Powerpoint Templates and Google slides for Use
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Usb security shield and tools for data safety ppt slides
Usb security shield and tools for data safety ppt slidesPresenting usb security shield and tools for data safety ppt slides. This is a usb security shield and tools for data safety ppt slides. This is a two stage process. The stages in this process are security.
-
 User login page with password verification ppt slides
User login page with password verification ppt slidesPresenting user login page with password verification ppt slides. This is a user login page with password verification ppt slides. This is a one stage process. The stages in this process are security.
-
 Using resources providing direction ppt slides
Using resources providing direction ppt slidesPresenting using resources providing direction ppt slides. This is a using resources providing direction ppt slides. This is a four stage process. The stages in this process are finding innovative solutions, embracing change, using resources, providing direction.
-
 Pass document approval using stamp holder
Pass document approval using stamp holderPresenting pass document approval using stamp holder. This is a pass document approval using stamp holder. This is a one stage process. The stages in this process are pass, progress, proceed.
-
 Login page of account with user id and password
Login page of account with user id and passwordPresenting this set of slides with name - Login Page Of Account With User Id And Password. This is a one stage process. The stages in this process are Security, Login, Authentication.
-
 Login with username and password and sign in
Login with username and password and sign inPresenting this set of slides with name - Login With Username And Password And Sign In. This is a one stage process. The stages in this process are Security, Login, Authentication.
-
 Problem solving icon using lock and key
Problem solving icon using lock and keyPresenting this set of slides with name - Problem Solving Icon Using Lock And Key. This is a three stages process. The stages in this process are Problem Solving Icon, Problem Statement And Solution Icon, Challenges And Solutions Icon.
-
 Application user interface authentication login
Application user interface authentication loginPresenting this set of slides with name Application User Interface Authentication Login. This is a three stage process. The stages in this process are Application User Interface Authentication Login. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Our equipments used for security bid proposal ppt powerpoint presentation infographic
Our equipments used for security bid proposal ppt powerpoint presentation infographicPresenting this set of slides with name Our Equipments Used For Security Bid Proposal Ppt Powerpoint Presentation Infographic. This is a eight stage process. The stages in this process are 2 Way Radios, Mobile Phones, Cameras, Surveillance Technology And Software, Vehicles, Security Trailers. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Online information security system icon for protecting user data
Online information security system icon for protecting user dataPresenting this set of slides with name Online Information Security System Icon For Protecting User Data. This is a one stage process. The stages in this process are Online Information, Security System, Icon Protecting, User Data. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 User profile information security icon with gear wheel
User profile information security icon with gear wheelPresenting this set of slides with name User Profile Information Security Icon With Gear Wheel. This is a four stage process. The stages in this process are User Profile, Information Security, Icon, Gear Wheel. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Woman using vpn technology for data security
Woman using vpn technology for data securityPresenting this set of slides with name Woman Using VPN Technology For Data Security. This is a three stage process. The stages in this process are Woman Using VPN Technology For Data Security. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cyber monitoring of system using biometric security identification icon
Cyber monitoring of system using biometric security identification iconPresenting this set of slides with name Cyber Monitoring Of System Using Biometric Security Identification Icon. This is a three stage process. The stages in this process are Cyber Monitoring Of System Using Biometric Security Identification Icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 User authentication human firewall security icon
User authentication human firewall security iconPresenting this set of slides with name User Authentication Human Firewall Security Icon. This is a three stage process. The stages in this process are User Authentication Human Firewall Security Icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Different technologies used in ammunition disposal detonation ppt slides
Different technologies used in ammunition disposal detonation ppt slidesWith technological advancement, we are capable in developing ammunition destruction plants that can be customized. We provide eco friendly and cost effective ammunition disposal. This slide presents various technologies used. Presenting this set of slides with name Different Technologies Used In Ammunition Disposal Detonation Ppt Slides. This is a one stage process. The stages in this process are Open Detonation, Application, Type Of Technology, Detonation Chamber, Fluidized Bed. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Application user interface through authorization icon
Application user interface through authorization iconPresenting this set of slides with name Application User Interface Through Authorization Icon. This is a three stage process. The stages in this process are Application User Interface Through Authorization Icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Key used to open locked door
Key used to open locked doorPresenting this set of slides with name Key Used To Open Locked Door. This is a three stage process. The stages in this process are Key Used To Open Locked Door. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Unlocking active user profile icon
Unlocking active user profile iconPresenting our set of slides with Unlocking Active User Profile Icon. This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Unlocking Active User Profile Icon.
-
 User profile and information privacy icon
User profile and information privacy iconIntroducing our premium set of slides with User Profile And Information Privacy Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like User Profile And Information Privacy Icon. So download instantly and tailor it with your information.
-
 User icon depicting secured personal account
User icon depicting secured personal accountPresenting our set of slides with User Icon Depicting Secured Personal Account. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on User Icon Depicting Secured Personal Account.
-
 Employee protecting data by using firewall network security device
Employee protecting data by using firewall network security devicePresenting our set of slides with Employee Protecting Data By Using Firewall Network Security Device. This exhibits information on one stage of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Employee Protecting Data By Using Firewall Network Security Device.
-
 Tools used in cloud security cloud security it ppt inspiration
Tools used in cloud security cloud security it ppt inspirationThis slide represents the list of tools utilized under cloud security systems to protect, manage, store and control data on the cloud.Introducing Tools Used In Cloud Security Cloud Security It Ppt Inspiration to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Tools Used In Cloud Security, using this template. Grab it now to reap its full benefits.
-
 Our equipments used for security guard services proposal ppt slides background designs
Our equipments used for security guard services proposal ppt slides background designsIntroducing Our Equipments Used For Security Guard Services Proposal Ppt Slides Background Designs to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Surveillance, Technology And Software, Security Trailers, Mobile Phones, using this template. Grab it now to reap its full benefits.
-
 Information Security And Risk Management User Information Security Risk Management
Information Security And Risk Management User Information Security Risk ManagementThis slide showcases expenses done by organization in different segments of information security and risk management. Key segments include - application security, cloud security, data security, identify access management, infrastructure protection, integrated risk management, security services etc. Introducing Information Security And Risk Management User Information Security Risk Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Marketing Segment, Identity Access Management, Information Security, using this template. Grab it now to reap its full benefits.
-
 User Access Management Open Source Tools Icon
User Access Management Open Source Tools IconIntroducing our premium set of slides with User Access Management Open Source Tools Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like User Access Management, Open Source Tools, Icon. So download instantly and tailor it with your information.
-
 Zero Trust Network Access User Flow Overview Ppt Outline Design Inspiration
Zero Trust Network Access User Flow Overview Ppt Outline Design InspirationThis slide describes the overview of zero trust network access user flow. The purpose of this slide is to showcase how the user moves into a network when the ZTNA security model is applied. The key components include a remote user, MFA, security policies, a cloud data center and a branch office. Increase audience engagement and knowledge by dispensing information using Zero Trust Network Access User Flow Overview Ppt Outline Design Inspiration. This template helps you present information on four stages. You can also present information on Particular Network, Security, Device using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Network Security Using Secure Web Gateway Table Of Contents
Network Security Using Secure Web Gateway Table Of ContentsIntroducing Network Security Using Secure Web Gateway Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Organization, Implementation, Timeline using this template. Grab it now to reap its full benefits.
-
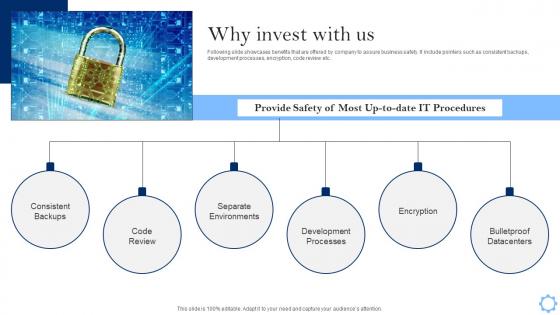 Why Invest With Us Fundraising Pitch Deck For Project Management Software
Why Invest With Us Fundraising Pitch Deck For Project Management SoftwareFollowing slide showcases benefits that are offered by company to assure business safety. It include pointers such as consistent backups, development processes, encryption, code review etc. Increase audience engagement and knowledge by dispensing information using Why Invest With Us Fundraising Pitch Deck For Project Management Software. This template helps you present information on six stages. You can also present information on Consistent Backups, Separate Environments, Development Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Digital Transformation In FMCG Using E Commerce Platform Icon
Digital Transformation In FMCG Using E Commerce Platform IconIntroducing our premium set of slides with Digital Transformation In FMCG Using E Commerce Platform Icon Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Digital Transformation, FMCG Using, E Commerce Platform Icon So download instantly and tailor it with your information.
-
 Manage Anti Virus Dashboard Using EDR Solutions
Manage Anti Virus Dashboard Using EDR SolutionsPresenting our set of slides with name Manage Anti Virus Dashboard Using EDR Solutions. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Manage Anti Virus Dashboard, Device Status, Attention Required, Security Risks.
-
 Mitigate EDR Incidents Icon Using Cybersecurity Technology
Mitigate EDR Incidents Icon Using Cybersecurity TechnologyPresenting our set of slides with name Mitigate EDR Incidents Icon Using Cybersecurity Technology. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Mitigate EDR Incidents, Icon Using Cybersecurity Technology.
-
 Tools And Techniques Used In Network Security
Tools And Techniques Used In Network SecurityThis slide showcases common tools of network security used in business including Metasploit, nessus, argus, wire shark, and air crack.Introducing our premium set of slides with name Tools And Techniques Used In Network Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Metasploit, Argus, Nessus, Wireshark, Aircrack. So download instantly and tailor it with your information.


