Powerpoint Templates and Google slides for System.
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
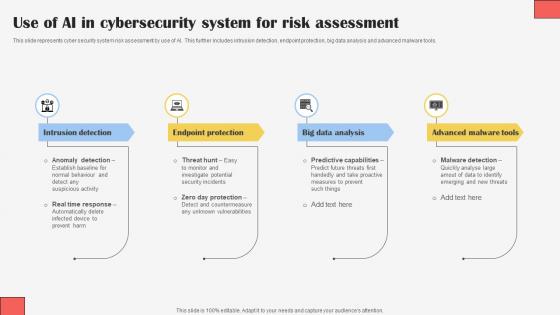 Use Of AI In Cybersecurity System For Risk Assessment
Use Of AI In Cybersecurity System For Risk AssessmentThis slide represents cyber security system risk assessment by use of AI. This further includes intrusion detection, endpoint protection, big data analysis and advanced malware tools. Presenting our set of slides with Use Of AI In Cybersecurity System For Risk Assessment. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Intrusion Detection, Endpoint Protection, Big Data Analysis.
-
 Hr Roles And Responsibilities Migrated To Robotic Process Automation System
Hr Roles And Responsibilities Migrated To Robotic Process Automation SystemThe slide showcases roles and responsibilities of HR managers that are migrated to RPA systems to increase efficiency in organization. It contains roles such as planning and organizing production schedules, coordinating and supervising employee work, keeping track of KPIs along with RPA work. Presenting our well structured Hr Roles And Responsibilities Migrated To Robotic Process Automation System. The topics discussed in this slide are Automates Schedules, Optimizing Production.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 RPA Deployment Phases In Healthcare Management Systems
RPA Deployment Phases In Healthcare Management SystemsThe slide showcases RPA deployment phases that assist in faster claim processing in healthcare management systems. It contains points such as preparation of project, analyzation, designing, implementation, etc. Presenting our set of slides with RPA Deployment Phases In Healthcare Management Systems. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Preparation Of Project, Analyzation.
-
 Cost Home Solar Power System In Powerpoint And Google Slides Cpb
Cost Home Solar Power System In Powerpoint And Google Slides CpbPresenting our Cost Home Solar Power System In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases two stages. It is useful to share insightful information on Cost Home Solar Power System This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Capital Market Model In Islamic Financial System Structure Of Islamic Financial System Fin SS
Capital Market Model In Islamic Financial System Structure Of Islamic Financial System Fin SSThis slide covers the details related to the Islamic capital market structure, where investment activities do not contradict the principles of Shariah. It includes the details related to the Islamic capital market, which is free of Riba unnecessarily high interest, Gharar deception, and Maysir gambling. Present the topic in a bit more detail with this Capital Market Model In Islamic Financial System Structure Of Islamic Financial System Fin SS. Use it as a tool for discussion and navigation on Profit Distribution, Fund Contribution, Purchase Undertaking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Different Financial Contracts Based On Islamic Law Structure Of Islamic Financial System Fin SS
Different Financial Contracts Based On Islamic Law Structure Of Islamic Financial System Fin SSThis slide depicts the flowchart representing different financial contracts based on Islamic law. It consists of details related to debt-like contracts, risk sharing contracts, and leasing contracts. Deliver an outstanding presentation on the topic using this Different Financial Contracts Based On Islamic Law Structure Of Islamic Financial System Fin SS. Dispense information and present a thorough explanation of Islamic Contracts, Leasing Contracts, Manufacturing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Different Types Of Murabaha Contracts In Islamic Finance Structure Of Islamic Financial System Fin SS
Different Types Of Murabaha Contracts In Islamic Finance Structure Of Islamic Financial System Fin SSThis slide covers the details related to the Murabaha a type of Islamic financing transaction that is widely used in the Islamic finance industry. It includes details related to the different types of Murabaha specified in the Islamic standard statement. Present the topic in a bit more detail with this Different Types Of Murabaha Contracts In Islamic Finance Structure Of Islamic Financial System Fin SS. Use it as a tool for discussion and navigation on Acquisition, Ownership, Transaction. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Islamic Exchange Traded Fund Structure Structure Of Islamic Financial System Fin SS
Islamic Exchange Traded Fund Structure Structure Of Islamic Financial System Fin SSThis slide depicts the structure of an Islamic exchange-traded fund ETF. It consists of details related to the manager, trustee, committee, participating dealers, liquidity providers, etc. Deliver an outstanding presentation on the topic using this Islamic Exchange Traded Fund Structure Structure Of Islamic Financial System Fin SS. Dispense information and present a thorough explanation of Structure, Liquidity Providers, Investors using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Islamic Financing Structure For Murabaha Contract Structure Of Islamic Financial System Fin SS
Islamic Financing Structure For Murabaha Contract Structure Of Islamic Financial System Fin SSThis slide covers the details related to the Murabaha, a type of Islamic financing transaction that is widely used in the Islamic finance industry. It includes details related to the structure used in cost plus financing. Introducing Islamic Financing Structure For Murabaha Contract Structure Of Islamic Financial System Fin SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Financing, Structure, Deferred Consideration For Asset, using this template. Grab it now to reap its full benefits.
-
 Islamic Money Market Structure For Financial Institutions Structure Of Islamic Financial System Fin SS
Islamic Money Market Structure For Financial Institutions Structure Of Islamic Financial System Fin SSThis slide covers the details related to the Islamic money market structure, which provides a platform for large corporations and financial institutions to access short-term financing from large institutions. It includes details related to the money market and its instruments. Deliver an outstanding presentation on the topic using this Islamic Money Market Structure For Financial Institutions Structure Of Islamic Financial System Fin SS. Dispense information and present a thorough explanation of Islamic Banking, Conventional Banking, Conventional Money using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Islamic Structure Islamic Derivatives Structure Of Islamic Financial System Fin SS
Islamic Structure Islamic Derivatives Structure Of Islamic Financial System Fin SSThis slide covers the details related to the Islamic derivatives also known as Shariah-compliant derivatives or simply as Islamics. It includes details related to a financial instrument that have been designed to comply with Islamic law or Shariah. Present the topic in a bit more detail with this Islamic Structure Islamic Derivatives Structure Of Islamic Financial System Fin SS. Use it as a tool for discussion and navigation on Financing Structure, Islamic Derivatives, Instrument. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Structure For Islamic Derivatives Structure Of Islamic Financial System Fin SS
Structure For Islamic Derivatives Structure Of Islamic Financial System Fin SSThis slide defines the steps taken under the Islamic derivatives structure in which Company exchanges its floating rate exposure under the underlying Shariah-compliant facility for fixed-rate exposure. Deliver an outstanding presentation on the topic using this Structure For Islamic Derivatives Structure Of Islamic Financial System Fin SS. Dispense information and present a thorough explanation of Islamic Derivatives, Structure, Counterparty using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Structure Of Ijara Lease In Islamic Finance Structure Of Islamic Financial System Fin SS
Structure Of Ijara Lease In Islamic Finance Structure Of Islamic Financial System Fin SSThis slide covers the details related to the Ijara lease, a contract where one party transfers the right to use an item he owns to another party for a specified period in exchange for an agreed consideration. It includes details related to the financing workflow based on Islamic law. Present the topic in a bit more detail with this Structure Of Ijara Lease In Islamic Finance Structure Of Islamic Financial System Fin SS. Use it as a tool for discussion and navigation on Structure, Liabilities, Agreement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Structure Of Islamic Financial Contract Of Mudarabah Structure Of Islamic Financial System Fin SS
Structure Of Islamic Financial Contract Of Mudarabah Structure Of Islamic Financial System Fin SSThis slide defines the Mudarabah or Mudarabah contract as a profit-and-loss sharing contract where one party, the rab al-mal the capital provider, provides funds to another party, the mudarib the manager, who invests the funds in a business venture. Deliver an outstanding presentation on the topic using this Structure Of Islamic Financial Contract Of Mudarabah Structure Of Islamic Financial System Fin SS. Dispense information and present a thorough explanation of Structure, Mudarabah, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Structure Of Istisna And Ijara Contracts In Islamic Finance Structure Of Islamic Financial System Fin SS
Structure Of Istisna And Ijara Contracts In Islamic Finance Structure Of Islamic Financial System Fin SSThis slide covers the details related to the Istisna a sales contract whereby a manufacturer agrees to deliver a made-to-order asset at a pre-determined future time at an agreed price. It includes details related to the financing structure based on Islamic law. Present the topic in a bit more detail with this Structure Of Istisna And Ijara Contracts In Islamic Finance Structure Of Islamic Financial System Fin SS. Use it as a tool for discussion and navigation on Structure, Financier, Manufacturer. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Structure Of Sukuk In Islamic Finance Structure Of Islamic Financial System Fin SS
Structure Of Sukuk In Islamic Finance Structure Of Islamic Financial System Fin SSThis slide covers the details related to the flowchart representing sukuk, a Shariah-compliant bond-like instrument used in Islamic finance. It includes details related to the Islamic financial certificate that represents a portion of ownership in a portfolio of eligible existing or future assets. Deliver an outstanding presentation on the topic using this Structure Of Sukuk In Islamic Finance Structure Of Islamic Financial System Fin SS. Dispense information and present a thorough explanation of Structure, Islamic Finance, Ownership using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Structure Of Takaful Mudarabah Model Structure Of Islamic Financial System Fin SS
Structure Of Takaful Mudarabah Model Structure Of Islamic Financial System Fin SSThis slide covers the details related to the structure of insurance followed based on Islamic guidelines. It also includes attributes associated with Takaful, a type of Islamic insurance wherein members contribute money into a pool system to guarantee each other. Present the topic in a bit more detail with this Structure Of Takaful Mudarabah Model Structure Of Islamic Financial System Fin SS. Use it as a tool for discussion and navigation on Structure, Management Expenses, Administration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Structure Of Takaful Wakala Waqf Model Structure Of Islamic Financial System Fin SS
Structure Of Takaful Wakala Waqf Model Structure Of Islamic Financial System Fin SSThis slide covers the details related to the structure of insurance followed based on Islamic guidelines. It also includes attributes associated with Takaful, a type of Islamic insurance wherein members contribute money into a pool system to guarantee each other. Deliver an outstanding presentation on the topic using this Structure Of Takaful Wakala Waqf Model Structure Of Islamic Financial System Fin SS. Dispense information and present a thorough explanation of Investment Income, Management, Shareholders using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Structure Of Wakala Model Structure Of Islamic Financial System Fin SS
Structure Of Wakala Model Structure Of Islamic Financial System Fin SSThis slide covers the details related to the structure of insurance followed based on Islamic guidelines. It also includes attributes associated with Takaful, a type of Islamic insurance wherein members contribute money into a pool system to guarantee each other. Present the topic in a bit more detail with this Structure Of Wakala Model Structure Of Islamic Financial System Fin SS. Use it as a tool for discussion and navigation on Structure, Management, Shareholders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents Structure Of Islamic Financial System Fin SS
Table Of Contents Structure Of Islamic Financial System Fin SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents Structure Of Islamic Financial System Fin SS. This template helps you present information on twelve stages. You can also present information on Structure, Structure Of Takaful Model, Financial Contract Of Mudarabah using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ack Tee 2 0 Architecture And Workflow Confidential Computing System Technology
Ack Tee 2 0 Architecture And Workflow Confidential Computing System TechnologyThis slide outlines the architecture of Container Service for Kubernetes trusted execution environment version 2. The purpose of this slide is to demonstrate the features, date of launch and target users. It also covers the architecture and working of ACK TEE 2.0. Present the topic in a bit more detail with this Ack Tee 2 0 Architecture And Workflow Confidential Computing System Technology. Use it as a tool for discussion and navigation on Architecture, Workflow, Confidential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ack Tee Introduction And Version 1 0 Confidential Computing System Technology
Ack Tee Introduction And Version 1 0 Confidential Computing System TechnologyThis slide talks about the introduction of Container Service for Kubernetes trusted execution environment and its version 1.0. The purpose of this slide is to showcase its features, data of launch, objective and target users. It also includes the architecture and workflow of ACK TEE and its working. Deliver an outstanding presentation on the topic using this Ack Tee Introduction And Version 1 0 Confidential Computing System Technology. Dispense information and present a thorough explanation of Introduction, Maintenance, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Agenda For Confidential Computing System Technology
Agenda For Confidential Computing System TechnologyIntroducing Agenda For Confidential Computing System Technology to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Applications, Environment, using this template. Grab it now to reap its full benefits.
-
 Budget For Implementing Architecture Confidential Computing System Technology
Budget For Implementing Architecture Confidential Computing System TechnologyThis slide describes the implementation cost of confidential computing, including required tools, hardware and software costs, and other expenditures. The purpose of this slide is to showcase the estimated cost, actual cost and variance. Deliver an outstanding presentation on the topic using this Budget For Implementing Architecture Confidential Computing System Technology. Dispense information and present a thorough explanation of Implementing, Confidential, Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Case Study Irene Energy Confidential Computing System Technology
Case Study Irene Energy Confidential Computing System TechnologyThis slide talks about the case study carried out at Irene Energy organization. The purpose of this slide is to demonstrate how this corporation uses confidential computing technologies to provide electricity to remote American areas. The case study includes issues experienced, objectives, provided solutions and impact. Present the topic in a bit more detail with this Case Study Irene Energy Confidential Computing System Technology. Use it as a tool for discussion and navigation on Manufacturers, Distributors, Solutions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Checklist To Implement Architecture Confidential Computing System Technology
Checklist To Implement Architecture Confidential Computing System TechnologyThis slide depicts the checklist to implement confidential computing architecture in a cloud environment. The purpose of this slide is to showcase the various steps to be taken to deploy confidential computing, including its status and the responsible person. Deliver an outstanding presentation on the topic using this Checklist To Implement Architecture Confidential Computing System Technology. Dispense information and present a thorough explanation of Confidential, Computing, Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Client Signature And Server Signature In Inclavare Confidential Computing System Technology
Client Signature And Server Signature In Inclavare Confidential Computing System TechnologyThis slide represents the client and server signature used in inclavare containers to protect sensitive applications and data. The purpose of this slide is to demonstrate the comparison between the client signature and the server signature and the benefits of the server signature. Present the topic in a bit more detail with this Client Signature And Server Signature In Inclavare Confidential Computing System Technology. Use it as a tool for discussion and navigation on Technology, Business, Certifications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Companies Paving The Path For Confidential Computing System Technology
Companies Paving The Path For Confidential Computing System TechnologyThis slide represents the top companies leading the way for confidential computing. The purpose of this slide is to showcase the leading companies adopting confidential computing to protect organizational and customer information in cloud environments. Top companies include IBM, Google, Microsoft, etc. Introducing Companies Paving The Path For Confidential Computing System Technology to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Containerized, Services, Execution, using this template. Grab it now to reap its full benefits.
-
 Confidential Applications In Different Sectors Confidential Computing System Technology
Confidential Applications In Different Sectors Confidential Computing System TechnologyThis slide represents the applications of confidential computing in different sectors. This slide aims to demonstrate the confidential computing applications in healthcare and research, finance, engineering and manufacturing, and automobile sectors. Deliver an outstanding presentation on the topic using this Confidential Applications In Different Sectors Confidential Computing System Technology. Dispense information and present a thorough explanation of Businesses, Information, Confidentiality using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Architecture And Realms Working Confidential Computing System Technology
Confidential Architecture And Realms Working Confidential Computing System TechnologyThis slide outlines the architecture of confidential computing and the working of realms. The purpose of this slide is to demonstrate the confidential computing architecture, including its components such as realm, applications, operating system, realm manager, hypervisor, and so on. Present the topic in a bit more detail with this Confidential Architecture And Realms Working Confidential Computing System Technology. Use it as a tool for discussion and navigation on Confidential, Computing, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing Architecture Implementation Confidential Computing System Technology
Confidential Computing Architecture Implementation Confidential Computing System TechnologyThis slide outlines the implementation timeline for confidential computing architecture. The purpose of this slide is to demonstrate the various steps to be taken to deploy confidential computing in a cloud environment, such as executing an existing Redis database unprotected, running within a confidential cloud, etc. Introducing Confidential Computing Architecture Implementation Confidential Computing System Technology to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Architecture, Implementation, Timeline, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing Based On Azure Services Confidential Computing System Technology
Confidential Computing Based On Azure Services Confidential Computing System TechnologyThis slide represents the architecture of confidential computing based on Azure confidential computing services. The purpose of this slide is to showcase the problems with typical approaches and confidential computing solutions. It also includes the architecture components such as sensitive data, etc. Present the topic in a bit more detail with this Confidential Computing Based On Azure Services Confidential Computing System Technology. Use it as a tool for discussion and navigation on Architecture, Services, Solutions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing System Technology For Table Of Contents
Confidential Computing System Technology For Table Of ContentsIntroducing Confidential Computing System Technology For Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Approaches, Architecture, using this template. Grab it now to reap its full benefits.
-
 Confidential Consortium Membership Levels Confidential Computing System Technology
Confidential Consortium Membership Levels Confidential Computing System TechnologyThis slide represents the confidential computing consortium membership and participation levels. The purpose of this slide is to demonstrate the various partnership levels, annual fees, board seats, technical advisory committee seats, outreach committees, and notes. Deliver an outstanding presentation on the topic using this Confidential Consortium Membership Levels Confidential Computing System Technology. Dispense information and present a thorough explanation of Confidential, Computing, Consortium using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Consortium Overview And Benefits Confidential Computing System Technology
Confidential Consortium Overview And Benefits Confidential Computing System TechnologyThis slide represents the overview of the confidential computing consortium and its benefits. The purpose of this slide is to showcase the overview, objective and projects lead by the confidential computing consortium. It also includes the benefits for the members to participate in the confidential computing consortium. Present the topic in a bit more detail with this Confidential Consortium Overview And Benefits Confidential Computing System Technology. Use it as a tool for discussion and navigation on Confidential, Consortium, Overview. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Executive Summary Of Key Findings Confidential Computing System Technology
Confidential Executive Summary Of Key Findings Confidential Computing System TechnologyThis slide outlines the executive summary of key findings of confidential computing. The purpose of this slide is to showcase the key findings such as market expansion rate, hardware and software segments drive rate, industries that will dominate implementation, and so on. Present the topic in a bit more detail with this Confidential Executive Summary Of Key Findings Confidential Computing System Technology. Use it as a tool for discussion and navigation on Implementation, Considerations, Executives. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Implementation Roadmap Confidential Computing System Technology
Confidential Implementation Roadmap Confidential Computing System TechnologyThis slide represents the implementation roadmap for confidential computing architecture. The purpose of this slide is to demonstrate the various steps to be taken to deploy confidential computing in a cloud environment, such as executing an existing Redis database unprotected, running within a confidential cloud, etc. Increase audience engagement and knowledge by dispensing information using Confidential Implementation Roadmap Confidential Computing System Technology. This template helps you present information on five stages. You can also present information on Architecture, Implementation, Roadmap using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Critical Functions Of Confidential Computing Technology Confidential Computing System Technology
Critical Functions Of Confidential Computing Technology Confidential Computing System TechnologyThis slide represents the critical functions of confidential computing. The purpose of this slide is to show the various features of confidential computing, such as popular and holistic data security model, data confidentiality, data integrity and code integrity. Present the topic in a bit more detail with this Critical Functions Of Confidential Computing Technology Confidential Computing System Technology. Use it as a tool for discussion and navigation on Data Confidentially, Data Integrity, Code Integrity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Financial And Healthcare Industry Scenario Analysis Confidential Computing System Technology
Financial And Healthcare Industry Scenario Analysis Confidential Computing System TechnologyThis slide represents the comparative analysis of financial services and healthcare industries based on different scenarios. The purpose of this slide is to demonstrate the different scenarios of financial services and healthcare industries. The different scenarios include best case, median case and worst case scenario. Deliver an outstanding presentation on the topic using this Financial And Healthcare Industry Scenario Analysis Confidential Computing System Technology. Dispense information and present a thorough explanation of Financial, Services, Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Future Of Confidential Computing Technology Confidential Computing System Technology
Future Of Confidential Computing Technology Confidential Computing System TechnologyThis slide represents the future of confidential computing technology. The purpose of this slide is to demonstrate the state of confidential computing in the coming years. It also includes how it will protect sensitive data from malicious attacks in the cloud environment. Introducing Future Of Confidential Computing Technology Confidential Computing System Technology to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Confidential, Computing, Technology, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Confidential Computing System Technology
Icons Slide For Confidential Computing System TechnologyPresent the topic in a bit more detail with this Icons Slide For Confidential Computing System Technology. Use it as a tool for discussion and navigation on Icons. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 In And Threat Vectors For Confidential Computing Confidential Computing System Technology
In And Threat Vectors For Confidential Computing Confidential Computing System TechnologyThis slide represents the in-scope and out-of-scope threat for confidential computing. The purpose of this slide is to showcase the threats that confidential computing handles, such as software, protocol, cryptographic and physical attacks. It also caters to the out of scope threats such as sophisticated physical and upstream hardware supply-chain attacks. Increase audience engagement and knowledge by dispensing information using In And Threat Vectors For Confidential Computing Confidential Computing System Technology. This template helps you present information on seven stages. You can also present information on Software Attacks, Protocol Attacks, Cryptographic Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Features Of Confidential Computing Platform Confidential Computing System Technology
Key Features Of Confidential Computing Platform Confidential Computing System TechnologyThis slide depicts the key features of confidential computing platform, including confidential virtual machines, confidential space, confidential dataproc, and confidential Google Kubernetes Engine node. Introducing Key Features Of Confidential Computing Platform Confidential Computing System Technology to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Confidential Space, Confidential Dataproc, Confidential Gke Nodes, using this template. Grab it now to reap its full benefits.
-
 Multi Team And Cooperation In Inclavare Containers Confidential Computing System Technology
Multi Team And Cooperation In Inclavare Containers Confidential Computing System TechnologyThis slide outlines the architecture of multi-team construction and cooperation. The components of the architecture include occlum, graphene SGX, dragon well, customer enclave runtime, SGX-device-plugin, cloud Linux, shim-rune, and Kubernetes. Deliver an outstanding presentation on the topic using this Multi Team And Cooperation In Inclavare Containers Confidential Computing System Technology. Dispense information and present a thorough explanation of Construction, Cooperation, Containers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Multiparty Privacy Computation Architecture Design Confidential Computing System Technology
Multiparty Privacy Computation Architecture Design Confidential Computing System TechnologyThis slide represents the overview of the architecture design of multiparty computing used in confidential computing. This slide aims to demonstrate the different attributes, benefits and technology options available such as blockchain with Azure virtual machine, blockchain as a service, and so on. Present the topic in a bit more detail with this Multiparty Privacy Computation Architecture Design Confidential Computing System Technology. Use it as a tool for discussion and navigation on Computation, Architecture, Technologies . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Occlum System Architecture And Features Confidential Computing System Technology
Occlum System Architecture And Features Confidential Computing System TechnologyThis slide depicts the features and architecture of the Occlum system in confidential computing. The purpose of this slide is to showcase the features, architecture and process of the trusted and untrusted environment. The components include the build command, Occlum CLI tool, deployment environment, and so on. Present the topic in a bit more detail with this Occlum System Architecture And Features Confidential Computing System Technology. Use it as a tool for discussion and navigation on Trusted Environment, Untrusted Environment, Memory Security Guarantee. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overview Of Computing Consortium Structure Confidential Computing System Technology
Overview Of Computing Consortium Structure Confidential Computing System TechnologyThis slide describes the overview of confidential computing consortium structure. The purpose of this slide is to demonstrate the various levels of consortium structure, covering governing board, technical advisory council, outreach, legal, DEV community, and so on. Present the topic in a bit more detail with this Overview Of Computing Consortium Structure Confidential Computing System Technology. Use it as a tool for discussion and navigation on Computing, Consortium, Structure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Shim Rune Workflow In Inclavare Containers Confidential Computing System Technology
Shim Rune Workflow In Inclavare Containers Confidential Computing System TechnologyThis slide represents the shim-rune workflow and working. The purpose of this slide is to show the various functions perform by shim-rune components. The primary components of the shim-rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Present the topic in a bit more detail with this Shim Rune Workflow In Inclavare Containers Confidential Computing System Technology. Use it as a tool for discussion and navigation on Component, Workflow, Inclavare Containers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Technical Stack For Confidential Computing Solutions Confidential Computing System Technology
Technical Stack For Confidential Computing Solutions Confidential Computing System TechnologyThis slide depicts the technical stack while assessing confidential computing solutions. The stack divides these solutions into four levels, including application software vendors, infrastructure providers, hardware vendors, and cryptographic building blocks. Present the topic in a bit more detail with this Technical Stack For Confidential Computing Solutions Confidential Computing System Technology. Use it as a tool for discussion and navigation on Application Software Vendors, Infrastructure Providers, Hardware Vendors. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Technologies Used To Protect Data In Use Confidential Computing System Technology
Technologies Used To Protect Data In Use Confidential Computing System TechnologyThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Deliver an outstanding presentation on the topic using this Technologies Used To Protect Data In Use Confidential Computing System Technology. Dispense information and present a thorough explanation of Technologies, Security Comparison, Scalability Comparison using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 What Is Environment Tee In Confidential Computing Confidential Computing System Technology
What Is Environment Tee In Confidential Computing Confidential Computing System TechnologyThis slide outlines the overview of the trusted execution environment used in confidential computing to protect the in-use data. The purpose of this slide is to showcase the overview, and properties of TEE, such as confidentiality, data integrity and code integrity. It also includes the other offerings of TEE environments. Present the topic in a bit more detail with this What Is Environment Tee In Confidential Computing Confidential Computing System Technology. Use it as a tool for discussion and navigation on Confidentiality, Data Integrity, Code Integrity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Working Of Confidential Computing Technology Confidential Computing System Technology
Working Of Confidential Computing Technology Confidential Computing System TechnologyThis slide describes the working of confidential computing technology to protect businesses in-memory crucial data while performing computations. It also includes how this approach makes data invisible to the operating system, cloud providers, users and other compute stack assets. Present the topic in a bit more detail with this Working Of Confidential Computing Technology Confidential Computing System Technology. Use it as a tool for discussion and navigation on Confidential, Computing, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ecommerce Order Management System Compressive Plan For Moving Business Strategy SS V
Ecommerce Order Management System Compressive Plan For Moving Business Strategy SS VThe following slide presents a software comparison assessment of various order management system of ecommerce business based on integrations. It assess performance based on various integrations such as Shopify, Magento, WooCommerce, BigCommerce, Amazon, eBay, Etsy. Walmart, etc. Present the topic in a bit more detail with this Ecommerce Order Management System Compressive Plan For Moving Business Strategy SS V. Use it as a tool for discussion and navigation on Software, Integrations, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing System Technology Components Of Inclavare Containers Architecture
Confidential Computing System Technology Components Of Inclavare Containers ArchitectureThis slide outlines the primary components of inclavare containers architecture. The purpose of this slide is to demonstrate the different elements of inclavare containers and their working. The main components include Kubelet, shim-rune, language runtime, liberpal.so, containerd, rune, SGX libOS, and PAL-API. Increase audience engagement and knowledge by dispensing information using Confidential Computing System Technology Components Of Inclavare Containers Architecture. This template helps you present information on eight stages. You can also present information on Language Runtime, Containers Architecture, Components using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Confidential Computing System Technology Functional Comparison Of Different Tee Environments
Confidential Computing System Technology Functional Comparison Of Different Tee EnvironmentsThis slide talks about the functional comparison between different TEE environments available in the market. The purpose of this slide is to demonstrate the comparison and challenges with TEE environments. The main TEE environment provider includes Intel SGX, AMD SEV-ES, and IBM SE. Present the topic in a bit more detail with this Confidential Computing System Technology Functional Comparison Of Different Tee Environments. Use it as a tool for discussion and navigation on Environments, Functional, Comparison. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing System Technology Hi Tech And Manufacturing Industry Scenario Case Analysis
Confidential Computing System Technology Hi Tech And Manufacturing Industry Scenario Case AnalysisThis slide outlines the difference between hi-tech and manufacturing industries based on the best, median, and worst-case scenarios. The purpose of this slide is to showcase the hi-tech and manufacturing confidential computing market, and it also includes the change agent for best, and worst case. Deliver an outstanding presentation on the topic using this Confidential Computing System Technology Hi Tech And Manufacturing Industry Scenario Case Analysis. Dispense information and present a thorough explanation of Analysis, Manufacturing, Infrastructure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing System Technology Inclavare Confidential Containers Architecture In Tee
Confidential Computing System Technology Inclavare Confidential Containers Architecture In TeeThis slide represents the architecture of inclavare confidential containers in the TEE environment. The purpose of this slide is to showcase the various components and features of inclavare containers. The primary components include Kubelet, containerd, shim-rune, rune, PAL API, Pod and so on. Deliver an outstanding presentation on the topic using this Confidential Computing System Technology Inclavare Confidential Containers Architecture In Tee. Dispense information and present a thorough explanation of Collaboration, Technology, Compatibility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing System Technology Intel Sgx With A Smaller Trusted Computing Base Tcb
Confidential Computing System Technology Intel Sgx With A Smaller Trusted Computing Base TcbThis slide describes the deployment of applications in Intel SGX with smaller TCB. The purpose of this slide is to showcase the difference between standard deployment and deployment in TEE. The main components include the operating system, virtual machine monitor, applications and hardware. Present the topic in a bit more detail with this Confidential Computing System Technology Intel Sgx With A Smaller Trusted Computing Base Tcb. Use it as a tool for discussion and navigation on Deployment, Environment, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing System Technology Introduction To Confidential Computing Technology
Confidential Computing System Technology Introduction To Confidential Computing TechnologyThis slide represents the introduction to confidential computing, including its overview and objectives. Confidential computing is a cloud computing method to secure data while processing and gives business confidence to migrate their information and valuable assets to the cloud. Deliver an outstanding presentation on the topic using this Confidential Computing System Technology Introduction To Confidential Computing Technology. Dispense information and present a thorough explanation of Introduction, Confidential, Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing System Technology Need For Confidential Computing In Cloud Environment
Confidential Computing System Technology Need For Confidential Computing In Cloud EnvironmentThis slide depicts the need for confidential computing in a cloud environment and by showcasing the security concerns with early data processing system and confidential computing solutions to overcome those problems. Deliver an outstanding presentation on the topic using this Confidential Computing System Technology Need For Confidential Computing In Cloud Environment. Dispense information and present a thorough explanation of Confidential, Environment, Solutions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.





