Powerpoint Templates and Google slides for Terrorism
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Best Advanced Threat Protection Software
Best Advanced Threat Protection SoftwareThe following slide exhibits diverse specialized software that helps in detecting unauthorized, and external attacks to private systems. Introducing our premium set of slides with Best Advanced Threat Protection Software. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protection, Endpoint, Networks. So download instantly and tailor it with your information.
-
 Checklist Before Implementing Advanced Threat Protection Solutions
Checklist Before Implementing Advanced Threat Protection SolutionsThis slide represents the checklist to effectively ensure the effective deployment of advanced threat protection solutions within the systems. Presenting our set of slides with Checklist Before Implementing Advanced Threat Protection Solutions. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementing, Advanced, Protection.
-
 Cloud Based Advanced Threat Protection Icon
Cloud Based Advanced Threat Protection IconIntroducing our premium set of slides with Cloud Based Advanced Threat Protection Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protection, Cloud, Advanced. So download instantly and tailor it with your information.
-
 Cloud Integration With Advanced Threat Protection Solutions
Cloud Integration With Advanced Threat Protection SolutionsThe mentioned slide outlines key considerations of indulging cloud technology with advanced threat protection to mitigate sophisticated cyber threats effectively. Presenting our set of slides with Cloud Integration With Advanced Threat Protection Solutions. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Machine, Intelligence, Analytics.
-
 Comparing Advanced Threat Protection Tools
Comparing Advanced Threat Protection ToolsThe mentioned slide showcases a comparison of various advanced threat protection tools to protect systems crucial data. Presenting our well structured Comparing Advanced Threat Protection Tools. The topics discussed in this slide are Techniques, Security, Platforms. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Core Features Of Advanced Security Threats
Core Features Of Advanced Security ThreatsThe mentioned slides highlights various components of advanced security threat that helps with crucial security vulnerabilities. Presenting our set of slides with Core Features Of Advanced Security Threats. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vulnerabilities, Information, Periods.
-
 Emerging Trends In Advanced Threat Protection
Emerging Trends In Advanced Threat ProtectionThe purpose of this slide is to exhibit latest trends associated with advanced threat protection such as usage of AI, edge computing security, blockchain for IoT security, etc. Introducing our premium set of slides with Emerging Trends In Advanced Threat Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security, Device, Cybersecurity. So download instantly and tailor it with your information.
-
 Integrating AI With Advanced Threat Protection Icon
Integrating AI With Advanced Threat Protection IconIntroducing our Integrating AI With Advanced Threat Protection Icon set of slides. The topics discussed in these slides are Protection, Threat, Integrating. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 IoT Cyber Security Technologies For Advanced Threat Protection
IoT Cyber Security Technologies For Advanced Threat ProtectionThe purpose of this slide is to showcase various types of Internet of Things IoT security technologies that assists in safeguarding cyber threats. Introducing our premium set of slides with IoT Cyber Security Technologies For Advanced Threat Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Architecture, Security, Computing. So download instantly and tailor it with your information.
-
 Process To Formulate Advanced Threat Protection Measures
Process To Formulate Advanced Threat Protection MeasuresThe purpose of the mentioned slide is to showcase various steps involved in creating advanced threat protection solutions. Presenting our set of slides with Process To Formulate Advanced Threat Protection Measures. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prepare, Report, Design.
-
 Real World Example Of Advanced Threat Protection Effectiveness
Real World Example Of Advanced Threat Protection EffectivenessThe mentioned slide showcases real life instances of utilizing advanced threat protection solutions that contribute to a proactive defense strategy. Introducing our premium set of slides with Real World Example Of Advanced Threat Protection Effectiveness. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ransomware, Destructive, Analytics. So download instantly and tailor it with your information.
-
 Solutions To Overcome Advanced Threat Protection Implementation Challenges
Solutions To Overcome Advanced Threat Protection Implementation ChallengesThe purpose of this slide is to showcase various solutions that assist in resolving issues while implementing advanced threat protection solutions in the systems. Presenting our set of slides with Solutions To Overcome Advanced Threat Protection Implementation Challenges. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Standardization, Security, Physical.
-
 Various Attacks Remediate By Advanced Threat Protection
Various Attacks Remediate By Advanced Threat ProtectionThe following slide showcases different types of potential attacks and their possible remediate solutions offered by advanced threat protection. Introducing our premium set of slides with Various Attacks Remediate By Advanced Threat Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ransomware, Engineering, Exploits. So download instantly and tailor it with your information.
-
 Types Of Threats In IT Infrastructure Security
Types Of Threats In IT Infrastructure SecurityThis slide showcases the common threats faced in infrastructure security. Its aim is to identify threats and eliminate them. This slide includes phishing, ransomware, botnet and physical theft. Presenting our set of slides with Types Of Threats In IT Infrastructure Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Infrastructure, Personal, Exploitation.
-
 Saas Cyber Security Icon For Threat Mitigation
Saas Cyber Security Icon For Threat MitigationIntroducing our premium set of slides with Saas Cyber Security Icon For Threat Mitigation Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Saas Cyber Security Icon, Threat Mitigation. So download instantly and tailor it with your information.
-
 External Threats To Data Security Management With Solutions
External Threats To Data Security Management With SolutionsThis slide showcases various external threats that affect the data security management of businesses with solutions to mitigate those risks. It includes various threats such as SQL injection, ransomware, phishing, and accidental exposure. Introducing our premium set of slides with External Threats To Data Security Management With Solutions. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Accidental Exposure, Unwanted Operations, Secure Mechanism. So download instantly and tailor it with your information.
-
 Security Management Policies To Mitigate Internal Data Threats
Security Management Policies To Mitigate Internal Data ThreatsThis slide focuses on the policies for security management helping companies to mitigate internal data threats efficiently. It includes policies for metadata, backup, internal protocol, emails, etc. Introducing our premium set of slides with Security Management Policies To Mitigate Internal Data Threats. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protocol For Visitors, Internet Protocol, Security Audit. So download instantly and tailor it with your information.
-
 Threats To Mobile Computing In Corporate Environment
Threats To Mobile Computing In Corporate EnvironmentThis slide depicts the threats to mobile computing in corporate environments. The purpose of this slide is to help the business install suitable measures to prevent mobile computing threats. It includes data loss, information leaks, etc. Introducing our premium set of slides with Threats To Mobile Computing In Corporate Environment. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Leaks, Insufficient Management Tools, Unsecure WIFI Network. So download instantly and tailor it with your information.
-
 Impact Of Cyber Security Threats On Organisational Policy
Impact Of Cyber Security Threats On Organisational PolicyThis slide covers the negative impacts of prevalent cybersecurity threats. This template aims to highlight two key negative impacts of threats, including DNS Attacks, SQL Injection, Malware, Phishing, and Ransomware. Presenting our set of slides with Impact Of Cyber Security Threats On Organisational Policy This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malware, DNS Attack, SQL Injection
-
 File Integrity Monitoring Use Cases For Threat Reduction
File Integrity Monitoring Use Cases For Threat ReductionThis slide covers File Integrity Monitoring FIM Use Cases. The purpose of this template is to highlight the diverse applications of File Integrity Monitoring in enhancing cybersecurity. It includes detecting cyberattacks, expediting threat detection, identifying weaknesses, and streamlining compliance efforts. Presenting our set of slides with File Integrity Monitoring Use Cases For Threat Reduction This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detecting Cyberattack, Expediting Threat Detection, Identifying Weaknesses
-
 Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity Matrix
Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity MatrixThe following slide depicts cyber security risk assessment grid to prioritize and eliminate occurrence of threats. It includes elements such as moderate, severe, minor, negligible, rate, possible, likely, unlikely etc. Introducing Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity Matrix to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Very Severe, Severe, Moderate using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Data Threat Detection Icon
Cybersecurity Data Threat Detection IconPresenting our well structured Cybersecurity Data Threat Detection Icon. The topics discussed in this slide are Cybersecurity Data, Threat Detection, Icon. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 SWOT Analysis Threat Advisory Services Provider Profile Company Profile CP SS V
SWOT Analysis Threat Advisory Services Provider Profile Company Profile CP SS VThis slide represents SWOT analysis highlighting threats to the company. It includes details regarding intense competition and political uncertainty. Increase audience engagement and knowledge by dispensing information using SWOT Analysis Threat Advisory Services Provider Profile Company Profile CP SS V This template helps you present information on four stages. You can also present information on Intense Competition, Political Uncertainty using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SWOT Analysis Threat Ernst And Young Company Profile CP SS
SWOT Analysis Threat Ernst And Young Company Profile CP SSThis slide represents SWOT analysis highlighting threats to the company. It includes details regarding intense competition and political uncertainty. Introducing SWOT Analysis Threat Ernst And Young Company Profile CP SS to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Intense Competition, Political Uncertainty using this template. Grab it now to reap its full benefits.
-
 SWOT Analysis Threats Athletics Equipment Company Profile CP SS V
SWOT Analysis Threats Athletics Equipment Company Profile CP SS VThis slide focuses on Threats to evaluate competitive position of company. It assists business to determine internal and external factors affecting growth and development. Introducing SWOT Analysis Threats Athletics Equipment Company Profile CP SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Counterfeit Products, Economic Fluctuations, Changing Consumer Preferences using this template. Grab it now to reap its full benefits.
-
 ATP Cyber Security Threat Detection System
ATP Cyber Security Threat Detection SystemThis slide depicts the ATP cyber security detection system. Its aim is to use various approach to kill off any threats during cyber attack. This slide includes multilayer approach, behavioural analysis, machine learning, sand boxing, threat intelligence, etc. Presenting our set of slides with name ATP Cyber Security Threat Detection System. This exhibits information on Nine stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Multilayered Approach, Behavioural Analysis, Machine Learning, Threat Intelligence, Endpoint Detection.
-
 BCP Cybersecurity Icon To Address Information Threats Effectively
BCP Cybersecurity Icon To Address Information Threats EffectivelyPresenting our set of slides with BCP Cybersecurity Icon To Address Information Threats Effectively This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on BCP Cybersecurity, Address Information, Threats Effectively
-
 Strategies To Mitigate SCADA Network Cybersecurity Threats
Strategies To Mitigate SCADA Network Cybersecurity ThreatsThis slide represents various strategies that assist companies to mitigate various SCADA network threats for enhancing data cybersecurity. It includes various threats such as hackers, malware, and employees. In Presenting our well structured Strategies To Mitigate SCADA Network Cybersecurity Threats The topics discussed in this slide are Hackers, Malware, Employees. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Mobile Security Threats And Risk Assessment
Mobile Security Threats And Risk AssessmentThis slide showcases risk and threat evaluation of mobile security and includes security breaches, phishing attacks, and mobile ransomware. Introducing our Mobile Security Threats And Risk Assessment set of slides. The topics discussed in these slides are Security Breaches, Phishing Attacks, Mobile Ransomware. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Threat Icon To Prevent Gap
Cyber Security Threat Icon To Prevent GapPresenting our set of slides with name Cyber Security Threat Icon To Prevent Gap. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Threat, Icon Prevent Gap.
-
 Threat Detection Icon To Manage Security Gap
Threat Detection Icon To Manage Security GapPresenting our set of slides with name Threat Detection Icon To Manage Security Gap. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Threat Detection Icon, Manage Security Gap.
-
 SWOT Analysis Threats Digital Restaurant Reservation Company Profile CP SS V
SWOT Analysis Threats Digital Restaurant Reservation Company Profile CP SS VMentioned slide provides information about threats faced by company. It includes threats such as competitors, technological disruption, and regulatory changes. Increase audience engagement and knowledge by dispensing information using SWOT Analysis Threats Digital Restaurant Reservation Company Profile CP SS V This template helps you present information on three stages. You can also present information on Technology Disruptions, Competition, Regulatory Changes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Impact Analysis Of Cybersecurity Threats In Retail Industry
Impact Analysis Of Cybersecurity Threats In Retail IndustryThis slide highlights impact assessment of cyber safety concerns in retail sector. The purpose of this template is to aid businesses in assessing potential consequences for protecting against threats with highest impact in timely manner. It includes elements such as payment data breach, supply chain disruption, etc. Introducing our Impact Analysis Of Cybersecurity Threats In Retail Industry set of slides. The topics discussed in these slides are Payment Data Breach, Supply Chain, Customer Data Compromise This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Potential Insider Threats In Retail Cybersecurity
Potential Insider Threats In Retail CybersecurityThis slide highlights insider cyber security vulnerabilities in retail sector. The purpose of this template is to aid businesses in identifying and managing risks for preserving the integrity of retail systems. It includes elements such as vendors, employees, collaborators, etc. Presenting our set of slides with Potential Insider Threats In Retail Cybersecurity This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vendors, Collaborators, Non Responders
-
 Threats To Cybersecurity Infrastructure In Education
Threats To Cybersecurity Infrastructure In EducationThis slide depicts the threats to cybersecurity infrastructure in education. The purpose of this slide is to help the business ensure the organization is able to prevent attacks such insider threats, phishing, ransomware, etc. Presenting our set of slides with Threats To Cybersecurity Infrastructure In Education. This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Insider Threats, Malware, Phishing, Ransomware
-
 Hacking Threats In IT Industry With Mitigation Strategies
Hacking Threats In IT Industry With Mitigation StrategiesThis slide showcases potential hacking incidents in IT sector with mitigation strategies. The purpose of this slide is to help software businesses in strengthening their network security by securing digital assets. It covers mitigation strategies to overcome various hacking threats such as insider threats, phishing attacks, viruses, botnets, etc. Introducing our premium set of slides with Hacking Threats In IT Industry With Mitigation Strategies Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Insider Threats, Monitor Account Activity, Network Traffic Monitoring. So download instantly and tailor it with your information.
-
 Strategies To Prevent System Hacking Threats
Strategies To Prevent System Hacking ThreatsThis slide highlights approaches to ensure protection against potential hacking threats. The purpose of this slide is to help businesses in defending internet connected devices from malevolent attacks, identity theft, data breaches and financial losses by cybercriminals. It covers strategies such as software update, strong password policy and HTTP encryption. Presenting our well structured Strategies To Prevent System Hacking Threats The topics discussed in this slide are Alphanumeric Passwords, Ensuring Unique Passwords, Updating Operating. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Approaches For Aquatic Biological Diversity Threats
Approaches For Aquatic Biological Diversity ThreatsThis slide showcases the major techniques to protect aquatic biodiversity from threats. It include details such as exotic species extinction,water pollution,etc. Introducing our Approaches For Aquatic Biological Diversity Threats set of slides. The topics discussed in these slides are Protects Water Diversity,Increases Public Awareness,Enhances Regional Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Primary Types Of Mobile Security Threats
Primary Types Of Mobile Security ThreatsThis slide discusses the various types of mobile security threats which include phishing, malware and ransomware, crypto jacking and outdated operating system. Introducing our premium set of slides with name Primary Types Of Mobile Security Threats. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Phishing, Malware And Ransomware, Outdated Operating Systems, Crypto Jacking. So download instantly and tailor it with your information.
-
 Techniques To Counter Mobile Security Threats
Techniques To Counter Mobile Security ThreatsThis slide highlights the techniques to counter mobile security threats which include remote wipe for lost devices, segment storage to prevent malware, etc. Presenting our set of slides with name Techniques To Counter Mobile Security Threats. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implement Network Security, Techniques To Counter, Mobile Security Threats.
-
 SWOT Analysis Threats KPMG Company Profile Ppt Topics CP SS
SWOT Analysis Threats KPMG Company Profile Ppt Topics CP SSThis slide focuses on Threats to evaluate competitive position of company. It assists business to determine internal and external factors affecting growth and development. Introducing SWOT Analysis Threats KPMG Company Profile Ppt Topics CP SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Intense Competition, Economic Downturn, Legal And Regulatory Risks, using this template. Grab it now to reap its full benefits.
-
 Our Threats Vestas Company Profile CP SS
Our Threats Vestas Company Profile CP SSThe following slide showcases the threats to Vestas company and showcases external factors that can be a hurdle in business growth and development. It showcases elements such as competition, government policies and regulatory changes. Introducing Our Threats Vestas Company Profile CP SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Competition, Government Policies, Economic Downturn using this template. Grab it now to reap its full benefits.
-
 Implementing Effective Tokenization Existing IT Security Infrastructure Threats
Implementing Effective Tokenization Existing IT Security Infrastructure ThreatsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. Present the topic in a bit more detail with this Implementing Effective Tokenization Existing IT Security Infrastructure Threats. Use it as a tool for discussion and navigation on Compliance Challenges, Resource Intensiveness, Faced Security Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Emergency Preparedness Steps For Cyber Threat Mitigation
Emergency Preparedness Steps For Cyber Threat MitigationThis slide represents steps for emergency preparedness for cyber risk mitigation including steps such as identifying critical data, assess risks, developing team, etc. Introducing our premium set of slides with Emergency Preparedness Steps For Cyber Threat Mitigation. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Assess Risks, Create Procedures, Develop Team. So download instantly and tailor it with your information.
-
 SWOT Analysis Threats Online Retailer Company Profile CP SS V
SWOT Analysis Threats Online Retailer Company Profile CP SS VThis slide showcase SWOT Strengths, Weaknesses, Opportunities and Threats analysis of ecommerce giant that helps in converting company weakness into strengths and threats into opportunities Introducing SWOT Analysis Threats Online Retailer Company Profile CP SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strengths, Weaknesses, Opportunities using this template. Grab it now to reap its full benefits.
-
 Our Threats Music And Entertainment Company Profile CP SS V
Our Threats Music And Entertainment Company Profile CP SS VThe following slide showcases the threats to Spotify company and showcases external factors that can be a hurdle in business growth and development. It showcases elements such as data privacy regulations, technology disruptions and piracy. Increase audience engagement and knowledge by dispensing information using Our Threats Music And Entertainment Company Profile CP SS V. This template helps you present information on three stages. You can also present information on Data Privacy Regulations, Technology Disruptions, Piracy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Comparison Of Cybersecurity Apps For Threat Detection
Comparison Of Cybersecurity Apps For Threat DetectionThis slide represents comparison table for cybersecurity applications for online risk mitigation including Wireshark, Metasploit, and Entersoft apps. Introducing our premium set of slides with Comparison Of Cybersecurity Apps For Threat Detection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network Protocol Analysis, Security Assessment, Infrastructure Security Analysis. So download instantly and tailor it with your information.
-
 Top Web Application Security Threats Ppt File Example Topics
Top Web Application Security Threats Ppt File Example TopicsThis slide discusses the vulnerabilities and security threats in web application such as SQL injection, cross-site scripting, etc. Deliver an outstanding presentation on the topic using this Top Web Application Security Threats Ppt File Example Topics. Dispense information and present a thorough explanation of Cross Site Request Forgery, Insecure Direct Object References, Web Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Gathering And Analyzing Threat Intelligence Opportunities And Risks Of ChatGPT AI SS V
Gathering And Analyzing Threat Intelligence Opportunities And Risks Of ChatGPT AI SS VThis slide showcases various data sources that are leveraged by ChatGPT for threat intelligence to tack cyber attack on organization. Various data sources for threat intelligence are security blogs, social media and security forums. Introducing Gathering And Analyzing Threat Intelligence Opportunities And Risks Of ChatGPT AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security Blogs, Security Forums, Security Media, using this template. Grab it now to reap its full benefits.
-
 Overview And Importance Of Threat Intelligence Opportunities And Risks Of ChatGPT AI SS V
Overview And Importance Of Threat Intelligence Opportunities And Risks Of ChatGPT AI SS VThis slide showcases threat intelligence overview which can help organization to tackle the cyber attack. It also highlights key importance of threat intelligence that are tackle ongoing attacks, make informed decisions, formulate threat mitigation strategies etc. Present the topic in a bit more detail with this Overview And Importance Of Threat Intelligence Opportunities And Risks Of ChatGPT AI SS V. Use it as a tool for discussion and navigation on Security Operation Center, Security Analyst, Computer Security Incident Response Team. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Potential Threats Impacting Information Security
Potential Threats Impacting Information SecurityThis slide highlights possible vulnerabilities to data security. The purpose of this template is to help businesses in overcoming various challenges in protecting data for creating a safer environment. It includes elements such as malware, phishing, data breaches, etc. Introducing our Potential Threats Impacting Information Security set of slides. The topics discussed in these slides are General Data Protection, Health Insurance Portability, Security Management Act FISMA. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Best Practices For Integrating Threat Intelligence With Cybersecurity
Best Practices For Integrating Threat Intelligence With CybersecurityThis slide depicts the best practices for integrating cyber threat intelligence with cybersecurity. The purpose of this slide is to help the business successfully integrate threat intelligence with cybersecurity. It includes automation of data processing,, establishment of threat intelligence sharing policies, etc. Presenting our set of slides with Best Practices For Integrating Threat Intelligence With Cybersecurity This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ensure Integration, Current System, Automate Data Processing
-
 Challenges Faced During Business Cyber Threat Intelligence
Challenges Faced During Business Cyber Threat IntelligenceThis slide showcases the challenges faced during business cyber threat intelligence. The purpose of this slide is to help the business overcome these challenges through the use of provided solutions. It includes challenges such as improper management of information, streamlined integration, etc. Introducing our premium set of slides with Challenges Faced During Business Cyber Threat Intelligence Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Description, Challenges, Solutions So download instantly and tailor it with your information.
-
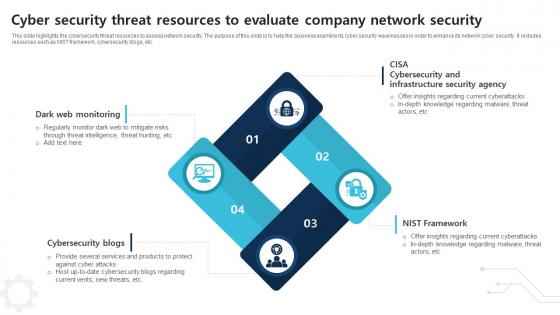 Cyber Security Threat Resources To Evaluate Company Network Security
Cyber Security Threat Resources To Evaluate Company Network SecurityThis slide highlights the cybersecurity threat resources to assess network security. The purpose of this slide is to help the business examine its cyber security weaknesses in order to enhance its network cyber security. It includes resources such as NIST framework, cybersecurity blogs, etc. Introducing our premium set of slides with Cyber Security Threat Resources To Evaluate Company Network Security Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Dark Web Monitoring, Cybersecurity Blogs, Nist Framework So download instantly and tailor it with your information.
-
 Cyber Threat Intelligence Framework To Safeguard Business Networks
Cyber Threat Intelligence Framework To Safeguard Business NetworksThis slide depicts the cyber threat intelligence framework utilized to safeguard business networks. The purpose of this slide is to help the business properly integrate cyber threat intelligence. It includes elements such as strategic CTI, tactical CTI, etc. Presenting our set of slides with Cyber Threat Intelligence Framework To Safeguard Business Networks This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Operational CTI, Strategic CTI
-
 Cyber Threat Intelligence Icon To Detect Digital Attacks
Cyber Threat Intelligence Icon To Detect Digital AttacksIntroducing our premium set of slides with Cyber Threat Intelligence Icon To Detect Digital Attacks Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Intelligence Icon, Detect Digital Attacks So download instantly and tailor it with your information.
-
 Cyber Threat Intelligence Icon To Enhance Cybersecurity
Cyber Threat Intelligence Icon To Enhance CybersecurityPresenting our set of slides with Cyber Threat Intelligence Icon To Enhance Cybersecurity This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Threat Intelligence Icon, Enhance Cybersecurity
-
 Cyber Threat Intelligence Vendor Comparative Analysis
Cyber Threat Intelligence Vendor Comparative AnalysisThis slide showcases the cyber threat intelligence vendor comparative analysis. The purpose of this slide is to help the business make an informed purchase decision regarding vendor services. It includes comparison on the basis of description, pricing and ratings Introducing our Cyber Threat Intelligence Vendor Comparative Analysis set of slides. The topics discussed in these slides are Vendor, Description, Pricing This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Sources For Cyber Threat Intelligence During Cybersecurity
Sources For Cyber Threat Intelligence During CybersecurityThis slide showcases the sources for cyber threat intelligence during cyber security. The purpose of this slide is to establish rigid security through the use of cyber threat intelligence. It includes open source intelligence, internal intelligence, etc. Presenting our well structured Sources For Cyber Threat Intelligence During Cybersecurity The topics discussed in this slide are CTI Information Source, Description, Examples This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Steps For Cyber Threat Intelligence Lifecycles
Steps For Cyber Threat Intelligence LifecyclesThis slide depicts the steps for cyber threat intelligence lifecycles. The purpose of this slide is to help the business successfully implement cyber threat intelligence practices. It includes steps such as requirements, collection, processing, etc. Introducing our premium set of slides with Steps For Cyber Threat Intelligence Lifecycles Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Requirements, Collection, Processing So download instantly and tailor it with your information.





