Powerpoint Templates and Google slides for Security Strategy
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Successful siem strategies audit compliance benchmarking security operations maturity
Successful siem strategies audit compliance benchmarking security operations maturityThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Increase audience engagement and knowledge by dispensing information using Successful Siem Strategies Audit Compliance Benchmarking Security Operations Maturity. This template helps you present information on three stages. You can also present information on Improve Visibility, Quickly Identify Threats, Decrease Response Time using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 F267 Strategies To Enhance Retail Store Security Retail Store Operations Performance Assessment
F267 Strategies To Enhance Retail Store Security Retail Store Operations Performance AssessmentThis slide provides information regarding the strategies to enhance retail store security such as integrate access control technology, deploy video surveillance, utilizes electronic article surveillance, install monitored alarms. Increase audience engagement and knowledge by dispensing information using F267 Strategies To Enhance Retail Store Security Retail Store Operations Performance Assessment. This template helps you present information on four stages. You can also present information on Technology, Surveillance, Strategies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Securing Our Data With CRM Customer Relationship Management Deployment Strategy
Securing Our Data With CRM Customer Relationship Management Deployment StrategyThis slide highlights the data security using CRM which incorporates IP restriction, two factor authentication, data storage, communication protection and data security.Increase audience engagement and knowledge by dispensing information using Securing Our Data With CRM Customer Relationship Management Deployment Strategy This template helps you present information on three stages. You can also present information on Factor Authentication, Storage And Failover, Communication Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Threat Mitigation Strategies
Cyber Security Threat Mitigation StrategiesThe following slide highlights the six strategies for cyber security threat mitigation illustrating risk assessment, access control, security solution, patch management, traffic monitoring and incident response. Presenting our set of slides with name Cyber Security Threat Mitigation Strategies. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Assessment, Patch Management, Traffic Monitoring.
-
 Ecommerce Security Strategy Framework To Prevent Fraudulent Transactions Icon
Ecommerce Security Strategy Framework To Prevent Fraudulent Transactions IconIntroducing our premium set of slides with Ecommerce Security Strategy Framework To Prevent Fraudulent Transactions Icon. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ecommerce, Security Strategy Framework, Prevent Fraudulent, Transactions Icon. So download instantly and tailor it with your information.
-
 IT Risk Management Strategies Security Criteria And Control Measures For IT System Vulnerabilities
IT Risk Management Strategies Security Criteria And Control Measures For IT System VulnerabilitiesThis slide highlights the security criteria for information technology system vulnerabilities with security area which includes management security, operational security and technical security. Introducing IT Risk Management Strategies Security Criteria And Control Measures For It System Vulnerabilities to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Security, Operational Security, Technical Security, using this template. Grab it now to reap its full benefits.
-
 Cloud Architecture And Security Review Strategies To Avoid Lock In With Multi Cloud
Cloud Architecture And Security Review Strategies To Avoid Lock In With Multi CloudThis slide covers the strategies to avoid lock ins with multi cloud such as using devops culture, keeping application managed, using opensource protocols, using opensource technologies and many more. Increase audience engagement and knowledge by dispensing information using Cloud Architecture And Security Review Strategies To Avoid Lock In With Multi Cloud. This template helps you present information on six stages. You can also present information on Ensuring Proprietary, Technology Is Ubiquitous, Isolate Proprietary Services, Infrastructure From Code using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Defense Strategy Maturity Evaluation
Cyber Security Defense Strategy Maturity EvaluationThis slide represents cyber security defense strategy maturity evaluation mode illustrating culture and organization, governance, visibility and controls, focused defense and intelligence operations. Introducing our premium set of slides with name Cyber Security Defense Strategy Maturity Evaluation. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Culture And Organization, Governance, Visibility And Controls. So download instantly and tailor it with your information.
-
 Cyber Security Strategy Icon Depicting Computer Protection
Cyber Security Strategy Icon Depicting Computer ProtectionIntroducing our premium set of slides with name Cyber Security Strategy Icon Depicting Computer Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security, Strategy Icon, Depicting Computer, Protection. So download instantly and tailor it with your information.
-
 Key Elements Of Cyber Security Strategy
Key Elements Of Cyber Security StrategyThis slide represents key elements of cyber security strategy such as cyber risk management, security regulatory and compliance, cyber transformation, cyber strategy etc. Introducing our premium set of slides with name Key Elements Of Cyber Security Strategy. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Risk Management, Cyber Transformation, Risk Maturity Assessment. So download instantly and tailor it with your information.
-
 Implementing Cyber Security Strategies To Analyze Cyber Security Incidents Ppt Elements
Implementing Cyber Security Strategies To Analyze Cyber Security Incidents Ppt ElementsThis slide represents the techniques to be used by the organizations to analyze the impact of cyber security incidents on business operations. It includes strategies for analyzing cyber incidents such as profile network and systems etc. Increase audience engagement and knowledge by dispensing information using Implementing Cyber Security Strategies To Analyze Cyber Security Incidents Ppt Elements. This template helps you present information on two stages. You can also present information on Profile Network And Systems, Understand Normal Behaviors, Perform Event Correlation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Parameters To Select Cyber Security Containment Strategy Ppt Elements
Key Parameters To Select Cyber Security Containment Strategy Ppt ElementsThis slide represents the various parameters to look for before choosing an effective and efficient cyber security containment strategy. It includes key parameters such as higher potential damages and theft of organizational resources etc. Increase audience engagement and knowledge by dispensing information using Key Parameters To Select Cyber Security Containment Strategy Ppt Elements. This template helps you present information on five stages. You can also present information on Organizational Resources, Cyber Security Incidents, Containment Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mitigation Strategies To Tackle Information Security Threats Formulating Cybersecurity Plan
Mitigation Strategies To Tackle Information Security Threats Formulating Cybersecurity PlanThis slide showcases mitigation strategies that can help organization to tackle the cybersecurity attacks. It can help organization to minimize the financial loss and maintain reputation of business. Increase audience engagement and knowledge by dispensing information using Mitigation Strategies To Tackle Information Security Threats Formulating Cybersecurity Plan. This template helps you present information on five stages. You can also present information on Malware, Phishing, Mitigation Strategies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mitigation Strategies To Avoid Information Breach Information System Security And Risk Administration Plan
Mitigation Strategies To Avoid Information Breach Information System Security And Risk Administration PlanThis slide showcases strategies that can help organization to avoid information breach. Key strategies include implement antivirus software, monitor network traffic, incident response plan, patch management schedule and establish network access controls. Increase audience engagement and knowledge by dispensing information using Mitigation Strategies To Avoid Information Breach Information System Security And Risk Administration Plan. This template helps you present information on five stages. You can also present information on Incident Response Plan, Monitor Network Traffic, Patch Management Schedule using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mitigation Strategies To Tackle Information Security Information System Security And Risk Administration Plan
Mitigation Strategies To Tackle Information Security Information System Security And Risk Administration PlanThis slide showcases mitigation strategies that can help organization to tackle the cybersecurity attacks. It can help organization to minimize the financial loss and main reputation of business. Introducing Mitigation Strategies To Tackle Information Security Information System Security And Risk Administration Plan to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Phishing, SQL Injection, using this template. Grab it now to reap its full benefits.
-
 Information Security Governance Strategic Model
Information Security Governance Strategic ModelThe following slide showcases a framework presenting strategy development and implementation phase in information security governance. It includes key components such as organizational structure, value delivery, strategic alignment, resource optimization, performance measurement, etc. Presenting our set of slides with Information Security Governance Strategic Model. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Organizational Structure, Strategic Alignment, Compliance.
-
 Security Strategic Planning Process For Cps Collective Intelligence Systems
Security Strategic Planning Process For Cps Collective Intelligence SystemsThis slide represents the security strategic planning process for CPS, including business strategy, technology roadmap, vision statement environment trends, current state assessment, and so on. Increase audience engagement and knowledge by dispensing information using Security Strategic Planning Process For Cps Collective Intelligence Systems. This template helps you present information on one stages. You can also present information on Business Strategy, Environmental Trends, Gap Analysis, Prioritization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategic Framework To Manage Cyber Security Risk
Strategic Framework To Manage Cyber Security RiskThis slide shows framework which can be used by IT organizations for managing cyber security related risk. It includes step such as categorize system, security controls, implementation, assess, etc. Introducing our premium set of slides with Strategic Framework To Manage Cyber Security Risk. Elucidate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strategic, Framework, Security Risk. So download instantly and tailor it with your information.
-
 Comparative Analysis Of Cyber Security Incident Mitigation Incident Response Strategies Deployment
Comparative Analysis Of Cyber Security Incident Mitigation Incident Response Strategies DeploymentThis slide represents the comparison between various cyber security incident management softwares based on multiple parameters to help organization select the best incident management software for their organization. It includes comparison between softwares based on user rating, price, mobile support etc. Introducing Comparative Analysis Of Cyber Security Incident Mitigation Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Mobile, Customizable, Price, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Incident Handler Contact Information Incident Response Strategies Deployment
Cyber Security Incident Handler Contact Information Incident Response Strategies DeploymentThis slide represents the contact information of the members responsible for handling and managing the cyber security incidents. It includes details related to name, organization, role and contact details of cyber security incident handler. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handler Contact Information Incident Response Strategies Deployment. This template helps you present information on three stages. You can also present information on Organisation, Role, Contact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Incident Handling Checklist Incident Response Strategies Deployment
Cyber Security Incident Handling Checklist Incident Response Strategies DeploymentThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Introducing Cyber Security Incident Handling Checklist Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Parameters, Analysis, Containment, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Incident Management Team Roles Incident Response Strategies Deployment
Cyber Security Incident Management Team Roles Incident Response Strategies DeploymentThis slide represents the duties performed by the various members of the cyber incident management team. It includes roles and responsivities of ICT technical support staff, crisis manager etc. Introducing Cyber Security Incident Management Team Roles Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Responsibilities, Roles, Management, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Incident Response Plan Timeline Incident Response Strategies Deployment
Cyber Security Incident Response Plan Timeline Incident Response Strategies DeploymentThis slide represents the timeline representing the action plan to effectively respond to cyber security incidents experienced by the organization. It starts with preparation of cyber incident report and ends with return to normal flow. Introducing Cyber Security Incident Response Plan Timeline Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Verification, Detection, Response, using this template. Grab it now to reap its full benefits.
-
 Key Issues Faced By Organization Due To Cyber Security Incidents Response Strategies Deployment
Key Issues Faced By Organization Due To Cyber Security Incidents Response Strategies DeploymentThis slide shows the challenges faced by enterprise due to increase in cyber attacks. It includes cyber security incidents experienced by the organization such as cloud computing issues, theft of sensitive information, ransomware attacks etc. Increase audience engagement and knowledge by dispensing information using Key Issues Faced By Organization Due To Cyber Security Incidents Response Strategies Deployment. This template helps you present information on five stages. You can also present information on Compliance, Information, Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Multiple Strategic Cyber Security Approaches Cyber Attack Risks Mitigation
Multiple Strategic Cyber Security Approaches Cyber Attack Risks MitigationThe following slide depicts various cyber safety approaches to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as data, application, infrastructure, network, devices, automation etc. Increase audience engagement and knowledge by dispensing information using Multiple Strategic Cyber Security Approaches Cyber Attack Risks Mitigation. This template helps you present information on one stage. You can also present information on Identities, Organization Policy, Threat Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps To Create Cyber Security Strategies Cyber Attack Risks Mitigation
Steps To Create Cyber Security Strategies Cyber Attack Risks MitigationThe following slide illustrates some steps to create and implement cybersecurity techniques. It includes elements such as determining threat type, selecting security framework, optimizing plan, implementing strategy etc. Introducing Steps To Create Cyber Security Strategies Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Comprehend Threat Landscape, Evaluate Cybersecurity Maturity, Optimize Cybersecurity Program, using this template. Grab it now to reap its full benefits.
-
 Strategic Cyber Security Action Plan Cyber Attack Risks Mitigation
Strategic Cyber Security Action Plan Cyber Attack Risks MitigationThe following slide depicts action plan to minimize impact of cyber attacks. It includes elements such as understand, develop, deliver, assess organizational principles, evaluate alternatives, examine possible alternatives, execute actions etc. Increase audience engagement and knowledge by dispensing information using Strategic Cyber Security Action Plan Cyber Attack Risks Mitigation. This template helps you present information on three stages. You can also present information on Understand, Develop, Deliver, Organizational Principles using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Strategy Roadmap In Powerpoint And Google Slides Cpb
Security Strategy Roadmap In Powerpoint And Google Slides CpbPresenting Security Strategy Roadmap In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Strategy Roadmap. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Strategic Content Marketing Plan To Engage Audience Security Token Offerings BCT SS
Strategic Content Marketing Plan To Engage Audience Security Token Offerings BCT SSThe following slide illustrates content marketing action plan for security token offerings STO to maximize reach. It includes elements such as objectives, target audience, content strategy, create blogs, determine areas of improvement, etc. Introducing Strategic Content Marketing Plan To Engage Audience Security Token Offerings BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Objectives, Target Audience, Content Strategy, Monitor Performance, using this template. Grab it now to reap its full benefits.
-
 Strategic Influencer Marketing Plan To Create Awareness Security Token Offerings BCT SS
Strategic Influencer Marketing Plan To Create Awareness Security Token Offerings BCT SSThe following slide depicts influencer promotion plan for security token offerings STO project to generate more leads. It includes elements such as objectives, budget, giveaways, tracking and monitoring performance, etc. Increase audience engagement and knowledge by dispensing information using Strategic Influencer Marketing Plan To Create Awareness Security Token Offerings BCT SS. This template helps you present information on five stages. You can also present information on Objectives, Budget, Engage With Influencers, Giveaways using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Business Expansion And Data Security Strategy Icon
Business Expansion And Data Security Strategy IconIntroducing our premium set of slides with Business Expansion And Data Security Strategy Icon. Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Business Expansion, Data Security Strategy Icon. So download instantly and tailor it with your information.
-
 Key Strategies To Secure Business Data
Key Strategies To Secure Business DataThis slide showcase strategies that can be used for securing cyberattacks and target organizational data security and access. It includes updating devices, secure iot technology, track cloud storage, train employees and secure network access. Introducing our premium set of slides with Key Strategies To Secure Business Data. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Updated Devices, Track Cloud Storage, Train Employees. So download instantly and tailor it with your information.
-
 Strategies Enhancing Consumer Iot Security
Strategies Enhancing Consumer Iot SecurityThis slide showcases strategies that assist in enhancing security while using IOT devices by consumers. It contains strategies such as robust authentication mechanisms, software updates and patch management, network segmentation and isolation, user awareness and education etc. Introducing our premium set of slides with Strategies Enhancing Consumer Iot Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Robust Authentication, Network Segmentation, Software Updates. So download instantly and tailor it with your information.
-
 Budget Securing Tips For Public Relations Brand Positioning Strategies To Boost Online MKT SS V
Budget Securing Tips For Public Relations Brand Positioning Strategies To Boost Online MKT SS VThis slide shows various tips which can be used by organizations to while developing marketing budget. It includes aligning marketing outcome with organizational goals, strategic insights and highlight impacts. Increase audience engagement and knowledge by dispensing information using Budget Securing Tips For Public Relations Brand Positioning Strategies To Boost Online MKT SS V. This template helps you present information on three stages. You can also present information on Company, Strategic, Impacts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementation Of Information Best Practices For Effective Endpoint Security Strategy SS V
Implementation Of Information Best Practices For Effective Endpoint Security Strategy SS VThis slide represents best practices for effective endpoint security. It covers educating users finding and tracking business owned devices and installation maintenance of operating systems. Increase audience engagement and knowledge by dispensing information using Implementation Of Information Best Practices For Effective Endpoint Security Strategy SS V. This template helps you present information on three stages. You can also present information on Educate Users, Installation Maintenance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V
Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Protection Of Digital, Safeguard Against Cyber, using this template. Grab it now to reap its full benefits.
-
 Strategies To Enhance Security System In Business
Strategies To Enhance Security System In BusinessThis slide highlights business security system enhancing key strategies. This further includes smart locks, alarm cameras and night safety platforms such as wireless alarms and improved access control. Introducing our premium set of slides with Strategies To Enhance Security System In Business. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Smart Locks, Alarm Cameras, Night Safety Platforms. So download instantly and tailor it with your information.
-
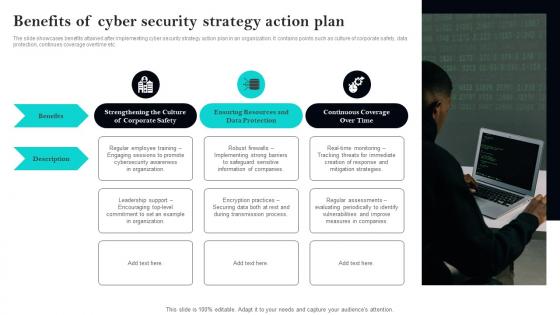 Benefits Of Cyber Security Strategy Action Plan
Benefits Of Cyber Security Strategy Action PlanThe slide showcases benefits attained after implementing cyber security strategy action plan in an organization. It contains points such as culture of corporate safety, data protection, continues coverage overtime etc. Presenting our set of slides with Benefits Of Cyber Security Strategy Action Plan. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Benefits, Description, Protection.
-
 Icon For Implementation Of Cyber Security Strategy Action Plan
Icon For Implementation Of Cyber Security Strategy Action PlanPresenting our set of slides with Icon For Implementation Of Cyber Security Strategy Action Plan. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Strategy, Security.
-
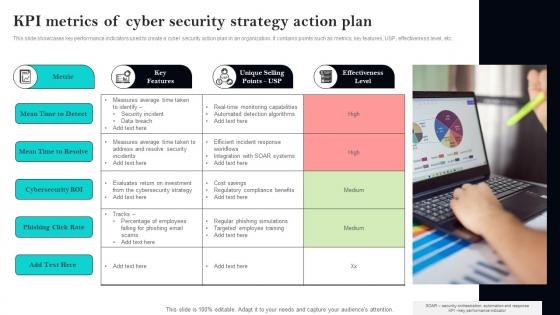 KPI Metrics Of Cyber Security Strategy Action Plan
KPI Metrics Of Cyber Security Strategy Action PlanThis slide showcases key performance indicators used to create a cyber security action plan in an organization. It contains points such as metrics, key features, USP, effectiveness level, etc. Presenting our set of slides with KPI Metrics Of Cyber Security Strategy Action Plan. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Metric, Features, Selling.
-
 Prevention Strategies For Website Cloning To Ensure Cyber Security
Prevention Strategies For Website Cloning To Ensure Cyber SecurityThis slide shows various ways to ensure protection against website cloning. It covers tips to recognize clone websites and strategies to prevent website cloning to achieve cyber security. Introducing our premium set of slides with name Prevention Strategies For Website Cloning To Ensure Cyber Security. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Prevention Strategies, Grammatical Errors, Clone Websites. So download instantly and tailor it with your information.
-
 Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS
Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SSThis slide presents key strategies to ensure data security in retail industry to protect consumer data. It includes PCI DSS compliance, POS security, customer data protection, secure online transactions, inventory management security, and employee training and awareness. Increase audience engagement and knowledge by dispensing information using Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS This template helps you present information on six stages. You can also present information on Customer Data Protection, Online Transactions, Management Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Exit Strategy Investor Capital Pitch Deck For Pauboxs Secure Email Platform
Exit Strategy Investor Capital Pitch Deck For Pauboxs Secure Email PlatformThis slide covers the exit strategy of the email security software company. It includes various exit options such as merger and acquisition and initial public offering. Increase audience engagement and knowledge by dispensing information using Exit Strategy Investor Capital Pitch Deck For Pauboxs Secure Email Platform This template helps you present information on Two stages. You can also present information on Merger And Acquisition, Initial Public Offering using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Infrastructure Security Management Optimisation Strategies
Infrastructure Security Management Optimisation StrategiesThis slide represents the infrastructure security management utilisation methods. Its aim is to run security tools in a secure, documented with virtual team. This slide includes firewall system, remote access, cloud management and workflow system. Introducing our premium set of slides with Infrastructure Security Management Optimisation Strategies. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Generation, Remote, Management. So download instantly and tailor it with your information.
-
 How To Strategically Engage Vendors To Secure Procurement Excellence
How To Strategically Engage Vendors To Secure Procurement ExcellenceThis slide showcases the ways engaging distributors for securing procurement excellence which helps an organization to manage and update approved suppliers lists effectively and quickly. It include details such as analyze vendor performance, provide self service portals, etc. Presenting our set of slides with How To Strategically Engage Vendors To Secure Procurement Excellence. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Analyze Vendor Performance, Service Portals, Vendor Dashboards.
-
 Agenda Implementing Strategies To Mitigate Cyber Security Threats
Agenda Implementing Strategies To Mitigate Cyber Security ThreatsIntroducing Agenda Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Security Awareness, Risk Management Process, Cyber Risk using this template. Grab it now to reap its full benefits.
-
 Cyber Security Awareness Facts And Statistics Implementing Strategies To Mitigate Cyber Security Threats
Cyber Security Awareness Facts And Statistics Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases some facts and figures to generate awareness about cyber crimes. It includes elements such as hike in ransomware attacks, more employees are expected to be target of malware attacks, increasing cost of data breaches etc Introducing Cyber Security Awareness Facts And Statistics Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Malware Attacks, Employees, Social Engineering Attacks using this template. Grab it now to reap its full benefits.
-
 Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security Threats
Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the negative impact of cyber crimes on business to build control actions and strategies. It includes key elements such as rising costs, reputational damage, operational disruption, loss of revenue etc. Introducing Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Rising Cost, Reputational Damage, Operational Disruption using this template. Grab it now to reap its full benefits.
-
 Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By Companies
Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By CompaniesThe purpose of this slide is to assess security and privacy challenges, and their impact on data migration process. It includes challenges and need for ensuring data privacy. Introducing Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By Companies to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Data Security And Privacy Challenges, Loss Of Customers, Sensitive Data, Poses Security And Privacy Concerns, using this template. Grab it now to reap its full benefits.
-
 Strategic Approach For Effective Data Migration Steps For A Secure Data Migration Process
Strategic Approach For Effective Data Migration Steps For A Secure Data Migration ProcessThe purpose of this slide is to represent the process of secure and safe data migration from one platform to another. It includes various stages such as assessing data sources, choosing method, designing architecture, etc. Introducing Strategic Approach For Effective Data Migration Steps For A Secure Data Migration Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Design Architecture, Validate And Verify Results, Assess Data Sources, Data Migration Process, using this template. Grab it now to reap its full benefits.
-
 Strategic Influencer Beginners Guide To Successfully Launch Security Token BCT SS V
Strategic Influencer Beginners Guide To Successfully Launch Security Token BCT SS VThe following slide depicts influencer promotion plan for security token offerings STO project to generate more leads. It includes elements such as objectives, budget, giveaways, tracking and monitoring performance, etc. Increase audience engagement and knowledge by dispensing information using Strategic Influencer Beginners Guide To Successfully Launch Security Token BCT SS V. This template helps you present information on five stages. You can also present information on Objectives, Budget, Giveaways using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
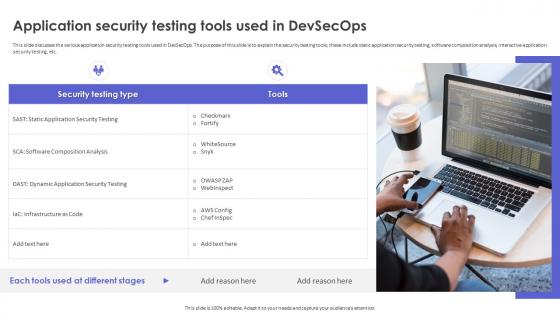 Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOps
Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOpsThis slide discusses the various application security testing tools used in DevSecOps. The purpose of this slide is to explain the security testing tools these include static application security testing, software composition analysis, interactive application security testing, etc. Increase audience engagement and knowledge by dispensing information using Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOps. This template helps you present information on one stages. You can also present information on Application Security Testing, Software Composition Analysis, Interactive Application Security Testing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Automation Strategies To Enhance Security And Compliance
Cloud Automation Strategies To Enhance Security And ComplianceThis slide represents cloud automation strategies to enhance security and compliance which assists organizations to streamline operations and minimizes manual intervention. It includes cloud automation strategies to enhance security and compliances such as utilize infrastructure as code, etc. Introducing our premium set of slides with name Cloud Automation Strategies To Enhance Security And Compliance. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Consulting Partner, Leverage Automation, Enhance Compliance, Utilize Policy As Tools. So download instantly and tailor it with your information.
-
 Impact Of Establishing Strategic On IoT Security Boosting Manufacturing Efficiency With IoT
Impact Of Establishing Strategic On IoT Security Boosting Manufacturing Efficiency With IoTThis slide showcases positive effects of implementing strategies on IoT security. It includes various KPIs such as web interfaces, network services, encryption, mobile interfaces, etc. Introducing Impact Of Establishing Strategic On IoT Security Boosting Manufacturing Efficiency With IoT to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Web Interfaces, Network Services, Encryption, using this template. Grab it now to reap its full benefits.
-
 Securing Food Safety In Online Strategies To Mitigate Food Delivery Challenges Faced
Securing Food Safety In Online Strategies To Mitigate Food Delivery Challenges FacedThis slide covers strategies to mitigate challenges faced by restaurant business such as third party integrations, innovative packaging, route optimization software and cyber security measures. Introducing Securing Food Safety In Online Strategies To Mitigate Food Delivery Challenges Faced to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Challenges, Innovative Packaging, Technology Integrations, using this template. Grab it now to reap its full benefits.
-
 Major Types Of Application Security Strategies
Major Types Of Application Security StrategiesThis slide showcases the different techniques of application security which include authentication, authorization, encryption, logging, and security testing. Presenting our set of slides with Major Types Of Application Security Strategies This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Spot Potential, Recognize Valuable Data, Vulnerable Areas
-
 Endpoint Security Roadmap With Strategic Building Next Generation Endpoint Security Cybersecurity SS
Endpoint Security Roadmap With Strategic Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases a timeline which will guide businesses in implementing their enhanced endpoint security initiatives such as antivirus, privilege management, EDR, etc.Increase audience engagement and knowledge by dispensing information using Endpoint Security Roadmap With Strategic Building Next Generation Endpoint Security Cybersecurity SS. This template helps you present information on one stages. You can also present information on Other Endpoint Security Tools, Endpoint Privilege Management, Antivirus, End Point Detection And Response using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategies To Mitigate Cyber Security Risks In Banking Sector
Strategies To Mitigate Cyber Security Risks In Banking SectorThis slide represents approaches to reduce risk of cyber security in banking sector. This template aims to cyber security risks in banking sector to protect sensitive financial data and maintain customer trust. It includes various strategies such as risk determination, mitigating identity theft and fraud, etc. Introducing our premium set of slides with Strategies To Mitigate Cyber Security Risks In Banking Sector. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Privacy Protection, Application Control, Risk Determination. So download instantly and tailor it with your information.
-
 User Based Security Training Model Strategic Guide To Implement Strategy SS
User Based Security Training Model Strategic Guide To Implement Strategy SSIntroducing User Based Security Training Model Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Compromised System, Compromised Network, Critical Assets, Exfiltrate Sensitive Data, using this template. Grab it now to reap its full benefits.
-
 Wi Fi Security To Protect Network And Connected Devices Strategic Guide To Implement Strategy SS
Wi Fi Security To Protect Network And Connected Devices Strategic Guide To Implement Strategy SSThis slide showcases the Wi-Fi security to protect network and connected devices. It includes strategies such as strong passwords, encryption, firewall and intrusion detection systems IDS and two-factor authentication 2FA.Introducing Wi Fi Security To Protect Network And Connected Devices Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Two Factor Authentication, Intrusion Detection Systems, Encryption, Strong Passwords, using this template. Grab it now to reap its full benefits.



