducing IT Risk Management Framework To Manage Security Threats Definitive Guide To Manage Strategy SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Implement Enterprise Security Program, Implement Control Environment, Implement Security Processes, using this template. Grab it now to reap its full benefits.
-
 Communication Plan For It Asset Security Threats
Communication Plan For It Asset Security ThreatsThis slide consists of a communication plan that can be implemented by managers to safeguard IT assets from cyber threats and create an effective response plan. Major elements covered are IT security assets, risk, threat, risk impact, etc. Presenting our set of slides with Communication Plan For It Asset Security Threats This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on IT Security Assets, IT Servers
-
 It Risk Management Framework To Threats Strategic Plan To Secure It Infrastructure Strategy SS V
It Risk Management Framework To Threats Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Deliver an outstanding presentation on the topic using this It Risk Management Framework To Threats Strategic Plan To Secure It Infrastructure Strategy SS V. Dispense information and present a thorough explanation of Management, Framework, Environment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Management Plan To Manage Cyber Threats Strategic Plan To Secure It Infrastructure Strategy SS V
Risk Management Plan To Manage Cyber Threats Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Risk Management Plan To Manage Cyber Threats Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Risk Management, Initiatives, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It Risk Management Framework To Manage Security Threats Cios Guide For It Strategy Strategy SS V
It Risk Management Framework To Manage Security Threats Cios Guide For It Strategy Strategy SS VThis slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Present the topic in a bit more detail with this It Risk Management Framework To Manage Security Threats Cios Guide For It Strategy Strategy SS V. Use it as a tool for discussion and navigation on Management, Framework, Environment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Management Plan To Manage Cyber Threats Cios Guide For It Strategy Strategy SS V
Risk Management Plan To Manage Cyber Threats Cios Guide For It Strategy Strategy SS VThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Risk Management Plan To Manage Cyber Threats Cios Guide For It Strategy Strategy SS V. Use it as a tool for discussion and navigation on Risk Management, Vulnerability, Likelihood . This template is free to edit as deemed fit for your organization. Therefore download it now.





