Powerpoint Templates and Google slides for Security Rules
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Hotel safety and security emergency process with 5 boxes
Hotel safety and security emergency process with 5 boxesPresenting hotel safety and security emergency process with 5 boxes. This is a hotel safety and security emergency process with 5 boxes. This is a five stage process. The stages in this process are hotel safety and security, guest house safety, lodge safety.
-
 Hotel safety and security procedures with converging arrows and boxes
Hotel safety and security procedures with converging arrows and boxesPresenting hotel safety and security procedures with converging arrows and boxes. This is a hotel safety and security procedures with converging arrows and boxes. This is a six stage process. The stages in this process are hotel safety and security, guest house safety, lodge safety.
-
 Business process automation standardise security collaboration consistency
Business process automation standardise security collaboration consistencyPresenting this set of slides with name - Business Process Automation Standardise Security Collaboration Consistency. This is a eight stage process. The stages in this process are Business Process Automation, Robotic Process Automation, Software Development.
-
 Intelligent process automation framework icons slide security ppt powerpoint presentation file
Intelligent process automation framework icons slide security ppt powerpoint presentation filePresenting this set of slides with name Intelligent Process Automation Framework Icons Slide Security Ppt Powerpoint Presentation File. The topics discussed in these slides are Technology, Communication, Knowledge, Planning, Marketing. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Intelligent process automation framework security a136 ppt powerpoint presentation layouts
Intelligent process automation framework security a136 ppt powerpoint presentation layoutsPresenting this set of slides with name Intelligent Process Automation Framework Security A136 Ppt Powerpoint Presentation Layouts. This is a five stage process. The stages in this process are Technology, Cognitive Agents, Planning, Strategy, Marketing. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Investment process security analysis ppt powerpoint presentation icon background images cpb
Investment process security analysis ppt powerpoint presentation icon background images cpbPresenting this set of slides with name Investment Process Security Analysis Ppt Powerpoint Presentation Icon Background Images Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Investment Process Security Analysis to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Encryption security ppt powerpoint presentation icon rules cpb
Encryption security ppt powerpoint presentation icon rules cpbPresenting this set of slides with name Encryption Security Ppt Powerpoint Presentation Icon Rules Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Encryption Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security essentials ppt powerpoint presentation model rules cpb
Cyber security essentials ppt powerpoint presentation model rules cpbPresenting this set of slides with name Cyber Security Essentials Ppt Powerpoint Presentation Model Rules Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Cyber Security Essentials to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Computer security trends information security ppt powerpoint presentation icon rules cpb
Computer security trends information security ppt powerpoint presentation icon rules cpbPresenting this set of slides with name Computer Security Trends Information Security Ppt Powerpoint Presentation Icon Rules Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Computer Security Trends Information Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security audit procedures ppt powerpoint presentation infographics slides cpb
Cyber security audit procedures ppt powerpoint presentation infographics slides cpbPresenting this set of slides with name Cyber Security Audit Procedures Ppt Powerpoint Presentation Infographics Slides Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Cyber Security Audit Procedures to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Itil security management process ppt powerpoint presentation visual aids slides cpb
Itil security management process ppt powerpoint presentation visual aids slides cpbPresenting this set of slides with name ITIL Security Management Process Ppt Powerpoint Presentation Visual Aids Slides Cpb. This is an editable Powerpoint three stages graphic that deals with topics like ITIL Security Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Application security management process ppt powerpoint presentation guide cpb
Application security management process ppt powerpoint presentation guide cpbPresenting this set of slides with name Application Security Management Process Ppt Powerpoint Presentation Guide Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Application Security Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security processing ppt powerpoint presentation file design ideas cpb
Security processing ppt powerpoint presentation file design ideas cpbPresenting this set of slides with name Security Processing Ppt Powerpoint Presentation File Design Ideas Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Security Processing to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Computer security cyber security quotes ppt powerpoint presentation show rules cpb
Computer security cyber security quotes ppt powerpoint presentation show rules cpbPresenting our Computer Security Cyber Security Quotes Ppt Powerpoint Presentation Show Rules Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Computer Security Cyber Security Quotes This PPT slide can be easily accessed in standard screen 4.3 and widescreen 16.9 aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Step 1 2 3 of network security process
Step 1 2 3 of network security processPresenting our set of slides with name Step 1 2 3 Of Network Security Process. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Step 1 2 3 Network, Security, Process.
-
 Application security review process ppt powerpoint presentation icon ideas cpb
Application security review process ppt powerpoint presentation icon ideas cpbPresenting our Application Security Review Process Ppt Powerpoint Presentation Icon Ideas Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Application Security Review Process This PPT slide can be easily accessed in standard screen 4.3 and widescreen 16.9 aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security risk management process ppt powerpoint presentation file vector cpb
Security risk management process ppt powerpoint presentation file vector cpbPresenting our Security Risk Management Process Ppt Powerpoint Presentation File Vector Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Online Security Issues This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Data and security breach process
Data and security breach processThis slide exhibits data and security breach attack process conducted by hackers to get access to company data. It includes multiple activities such as- link forwarding by emails, data sharing and attacking and so on. Introducing our Data And Security Breach Process set of slides. The topics discussed in these slides are Research, Stage Attack, Exfiltrate. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Process for responding to security data breach
Process for responding to security data breachThis slide exhibits process for responding to security data breach. It includes multiple steps such as- analyzing the current damage, keeping record how much damage is caused and so on. Introducing our Process For Responding To Security Data Breach set of slides. The topics discussed in these slides are Survey, Limit, Learn, Engage, Record. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security data breach process by backdoor
Security data breach process by backdoorFollowing slide showcase how a data breach process is performed by hacker to collect and utilize company data. It includes following activities such as- code integration with company software, so on. Introducing our Security Data Breach Process By Backdoor set of slides. The topics discussed in these slides are Execution Persistence, Defense Evasion, Supply Chain Attack, Exfiltration, Backdoor Activates. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Smart criteria software security ppt powerpoint presentation show rules cpb
Smart criteria software security ppt powerpoint presentation show rules cpbPresenting Smart Criteria Software Security Ppt Powerpoint Presentation Show Rules Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Smart Criteria Software Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Five steps information security process model ppt powerpoint presentation background images cpb
Five steps information security process model ppt powerpoint presentation background images cpbPresenting Five Steps Information Security Process Model Ppt Powerpoint Presentation Background Images Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Five Steps Information Security Process Model. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Steps to ensure robotic process automation security ppt powerpoint presentation model example
Steps to ensure robotic process automation security ppt powerpoint presentation model exampleThis slide defines steps to ensure the security of robotic process automation, and it covers guarantee accountability for bot activities, protection from abuse, frauds, logs and bot development. Increase audience engagement and knowledge by dispensing information using Steps To Ensure Robotic Process Automation Security Ppt Powerpoint Presentation Model Example. This template helps you present information on four stages. You can also present information on Development, Respectability, Guarantee Accountability using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations.
-
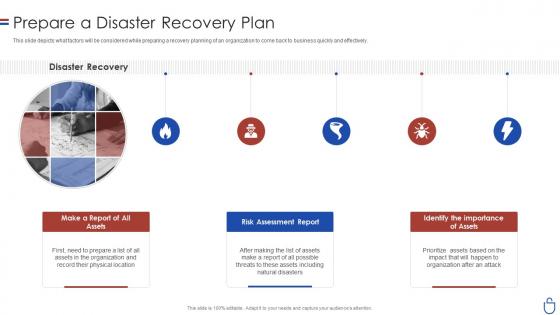 Data security it prepare a disaster recovery plan ppt slides rules
Data security it prepare a disaster recovery plan ppt slides rulesThis slide depicts what factors will be considered while preparing a recovery planning of an organization to come back to business quickly and effectively. Introducing Data Security IT Prepare A Disaster Recovery Plan Ppt Slides Rules to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Disaster Recovery, Make Report Assets, Risk Assessment Report Assets, Identify importance, using this template. Grab it now to reap its full benefits.
-
 Information Security Management System Audit Process
Information Security Management System Audit ProcessThe following slide highlights the information security management system audit process illustrating information security system details, information collection, statement o applicability review, audit scope, risk management analysis, gap analysis, business continuity and contingency plan review, mitigation strategy and compliance audit activities Introducing our Information Security Management System Audit Process set of slides. The topics discussed in these slides are Information Collection, Mitigation Strategy, Gap Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Roadmap With Process And Tasks
Cyber Security Roadmap With Process And TasksThis slide represent roadmap for various cyber security task and process like response planning ,risk assessment progress in an organization with timeline. It includes hours per week ,owner and start date introducing our Cyber Security Roadmap With Process And Tasks set of slides. The topics discussed in these slides are Roadmap, Process, Assessment. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Key Steps Of Saas Security Process
Key Steps Of Saas Security ProcessThe following slide depicts the SaaS security process to acknowledge the gap and have proactive approach. It mainly constitutes of three phases discover, monitor and protect. Presenting our set of slides with name Key Steps Of Saas Security Process. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ascertain Threats And Attacks, Encrypt Sensitive Data, Review Log Activities.
-
 Process Of Security Risk Management Plan
Process Of Security Risk Management PlanThis slide shows the process of security risk management plan which includes communication and consultation, monitoring and reviewing with establishing context such as strategic, security and entity with risk assessment steps that focuses on identification, assessment, etc. Introducing our Process Of Security Risk Management Plan set of slides. The topics discussed in these slides are Threat Assessment, Vulnerability Assessment, Security Context . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Nist Framework Process For Security Control Selection
Nist Framework Process For Security Control SelectionMentioned Slide Showcases The Process To Choose Security Controls Based On Nist Security Control. It Include Steps Like Security Categorization Using Fips 199, Identify Baseline Security Controls, Tailoring Baseline Security Controls And Document The Control Selection Process. Presenting Our Well Structured Nist Framework Process For Security Control Selection. The Topics Discussed In This Slide Are Framework, Process, Categorization. This Is An Instantly Available Powerpoint Presentation That Can Be Edited Conveniently. Download It Right Away And Captivate Your Audience.
-
 Six Step Process For Risk Management In Cyber Security Project
Six Step Process For Risk Management In Cyber Security ProjectThis slide signifies the six step process for risk assessment in cyber security project. It covers information about stages like identify, analyse, evaluate, prioritize, treat and monitor Presenting our set of slides with name Six Step Process For Risk Management In Cyber Security Project. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Management, Process, Computing Software.
-
 Two Factor Authentication Process Flow For Enhanced Security E Wallets As Emerging Payment Method Fin SS V
Two Factor Authentication Process Flow For Enhanced Security E Wallets As Emerging Payment Method Fin SS VThis slide shows flow chart which can be used to understand how two factor authentication security feature works. It includes steps such as enter username and password, verify biometrics or enter OTP, etc. Present the topic in a bit more detail with this Two Factor Authentication Process Flow For Enhanced Security E Wallets As Emerging Payment Method Fin SS V. Use it as a tool for discussion and navigation on Authentication, Process, Possession Verification. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Step By Step Process Of E Commerce Security
Step By Step Process Of E Commerce SecurityThis slide shows e-commerce transactions and data integrity through comprehensive multi-layer security measures. The steps are regular back of database, set up strong passwords, use malware softwwares,etc. Presenting our set of slides with Step By Step Process Of E Commerce Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Process, Ecommerce Security, Security Measures.
-
 Endpoint Security Process With Key Stages Building Next Generation Endpoint Security Cybersecurity SS
Endpoint Security Process With Key Stages Building Next Generation Endpoint Security Cybersecurity SSIntroducing Endpoint Security Process With Key Stages Building Next Generation Endpoint Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Gather Information, Choose Security Solutions, Implement Chosen Solutions, using this template. Grab it now to reap its full benefits.
-
 Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security Measures
Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security MeasuresThe slide depicts secure sockets layer SSL process to encrypt sensitive information between a webs browser and server. It include client web browser, websiteserver, SSL certificate etc. Introducing Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security Measures to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Client Check Certificate, Impact, Delivers Encrypted Content, using this template. Grab it now to reap its full benefits.


