Powerpoint Templates and Google slides for Security Threat
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Computer system security common methods used to threaten computer security
Computer system security common methods used to threaten computer securityThis slide depicts the standard methods used to threaten cyber security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Increase audience engagement and knowledge by dispensing information using Computer System Security Common Methods Used To Threaten Computer Security. This template helps you present information on five stages. You can also present information on Malware, Daniel Of Service, Man In The Middle, SQL Injection, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data security it types of threats in data security ppt slides graphic tips
Data security it types of threats in data security ppt slides graphic tipsThis slide depicts the main types of threats in data security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Increase audience engagement and knowledge by dispensing information using Data Security IT Types Of Threats In Data Security Ppt Slides Graphic Tips. This template helps you present information on three stages. You can also present information on Cyber Crime, Cyber Terrorism, Cyber Attack, Cause Disruption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Internal security threats ppt powerpoint presentation layouts elements cpb
Internal security threats ppt powerpoint presentation layouts elements cpbPresenting Internal Security Threats Ppt Powerpoint Presentation Layouts Elements Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Internal Security Threats. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Common methods used to threaten electronic information security
Common methods used to threaten electronic information securityIntroducing Common Methods Used To Threaten Electronic Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Daniel Service, Man Middle, SQL Injection, Phishing , using this template. Grab it now to reap its full benefits.
-
 Cyber security risk management various types of workplace violence and threats
Cyber security risk management various types of workplace violence and threatsThis slide provides details regarding various types of workplace violence threats created by people in terms of stalking, physical assault, harassment or intimidation, etc. Introducing Cyber Security Risk Management Various Types Of Workplace Violence And Threats to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Threats Or Threatening Behavior, Physical Assault, Property Damage, using this template. Grab it now to reap its full benefits.
-
 Building organizational security strategy plan how firm handle various insider threats at workplace
Building organizational security strategy plan how firm handle various insider threats at workplaceThis slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc. Introducing Building Organizational Security Strategy Plan How Firm Handle Various Insider Threats At Workplace to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Workplace, Information, Coordination, using this template. Grab it now to reap its full benefits.
-
 Security threat assessment ppt powerpoint presentation diagram ppt cpb
Security threat assessment ppt powerpoint presentation diagram ppt cpbPresenting Security Threat Assessment Ppt Powerpoint Presentation Diagram Ppt Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Threat Assessment. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Critical security threats ppt powerpoint presentation model mockup cpb
Critical security threats ppt powerpoint presentation model mockup cpbPresenting our Critical Security Threats Ppt Powerpoint Presentation Model Mockup Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Critical Security Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Addressing ways to handling managing critical threat vulnerabilities and security threats
Addressing ways to handling managing critical threat vulnerabilities and security threatsThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Introducing Addressing Ways To Handling Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cash Requirement, Financial Statements, Overheads Analysis, Currency Hedging, using this template. Grab it now to reap its full benefits.
-
 Impact analysis of successful managing critical threat vulnerabilities and security threats
Impact analysis of successful managing critical threat vulnerabilities and security threatsThis slide depicts the impact of successful implementation of threat management in terms improved incident management and customer satisfaction and depicts that how much the focus area has been improved from the previous state. Increase audience engagement and knowledge by dispensing information using Impact Analysis Of Successful Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Focus Area, Past State, Present State, Benefit using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Roles and responsibilities to managing critical threat vulnerabilities and security threats
Roles and responsibilities to managing critical threat vulnerabilities and security threatsThis slide provides details regarding roles and responsibilities assigned to ensure minimum violence work environment. Introducing Roles And Responsibilities To Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Employee Responsibilities, Manager Responsibilities, Unit Responsibilities, Human Resources Responsibilities, using this template. Grab it now to reap its full benefits.
-
 Various types of workplace violence managing critical threat vulnerabilities and security threats
Various types of workplace violence managing critical threat vulnerabilities and security threatsThis slide provides details regarding various types of workplace violence threats created by people in terms of stalking, physical assault, harassment or intimidation, etc. Increase audience engagement and knowledge by dispensing information using Various Types Of Workplace Violence Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on six stages. You can also present information on Threatening Behavior Stalking, Physical Assault, Harassment And Intimidation, Property Damage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing indicators associated to insider cyber threats corporate security management
Addressing indicators associated to insider cyber threats corporate security managementThis slide provides details regarding indicators associated to insider threats in terms of traits, demeanor and goals, etc. Increase audience engagement and knowledge by dispensing information using Addressing Indicators Associated To Insider Cyber Threats Corporate Security Management. This template helps you present information on three stages. You can also present information on Traits, Demeanor, Goals using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Corporate security management determine sequence phases for threat attack
Corporate security management determine sequence phases for threat attackThis slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Increase audience engagement and knowledge by dispensing information using Corporate Security Management Determine Sequence Phases For Threat Attack. This template helps you present information on four stages. You can also present information on Reconnaissance, Weaponization, Delivery, Exploitation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine sequence phases for threat attack actions corporate security management
Determine sequence phases for threat attack actions corporate security managementThis slide provides details regarding sequence phases for threat attack by threat actor in terms of installation, command and control, actions and objectives, covering tracks. Introducing Determine Sequence Phases For Threat Attack Actions Corporate Security Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Installation, Command And Control, Actions And Objectives, Covering Tracks, using this template. Grab it now to reap its full benefits.
-
 Cyber threat strategies for security protection
Cyber threat strategies for security protectionThis slide highlights the cyber threat strategies that include risk assessment, phishing program, software protocols and end point protection. Presenting our set of slides with Cyber Threat Strategies For Security Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Program, Software Protocols, End Point Protection.
-
 Network Security Common Methods Used To Threaten Network Security
Network Security Common Methods Used To Threaten Network SecurityThis slide depicts the standard methods used to threaten network security by cybercriminals attackers. It also shows the reasons for these threats and preventions from these threats. Increase audience engagement and knowledge by dispensing information using Network Security Common Methods Used To Threaten Network Security. This template helps you present information on five stages. You can also present information on Malicious, Necessary, Perform, Unavailable, Operations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Network Security Latest Threats In Network Security
Network Security Latest Threats In Network SecurityThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Introducing Network Security Latest Threats In Network Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Financial, Fraudulent, Information, Business, using this template. Grab it now to reap its full benefits.
-
 Network Security Types Of Threats In Network Security
Network Security Types Of Threats In Network SecurityThis slide depicts the main types of threats in network security, such as network crime, network terrorism, and cyberattacks to an organization and the purpose of each category threat. Increase audience engagement and knowledge by dispensing information using Network Security Types Of Threats In Network Security. This template helps you present information on three stages. You can also present information on Cyber Crime, Cyber Terrorism, Cyber Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Technology Security Common Methods Used Threaten Information Security
Information Technology Security Common Methods Used Threaten Information SecurityThis slide depicts the standard methods used to threaten cyber security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Introducing Information Technology Security Common Methods Used Threaten Information Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Daniel Of Service, Man In The Middle, SQL Injection , using this template. Grab it now to reap its full benefits.
-
 Small Business Cyber Security Threats Ppt Powerpoint Presentation Inspiration Themes Cpb
Small Business Cyber Security Threats Ppt Powerpoint Presentation Inspiration Themes CpbPresenting our Small Business Cyber Security Threats Ppt Powerpoint Presentation Inspiration Themes Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Small Business Cyber Security Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cloud Security Threats Shared Vulnerabilities Cloud Data Protection
Cloud Security Threats Shared Vulnerabilities Cloud Data ProtectionThis slide describes how organizations and providers share vulnerabilities of a system, so each party must take precautions to protect data. Introducing Cloud Security Threats Shared Vulnerabilities Cloud Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Secure Cloud Data, Organizations, Data Security, using this template. Grab it now to reap its full benefits.
-
 Various Cyber Security Threats And Strategies To Manage Network Service
Various Cyber Security Threats And Strategies To Manage Network ServiceThis slide highlights different types of cybersecurity threat such as malware, phishing, trojan horse and rootkit. The template also provides information about various strategies which will assist IT department to manage its network services. Introducing our premium set of slides with Various Cyber Security Threats And Strategies To Manage Network Service. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strategies Overcome Threats, IT Security Services, Provide Security Awareness. So download instantly and tailor it with your information.
-
 Cyber Security Threats In Powerpoint And Google Slides Cpb
Cyber Security Threats In Powerpoint And Google Slides CpbPresenting our Cyber Security Threats In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Cyber Security Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Mitigation Strategies To Tackle Information Security Threats Information Security Risk Management
Mitigation Strategies To Tackle Information Security Threats Information Security Risk ManagementThis slide showcases mitigation strategies that can help organization to tackle the cybersecurity attacks. It can help organization to minimize the financial loss and maintain reputation of business. Increase audience engagement and knowledge by dispensing information using Mitigation Strategies To Tackle Information Security Threats Information Security Risk Management. This template helps you present information on five stages. You can also present information on Mitigation Strategies, Tackle Information, Security Threats using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Network Security Threats In Powerpoint And Google Slides Cpb
Network Security Threats In Powerpoint And Google Slides CpbPresenting Network Security Threats In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Network Security Threats. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Web Security Threats Approaches In Powerpoint And Google Slides Cpb
Web Security Threats Approaches In Powerpoint And Google Slides CpbPresenting Web Security Threats Approaches In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Web Security Threats Approaches. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Threat Social Security In Powerpoint And Google Slides Cpb
Threat Social Security In Powerpoint And Google Slides CpbPresenting our Threat Social Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Threat Social Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Common Cryptocurrency Security Threats Exploring The Role BCT SS
Common Cryptocurrency Security Threats Exploring The Role BCT SSThis slide covers major crypto security risks faced by investors and companies. It includes threats such as phishing attacks, malware and keyloggers, hacks and data breaches, social engineering, fake wallets and apps, insider threats, and unsecure smart contracts. Introducing Common Cryptocurrency Security Threats Exploring The Role BCT SS to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Attacks, Malware And Keyloggers, Insider Threats, using this template. Grab it now to reap its full benefits.
-
 Measures To Prevent Cryptocurrency Security Threats Exploring The Role BCT SS
Measures To Prevent Cryptocurrency Security Threats Exploring The Role BCT SSThis slide covers various methods to avoid crypto security risks. It includes solutions such as phishing attacks prevention, malware and keyloggers protection, hacks and data breaches mitigation, social engineering defense, fake wallets and apps vigilance, etc. Introducing Measures To Prevent Cryptocurrency Security Threats Exploring The Role BCT SS to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Attacks Prevention, Breaches Mitigation, Social Engineering Defense, using this template. Grab it now to reap its full benefits.
-
 Internal Cyber Security Threats In Powerpoint And Google Slides Cpb
Internal Cyber Security Threats In Powerpoint And Google Slides CpbPresenting Internal Cyber Security Threats In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Internal Cyber Security Threats. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber Security Threat Malware In Powerpoint And Google Slides Cpb
Cyber Security Threat Malware In Powerpoint And Google Slides CpbPresenting our Cyber Security Threat Malware In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cyber Security Threat Malware This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cloud Access Security Broker CASB V2 Pillar Threat Protection Ppt Icon Introduction
Cloud Access Security Broker CASB V2 Pillar Threat Protection Ppt Icon IntroductionThis slide describes the threat protection pillar of cloud access security broker. The purpose of this slide is to highlight how CASB can help organizations to detect threats in advance through machine learning algorithms. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Pillar Threat Protection Ppt Icon Introduction. This template helps you present information on four stages. You can also present information on Threat Protection Pillar, Cloud Access Security Broker, Machine Learning Algorithms using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V
Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Introducing Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Block Users Network, Foster Attack, Breach Privacy, using this template. Grab it now to reap its full benefits.
-
 Chatgpt Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Chatgpt Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various ChatGPT use cases for streamlining and automating the cybersecurity operations of organization. Its key elements are establish security policies, automate repetitive tasks and identification of vulnerabilities Increase audience engagement and knowledge by dispensing information using Chatgpt Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on three stages. You can also present information on Streamlining, Operations, Identify Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
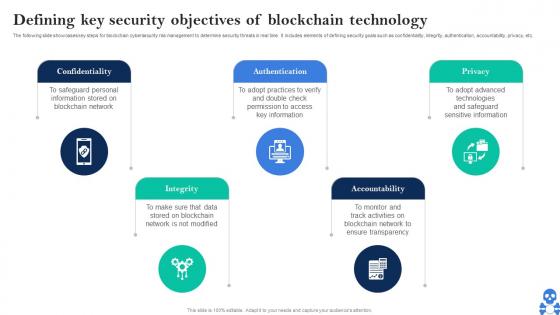 Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS V
Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS VThe following slide showcases key steps for blockchain cybersecurity risk management to determine security threats in real time. It includes elements of defining security goals such as confidentiality, integrity, authentication, accountability, privacy, etc. Introducing Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Integrity, Authentication using this template. Grab it now to reap its full benefits.
-
 Cyber Threats In Blockchain Methods To Ensure Smart Contract Security BCT SS V
Cyber Threats In Blockchain Methods To Ensure Smart Contract Security BCT SS VThe following slide showcases some tips and practices to ensure smart contract security. It includes elements such as careful rollouts, keeping them simple, updating and monitoring new developments, reviewing fundamental tradeoffs, etc. Introducing Cyber Threats In Blockchain Methods To Ensure Smart Contract Security BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Careful Rollouts, Contracts Simple, Monitor New Advancements using this template. Grab it now to reap its full benefits.
-
 Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V
Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS VThe following slide illustrates some methods to minimize the adverse impact of eclipse attack on blockchain network and facilitate security features. It includes elements such as random node selection, deterministic node selection, increased node connections, new node restrictions, etc. Introducing Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Mining Capability, Mining Capabilities, Much Faster Rate using this template. Grab it now to reap its full benefits.
-
 Different Security Threats To Be Managed By Web Strategic Guide For Web Design Company
Different Security Threats To Be Managed By Web Strategic Guide For Web Design CompanyMentioned slide provides insights into various security threats to be managed by web designers. It includes key components such as SQL injection, ransomware, spyware, phishing, cross site scription, and virus and bugs. Increase audience engagement and knowledge by dispensing information using Different Security Threats To Be Managed By Web Strategic Guide For Web Design Company. This template helps you present information on six stages. You can also present information on Injection, Scription, Developers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Understanding The Cyber Threats Prevented By Waf
Firewall Network Security Understanding The Cyber Threats Prevented By WafThis slide represents the many cyberattacks that a WAF is designed to stop. The purpose of this slide is to showcase the various cyber attacks that can avoided with the help of WAF, such as DDoS attacks, zero-day threats, cross-site scripting XSS, cookie poisoning, web scrapping, parameter tampering, and SQL injection. Introducing Firewall Network Security Understanding The Cyber Threats Prevented By Waf to increase your presentation threshold. Encompassed with Eight stages, this template is a great option to educate and entice your audience. Dispence information on Cookie Poisoning, Sql Injection, Parameter Tampering using this template. Grab it now to reap its full benefits.
-
 Firewall Network Security Unified Threat Management UTM Firewall System Overview
Firewall Network Security Unified Threat Management UTM Firewall System OverviewThis slide provides an introduction to the Unified Threat Management firewall system. The purpose of this slide is to showcase the features, benefits, and inspection methods of Unified Threat Management firewall systems, such as flow-based and proxy-based inspection. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Understanding Critical Risks Of Firewall Absence This template helps you present information on Three stages. You can also present information on Content Filtering, Faster Security, Flexibility And Adaptability using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Modern Threats Exploiting Firewall Vulnerabilities
Firewall Network Security Modern Threats Exploiting Firewall VulnerabilitiesThis slide represents the various modern risks that can take advantage of firewall weaknesses. The purpose of this slide is to showcase the different current threats that can exploit firewall vulnerabilities, including insider attacks, DDoS attacks, malware and patching and configuration. Introducing Firewall Network Security Modern Threats Exploiting Firewall Vulnerabilities to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Requested Data, NAT Firewall, Forwarding Table using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker Pillar Threat Protection Next Generation CASB
Cloud Access Security Broker Pillar Threat Protection Next Generation CASBThis slide describes the threat protection pillar of cloud access security broker. The purpose of this slide is to highlight how CASB can help organizations to detect threats in advance through machine learning algorithms. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Pillar Threat Protection Next Generation CASB This template helps you present information on five stages. You can also present information on Services, Cloud Storage, Compromised Accounts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Advanced Threat Security Solutions With Costing
Advanced Threat Security Solutions With CostingThe mentioned slide showcases different categories of advanced threat protection solutions along with their estimated cost. Introducing our premium set of slides with Advanced Threat Security Solutions With Costing. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Analytics, Security, Intelligence. So download instantly and tailor it with your information.
-
 IoT Cyber Security Technologies For Advanced Threat Protection
IoT Cyber Security Technologies For Advanced Threat ProtectionThe purpose of this slide is to showcase various types of Internet of Things IoT security technologies that assists in safeguarding cyber threats. Introducing our premium set of slides with IoT Cyber Security Technologies For Advanced Threat Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Architecture, Security, Computing. So download instantly and tailor it with your information.
-
 Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security Threats
Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti virus, preventing to open suspicious emails, keeping systems up to date etc. Introducing Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Leverage Firewalls, Prevent Opening Suspicious Emails using this template. Grab it now to reap its full benefits.
-
 Global Cyber Security Trend Analysis Implementing Strategies To Mitigate Cyber Security Threats
Global Cyber Security Trend Analysis Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the key statistics about cyber security trends to project future performance. It mainly includes elements such as increase in ransomware attacks, average data breach costs, approximate number of businesses prone to cyber attacks etc. Increase audience engagement and knowledge by dispensing information using Global Cyber Security Trend Analysis Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on six stages. You can also present information on Attack, Data Breaches, Cyber Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security Threats
Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates some practices to ensure strong password management and restrict access to data. It includes activities such as avoiding weak passwords, encryption, multi factor authentication, conducting test etc. Introducing Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Conduct Password Test, Password Encryption, Multi Factor Authentication using this template. Grab it now to reap its full benefits.
-
 Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security Threats
Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the various types of cyber attacks faced by staff to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service tec. Introducing Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Ransomware, Phishing using this template. Grab it now to reap its full benefits.
-
 Techniques To Counter Mobile Security Threats
Techniques To Counter Mobile Security ThreatsThis slide highlights the techniques to counter mobile security threats which include remote wipe for lost devices, segment storage to prevent malware, etc. Presenting our set of slides with name Techniques To Counter Mobile Security Threats. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implement Network Security, Techniques To Counter, Mobile Security Threats.
-
 Monitor Vulnerability Disclosure And Threat Intelligence Internet Of Things IoT Security Cybersecurity SS
Monitor Vulnerability Disclosure And Threat Intelligence Internet Of Things IoT Security Cybersecurity SSThis slide showcases vulnerability assessment disclosure and threat intelligence on internet of things IoT devices, referable for businesses in developing mitigation process. It provides details about continuous monitoring, correlation, disclosure, etc. Introducing Monitor Vulnerability Disclosure And Threat Intelligence Internet Of Things IoT Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Continuous Monitoring, Correlation With Metadata, Disclosure Implementation, using this template. Grab it now to reap its full benefits.
-
 Mobile Threats Faced By Different Departments Mobile Device Security Cybersecurity SS
Mobile Threats Faced By Different Departments Mobile Device Security Cybersecurity SSThis slide showcases mobile security threats faced in different departments. Its key components are department, number of mobile threats and type of attacks Increase audience engagement and knowledge by dispensing information using Mobile Threats Faced By Different Departments Mobile Device Security Cybersecurity SS This template helps you present information on Three stages. You can also present information on Compliance, Incident Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Types Of Threats Faced During Ecommerce Security
Types Of Threats Faced During Ecommerce SecurityThis slide shows the various types of threats which hindrance the ecommerce security such as credit cards frauds, bad bots, hacking of confidential of data, denial of services ,etc. Introducing our premium set of slides with Types Of Threats Faced During Ecommerce Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Denial Of Service,Customer Journey Hacking,Credit Cards Frauds. So download instantly and tailor it with your information.
-
 Application Based Mobile Security Threats Mobile Security
Application Based Mobile Security Threats Mobile SecurityThis slide represents the different types of application based mobile security threats which include malicious apps, fake or clone apps and app spoofing. Increase audience engagement and knowledge by dispensing information using Application Based Mobile Security Threats Mobile Security This template helps you present information on Five stages. You can also present information on Simplicity, Ubiquitousness, Cost Effective using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Various Common Threats In Web Security Solution
Various Common Threats In Web Security SolutionThis slide outlines the different hazards in web security which include ransomware, malware, phishing, SQL injection, and so on. Introducing Various Common Threats In Web Security Solution to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Malware, Phishing, Sql Injection, Denial Of Service, using this template. Grab it now to reap its full benefits.
-
 Threats Faced In Fintech Cyber Security
Threats Faced In Fintech Cyber SecurityThis slide showcases the threats faced in fintech cyber security. Its use is to face threats in fintech cyber security and help protect against zero day attacks. This slide includes spoofing, ransomware, organisation, malware, etc. Introducing our premium set of slides with name Threats Faced In Fintech Cyber Security. Ellicudate the nine stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like DDOS, Advanced Threats, Phishing, Sniffing, Malware. So download instantly and tailor it with your information.
-
 Best Practices For Minimizing Risks Of Insider Threats IT Security Awareness Training Cybersecurity SS
Best Practices For Minimizing Risks Of Insider Threats IT Security Awareness Training Cybersecurity SSThis slide represents best practices for mitigating threats that originate from within the targeted organization. It includes best practices such as perform enterprise-wide risk assessment etc. Increase audience engagement and knowledge by dispensing information using Best Practices For Minimizing Risks Of Insider Threats IT Security Awareness Training Cybersecurity SS. This template helps you present information on four stages. You can also present information on Enforce Policies And Controls, Establish Physical Security, Harden Network Perimeter Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Potential Security Threats To Ai Chatbots
Potential Security Threats To Ai ChatbotsThis slide shows extensive information regarding multiple types of security threats associated with artificial intelligence-powered chatbots. These chatbot threats are ransomware, malware, and phishing. It also includes potential impact of these threats. Introducing our premium set of slides with Potential Security Threats To Ai Chatbots. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ransomware, Malware, Phishing. So download instantly and tailor it with your information.
-
 Ai Powered Network Security Threats
Ai Powered Network Security ThreatsThis slide shows the various threats faced by companies after deploying artificial intelligence in cloud computing security networks. The major threats organizations face are advanced phishing attacks, deep fake attacks, credential stuffing Presenting our set of slides with Ai Powered Network Security Threats. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Advanced Phishing Attacks, Deepfake Attacks, Credential Stuffing .
-
 Protecting Sensitive Data From Network Security Threats
Protecting Sensitive Data From Network Security ThreatsThis slide highlights network security threats to protect from unauthorized access including trojan viruses, malware, and computer worms. Introducing our premium set of slides with name Protecting Sensitive Data From Network Security Threats. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Trojan Virus, Malware, Computer Worms. So download instantly and tailor it with your information.



