Powerpoint Templates and Google slides for Secured Cloud
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cloud Network Security Server Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Network Security Server Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon depicts a cloud server, perfect for illustrating cloud computing concepts. The image is vibrant and eye catching, making it ideal for presentations and other digital projects.
-
 Cloud Network Security Server Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Network Security Server Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon is a great way to represent Cloud Server in your presentations. The icon features a cloud like shape with a single color, making it easy to customize for your needs. Its perfect for illustrating cloud computing concepts in a simple, yet effective way.
-
 Cloud Security Server Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Security Server Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon depicts a cloud server, perfect for illustrating cloud computing concepts. The image is vibrant and eye catching, making it ideal for presentations and other digital projects.
-
 Cloud Security Server Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Security Server Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon is a great way to represent Cloud Server in your presentations. The icon features a cloud like shape with a single color, making it easy to customize for your needs. Its perfect for illustrating cloud computing concepts in a simple, yet effective way.
-
 Cloudfront Security For Company Web Service
Cloudfront Security For Company Web ServiceThis slide outlines the Cloudfront security that helps to protect content and ensure secure delivery to end users. It includes various aspects such as origin access identity, application acceleration, DDoS protection and geo restriction.Presenting our set of slides with Cloudfront Security For Company Web Service. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Communication,Connection,Consensus.
-
 Cloudfront Service Delivery And Security Icon
Cloudfront Service Delivery And Security IconIntroducing our premium set of slides with Cloudfront Service Delivery And Security Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Encourage Communication,Save Money,Time Sensitive Environments. So download instantly and tailor it with your information.
-
 Comparison Secure Web Gateway And Cloud Network Security Using Secure Web Gateway
Comparison Secure Web Gateway And Cloud Network Security Using Secure Web GatewayThis slide demonstrates the concept of cloud security gateways and Secure Web Gateways. The purpose of this slide is to compare cloud security gateways and SWGs on the basis of various factors such as scope, deployment, architecture, features and cost. Deliver an outstanding presentation on the topic using this Comparison Secure Web Gateway And Cloud Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Deployment, Architecture, Comparison using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Data Security Warning Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Data Security Warning Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon features a warning cloud with an exclamation mark, perfect for adding to presentations to warn viewers of potential risks or issues. It is a simple yet effective way to draw attention and communicate important information.
-
 Cloud Data Security Warning Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Data Security Warning Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Cloud Warning is a perfect visual aid for presentations and documents. It is a simple yet effective design that conveys the message of a warning in the cloud. It is easy to use, and can be easily customized to fit your needs.
-
 Cloud Security Warning Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Security Warning Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon features a warning cloud with an exclamation mark, perfect for adding to presentations to warn viewers of potential risks or issues. It is a simple yet effective way to draw attention and communicate important information.
-
 Cloud Security Warning Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Security Warning Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Cloud Warning is a perfect visual aid for presentations and documents. It is a simple yet effective design that conveys the message of a warning in the cloud. It is easy to use, and can be easily customized to fit your needs.
-
 Automated Cloud Security In Powerpoint And Google Slides Cpb
Automated Cloud Security In Powerpoint And Google Slides CpbPresenting our Automated Cloud Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases Three stages. It is useful to share insightful information on Automated Cloud Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cloud Development Security Use Cases
Cloud Development Security Use CasesThis slide mentions certain use cases of cloud development security to automate threat detection tools and reduce risk. It involves use cases such as cloud migration, cloud threat analysis, devsecops and cloud security compliance. Introducing our premium set of slides with Cloud Development Security Use Cases. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Threat Analysis, Cloud Migration. So download instantly and tailor it with your information.
-
 Cloud Network Security Development Icon
Cloud Network Security Development IconIntroducing our premium set of slides with Cloud Network Security Development Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Network Security Development. So download instantly and tailor it with your information.
-
 Impact Of Encryption Implementation On Cloud Security Cloud Data Encryption
Impact Of Encryption Implementation On Cloud Security Cloud Data EncryptionThis slide represents the various factors that showcase the improvement of application security after adopting encryption. The parameters discussed are unauthorized access, data breaches, malware and ransomware, phishing attacks, etc. Deliver an outstanding presentation on the topic using this Impact Of Encryption Implementation On Cloud Security Cloud Data Encryption. Dispense information and present a thorough explanation of Unauthorized Access, Data Breaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Timeline For Cloud Data Security Implementation Cloud Data Encryption
Timeline For Cloud Data Security Implementation Cloud Data EncryptionThis slide represents the timeline to implement cloud data encryption in an organization. The main components included are determine sensitive data and required encryption technique, choose a cloud service provider, implement encryption solution in cloud, etc. Introducing Timeline For Cloud Data Security Implementation Cloud Data Encryption to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Test Encryption Solutions, Implement Encryptions Solution, using this template. Grab it now to reap its full benefits.
-
 Cloud Cyber Security System Architecture
Cloud Cyber Security System ArchitectureThis slide showcases cyber security system architecture for business cloud data protection from hacks. This further includes key takeaways such as business having cloud misconfiguration that pose serious hazards. Introducing our Cloud Cyber Security System Architecture set of slides. The topics discussed in these slides are Emulated Components, Cyber Security, System Architecture. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cloud Data Security Software In Powerpoint And Google Slides Cpb
Cloud Data Security Software In Powerpoint And Google Slides CpbPresenting Cloud Data Security Software In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cloud Data Security Software. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Agenda For Cloud Access Security Broker CASB V2 Ppt Ideas Introduction
Agenda For Cloud Access Security Broker CASB V2 Ppt Ideas IntroductionIntroducing Agenda For Cloud Access Security Broker CASB V2 Ppt Ideas Introduction to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Broker Technology, Architecture, Technologies, using this template. Grab it now to reap its full benefits.
-
 Benefits Of Cloud Access Security Broker 2 0 Cloud Access Security Broker CASB V2
Benefits Of Cloud Access Security Broker 2 0 Cloud Access Security Broker CASB V2This slide represents the advantages of cloud access security broker version 2.0. The purpose of this slide is to highlight the main benefits of CASB 2.0, including comprehensive coverage, cost-effectiveness, enhanced security efficacy, improved visibility, app database, and so on. Increase audience engagement and knowledge by dispensing information using Benefits Of Cloud Access Security Broker 2 0 Cloud Access Security Broker CASB V2. This template helps you present information on five stages. You can also present information on Cloud Access Security Broker, Comprehensive Coverage, Enhanced Security Efficacy, Cost Effectiveness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 CASB Vs CSPM Vs CWPP Cloud Access Security Broker CASB V2 Ppt Ideas Samples
CASB Vs CSPM Vs CWPP Cloud Access Security Broker CASB V2 Ppt Ideas SamplesThis slide describes the difference between Cloud Access Security Broker CASB, cloud security posture management CSPM, and cloud workload protection platforms CWPP. The purpose of this slide is to highlight the key differences between the three technologies based on features such as focus, use cases, deployment model, etc. Present the topic in a bit more detail with this CASB Vs CSPM Vs CWPP Cloud Access Security Broker CASB V2 Ppt Ideas Samples. Use it as a tool for discussion and navigation on Cloud Workload Protection, Threat Detection And Response, Vulnerability Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 30 60 90 Days Plan To Deploy CASB Model
Cloud Access Security Broker CASB V2 30 60 90 Days Plan To Deploy CASB ModelThis slide represents the 30-0-90 days plan to implement the Cloud Access Security Broker model in an organization. The purpose of this slide is to showcase the various steps to be taken to deploy CASB at the interval every 30 days. Introducing Cloud Access Security Broker CASB V2 30 60 90 Days Plan To Deploy CASB Model to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Scope, Current Security Architecture, Security Operations Center Functions, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based Deployment
Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based DeploymentThis slide represents the benefits and drawbacks of proxy-based CASB deployment. The purpose of this slide is to showcase the various pros and cons of proxy-based cloud access security brokers and the advantages cover flexibility, secure SaaS applications, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based Deployment. This template helps you present information on two stages. You can also present information on Cloud Access Security Brokers, Cover Flexibility, Secure SaaS Applications, Enforcement Of Security Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 And Encryption Ppt Gallery Design Templates
Cloud Access Security Broker CASB V2 And Encryption Ppt Gallery Design TemplatesThis slide describes the improved encryption with CASB version 2.0. The purpose of this slide is to showcase the various encryption features of Cloud Access Security Broker version 2.0, including security that follows the data, content access that can be revoked at any time, and multi-platform compatibility. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 And Encryption Ppt Gallery Design Templates. Dispense information and present a thorough explanation of Detecting Sensitive Information, Personally Identifiable Information, Personal Health Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 And Secure Web Gateway Ppt Gallery Shapes
Cloud Access Security Broker CASB V2 And Secure Web Gateway Ppt Gallery ShapesThis slide represents how CASB 2.0 not just discovers the shadow IT but helps to control it too. The purpose of this slide is to showcase how CASB 2.0 improves the SWG model by empowering it with rich cloud app data, getting dynamic control of shadow IT and simplifying deployment. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 And Secure Web Gateway Ppt Gallery Shapes. Use it as a tool for discussion and navigation on Simplifying Deployment, Cloud Access Security Broker, Secure Web Gateway, Standardizing Authentication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB Deployment
Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB DeploymentThis slide outlines the use cases of API-based CASB deployment. This slide highlights the main use cases of API-based deployment of CASB deployment, including identifying malware in cloud services, implementing data transfer policies across different cloud services, auditing user access provisioning and so on. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB Deployment. Dispense information and present a thorough explanation of Malware In Cloud Services, Data Transfer Policies, Cloud Services, Auditing User Access Provisioning using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 API Scanning CASB Deployment Model
Cloud Access Security Broker CASB V2 API Scanning CASB Deployment ModelThis slide outlines the overview of the API scanning model of CASB deployment. The purpose of this slide is to showcase its features and introduce APIs and how this deployment works. It also represents the architecture of the API scanning model and its components include mobile and corporate devices and APIs. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 API Scanning CASB Deployment Model. Use it as a tool for discussion and navigation on Corporate Devices, Facilitate Communication, Real Time Protection, Non Intrusive Security Technique. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 Architectural Components Ppt Gallery Microsoft
Cloud Access Security Broker CASB V2 Architectural Components Ppt Gallery MicrosoftThis slide outlines the main components of Cloud Access Security Broker architecture. The purpose of this slide is to showcase the primary elements of CASB architecture, including immediate enterprise core, secondary enterprise core, PaaS, IaaS, PaaS, connectivity gateway, and so on. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Architectural Components Ppt Gallery Microsoft. Dispense information and present a thorough explanation of Cloud Access Security, Broker Architectural, Connectivity Gateway, Software As A Service using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 Benefits Of Cloud Access Security Broker
Cloud Access Security Broker CASB V2 Benefits Of Cloud Access Security BrokerThis slide outlines the different advantages of Cloud Access Security Broker technology. This slide highlights the pros of CASB technology, including risk visibility, cyber threat prevention, granular cloud usage control, shadow IT assessment and management, DLP, managing privileged accounts and admin and controlled data sharing. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Benefits Of Cloud Access Security Broker. Use it as a tool for discussion and navigation on Cyber Threat Prevention, Granular Cloud Usage Control, Data Loss Prevention, Controlled External File Sharing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 Best Practices To Implement Cloud Access Security Broker
Cloud Access Security Broker CASB V2 Best Practices To Implement Cloud Access Security BrokerThis slide represents the best practices for implementing a Cloud Access Security Broker within an organization. The purpose of this slide is to demonstrate the best practices and their possible impact on the overall business operations. The best practices include building visibility, forecasting risk and releasing CASB. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Best Practices To Implement Cloud Access Security Broker. Dispense information and present a thorough explanation of Cloud Access Security Broker, Business Operations, Building Visibility, Forecasting Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 CASB Application In Accounting And Finance Sector
Cloud Access Security Broker CASB V2 CASB Application In Accounting And Finance SectorThis slide outlines the application of the CASB model in the accounting and banking sectors. The purpose of this slide is to give an overview and represent the challenges that occur due to cloud data exchange and how CASB can overcome those challenges. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 CASB Application In Accounting And Finance Sector. This template helps you present information on three stages. You can also present information on Accounting And Banking Sectors, Cloud Data Exchange, Finance Organization, Data Drives Banking Business using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 CASB Application In Learning And Education Sector
Cloud Access Security Broker CASB V2 CASB Application In Learning And Education SectorThis slide represents the application of a Cloud Access Security Broker in the learning and education department. The purpose of this slide is to highlight the overview, challenges caused by the transition in education, and CASB solutions. Introducing Cloud Access Security Broker CASB V2 CASB Application In Learning And Education Sector to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Learning And Education Department, Transition In Education, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 CASB As A Streamline Endpoint Protection Solution
Cloud Access Security Broker CASB V2 CASB As A Streamline Endpoint Protection SolutionThis slide outlines how Cloud Access Security Broker 2.0 streamlines endpoint protection. The purpose of this slide is to showcase how CASB 2.0 improves endpoint security for streamlined deployment. It also includes the features of CASB 2.0 and endpoint security integration. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 CASB As A Streamline Endpoint Protection Solution. Use it as a tool for discussion and navigation on Cloud Access Security Broker, Streamlines Endpoint Protection, Streamlined Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 CASB Deployment With Optional Components Pricing
Cloud Access Security Broker CASB V2 CASB Deployment With Optional Components PricingThis slide outlines the pricing of CASB deployment with optional or add-on components. The purpose of this slide is to showcase the pricing of additional components in CASB deployment, including data security subscription, support, threat protection subscription, data retention, and so on. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 CASB Deployment With Optional Components Pricing. Dispense information and present a thorough explanation of Data Security Subscription, Threat Protection Subscription, Data Retention, Customer Relationship Admins using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 CASB Deployment With Standard Components Pricing
Cloud Access Security Broker CASB V2 CASB Deployment With Standard Components PricingThis slide represents the cost of CASB deployment with standard components. This slide aims to showcase the pricing of classic elements for CASB deployment in an organization. The components include visibility, compliance, threat protection, and data security with Salesforce, Box, and Office 365 environments. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 CASB Deployment With Standard Components Pricing. Use it as a tool for discussion and navigation on Pricing Of Classic Elements, Components Include Visibility, Threat Protection, Data Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use Cases
Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use CasesThis slide highlights the main use cases of forward proxy server CASB deployment. The main purpose of this slide is to showcase the primary use cases of the forward proxy, including implementing granular access and activity controls and detecting show IT in the network. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use Cases. This template helps you present information on two stages. You can also present information on Deploying Granular Access, Activity Controls, Detecting Shadow, IT In The Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 CASB Reverse Proxy Deployment Use Cases
Cloud Access Security Broker CASB V2 CASB Reverse Proxy Deployment Use CasesThis slide illustrates the use cases of reverse proxy server deployment of the Cloud Access Security Broker model. The purpose of this slide is to highlight the main use cases of reverse proxy deployment, including using user behavior to enforce access constraints, keeping data from certain programs from being lost, and so on. Introducing Proxy to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Reverse Proxy Server Deployment, Cloud Access Security Broker, Reverse Proxy Deployment, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Checklist To Adopt A Cloud Access Security Broker
Cloud Access Security Broker CASB V2 Checklist To Adopt A Cloud Access Security BrokerThis slide represents the main points to consider before adopting a cloud access security broker. The purpose of this slide is to showcase the key measures that organizations should keep in mind before choosing a CASB solution and the measures include conducting the trial, outlining CASB roles, and so on. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Checklist To Adopt A Cloud Access Security Broker. Use it as a tool for discussion and navigation on Cloud Access Security Broker, Cloud Requirements, Conduct Regular Audits. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 Cloud Access Security Broker And User Authentication
Cloud Access Security Broker CASB V2 Cloud Access Security Broker And User AuthenticationThis slide represents the improved user authentication method in Cloud Access Security Broker version 2.0. The purpose of this slide is to showcase how the user authentication process can be enhanced by integrating CASB 2.0. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Cloud Access Security Broker And User Authentication. Dispense information and present a thorough explanation of Authentication Solutions, Creating Adaptive Authentication, Businesses To Dynamically using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 Cloud Security Standards And Control Frameworks
Cloud Access Security Broker CASB V2 Cloud Security Standards And Control FrameworksThis slide provides an overview of the cloud security protocols and control frameworks. The purpose of this slide is to showcase the various information security standards and control frameworks, including ISO-27001, ISO-27017, ISO-27018, GDPR, SOC reporting, PCI DSS, and HIPAA. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Cloud Security Standards And Control Frameworks. Use it as a tool for discussion and navigation on Payment Card Industry, Data Security Standard, System And Organization Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 Comparison Between CASB And Data Loss Prevention DLP
Cloud Access Security Broker CASB V2 Comparison Between CASB And Data Loss Prevention DLPThis slide describes the difference between Cloud Access Security Broker and data loss prevention. This slide highlights the main comparisons between CASB and DLP systems based on their purpose, focus area, use cases, key features, implementation and relationship. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Comparison Between CASB And Data Loss Prevention DLP. Dispense information and present a thorough explanation of Content Inspection, Data Classification, Encryption, Access Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 Comparison Between Reverse Proxy And Load Balancer
Cloud Access Security Broker CASB V2 Comparison Between Reverse Proxy And Load BalancerThis slide represents the difference between reverse proxy and load balancer. The purpose of this slide is to highlight the main differences between reverse proxy server and load balancer based on how they respond to client request, number of servers required, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Comparison Between Reverse Proxy And Load Balancer. This template helps you present information on one stages. You can also present information on Reverse Proxy And Load Balancer, Reverse Proxy, Site Requires Several Servers, Scalability And Flexibility using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Conventional CASB Vs Next Generation CASB
Cloud Access Security Broker CASB V2 Conventional CASB Vs Next Generation CASBThis slide outlines the comparison between Cloud Access Security Broker and next-generation CASB. This slide highlights the main differences between conventional and next-generation CASB based on features such as focus, deployment model, integration approach, security capabilities, scalability, etc. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Conventional CASB Vs Next Generation CASB. Use it as a tool for discussion and navigation on Integration Approach, Security Capabilities, Deployment Flexibility, Management Complexity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 Emerging Cloud Security Risks And Threats
Cloud Access Security Broker CASB V2 Emerging Cloud Security Risks And ThreatsThis slide represents the emerging cloud security risks, and threats organizations can encounter. The purpose of this slide is to highlight the various threats that CASB deployment can help overcome, including VPNs, system misconfiguration, non-zero security permissions, and so on. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Emerging Cloud Security Risks And Threats. Dispense information and present a thorough explanation of System Misconfigurations, Continuous Integration And Development, Supply Chain Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 For Table Of Contents Ppt Ideas Designs Download
Cloud Access Security Broker CASB V2 For Table Of Contents Ppt Ideas Designs DownloadIntroducing Cloud Access Security Broker CASB V2 For Table Of Contents Ppt Ideas Designs Download to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Shadow IT Management Lifecycle, Cloud Security Standards, Control Frameworks, Requirements, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And Working
Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And WorkingThis slide describes the overview of the forward proxy deployment mode of the CASB model, including its working. The purpose of this slide is to showcase the working of proxy-based CASB deployment and the main components include user or clients, forward proxy, internet and origin server. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And Working. Use it as a tool for discussion and navigation on Deployment Overview And Working, Web Servers They Visit, Forward Proxy Method Is A Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 Future Of Cloud Access Security Broker CASB 2 0
Cloud Access Security Broker CASB V2 Future Of Cloud Access Security Broker CASB 2 0This slide outlines the overview of Cloud Access Security Broker 2.0. The purpose of this slide is to showcase the various limitations of CASB version 1.0 and the emerging need for CASB 2.0. The components of CASB 2.0 include user authentication, web security, data loss prevention, advanced malware protection, etc. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Future Of Cloud Access Security Broker CASB 2 0. This template helps you present information on seven stages. You can also present information on Data Loss Prevention, Advanced Malware Protection, Managed Security Service, Endpoint Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB Model
Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB ModelThis slide gives an overview of the technologies that can be used in the Cloud Access Security Broker model in the future. The purpose of this slide is to showcase the various emerging technologies that can help CASB to grow in the future. The technologies include AI, ML, CSPM, data privacy and protection, etc. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB Model. Dispense information and present a thorough explanation of Cloud Security Posture Management, Data Privacy And Protection, Zero Trust Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
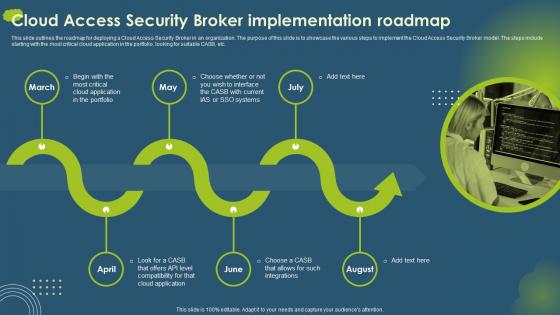 Cloud Access Security Broker CASB V2 Implementation Roadmap Ppt Gallery Portrait
Cloud Access Security Broker CASB V2 Implementation Roadmap Ppt Gallery PortraitThis slide outlines the roadmap for deploying a Cloud Access Security Broker in an organization. The purpose of this slide is to showcase the various steps to implement the Cloud Access Security Broker model. The steps include starting with the most critical cloud application in the portfolio, looking for suitable CASB, etc. Introducing Cloud Access Security Broker CASB V2 Implementation Roadmap Ppt Gallery Portrait to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Critical Cloud Application, Compatibility, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Introduction Ppt Infographic Template Deck
Cloud Access Security Broker CASB V2 Introduction Ppt Infographic Template DeckThis slide outlines the overview and benefits of cloud access security broker. The purpose of this slide is to demonstrate the overview, benefits, and pillars of CASB, such as compliance, visibility, threat protection, and data security. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Introduction Ppt Infographic Template Deck. Use it as a tool for discussion and navigation on Risk Visibility, Threat Prevention, Granular Cloud Usage Control, Data Security . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 Leading Cloud Access Security Broker Platforms
Cloud Access Security Broker CASB V2 Leading Cloud Access Security Broker PlatformsThis slide outlines the Leading Cloud Access Security Broker platforms. The purpose of this slide is to highlight the leading CASB platforms, including G-suite, office 365, and Amazon Web Services, and it also represents the benefits and features of these cloud platforms. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Leading Cloud Access Security Broker Platforms. This template helps you present information on three stages. You can also present information on Cloud Access Security, Broker Platforms, Amazon Web Services, Cloud Platforms using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Life Cycle Protection Ppt Gallery Layout Ideas
Cloud Access Security Broker CASB V2 Life Cycle Protection Ppt Gallery Layout IdeasIntroducing Cloud Access Security Broker CASB V2 Life Cycle Protection Ppt Gallery Layout Ideas to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Continuous Visibility And Assessment Systems, System Activity Payload Network, Contain Or Mitigate Risk, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Overview Of CASB Deployment Models
Cloud Access Security Broker CASB V2 Overview Of CASB Deployment ModelsThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out-of-band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Overview Of CASB Deployment Models. This template helps you present information on four stages. You can also present information on Cloud Access Security Broker, Unmanaged Gadgets, Inline Deployment, Scalable And Strong Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Overview Of Cloud Access Security Broker Architecture
Cloud Access Security Broker CASB V2 Overview Of Cloud Access Security Broker ArchitectureThis slide gives an overview of Cloud Access Security Broker architecture. The purpose of this slide is to highlight architecture and its main components covering immediate enterprise core, secondary enterprise core, PaaS, SaaS, IaaS, connectivity gateway, security and compliance rules, etc. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Overview Of Cloud Access Security Broker Architecture. Dispense information and present a thorough explanation of Visibility, Compliance, Threat Protection, Enterprise Integration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 Pillar Compliance Ppt Icon Background Images
Cloud Access Security Broker CASB V2 Pillar Compliance Ppt Icon Background ImagesThis slide gives an overview of the compliance pillar of cloud access security broker. The purpose of this slide is to showcase how compliance is a vital factor for an organization migrating its data and systems to the cloud. Compliance can help industries such as healthcare, retail, and financial services. Introducing Cloud Access Security Broker CASB V2 Pillar Compliance Ppt Icon Background Images to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Compliance Pillar, Cloud Access Security Broker, Financial Services, Compliance Risk Domains, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Pillar Data Security Ppt Icon Backgrounds
Cloud Access Security Broker CASB V2 Pillar Data Security Ppt Icon BackgroundsThis slide talks about the data security pillar of the Cloud Access Security Broker pillar. This slide highlights how CASB data security can help organizations improve their IT requirements and business operations and detect security breaches before they happen. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Pillar Data Security Ppt Icon Backgrounds. This template helps you present information on four stages. You can also present information on Document Fingerprinting, Data Security Pillar, Cloud Access Security Broker Pillar using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Pillar Overview Ppt Icon Background Designs
Cloud Access Security Broker CASB V2 Pillar Overview Ppt Icon Background DesignsThis slide represents the four major pillars of cloud access security broker. The purpose of this slide is to showcase the main pillars of implementing a cloud access security broker. The pillars include compliance, visibility, threat protection, and data security. Introducing Cloud Access Security Broker CASB V2 Pillar Overview Ppt Icon Background Designs to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Threat Protection, Data Security, Compliance, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Pillar Threat Protection Ppt Icon Introduction
Cloud Access Security Broker CASB V2 Pillar Threat Protection Ppt Icon IntroductionThis slide describes the threat protection pillar of cloud access security broker. The purpose of this slide is to highlight how CASB can help organizations to detect threats in advance through machine learning algorithms. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Pillar Threat Protection Ppt Icon Introduction. This template helps you present information on four stages. You can also present information on Threat Protection Pillar, Cloud Access Security Broker, Machine Learning Algorithms using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Pillar Visibility Ppt Icon Background Image
Cloud Access Security Broker CASB V2 Pillar Visibility Ppt Icon Background ImageThis slide outlines the overview of the visibility pillar of cloud access security broker. The purpose of this slide is to showcase the working process of the visibility pillar of CASB and it also represents the topography of CASB visibility. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Pillar Visibility Ppt Icon Background Image. Dispense information and present a thorough explanation of Cloud Access Security Broker Pillar, Visibility, Cloud Discovery Analysis, Device And Location Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 Popular Cloud Access Security Broker Vendors
Cloud Access Security Broker CASB V2 Popular Cloud Access Security Broker VendorsThis slide outlines the popular Cloud Access Security Broker vendors. The purpose of this slide is to showcase the multiple leading service providers for CASB, including Forcepoint, McAfee, Cisco Systems, Microsoft, Bitglass, and Net Spoke. It also includes the features and technology used by these vendors. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Popular Cloud Access Security Broker Vendors. Use it as a tool for discussion and navigation on Cloud Access Security Broker, Mid To Large Enterprises, Robust Integration, Cisco Systems. This template is free to edit as deemed fit for your organization. Therefore download it now.





