Powerpoint Templates and Google slides for Vulnerable Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Effective information security defining vulnerability rating
Effective information security defining vulnerability ratingFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Present the topic in a bit more detail with this Effective Information Security Defining Vulnerability Rating. Use it as a tool for discussion and navigation on Vulnerability Ranking, Organization, Occurrence Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing asset security managing critical threat vulnerabilities and security threats
Addressing asset security managing critical threat vulnerabilities and security threatsThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Introducing Addressing Asset Security Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ownership, Location, Confidentiality, Integrity, using this template. Grab it now to reap its full benefits.
-
 Addressing critical business managing critical threat vulnerabilities and security threats
Addressing critical business managing critical threat vulnerabilities and security threatsThis slide provides details regarding business functions recovery as firm needs to retrieve the crucial information based on priorities in various departments and time taken to retrieve the information. Present the topic in a bit more detail with this Addressing Critical Business Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Department, Priorities, Allowable Downtime. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing cyber threats in managing critical threat vulnerabilities and security threats
Addressing cyber threats in managing critical threat vulnerabilities and security threatsThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Increase audience engagement and knowledge by dispensing information using Addressing Cyber Threats In Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Healthcare, Manufacturing, Government, Energy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing indicators associated managing critical threat vulnerabilities and security threats
Addressing indicators associated managing critical threat vulnerabilities and security threatsThis slide provides details regarding indicators associated to insider threats in terms of traits, demeanor and goals, etc. Introducing Addressing Indicators Associated Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Authentication Levels, Data Exfiltration, Traits, Demeanor, using this template. Grab it now to reap its full benefits.
-
 Addressing internal and external managing critical threat vulnerabilities and security threats
Addressing internal and external managing critical threat vulnerabilities and security threatsThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Increase audience engagement and knowledge by dispensing information using Addressing Internal And External Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on two stages. You can also present information on Targeted Intelligence, Malware Intelligence, Reputation Intelligence, External Sources, Internal Sources using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing natural calamities managing critical threat vulnerabilities and security threats
Addressing natural calamities managing critical threat vulnerabilities and security threatsThis slide provides details regarding natural calamities posing as threat to organization and threat management checklist during nature crisis. Deliver an outstanding presentation on the topic using this Addressing Natural Calamities Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Threat Management Checklist using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Addressing several financial managing critical threat vulnerabilities and security threats
Addressing several financial managing critical threat vulnerabilities and security threatsThis slide provides information regarding the various financial scenarios that pose a threat to firm profitability and determine signs of financial distress. Introducing Addressing Several Financial Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Insolvency Scenario, Currency Scenario, Unexpected Fluctuations, Bankruptcy, using this template. Grab it now to reap its full benefits.
-
 Addressing threat management critical threat vulnerabilities and security threats
Addressing threat management critical threat vulnerabilities and security threatsThe threat management team needs to have strong critical and creative thinking skills so that they become capable in taking key decisions without complete or conflicting information under immense tensed situations. The team will be trained by experts who will also use scenario based activities and costing will be per employee basis. Present the topic in a bit more detail with this Addressing Threat Management Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Hypotheticals, Workshops, Field Exercises. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing various ways to managing critical threat vulnerabilities and security threats
Addressing various ways to managing critical threat vulnerabilities and security threatsThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Increase audience engagement and knowledge by dispensing information using Addressing Various Ways To Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Management Policies, User Accounts, Active Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing ways to handling managing critical threat vulnerabilities and security threats
Addressing ways to handling managing critical threat vulnerabilities and security threatsThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Introducing Addressing Ways To Handling Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cash Requirement, Financial Statements, Overheads Analysis, Currency Hedging, using this template. Grab it now to reap its full benefits.
-
 Budget for effective threat managing critical threat vulnerabilities and security threats
Budget for effective threat managing critical threat vulnerabilities and security threatsFirm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Deliver an outstanding presentation on the topic using this Budget For Effective Threat Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Incident Management, Risk Management, Client Onboarding Process, Document Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparative assessment of managing critical threat vulnerabilities and security threats
Comparative assessment of managing critical threat vulnerabilities and security threatsThis slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Present the topic in a bit more detail with this Comparative Assessment Of Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Insider Threat, Social Engineering, Maintenance Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Contingency plan for cyber managing critical threat vulnerabilities and security threats
Contingency plan for cyber managing critical threat vulnerabilities and security threatsThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Introducing Contingency Plan For Cyber Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Contingency Solutions, Contingency Considerations, using this template. Grab it now to reap its full benefits.
-
 Current potential implications managing critical threat vulnerabilities and security threats
Current potential implications managing critical threat vulnerabilities and security threatsThis slide provides information regarding the potential implications concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Deliver an outstanding presentation on the topic using this Current Potential Implications Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Increase Security Threats, Employees using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Determine sequence phases for managing critical threat vulnerabilities and security threats
Determine sequence phases for managing critical threat vulnerabilities and security threatsThis slide provides details regarding sequence phases for threat attack by threat actor in terms of installation, command and control, actions and objectives, covering tracks. Increase audience engagement and knowledge by dispensing information using Determine Sequence Phases For Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Installation, Command And Control, Actions And Objectives, Covering Tracks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine several threat actors managing critical threat vulnerabilities and security threats
Determine several threat actors managing critical threat vulnerabilities and security threatsThis slide provides details regarding several threat actors profile such as cyber criminal and hacktivists and addressing them on parameters such as motive, intent, capability, action, target victim, etc. Deliver an outstanding presentation on the topic using this Determine Several Threat Actors Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Determine Several Threat Actors Profile using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Determine staff training schedule managing critical threat vulnerabilities and security threats
Determine staff training schedule managing critical threat vulnerabilities and security threatsThe employees will also require external training which will play important role in their development. The external training will be given by experts of various fields. This training will not be free, and charges will cost the firm per employee. Introducing Determine Staff Training Schedule Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Advanced Software Training, Training Module, using this template. Grab it now to reap its full benefits.
-
 Determine threat scenario managing critical threat vulnerabilities and security threats
Determine threat scenario managing critical threat vulnerabilities and security threatsThis slide provides details regarding threat scenario assessment by understanding various phases of threat actor attack on victim. Present the topic in a bit more detail with this Determine Threat Scenario Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Threat Campaign, Actions And Objectives, Covering Tracks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Financial performance tracking managing critical threat vulnerabilities and security threats
Financial performance tracking managing critical threat vulnerabilities and security threatsThis slide presents the dashboard which will help firm in tracking the fiscal performance. This dashboard displays revenues and expenses trends and payment received analysis. Present the topic in a bit more detail with this Financial Performance Tracking Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Revenue And Expense Trends, Receivables Analysis. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
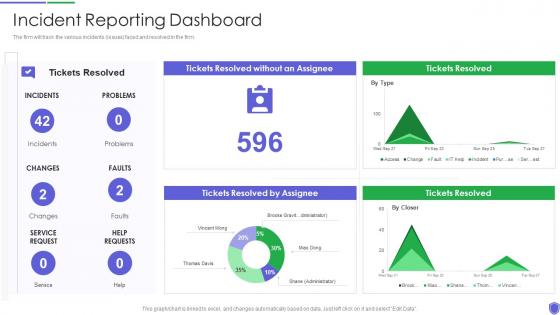 Incident reporting dashboard managing critical threat vulnerabilities and security threats
Incident reporting dashboard managing critical threat vulnerabilities and security threatsThe firm will track the various incidents issues faced and resolved in the firm. Present the topic in a bit more detail with this Incident Reporting Dashboard Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Incident Reporting Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Threats Vulnerabilities In Powerpoint And Google Slides Cpb
Security Threats Vulnerabilities In Powerpoint And Google Slides CpbPresenting our Security Threats Vulnerabilities In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Security Threats Vulnerabilities. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Recent Cyber Security Vulnerabilities In Powerpoint And Google Slides Cpb
Recent Cyber Security Vulnerabilities In Powerpoint And Google Slides CpbPresenting our Recent Cyber Security Vulnerabilities In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Recent Cyber Security Vulnerabilities This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Conducting Vulnerability Assessment To Respond And Recover Hands On Blockchain Security Risk BCT SS V
Conducting Vulnerability Assessment To Respond And Recover Hands On Blockchain Security Risk BCT SS VThe following slide showcases blockchain cybersecurity vulnerability assessment framework to optimize resilience and transparency. It includes key elements such as identify, protect, respond, recover, etc. Present the topic in a bit more detail with this Conducting Vulnerability Assessment To Respond And Recover Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Identity, Protect, Detect, Respond. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS V
Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS VThe following slide showcases key phases of penetration testing to identify potential flaws and malware. It includes elements of discovery phase such as architecture, compliance readiness, readiness analysis, etc. Introducing Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Architecture Of Blockchain, Compliance Readiness, Readiness Analysis, using this template. Grab it now to reap its full benefits.
-
 Reporting Analyzing Vulnerabilities Through Penetration Hands On Blockchain Security Risk BCT SS V
Reporting Analyzing Vulnerabilities Through Penetration Hands On Blockchain Security Risk BCT SS VThe following slide depicts brief summary of penetration testing report. it includes elements such as vulnerabilities, status, severity, risk score, unpatched operating system, cross site scripting, SQL injection, weak private key policies, misconfigured firewall rules, etc. Present the topic in a bit more detail with this Reporting Analyzing Vulnerabilities Through Penetration Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Vulnerabilities, Description, Status. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Conducting Vulnerability Assessment Securing Blockchain Transactions A Beginners Guide BCT SS V
Conducting Vulnerability Assessment Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity vulnerability assessment framework to optimize resilience and transparency. It includes key elements such as identify, protect, respond, recover, etc. Present the topic in a bit more detail with this Conducting Vulnerability Assessment Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Identity, Protect, Detect. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Reporting Analyzing Vulnerabilities Securing Blockchain Transactions A Beginners Guide BCT SS V
Reporting Analyzing Vulnerabilities Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts brief summary of penetration testing report . It includes elements such as vulnerabilities, status, severity, risk score, unpatched operating system, cross site scripting, SQL injection, weak private key policies, misconfigured firewall rules, etc. Present the topic in a bit more detail with this Reporting Analyzing Vulnerabilities Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Vulnerabilities, Status, Severity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Classify Assets Vulnerable To Cyber Attack Creating Cyber Security Awareness
Classify Assets Vulnerable To Cyber Attack Creating Cyber Security AwarenessThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Introducing Classify Assets Vulnerable To Cyber Attack Creating Cyber Security Awareness to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Sales Record, Customer Database, Product Database using this template. Grab it now to reap its full benefits.
-
 Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness
Identify Threat And Vulnerabilities Within Information System Creating Cyber Security AwarenessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness Dispense information and present a thorough explanation of Unclear Storage Mechanism, Monitor User Behaviour, No Appropriate Structure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ethical Hacking And Network Security Key Vulnerabilities That Ethical Hackers Check
Ethical Hacking And Network Security Key Vulnerabilities That Ethical Hackers CheckThis slide describes the critical vulnerabilities that ethical hackers check, such as injection attacks, modification in security configuration, exposure of critical information, and so on. Introducing Ethical Hacking And Network Security Key Vulnerabilities That Ethical Hackers Check to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Modification In Security Configurations, Exposure Of Critical Information, Authentication Standard Breach, Ethical Hackers Check, using this template. Grab it now to reap its full benefits.
-
 IoT Data Security Vulnerabilities And Privacy Concerns IoT Security And Privacy Safeguarding IoT SS
IoT Data Security Vulnerabilities And Privacy Concerns IoT Security And Privacy Safeguarding IoT SSThis slide includes common IoT security vulnerabilities and risk that helps organization implement security measures. It includes vulnerabilities such as lack of privacy protection, improper device management approach, default settings, weak credentials, etc. Increase audience engagement and knowledge by dispensing information using IoT Data Security Vulnerabilities And Privacy Concerns IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on six stages. You can also present information on Insecure Data Transfer, Weak Credentials, Insecure Default Settings using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Potential Security Vulnerabilities In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SS
Potential Security Vulnerabilities In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SSThis slide highlights security concerns in various areas of internet of things system in order to effectively address and mitigate such risks. It includes various components Of IoT ecosystem such as web and mobile application, cloud, communications, gateways, IoT sensors, etc. Increase audience engagement and knowledge by dispensing information using Potential Security Vulnerabilities In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on six stages. You can also present information on Insecure Communication, Closed Platforms, Communications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Modern Threats Exploiting Firewall Vulnerabilities
Firewall Network Security Modern Threats Exploiting Firewall VulnerabilitiesThis slide represents the various modern risks that can take advantage of firewall weaknesses. The purpose of this slide is to showcase the different current threats that can exploit firewall vulnerabilities, including insider attacks, DDoS attacks, malware and patching and configuration. Introducing Firewall Network Security Modern Threats Exploiting Firewall Vulnerabilities to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Requested Data, NAT Firewall, Forwarding Table using this template. Grab it now to reap its full benefits.
-
 Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security Threats
Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts some major assets that are more prone to cyber attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Present the topic in a bit more detail with this Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Sales Record, Customer Database, Product Database This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security
Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber SecurityThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security Dispense information and present a thorough explanation of Vulnerability, Threat, Threat Source using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Web Security Vulnerabilities And Their Prevention Strategies
Web Security Vulnerabilities And Their Prevention StrategiesThis slide covers common web security pitfalls and their mitigation strategies. The purpose of this slide is to help businesses in minimizing web related IT security pitfalls. It covers various prevention strategies to address web security vulnerabilities such as injection flaws, broken authentication, cross site scripting and security misconfiguration. Introducing our premium set of slides with Web Security Vulnerabilities And Their Prevention Strategies Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Injection Flaws, Broken Authentication, Cross Site Scripting So download instantly and tailor it with your information.
-
 Monitor Vulnerability Disclosure And Threat Intelligence Internet Of Things IoT Security Cybersecurity SS
Monitor Vulnerability Disclosure And Threat Intelligence Internet Of Things IoT Security Cybersecurity SSThis slide showcases vulnerability assessment disclosure and threat intelligence on internet of things IoT devices, referable for businesses in developing mitigation process. It provides details about continuous monitoring, correlation, disclosure, etc. Introducing Monitor Vulnerability Disclosure And Threat Intelligence Internet Of Things IoT Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Continuous Monitoring, Correlation With Metadata, Disclosure Implementation, using this template. Grab it now to reap its full benefits.
-
 Application Security Comparative Analysis Of Vulnerability Scanning And Penetration Testing
Application Security Comparative Analysis Of Vulnerability Scanning And Penetration TestingThis slide showcases the difference between vulnerability scanning and penetration testing based on aspects such as nature, purpose, etc. Present the topic in a bit more detail with this Application Security Comparative Analysis Of Vulnerability Scanning And Penetration Testing. Use it as a tool for discussion and navigation on Explores Weaknesses In Systems, Comparative Analysis, Vulnerability Scanning, Penetration Testing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Application Security Tools For Vulnerability Scanning In Security Testing
Application Security Tools For Vulnerability Scanning In Security TestingThis slide highlights the tools used for vulnerability scanning in security testing in application security which include Acunetix, Akto, etc. Present the topic in a bit more detail with this Application Security Tools For Vulnerability Scanning In Security Testing. Use it as a tool for discussion and navigation on Tools For Vulnerability, Scanning In Security Testing, Application Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Testing Types Vulnerability Scanning Application Security
Security Testing Types Vulnerability Scanning Application SecurityThis slide outlines the overview of vulnerability scanning in security testing for application security. Introducing Security Testing Types Vulnerability Scanning Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Assessing Security Readiness, Integral To Safeguarding Organizations, Identify System Security Weaknesses, using this template. Grab it now to reap its full benefits.
-
 Smart Contracts Security Measures Against Vulnerabilities Ppt File Outfit
Smart Contracts Security Measures Against Vulnerabilities Ppt File OutfitThis slide discusses the security measures of smart contracts against security vulnerability, these are security audits, penetration tests, and testing frameworks. Introducing Smart Contracts Security Measures Against Vulnerabilities Ppt File Outfit to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Security Audits, Testing Frameworks, Penetration Tests, Against Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
 Web Security Tools For Vulnerability Scanning
Web Security Tools For Vulnerability ScanningThis slide represents the tools utilized in scanning threats for web security which includes Qualys, SUCURI, Quttera, UpGuard Web Scan, etc. Introducing our Web Security Tools For Vulnerability Scanning set of slides. The topics discussed in these slides are Vulnerability Scanning, Vulnerability Management, Unknown Malware Detection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Top Web Application Security Vulnerabilities
Top Web Application Security VulnerabilitiesIntroducing our premium set of slides with Top Web Application Security Vulnerabilities Ellicudate the Eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Faulty Authentication, Object References So download instantly and tailor it with your information.
-
 Addressing Mobile Application Security Vulnerabilities For Effective Risk Protection
Addressing Mobile Application Security Vulnerabilities For Effective Risk ProtectionFollowing slide showcases application security vulnerabilities of mobiles for risk protection. It further includes factors such as poor server side controls, accidental data leak, poor authorization along side description, solution, etc. Introducing our Addressing Mobile Application Security Vulnerabilities For Effective Risk Protection set of slides. The topics discussed in these slides are Accidental Data Leak, Poor Authorization, Poor Server Side ControlsThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Architecture For Security Vulnerability In Iot
Architecture For Security Vulnerability In IotFollowing slide higlhights security vulnerability in IOT for protecting company sensitive data. It further covers personal and public network and also includes IoT devices, IoT gateway. Presenting our well structured Architecture For Security Vulnerability In Iot The topics discussed in this slide are Abstraction Level, Technical Details, Perception LayerThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Checklists For Security Vulnerability Web Application
Checklists For Security Vulnerability Web ApplicationFollowing slide highlights security vulnerability web application checklist for mitigation of risks. It further covers authenticate all files for configuration, authenticate all cyber variables along side priority and responsible person. Introducing our Checklists For Security Vulnerability Web Application set of slides. The topics discussed in these slides are Priority, Responsible Person, Shell EscapesThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Comparative Analysis Of Security Vulnerabilities Software Application
Comparative Analysis Of Security Vulnerabilities Software ApplicationFollowing slide highlights software applications security vulnerability analysis for enhanced user trust. It further covers tools, best used for, free trial, price and rating along with deployment such as desktop app, on premise and wab hosted etc. Presenting our well structured Comparative Analysis Of Security Vulnerabilities Software Application The topics discussed in this slide are Deployment , Free Trial, Our RatingThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Comparative Analysis Of Tools To Measure Security Vulnerability Performance
Comparative Analysis Of Tools To Measure Security Vulnerability PerformanceFollowing slide represents security vulnerability performance by comparative analysis tools for choosing best option. It further covers tools, free trials, price, reviews and features such as scan global and local network ranges, custom extension, etc. Introducing our Comparative Analysis Of Tools To Measure Security Vulnerability Performance set of slides. The topics discussed in these slides are Features, Free TrialThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Components Of Malware Systems Contributing To Security Vulnerabilities
Components Of Malware Systems Contributing To Security VulnerabilitiesFollowing slide showcases vulnerabilities in security caused by malware system components for reducing breach threat. It further covers components such as malware, social engineering attacks and outdated software. Presenting our set of slides with Components Of Malware Systems Contributing To Security Vulnerabilities This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malware, Social Engineering Attacks, Outdated Software
-
 Framework Structure Of Online Security Vulnerability Remedy Software
Framework Structure Of Online Security Vulnerability Remedy SoftwareFollowing slide highlights online security vulnerability remedy software framework structure for gaining competitive advantage. It further includes hunters, submit vulnerability reports, report to sync, customer, etc. Introducing our Framework Structure Of Online Security Vulnerability Remedy Software set of slides. The topics discussed in these slides are Hunters, Customer, DevelopersThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Methods To Test Security Vulnerabilities For Enhanced Safety
Methods To Test Security Vulnerabilities For Enhanced SafetyFollowing slide showcases security vulnerabilities test methods for enhanced safety. It further covers testing techniques such as active, passive, network and distributed testing. Introducing our premium set of slides with Methods To Test Security Vulnerabilities For Enhanced Safety Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Active Testing, Passive Testing, Network Testing So download instantly and tailor it with your information.
-
 Security Vulnerabilities In Smart Home Environment
Security Vulnerabilities In Smart Home EnvironmentFollowing slide represents smart home environment security vulnerabilities for prevention of breaches. It further covers internet gateway, smart lightning, remote access, video surveillance camera, access panel, etc. Introducing our Security Vulnerabilities In Smart Home Environment set of slides. The topics discussed in these slides are Internet Gateway, Video Surveillance Camera, Access PanelThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Strategies For Identifying Security Vulnerability In Network
Strategies For Identifying Security Vulnerability In NetworkFollowing slide represents identifying tactics of vulnerabilities in security network for improving data structure. It further covers run network audit, analyse system log data and audit IT supply chain. Presenting our set of slides with Strategies For Identifying Security Vulnerability In Network This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Run Network Audit, Analyse System Log Data, Audit IT Supply Chain
-
 Types Of Security Vulnerability Caused By Oversight
Types Of Security Vulnerability Caused By OversightFollowing slide highlights oversight due to security vulnerabilities type that lead to data breaching. It further covers types such as insider threat, lack of strong encryption, weak credentialing practices, etc. Presenting our set of slides with Types Of Security Vulnerability Caused By Oversight This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Insider Threat, Strong Encryption, Weak Credentialing Practices
-
 Web Security Upgradation Process Stages Of Implementing Vulnerability Scanning
Web Security Upgradation Process Stages Of Implementing Vulnerability ScanningThis slide gives an overview of the phases in the process of web security such as requirement analysis, test planning, test case development, etc. Present the topic in a bit more detail with this Web Security Upgradation Process Stages Of Implementing Vulnerability Scanning. Use it as a tool for discussion and navigation on Asset Inventory, Surface Scanning, Detection And Classification, Remediation Actions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Web Security Upgradation Steps For Implementing Vulnerability Scanning In Web Security
Web Security Upgradation Steps For Implementing Vulnerability Scanning In Web SecurityThis slide highlights the process phases for implementing vulnerability scanning which include creating asset inventory, scanning the attack surface, etc. Introducing Web Security Upgradation Steps For Implementing Vulnerability Scanning In Web Security to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Information Regarding Vulnerabilities Discovered, Creates Asset Inventory, using this template. Grab it now to reap its full benefits.
-
 Cyber Attacks Caused By IOT Security Vulnerabilities
Cyber Attacks Caused By IOT Security VulnerabilitiesThis slide showcases an overview of attacks that disrupt smooth functioning. Threats covered in the slide are IoT botnets and data exfiltration. Introducing our Cyber Attacks Caused By IOT Security Vulnerabilities set of slides. The topics discussed in these slides are Examples, Description, IOT Botnets, Data Exfiltration . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security Audits Report For Vulnerability Assessment Implementing E Commerce Security Measures
Security Audits Report For Vulnerability Assessment Implementing E Commerce Security MeasuresThe slide showcases security audit report to asses open vulnerabilities. It include vulnerability category, number of occurrences, and vulnerability level such as critical, high, medium and low. Present the topic in a bit more detail with this Security Audits Report For Vulnerability Assessment Implementing E Commerce Security Measures. Use it as a tool for discussion and navigation on Weak Authentication, Unauthorized Access, Security Misconfiguration, Payment Gateway Vulnerability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing Wireless Lan Security Threats And Vulnerabilities
Addressing Wireless Lan Security Threats And VulnerabilitiesThis slide showcases the security strategies that help companies to mitigate wireless LAN threats and vulnerabilities effectively. It includes threads such as IP, MAC spoofing, DNS cache spoofing, and Rogueevil twin access points. Introducing our Addressing Wireless Lan Security Threats And Vulnerabilities set of slides. The topics discussed in these slides are Threats And Vulnerabilities, Details, Security StrategiesThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.



