Powerpoint Templates and Google slides for Trusts
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Building a help desk user intimacy approach to develop trustworthy consumer base
Building a help desk user intimacy approach to develop trustworthy consumer baseThe following slide highlights the help desk software request type and detail which showcases status, priority and alert level. Present the topic in a bit more detail with this Building A Help Desk User Intimacy Approach To Develop Trustworthy Consumer Base. Use it as a tool for discussion and navigation on Product Replacement, Request Type, Bad Behavior. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Building tier based customer user intimacy approach to develop trustworthy consumer base
Building tier based customer user intimacy approach to develop trustworthy consumer baseThis slide illustrates tier based customer loyally program overview with multiple facilities offered by company such as coupon code. Access to VIP sales, early access to sales etc. Present the topic in a bit more detail with this Building Tier Based Customer User Intimacy Approach To Develop Trustworthy Consumer Base. Use it as a tool for discussion and navigation on Building Tier Based Customer Loyalty Program. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Establishing customer engagement user intimacy approach to develop trustworthy consumer base
Establishing customer engagement user intimacy approach to develop trustworthy consumer baseUnder this slide we are highlighting strategic plan for enhancing customer engagement with brand. It shows engagement objectives, engagement approach, engagement tools etc. Present the topic in a bit more detail with this Establishing Customer Engagement User Intimacy Approach To Develop Trustworthy Consumer Base. Use it as a tool for discussion and navigation on Engagement Approach, Engagement Objectives, Engagement Tool, Engagement Frequency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Establishing two way user intimacy approach to develop trustworthy consumer base
Establishing two way user intimacy approach to develop trustworthy consumer baseThis slide depicts a comprehensive strategic plan for communicating business objectives to customers. It includes date of communication and key channels being used to communicate objectives. Deliver an outstanding presentation on the topic using this Establishing Two Way User Intimacy Approach To Develop Trustworthy Consumer Base. Dispense information and present a thorough explanation of Establishing Two Way Communication Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Launching social media user intimacy approach to develop trustworthy consumer base
Launching social media user intimacy approach to develop trustworthy consumer baseThis slide highlights the social media campaign launch details which includes campaign objective, campaign message, campaign type, prospect type title, prospect type size and customer segment. Present the topic in a bit more detail with this Launching Social Media User Intimacy Approach To Develop Trustworthy Consumer Base. Use it as a tool for discussion and navigation on Campaign Objective, Campaign Massage, Campaign Type. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
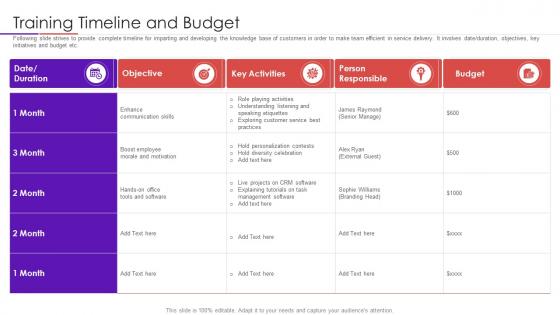 Training timeline and budget user intimacy approach to develop trustworthy consumer base
Training timeline and budget user intimacy approach to develop trustworthy consumer baseFollowing slide strives to provide complete timeline for imparting and developing the knowledge base of customers in order to make team efficient in service delivery. It involves date duration, objectives, key initiatives and budget etc. Increase audience engagement and knowledge by dispensing information using Training Timeline And Budget User Intimacy Approach To Develop Trustworthy Consumer Base. This template helps you present information on two stages. You can also present information on Objective, Key Activities, Person Responsible, Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Understanding types of user intimacy approach to develop trustworthy consumer base
Understanding types of user intimacy approach to develop trustworthy consumer baseFollowing slide provides a brief understanding of multiple types of loyalty program in order to make decision regarding which type of program best suits your company requirements. Present the topic in a bit more detail with this Understanding Types Of User Intimacy Approach To Develop Trustworthy Consumer Base. Use it as a tool for discussion and navigation on Program Types, Loyalty Program, Ecommerce. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Consumer Trust Statistics In Powerpoint And Google Slides Cpb
Consumer Trust Statistics In Powerpoint And Google Slides CpbIntroducing our well-designed Consumer Trust Statistics In Powerpoint And Google Slides Cpb. This PowerPoint design presents information on topics like Consumer Trust Statistics. As it is predesigned it helps boost your confidence level. It also makes you a better presenter because of its high-quality content and graphics. This PPT layout can be downloaded and used in different formats like PDF, PNG, and JPG. Not only this, it is available in both Standard Screen and Widescreen aspect ratios for your convenience. Therefore, click on the download button now to persuade and impress your audience.
-
 Case Study Duracell Trust Power Using Emotional And Rational Branding For Better Customer Outreach
Case Study Duracell Trust Power Using Emotional And Rational Branding For Better Customer OutreachThis slide showcases detailed case study of Duracells Trust Your Power campaign for generating social and motivational awareness amongst general public. It provides details about customer base, positive messages, donation, young athletes, YouTube views, etc. Present the topic in a bit more detail with this Case Study Duracell Trust Power Using Emotional And Rational Branding For Better Customer Outreach. Use it as a tool for discussion and navigation on Motivational, Awareness, Generating. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparative Analysis For Top Real Estate Investment Trusts
Comparative Analysis For Top Real Estate Investment TrustsThis slide compares various real estate investment trusts available in market to analyze industry growth potential of each. It includes details about annual revenue, scale and environmental initiatives. Presenting our well structured Comparative Analysis For Top Real Estate Investment Trusts. The topics discussed in this slide are Annual Revenue, Scale In Square Feet, Environmental Initiatives. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Case Study Duracell Trust Your Campaign Increasing Product Awareness And Customer Engagement
Case Study Duracell Trust Your Campaign Increasing Product Awareness And Customer EngagementThis slide showcases detailed case study of Duracells Trust Your Power campaign for generating social and motivational awareness amongst general public. It provides details about customer base, positive messages, donation, young athletes, YouTube views, etc. Present the topic in a bit more detail with this Case Study Duracell Trust Your Campaign Increasing Product Awareness And Customer Engagement. Use it as a tool for discussion and navigation on Motivational, Awareness, Customer. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Duracell Trust Your Power Emotional Implementation Of Neuromarketing Tools To Understand Customer
Duracell Trust Your Power Emotional Implementation Of Neuromarketing Tools To Understand CustomerThis slide represents case study for Duracell that launched a campaign trust your power to build emotional connection with its customers through empowerment. It include details regarding building brand impression, customer engagement etc. Deliver an outstanding presentation on the topic using this Duracell Trust Your Power Emotional Implementation Of Neuromarketing Tools To Understand Customer. Dispense information and present a thorough explanation of Marketing, Awareness, Success using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 F1026 Case Study Duracell Trust Your Power Enhancing Consumer Engagement Through Emotional Advertising
F1026 Case Study Duracell Trust Your Power Enhancing Consumer Engagement Through Emotional AdvertisingThis slide showcases detailed case study of Duracells Trust Your Power campaign for generating social and motivational awareness amongst general public. It provides details about customer base, positive messages, donation, young athletes, YouTube views, etc. Deliver an outstanding presentation on the topic using this F1026 Case Study Duracell Trust Your Power Enhancing Consumer Engagement Through Emotional Advertising. Dispense information and present a thorough explanation of Impressions, Awareness, Motivational using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Automating HR Compliance With Management Software Mitigating Risks And Building Trust Strategy SS
Automating HR Compliance With Management Software Mitigating Risks And Building Trust Strategy SSThis slide compares multiple HR compliance management software to select the right tool for optimizing HR compliance operations. It also includes criteria for selection. Deliver an outstanding presentation on the topic using this Automating HR Compliance With Management Software Mitigating Risks And Building Trust Strategy SS. Dispense information and present a thorough explanation of Key Features, Management, Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Compliance Strategy Implementation Timeline With Roles Mitigating Risks And Building Trust Strategy SS
Compliance Strategy Implementation Timeline With Roles Mitigating Risks And Building Trust Strategy SSThis slide represents a timeline detailing key responsibilities and roles for implementing company wide compliance program. It includes teams, quarterly timeline and key activities. Present the topic in a bit more detail with this Compliance Strategy Implementation Timeline With Roles Mitigating Risks And Building Trust Strategy SS. Use it as a tool for discussion and navigation on Responsibilities, Roles, Timeline. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Curriculum For Employee Workplace Health And Safety Mitigating Risks And Building Trust Strategy SS
Curriculum For Employee Workplace Health And Safety Mitigating Risks And Building Trust Strategy SSThis slide outlines a training plan on workplace health and safety improvement. It includes training on equipment safety, chemical handling, emergency response and general safety. Present the topic in a bit more detail with this Curriculum For Employee Workplace Health And Safety Mitigating Risks And Building Trust Strategy SS. Use it as a tool for discussion and navigation on Equipment Safety, Chemical Handling, Emergency Response. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Developing Formal Corporate Policies Procedures And Mitigating Risks And Building Trust Strategy SS
Developing Formal Corporate Policies Procedures And Mitigating Risks And Building Trust Strategy SSThis slide outlines policies, procedures and standards to be established within the organization. It includes policies such as, code of conduct, whistleblower, data protection, health and safety and risk management. Deliver an outstanding presentation on the topic using this Developing Formal Corporate Policies Procedures And Mitigating Risks And Building Trust Strategy SS. Dispense information and present a thorough explanation of Code Of Conduct, Whistleblower Policy, Data Protection Policy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Educating And Training Employees About Regulatory Mitigating Risks And Building Trust Strategy SS
Educating And Training Employees About Regulatory Mitigating Risks And Building Trust Strategy SSThis slide present a program outline to provide regular trainings to employees on different regulatory requirements. It includes training on requirements such as data privacy, workplace safety, and financial reporting regulations. Present the topic in a bit more detail with this Educating And Training Employees About Regulatory Mitigating Risks And Building Trust Strategy SS. Use it as a tool for discussion and navigation on Workplace Safety Regulations, Data Privacy Regulations, Financial Reporting Regulations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ensure Compliance With Data Protection Laws And Mitigating Risks And Building Trust Strategy SS
Ensure Compliance With Data Protection Laws And Mitigating Risks And Building Trust Strategy SSThis slide presents an overview of data protection regulations. It includes aspects such as regulation, purpose, applicability and key points. Present the topic in a bit more detail with this Ensure Compliance With Data Protection Laws And Mitigating Risks And Building Trust Strategy SS. Use it as a tool for discussion and navigation on Protection, Data, Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Establishing Code Of Conduct And Ethics Policies To Mitigating Risks And Building Trust Strategy SS
Establishing Code Of Conduct And Ethics Policies To Mitigating Risks And Building Trust Strategy SSThis slide presents key policies and guidelines to establish code of conduct and ethics in the company. It includes policies such as honesty and integrity, respect and dignity, confidentiality and privacy, responsibility and accountability. Present the topic in a bit more detail with this Establishing Code Of Conduct And Ethics Policies To Mitigating Risks And Building Trust Strategy SS. Use it as a tool for discussion and navigation on Policies, Employee, Establishing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Evaluating Company Current Level Of Compliance With Mitigating Risks And Building Trust Strategy SS
Evaluating Company Current Level Of Compliance With Mitigating Risks And Building Trust Strategy SSThis slide defines key techniques for determining the present level of compliance in the company. It includes methods such as internal review, external audit, compliance surveys and risk assessments. Present the topic in a bit more detail with this Evaluating Company Current Level Of Compliance With Mitigating Risks And Building Trust Strategy SS. Use it as a tool for discussion and navigation on Internal Review, External Audit, Compliance Surveys. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 HR Compliance Checklist To Identify Areas Of Non Mitigating Risks And Building Trust Strategy SS
HR Compliance Checklist To Identify Areas Of Non Mitigating Risks And Building Trust Strategy SSThis slide represents a checklist to ensure human resource compliance at workplace. It includes compliance areas such as employment law, anti discrimination, wage and hour, workplace safety, employee benefits and recordkeeping. Deliver an outstanding presentation on the topic using this HR Compliance Checklist To Identify Areas Of Non Mitigating Risks And Building Trust Strategy SS. Dispense information and present a thorough explanation of Employment Law Compliance, Workplace Safety Compliance, Recordkeeping Compliance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identifying Essential Resources And Budget For Mitigating Risks And Building Trust Strategy SS
Identifying Essential Resources And Budget For Mitigating Risks And Building Trust Strategy SSThis slide analyzes and allocates quarterly budget for multiple compliance management initiatives. It includes initiatives such as technology implementation, legal and regulatory compliance, risk assessments, communication and training and data compliance management. Present the topic in a bit more detail with this Identifying Essential Resources And Budget For Mitigating Risks And Building Trust Strategy SS. Use it as a tool for discussion and navigation on Management, Budget, Identifying. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identifying Potential Areas Of Risk And Vulnerability Mitigating Risks And Building Trust Strategy SS
Identifying Potential Areas Of Risk And Vulnerability Mitigating Risks And Building Trust Strategy SSThis slide presents key methods for locating compliances weak spots and risky places in business. It includes methods such as risk assessment, compliance audits, incident and complaint analysis, benchmarking and expert opinion. Deliver an outstanding presentation on the topic using this Identifying Potential Areas Of Risk And Vulnerability Mitigating Risks And Building Trust Strategy SS. Dispense information and present a thorough explanation of Risk Assessment, Compliance Audits, Benchmarking using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Overview Of Workplace Health And Safety Compliance Mitigating Risks And Building Trust Strategy SS
Overview Of Workplace Health And Safety Compliance Mitigating Risks And Building Trust Strategy SSThis slide presents an overview of workplace health and safety compliance. It includes compliances such as compliance with safety regulations, hazard identificationand assessment, employee training, emergency preparedness, workplace ergonomics. Deliver an outstanding presentation on the topic using this Overview Of Workplace Health And Safety Compliance Mitigating Risks And Building Trust Strategy SS. Dispense information and present a thorough explanation of Hazard Identification, Assessment, Employee Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Quality Control Processes To Ensure Compliance Mitigating Risks And Building Trust Strategy SS
Quality Control Processes To Ensure Compliance Mitigating Risks And Building Trust Strategy SSThis slide outlines quality control processes to ensure compliance of quality of products, services, or processes. It includes information about processes such as inspection, testing, statistical process control and six sigma. Present the topic in a bit more detail with this Quality Control Processes To Ensure Compliance Mitigating Risks And Building Trust Strategy SS. Use it as a tool for discussion and navigation on Products, Services, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
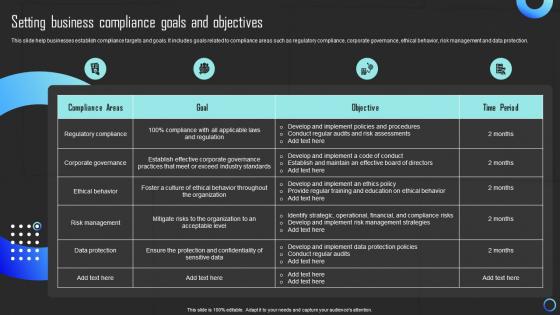 Setting Business Compliance Goals And Objectives Mitigating Risks And Building Trust Strategy SS
Setting Business Compliance Goals And Objectives Mitigating Risks And Building Trust Strategy SSThis slide help businesses establish compliance targets and goals. It includes goals related to compliance areas such as regulatory compliance, corporate governance, ethical behavior, risk management and data protection. Present the topic in a bit more detail with this Setting Business Compliance Goals And Objectives Mitigating Risks And Building Trust Strategy SS. Use it as a tool for discussion and navigation on Goals, Business, Objectives. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Severity Gap Between Predicted And Actual Risks Mitigating Risks And Building Trust Strategy SS
Severity Gap Between Predicted And Actual Risks Mitigating Risks And Building Trust Strategy SSThis slide highlights the severity gap between predicted and actual risks alongside the compliance status for each risk. It includes information about risks such as, cyberattack, product defect, workplace accidents, supply chain disruptions, regulatory risk and employee risks. Present the topic in a bit more detail with this Severity Gap Between Predicted And Actual Risks Mitigating Risks And Building Trust Strategy SS. Use it as a tool for discussion and navigation on Predicted, Severity, Risks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Taking Corrective Actions Against Business Ethical And Mitigating Risks And Building Trust Strategy SS
Taking Corrective Actions Against Business Ethical And Mitigating Risks And Building Trust Strategy SSThis slide highlights ethical and compliance risk present in the company. It includes information about risks such as, bribery and corruption, conflicts of interest, data privacy and security, discrimination and harassment, environment and health safety. Deliver an outstanding presentation on the topic using this Taking Corrective Actions Against Business Ethical And Mitigating Risks And Building Trust Strategy SS. Dispense information and present a thorough explanation of Business, Compliance, Actions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Guide To Digital Marketing Collateral Types Of Case Studies To Build Trust MKT SS
Guide To Digital Marketing Collateral Types Of Case Studies To Build Trust MKT SSThe following slide showcases types of case studies used in marketing collaterals with its description and usage. It presents types such as problem solution, results oriented, testimonials, industry specific an process. Present the topic in a bit more detail with this Guide To Digital Marketing Collateral Types Of Case Studies To Build Trust MKT SS. Use it as a tool for discussion and navigation on Product, Service, Specific Industry. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Guide To Digital Marketing Collateral Types Of Testimonials To Gain Customers Trust MKT SS
Guide To Digital Marketing Collateral Types Of Testimonials To Gain Customers Trust MKT SSThe following slide showcases types of case studies used in marketing collaterals with its description and usage. It presents types such as written testimonials, video testimonials, case studies, social proof, customer reviews and trade references. Present the topic in a bit more detail with this Guide To Digital Marketing Collateral Types Of Testimonials To Gain Customers Trust MKT SS. Use it as a tool for discussion and navigation on Social Proof, Video Testimonials, Customer Reviews. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Zero Trust Network Access Implementation Challenges Ppt Layouts Shapes
Zero Trust Network Access Implementation Challenges Ppt Layouts ShapesThis slide outlines the main challenges of ZTNA implementation. The purpose of this slide is to highlight the primary challenges that organizations face while deploying ZTNA. The challenges include continual management and maintenance, low productivity, security risks, and so on. Deliver an outstanding presentation on the topic using this Zero Trust Network Access Implementation Challenges Ppt Layouts Shapes. Dispense information and present a thorough explanation of Management, Comprehensive System, Productivity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Zero Trust Network Access Performance Tracking Dashboard Ppt Pictures Outline
Zero Trust Network Access Performance Tracking Dashboard Ppt Pictures OutlineThis slide represents the performance tracking dashboard for zero trust network access. The purpose of this slide is to showcase the level of request modes, connected users, daily usage of the network, security rating, device risk and threat flow. Present the topic in a bit more detail with this Zero Trust Network Access Performance Tracking Dashboard Ppt Pictures Outline. Use it as a tool for discussion and navigation on Zero Trust Network, Performance Tracking Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Zero Trust Network Access Vs Zero Trust Architecture Ppt Ideas Guidelines
Zero Trust Network Access Vs Zero Trust Architecture Ppt Ideas GuidelinesThis slide represents the comparison between zero trust network access and zero trust architecture. The purpose of this slide is to highlight the key differences between ZTNA and ZTA based on definition, focus, objective, technologies, and implementation. Present the topic in a bit more detail with this Zero Trust Network Access Vs Zero Trust Architecture Ppt Ideas Guidelines. Use it as a tool for discussion and navigation on Key Area, Implementation, Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 ZTNA Checklist To Build Zero Trust Network Access Architecture
ZTNA Checklist To Build Zero Trust Network Access ArchitectureThis slide outlines the checklist to develop a zero trust network access architecture. The purpose of this slide is to define the various measures organizations should take while building a ZTNA architecture. The measures include knowing the architecture, creating a strong device identity, and so on. Present the topic in a bit more detail with this ZTNA Checklist To Build Zero Trust Network Access Architecture. Use it as a tool for discussion and navigation on Network, Resources, Communication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 ZTNA Critical Principles Of Zero Trust Network Access Model
ZTNA Critical Principles Of Zero Trust Network Access ModelThis slide illustrates the key principles of zero trust network access model, including their impact. The purpose of this slide is to highlight the primary principles of the ZTNA model, including least privilege access, micro segmentation, MFA, device validation, and monitoring everything. Deliver an outstanding presentation on the topic using this ZTNA Critical Principles Of Zero Trust Network Access Model. Dispense information and present a thorough explanation of Security Management, Administration System, Potential Attackers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 ZTNA Key Points To Choose Zero Trust Solution Ppt Inspiration Show
ZTNA Key Points To Choose Zero Trust Solution Ppt Inspiration ShowThis slide highlights the main criteria while choosing the right zero trust solution for the organization. The purpose of this slide is to showcase the key points the businesses should keep in mind while selecting the ZTNA vendor. The main points include vendor support, zero trust technology type, and so on. Deliver an outstanding presentation on the topic using this ZTNA Key Points To Choose Zero Trust Solution Ppt Inspiration Show. Dispense information and present a thorough explanation of Entity Behaviour Analytics, Global Distribution, Legacy Application Support using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Trust Boundary Across Azure Confidential Computing Services Confidential Cloud Computing
Trust Boundary Across Azure Confidential Computing Services Confidential Cloud ComputingThis slide showcases how confidential computing provides total privacy assurance through technical assurance. It also includes the hyper-protect crypto service architecture, including its components such as application user, user interface, application, data service, and data at rest. Present the topic in a bit more detail with this Trust Boundary Across Azure Confidential Computing Services Confidential Cloud Computing. Use it as a tool for discussion and navigation on Confidential, Computing, Services. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Cloud Computing Intel Sgx With A Smaller Trusted Computing Base Tcb
Confidential Cloud Computing Intel Sgx With A Smaller Trusted Computing Base TcbThis slide describes the deployment of applications in Intel SGX with smaller TCB. The purpose of this slide is to showcase the difference between standard deployment and deployment in TEE. The main components include the operating system, virtual machine monitor, applications and hardware. Deliver an outstanding presentation on the topic using this Confidential Cloud Computing Intel Sgx With A Smaller Trusted Computing Base Tcb. Dispense information and present a thorough explanation of Sensitive Applications, Environment, Experience using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Cloud Computing Process Of Using Intel Sgx Based Trusted Applications
Confidential Cloud Computing Process Of Using Intel Sgx Based Trusted ApplicationsThis slide outlines the process of using intel sgx-based trusted applications. The purpose of this slide is to demonstrate the procedure of utilizing intel sgx-based trusted applications. The main components include applying for a key, installing the environment, developing, computing and building, and executing. Deliver an outstanding presentation on the topic using this Confidential Cloud Computing Process Of Using Intel Sgx Based Trusted Applications. Dispense information and present a thorough explanation of Applications, Process, Environment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Cloud Computing Trusted Execution Environment Tee Hardware Platform
Confidential Cloud Computing Trusted Execution Environment Tee Hardware PlatformThis slide represents the trusted execution environment hardware platform used in confidential computing. The TEE environment is supported by three hardware platforms covering Intel SGX, ARM TrustZone, and Advanced Micro Devices AMD. Deliver an outstanding presentation on the topic using this Confidential Cloud Computing Trusted Execution Environment Tee Hardware Platform. Dispense information and present a thorough explanation of Execution, Environment, Hardware Platform using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Cloud Computing What Is Trusted Execution Environment Tee In Confidential Computing
Confidential Cloud Computing What Is Trusted Execution Environment Tee In Confidential ComputingThis slide outlines the overview of the trusted execution environment used in confidential computing to protect the in-use data. The purpose of this slide is to showcase the overview, and properties of TEE, such as confidentiality, data integrity and code integrity. It also includes the other offerings of TEE environments. Deliver an outstanding presentation on the topic using this Confidential Cloud Computing What Is Trusted Execution Environment Tee In Confidential Computing. Dispense information and present a thorough explanation of Execution, Environment, Confidential Computing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Top Zero Trust Network Access Software Solutions Identity Defined Networking
Top Zero Trust Network Access Software Solutions Identity Defined NetworkingThis slide illustrates the top software solution for zero-trust network access. The purpose of this slide is to showcase the prominent tools for ZTNA implementation, including Okta identity-driven security, ping identity, Google BeyondCorp, Twingate, Permiter 81 and so on. Deliver an outstanding presentation on the topic using this Top Zero Trust Network Access Software Solutions Identity Defined Networking Dispense information and present a thorough explanation of Google Beyondcorp, Zscaler Private Access, Access Cloud using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Zero Trust Network Access Vs Zero Trust Architecture Identity Defined Networking
Zero Trust Network Access Vs Zero Trust Architecture Identity Defined NetworkingThis slide represents the comparison between zero-trust network access and zero-trust architecture. The purpose of this slide is to highlight the key differences between ZTNA and ZTA based on definition, focus, objective, technologies, and implementation. Deliver an outstanding presentation on the topic using this Zero Trust Network Access Vs Zero Trust Architecture Identity Defined Networking Dispense information and present a thorough explanation of Definition, Objective, Technologies, Implementation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Challenges Of VPN Based Remote Access Solutions Zero Trust Architecture ZTA
Challenges Of VPN Based Remote Access Solutions Zero Trust Architecture ZTAThis slide outlines the limitations of virtual private network-based remote access services. The purpose of this slide is to showcase the various challenges of the VPN network system and how the zero trust network model can overcome those issues. Present the topic in a bit more detail with this Challenges Of VPN Based Remote Access Solutions Zero Trust Architecture ZTA. Use it as a tool for discussion and navigation on Implicit Trust, Performance Problems, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Checklist To Build Zero Trust Network Access Architecture Ppt Diagram Lists
Checklist To Build Zero Trust Network Access Architecture Ppt Diagram ListsThis slide outlines the checklist to develop a zero-trust network access architecture. The purpose of this slide is to define the various measures organizations should take while building a ZTNA architecture. The measures include knowing the architecture, creating a strong device identity, and so on. Deliver an outstanding presentation on the topic using this Checklist To Build Zero Trust Network Access Architecture Ppt Diagram Lists. Dispense information and present a thorough explanation of Public Network, Network Topology, Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Features Of Zero Trust Network Access Security Model Ppt File Files
Features Of Zero Trust Network Access Security Model Ppt File FilesThis slide represents the main features of ZTNA. The purpose of this slide is to showcase the various features of zero trust network access, including safeguarding private apps, connecting security controls to apps more closely, restriction of access, recognizing internal app use, and so on. Present the topic in a bit more detail with this Features Of Zero Trust Network Access Security Model Ppt File Files. Use it as a tool for discussion and navigation on Safeguards Private Apps, Features, Description. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Characteristics Of Modern ZTNA Solution Zero Trust Architecture ZTA
Key Characteristics Of Modern ZTNA Solution Zero Trust Architecture ZTAThis slide outlines the top features that a modern ZTNA model should include. This slide highlights the characteristics of modern ZTNA solutions, including data loss prevention, scalable performance, granular visibility and reporting, BYOD deployment options, advanced threat protection, and SASE offering. Present the topic in a bit more detail with this Key Characteristics Of Modern ZTNA Solution Zero Trust Architecture ZTA. Use it as a tool for discussion and navigation on DLP Features, ZTNA System, Modern Work Environments. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Points To Choose Zero Trust Solution Ppt File Layouts
Key Points To Choose Zero Trust Solution Ppt File LayoutsThis slide highlights the main criteria while choosing the right zero trust solution for the organization. The purpose of this slide is to showcase the key points the businesses should keep in mind while selecting the ZTNA vendor. The main points include vendor support, zero trust technology type, and so on. Deliver an outstanding presentation on the topic using this Key Points To Choose Zero Trust Solution Ppt File Layouts. Dispense information and present a thorough explanation of Type Of Zero Trust Technology, Vendor Support, Behaviour Analytics using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Main Pillars Of Zero Network Trust Access Ppt File Outline
Main Pillars Of Zero Network Trust Access Ppt File OutlineThis slide outlines the critical pillars of the zero network trust access model. The purpose of this slide is to showcase the primary pillars of ZTNA, including users, devices, networks, infrastructure, applications, data, visibility and analytics, and orchestration and automation. Deliver an outstanding presentation on the topic using this Main Pillars Of Zero Network Trust Access Ppt File Outline. Dispense information and present a thorough explanation of Device, Network, Infrastructure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Overview Of Zero Trust Solution Categories Zero Trust Architecture ZTA
Overview Of Zero Trust Solution Categories Zero Trust Architecture ZTAThis slide represents the overview of zero-trust solution categories, including MFA, SSO, identity and access management, zero-trust network access and secure access service edge. The purpose of this slide is to give an overview of zero-trust technologies and their benefits. Deliver an outstanding presentation on the topic using this Overview Of Zero Trust Solution Categories Zero Trust Architecture ZTA. Dispense information and present a thorough explanation of Accounts Authorization, Login Credentials, Enterprise Applications using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Steps To Implement Zero Trust Network Access Model Zero Trust Architecture ZTA
Steps To Implement Zero Trust Network Access Model Zero Trust Architecture ZTAThis slide outlines the crucial steps to implement the zero trust network access model in an organization. The purpose of this slide is to highlight the key steps to perform to deploy the ZTNA model. The steps include identifying assets, defining protection surface, understanding the businesss security model, etc. Present the topic in a bit more detail with this Steps To Implement Zero Trust Network Access Model Zero Trust Architecture ZTA. Use it as a tool for discussion and navigation on Protection Surface, Security Model, Mapping Transaction Flows. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Technologies Used In Zero Trust Network Access Ppt File Clipart
Technologies Used In Zero Trust Network Access Ppt File ClipartThis slide represents the techniques used in the zero-trust network access model. The purpose of this slide is to showcase the multiple technologies used in the ZTNA model, including their functions and the network protection they offer. Present the topic in a bit more detail with this Technologies Used In Zero Trust Network Access Ppt File Clipart. Use it as a tool for discussion and navigation on Network Access Control, Device Access Control, Microsegmentation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Top Zero Trust Network Access Software Solutions Ppt File Graphics
Top Zero Trust Network Access Software Solutions Ppt File GraphicsThis slide illustrates the top software solution for zero-trust network access. The purpose of this slide is to showcase the prominent tools for ZTNA implementation, including Okta identity-driven security, ping identity, Google BeyondCorp, Twingate, Permiter 81 and so on. Present the topic in a bit more detail with this Top Zero Trust Network Access Software Solutions Ppt File Graphics. Use it as a tool for discussion and navigation on SSO Authentication, MFA Verification, Scalable. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Zero Trust Network Access Implementation Challenges Ppt File Rules
Zero Trust Network Access Implementation Challenges Ppt File RulesThis slide outlines the main challenges of ZTNA implementation. The purpose of this slide is to highlight the primary challenges that organizations face while deploying ZTNA. The challenges include continual management and maintenance, low productivity, security risks, and so on. Present the topic in a bit more detail with this Zero Trust Network Access Implementation Challenges Ppt File Rules. Use it as a tool for discussion and navigation on Hardware, Security Vulnerabilities, Software Modifications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Zero Trust Architecture ZTA Critical Principles Of Zero Trust Network Access Model
Zero Trust Architecture ZTA Critical Principles Of Zero Trust Network Access ModelThis slide illustrates the key principles of zero trust network access model, including their impact. The purpose of this slide is to highlight the primary principles of the ZTNA model, including least privilege access, micro-segmentation, MFA, device validation, and monitoring everything. Deliver an outstanding presentation on the topic using this Zero Trust Architecture ZTA Critical Principles Of Zero Trust Network Access Model. Dispense information and present a thorough explanation of Privilege Access, Micro Segmentation, Device Validation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Zero Trust Architecture ZTA Difference Between ZTNA And Software Defined Perimeter
Zero Trust Architecture ZTA Difference Between ZTNA And Software Defined PerimeterThis slide outlines the comparison between zero trust network access and software-defined perimeter. The purpose of this slide is to highlight the key difference between the two security approaches based on definitional, key features, deployment, use cases, benefits and challenges. Present the topic in a bit more detail with this Zero Trust Architecture ZTA Difference Between ZTNA And Software Defined Perimeter. Use it as a tool for discussion and navigation on Key Features, Deployment, Benefits. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTA
M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTAThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Deliver an outstanding presentation on the topic using this M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTA. Dispense information and present a thorough explanation of Factors, Traditional Security Model, ZTNA using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 M73 Training Program For Zero Trust Network Access Model Zero Trust Architecture ZTA
M73 Training Program For Zero Trust Network Access Model Zero Trust Architecture ZTAThis slide outlines the training program for implementing the zero-trust network access model in the organization. The purpose of this slide is to highlight the training agenda, objectives, system requirements, mode of training and cost of the training. Present the topic in a bit more detail with this M73 Training Program For Zero Trust Network Access Model Zero Trust Architecture ZTA. Use it as a tool for discussion and navigation on Agenda, Objectives, System Requirements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategies For Trusting Employees With Implementing Strategies To Enhance Employee Rating Strategy SS
Strategies For Trusting Employees With Implementing Strategies To Enhance Employee Rating Strategy SSThis slide showcases techniques for trusting employees with time management. It includes strategies such as flexible work arrangements, goal oriented time management, provide time management training and encourage regular breaks. Present the topic in a bit more detail with this Strategies For Trusting Employees With Implementing Strategies To Enhance Employee Rating Strategy SS Use it as a tool for discussion and navigation on Strategy, Description, Impact This template is free to edit as deemed fit for your organization. Therefore download it now.




