Powerpoint Templates and Google slides for Vulnerability Management
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Vulnerability management whitepaper overview ppt styles icon
Vulnerability management whitepaper overview ppt styles iconIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Overview Ppt Styles Icon. This template helps you present information on five stages. You can also present information on Vulnerability Management Plan, Vulnerability Management Process, List Sources Vulnerability Information, Definition Roles And Responsibilities, Approved Tools List using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper overview ppt styles rule
Vulnerability management whitepaper overview ppt styles ruleIntroducing Vulnerability Management Whitepaper Overview Ppt Styles Rule to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Management Strategy, List Stakeholders, Management Support, Budget Vulnerability Management, using this template. Grab it now to reap its full benefits.
-
 Vulnerability management whitepaper overview ppt styles style
Vulnerability management whitepaper overview ppt styles styleDeliver an outstanding presentation on the topic using this Vulnerability Management Whitepaper Overview Ppt Styles Style. Dispense information and present a thorough explanation of Security, Weakness, Technology, Vulnerability Management, Risk Management Program using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability management whitepaper provide training ppt styles template
Vulnerability management whitepaper provide training ppt styles templateIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Provide Training Ppt Styles Template. This template helps you present information on one stages. You can also present information on Organization, Skills To Appropriately, , Techniques, And Methodologies, Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper quotes ppt slides outfit
Vulnerability management whitepaper quotes ppt slides outfitPresent the topic in a bit more detail with this Vulnerability Management Whitepaper Quotes Ppt Slides Outfit. Use it as a tool for discussion and navigation on Quotes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability management whitepaper record discovered vulnerabilities ppt slide background
Vulnerability management whitepaper record discovered vulnerabilities ppt slide backgroundIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Record Discovered Vulnerabilities Ppt Slide Background. This template helps you present information on two stages. You can also present information on Risk Management, Team, Organizations Exposures, Vulnerability Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability management whitepaper resource the activities ppt styles background images
Vulnerability management whitepaper resource the activities ppt styles background imagesIntroducing Vulnerability Management Whitepaper Resource The Activities Ppt Styles Background Images to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Determine Stakeholder, Resource Responsibility, Opportunity, Business Operation, using this template. Grab it now to reap its full benefits.
-
 Vulnerability management whitepaper table of content ppt slides portrait
Vulnerability management whitepaper table of content ppt slides portraitPresent the topic in a bit more detail with this Vulnerability Management Whitepaper Table Of Content Ppt Slides Portrait. Use it as a tool for discussion and navigation on Introduction, Develop Plan, Vulnerability Management, Assess And Improve, Capability, Define Vulnerability Analysis And Resolution Strategy, Implement Vulnerability Analysis And Resolution Capability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability management whitepaper vulnerability management levels ppt styles show
Vulnerability management whitepaper vulnerability management levels ppt styles showIntroducing Vulnerability Management Whitepaper Vulnerability Management Levels Ppt Styles Show to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Automated Security Ecosystem, Committed Lifecycle Management, Proactive Execution, Purpose Driven Compliance, Primitive Operations, Importance Acknowledged, using this template. Grab it now to reap its full benefits.
-
 Vulnerability management whitepaper vulnerability management model ppt styles designs
Vulnerability management whitepaper vulnerability management model ppt styles designsDeliver an outstanding presentation on the topic using this Vulnerability Management Whitepaper Vulnerability Management Model Ppt Styles Designs. Dispense information and present a thorough explanation of Non Existent, Scanning, Assessment And Compliance, Analysis And Prioritization, Attack Management, Business Risk Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing threats vulnerabilities ppt powerpoint presentation layouts elements cpb
Managing threats vulnerabilities ppt powerpoint presentation layouts elements cpbPresenting our Managing Threats Vulnerabilities Ppt Powerpoint Presentation Layouts Elements Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Managing Threats Vulnerabilities This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Defining vulnerability rating effective information security risk management process
Defining vulnerability rating effective information security risk management processFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description.Present the topic in a bit more detail with this Defining Vulnerability Rating Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Occurrence Of Attack, Organization Is Reasonably, Organization Is Capable Enough. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing asset security managing critical threat vulnerabilities and security threats
Addressing asset security managing critical threat vulnerabilities and security threatsThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Introducing Addressing Asset Security Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ownership, Location, Confidentiality, Integrity, using this template. Grab it now to reap its full benefits.
-
 Addressing critical business managing critical threat vulnerabilities and security threats
Addressing critical business managing critical threat vulnerabilities and security threatsThis slide provides details regarding business functions recovery as firm needs to retrieve the crucial information based on priorities in various departments and time taken to retrieve the information. Present the topic in a bit more detail with this Addressing Critical Business Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Department, Priorities, Allowable Downtime. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing cyber threats in managing critical threat vulnerabilities and security threats
Addressing cyber threats in managing critical threat vulnerabilities and security threatsThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Increase audience engagement and knowledge by dispensing information using Addressing Cyber Threats In Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Healthcare, Manufacturing, Government, Energy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing indicators associated managing critical threat vulnerabilities and security threats
Addressing indicators associated managing critical threat vulnerabilities and security threatsThis slide provides details regarding indicators associated to insider threats in terms of traits, demeanor and goals, etc. Introducing Addressing Indicators Associated Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Authentication Levels, Data Exfiltration, Traits, Demeanor, using this template. Grab it now to reap its full benefits.
-
 Addressing internal and external managing critical threat vulnerabilities and security threats
Addressing internal and external managing critical threat vulnerabilities and security threatsThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Increase audience engagement and knowledge by dispensing information using Addressing Internal And External Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on two stages. You can also present information on Targeted Intelligence, Malware Intelligence, Reputation Intelligence, External Sources, Internal Sources using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing natural calamities managing critical threat vulnerabilities and security threats
Addressing natural calamities managing critical threat vulnerabilities and security threatsThis slide provides details regarding natural calamities posing as threat to organization and threat management checklist during nature crisis. Deliver an outstanding presentation on the topic using this Addressing Natural Calamities Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Threat Management Checklist using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Addressing several financial managing critical threat vulnerabilities and security threats
Addressing several financial managing critical threat vulnerabilities and security threatsThis slide provides information regarding the various financial scenarios that pose a threat to firm profitability and determine signs of financial distress. Introducing Addressing Several Financial Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Insolvency Scenario, Currency Scenario, Unexpected Fluctuations, Bankruptcy, using this template. Grab it now to reap its full benefits.
-
 Addressing threat management critical threat vulnerabilities and security threats
Addressing threat management critical threat vulnerabilities and security threatsThe threat management team needs to have strong critical and creative thinking skills so that they become capable in taking key decisions without complete or conflicting information under immense tensed situations. The team will be trained by experts who will also use scenario based activities and costing will be per employee basis. Present the topic in a bit more detail with this Addressing Threat Management Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Hypotheticals, Workshops, Field Exercises. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing various ways to managing critical threat vulnerabilities and security threats
Addressing various ways to managing critical threat vulnerabilities and security threatsThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Increase audience engagement and knowledge by dispensing information using Addressing Various Ways To Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Management Policies, User Accounts, Active Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing ways to handling managing critical threat vulnerabilities and security threats
Addressing ways to handling managing critical threat vulnerabilities and security threatsThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Introducing Addressing Ways To Handling Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cash Requirement, Financial Statements, Overheads Analysis, Currency Hedging, using this template. Grab it now to reap its full benefits.
-
 Budget for effective threat managing critical threat vulnerabilities and security threats
Budget for effective threat managing critical threat vulnerabilities and security threatsFirm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Deliver an outstanding presentation on the topic using this Budget For Effective Threat Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Incident Management, Risk Management, Client Onboarding Process, Document Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparative assessment of managing critical threat vulnerabilities and security threats
Comparative assessment of managing critical threat vulnerabilities and security threatsThis slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Present the topic in a bit more detail with this Comparative Assessment Of Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Insider Threat, Social Engineering, Maintenance Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Contingency plan for cyber managing critical threat vulnerabilities and security threats
Contingency plan for cyber managing critical threat vulnerabilities and security threatsThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Introducing Contingency Plan For Cyber Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Contingency Solutions, Contingency Considerations, using this template. Grab it now to reap its full benefits.
-
 Determine sequence phases for managing critical threat vulnerabilities and security threats
Determine sequence phases for managing critical threat vulnerabilities and security threatsThis slide provides details regarding sequence phases for threat attack by threat actor in terms of installation, command and control, actions and objectives, covering tracks. Increase audience engagement and knowledge by dispensing information using Determine Sequence Phases For Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Installation, Command And Control, Actions And Objectives, Covering Tracks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine several threat actors managing critical threat vulnerabilities and security threats
Determine several threat actors managing critical threat vulnerabilities and security threatsThis slide provides details regarding several threat actors profile such as cyber criminal and hacktivists and addressing them on parameters such as motive, intent, capability, action, target victim, etc. Deliver an outstanding presentation on the topic using this Determine Several Threat Actors Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Determine Several Threat Actors Profile using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Determine staff training schedule managing critical threat vulnerabilities and security threats
Determine staff training schedule managing critical threat vulnerabilities and security threatsThe employees will also require external training which will play important role in their development. The external training will be given by experts of various fields. This training will not be free, and charges will cost the firm per employee. Introducing Determine Staff Training Schedule Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Advanced Software Training, Training Module, using this template. Grab it now to reap its full benefits.
-
 Determine threat management managing critical threat vulnerabilities and security threats
Determine threat management managing critical threat vulnerabilities and security threatsThe threat management team generally comprise of senior management personnel that have authority and resources to accelerate the companys internal incident response. They will be responsible in managing human impacts both employees and community, company reputation, share values, and corporate assets. Increase audience engagement and knowledge by dispensing information using Determine Threat Management Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on two stages. You can also present information on Determine Threat Management Team Structure using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine threat scenario managing critical threat vulnerabilities and security threats
Determine threat scenario managing critical threat vulnerabilities and security threatsThis slide provides details regarding threat scenario assessment by understanding various phases of threat actor attack on victim. Present the topic in a bit more detail with this Determine Threat Scenario Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Threat Campaign, Actions And Objectives, Covering Tracks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Different kinds of insider digital managing critical threat vulnerabilities and security threats
Different kinds of insider digital managing critical threat vulnerabilities and security threatsThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Introducing Different Kinds Of Insider Digital Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Third Party Insider, Malicious Insider, using this template. Grab it now to reap its full benefits.
-
 Ensuring collaboration among managing critical threat vulnerabilities and security threats
Ensuring collaboration among managing critical threat vulnerabilities and security threatsThis slide provides details regarding ensuring collaboration among various functional areas in order to minimize insider cyber threats. Increase audience engagement and knowledge by dispensing information using Ensuring Collaboration Among Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on ten stages. You can also present information on Human Resources, Procurement, Public Relations, Compliance, Legal using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ensuring vital records maintenance managing critical threat vulnerabilities and security threats
Ensuring vital records maintenance managing critical threat vulnerabilities and security threatsThis slide provides information regarding vital record maintenance in order to store crucial information and the location where these records are kept also details about the alternate backup location of the records and the other sources through which records can be retrieved. Introducing Ensuring Vital Records Maintenance Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Settlement Agreements, Primary Location, using this template. Grab it now to reap its full benefits.
-
 Evaluating financial practices in firm managing critical threat vulnerabilities and security threats
Evaluating financial practices in firm managing critical threat vulnerabilities and security threatsThe firm can track the financial performance by looking the financial practices it follows in order to avoid any early signs of financial distress. Deliver an outstanding presentation on the topic using this Evaluating Financial Practices In Firm Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Accounting, Short Term Expenses, Financial Statements using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 How financial risk can be controlled managing critical threat vulnerabilities and security threats
How financial risk can be controlled managing critical threat vulnerabilities and security threatsThis slide provides details regarding various ways through financial risks can be controlled by handling liquidity risk, foreign exchange risk and credit exchange risk. Increase audience engagement and knowledge by dispensing information using How Financial Risk Can Be Controlled Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on three stages. You can also present information on Liquidity Risk, Exchange Risk, Credit Exchange Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Impact analysis for effective managing critical threat vulnerabilities and security threats
Impact analysis for effective managing critical threat vulnerabilities and security threatsThis slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Introducing Impact Analysis For Effective Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Security Requirement, Focus Areas, using this template. Grab it now to reap its full benefits.
-
 Impact analysis of successful managing critical threat vulnerabilities and security threats
Impact analysis of successful managing critical threat vulnerabilities and security threatsThis slide depicts the impact of successful implementation of threat management in terms improved incident management and customer satisfaction and depicts that how much the focus area has been improved from the previous state. Increase audience engagement and knowledge by dispensing information using Impact Analysis Of Successful Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Focus Area, Past State, Present State, Benefit using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
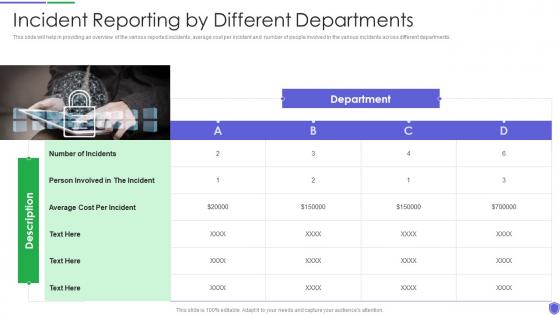 Incident reporting by different managing critical threat vulnerabilities and security threats
Incident reporting by different managing critical threat vulnerabilities and security threatsThis slide will help in providing an overview of the various reported incidents, average cost per incident and number of people involved in the various incidents across different departments. Increase audience engagement and knowledge by dispensing information using Incident Reporting By Different Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on one stages. You can also present information on Incident Reporting By Different Departments using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key activities checklist associated to managing critical threat vulnerabilities and security threats
Key activities checklist associated to managing critical threat vulnerabilities and security threatsThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Introducing Key Activities Checklist Associated To Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Plan And Collect, Review And Analyze, Develop Strategic Framework, using this template. Grab it now to reap its full benefits.
-
 Managing critical threat vulnerabilities and security threats addressing various ways to handle
Managing critical threat vulnerabilities and security threats addressing various ways to handleThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Increase audience engagement and knowledge by dispensing information using Managing Critical Threat Vulnerabilities And Security Threats Addressing Various Ways To Handle. This template helps you present information on four stages. You can also present information on Risk Assessment, End User, Networks And Individuals using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Managing critical threat vulnerabilities and security threats determine sequence phases
Managing critical threat vulnerabilities and security threats determine sequence phasesThis slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Introducing Managing Critical Threat Vulnerabilities And Security Threats Determine Sequence Phases to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reconnaissance, Weaponization, Delivery, Exploitation, using this template. Grab it now to reap its full benefits.
-
 Managing critical threat vulnerabilities and security threats table of contents
Managing critical threat vulnerabilities and security threats table of contentsIncrease audience engagement and knowledge by dispensing information using Managing Critical Threat Vulnerabilities And Security Threats Table Of Contents. This template helps you present information on four stages. You can also present information on Impact Assessment, Dashboard, Budget Assessment, Leveraging Workforce, Assets Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Roles and responsibilities to managing critical threat vulnerabilities and security threats
Roles and responsibilities to managing critical threat vulnerabilities and security threatsThis slide provides details regarding roles and responsibilities assigned to ensure minimum violence work environment. Introducing Roles And Responsibilities To Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Employee Responsibilities, Manager Responsibilities, Unit Responsibilities, Human Resources Responsibilities, using this template. Grab it now to reap its full benefits.
-
 Selecting secured threat management managing critical threat vulnerabilities and security threats
Selecting secured threat management managing critical threat vulnerabilities and security threatsThis slide will help firm in choosing the suitable automated threat management software which is to handle existing security and privacy issues and predict upcoming threats. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Deliver an outstanding presentation on the topic using this Selecting Secured Threat Management Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Security Incident, Automated Workflows, Access Rights using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Statistics associated to workplace managing critical threat vulnerabilities and security threats
Statistics associated to workplace managing critical threat vulnerabilities and security threatsThis slide provides details regarding statistics associated to workplace threats that firms face in terms of data records theft, workplace violence, financial phishing, etc. Increase audience engagement and knowledge by dispensing information using Statistics Associated To Workplace Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on five stages. You can also present information on Cyber Attacks Cost, Organizations Face, Data Records using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table of contents managing critical threat vulnerabilities and security threats
Table of contents managing critical threat vulnerabilities and security threatsIntroducing Table Of Contents Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Current Scenario Assessment, Digital Assets, Physical Security, using this template. Grab it now to reap its full benefits.
-
 Technological assessment of managing critical threat vulnerabilities and security threats
Technological assessment of managing critical threat vulnerabilities and security threatsThis slide provides details regarding present management capabilities assessment based on several parameters such as incidents and service requests handling rate, service failure rate, customer satisfaction score, etc. Present the topic in a bit more detail with this Technological Assessment Of Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Industry Standard, Firms Standard, Customer Satisfaction Score. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Threat management action managing critical threat vulnerabilities and security threats
Threat management action managing critical threat vulnerabilities and security threatsThe threat management action plan will help in keeping the track of various potential threats that are existing in the firm. The person responsible in handling the threats will keep track of the duration in which threat is resolved. Deliver an outstanding presentation on the topic using this Threat Management Action Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Threat Identification, Threat Treatment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Various types of workplace violence managing critical threat vulnerabilities and security threats
Various types of workplace violence managing critical threat vulnerabilities and security threatsThis slide provides details regarding various types of workplace violence threats created by people in terms of stalking, physical assault, harassment or intimidation, etc. Increase audience engagement and knowledge by dispensing information using Various Types Of Workplace Violence Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on six stages. You can also present information on Threatening Behavior Stalking, Physical Assault, Harassment And Intimidation, Property Damage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Workplace employee assistance managing critical threat vulnerabilities and security threats
Workplace employee assistance managing critical threat vulnerabilities and security threatsThe employee assistance program will help firm in enhancing their well being at workplace and enable them to handle critical situations. This program will render services like clinical services, work and life services and employer services, etc. Introducing Workplace Employee Assistance Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Clinical Services, Online Resources, Offline Resources, Employer Services, using this template. Grab it now to reap its full benefits.
-
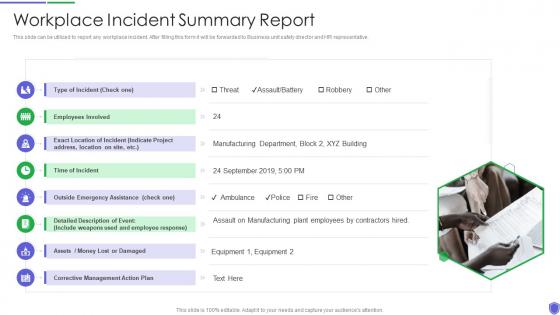 Workplace incident summary managing critical threat vulnerabilities and security threats
Workplace incident summary managing critical threat vulnerabilities and security threatsThis slide can be utilized to report any workplace incident. After filling this form it will be forwarded to Business unit safety director and HR representative. Increase audience engagement and knowledge by dispensing information using Workplace Incident Summary Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on one stages. You can also present information on Employees, Corrective Management, Time Of Incident using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Threat vulnerability asset matrix managing cyber risk in a digital age
Threat vulnerability asset matrix managing cyber risk in a digital ageMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Threat Vulnerability Asset Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Improve it security with vulnerability management how siem works
Improve it security with vulnerability management how siem worksIncrease audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management How Siem Works. This template helps you present information on four stages. You can also present information on Databases, Applications, Security Device using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix
Information Security Program Cybersecurity Management Threat Vulnerability Asset MatrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Management Framework For Information Security Defining Vulnerability Rating With Criteria
Risk Management Framework For Information Security Defining Vulnerability Rating With CriteriaFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Present the topic in a bit more detail with this Risk Management Framework For Information Security Defining Vulnerability Rating With Criteria. Use it as a tool for discussion and navigation on Vulnerability Ranking, Organization, High, Low, Medium. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Management Framework For Information Security Threat Identification And Vulnerability
Risk Management Framework For Information Security Threat Identification And VulnerabilityFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security Threat Identification And Vulnerability. Dispense information and present a thorough explanation of Communication And Network, Database, Failure To Segment Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cybersecurity Risk Management Framework Defining Vulnerability Rating
Cybersecurity Risk Management Framework Defining Vulnerability RatingFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Defining Vulnerability Rating. Dispense information and present a thorough explanation of Occurrence Attack, Asset Moderately Susceptible, Asset Highly Susceptible using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
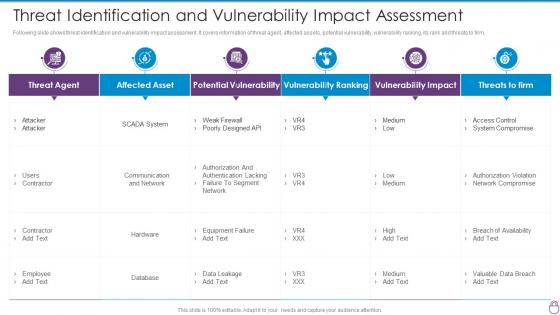 Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact
Cybersecurity Risk Management Framework Threat Identification And Vulnerability ImpactFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact. Dispense information and present a thorough explanation of Threat Agent, Affected Asset, Potential Vulnerability, Vulnerability Ranking, Vulnerability Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enterprise vulnerability management determine tools aligned to the strategy
Enterprise vulnerability management determine tools aligned to the strategyIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Determine Tools Aligned To The Strategy. This template helps you present information on five stages. You can also present information on Publish Authorized, Exception Process, Conduct Periodic Reviews using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise vulnerability management develop a plan revision process
Enterprise vulnerability management develop a plan revision processIntroducing Enterprise Vulnerability Management Develop A Plan Revision Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Review The Changes, Vulnerability Information, Update Toolset If Necessary, using this template. Grab it now to reap its full benefits.





