Powerpoint Templates and Google slides for Security Risks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Addressing cyber threats various industries cyber security risk management
Addressing cyber threats various industries cyber security risk managementThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Introducing Addressing Cyber Threats Various Industries Cyber Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Industry, Healthcare, Manufacturing, Government, Energy, using this template. Grab it now to reap its full benefits.
-
 Agenda of cyber security risk management ppt slides graphics
Agenda of cyber security risk management ppt slides graphicsThe purpose is to ensure management of various threats faced by firm and secure valuable assets associated to firm in terms of digital assets, people, financial assets, physical security, etc. Increase audience engagement and knowledge by dispensing information using Agenda Of Cyber Security Risk Management Ppt Slides Graphics. This template helps you present information on four stages. You can also present information on Management, Various Threats, Assets Associated, Digital Assets, People, Financial Assets using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber security risk management addressing asset security categorization
Cyber security risk management addressing asset security categorizationThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Introducing Cyber Security Risk Management Addressing Asset Security Categorization to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Position, Ownership, Location, Security Categorization, Integrity, Confidentiality, Availability, Value , using this template. Grab it now to reap its full benefits.
-
 Cyber security risk management addressing indicators associated to insider threats
Cyber security risk management addressing indicators associated to insider threatsThis slide provides details regarding indicators associated to insider threats in terms of traits, demeanor and goals, etc. Introducing Cyber Security Risk Management Addressing Indicators Associated To Insider Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Demeanor, goals, Traits, Data Exfiltration, Financial Stress, using this template. Grab it now to reap its full benefits.
-
 Cyber security risk management contingency plan for cyber threat handling
Cyber security risk management contingency plan for cyber threat handlingThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Introducing Cyber Security Risk Management Contingency Plan For Cyber Threat Handling to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Contingency Solutions, Contingency Considerations, System Backups, Vendors Coordination, using this template. Grab it now to reap its full benefits.
-
 Cyber security risk management incident reporting by different departments
Cyber security risk management incident reporting by different departmentsThis slide will help in providing an overview of the various reported incidents, average cost per incident and number of people involved in the various incidents across different departments. Introducing Cyber Security Risk Management Incident Reporting By Different Departments to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Number Incidents, Person Involved Incident, Average Cost Per Incident, using this template. Grab it now to reap its full benefits.
-
 Impact analysis for effective threat management in cyber security risk management
Impact analysis for effective threat management in cyber security risk managementThis slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Introducing Impact Analysis For Effective Threat Management In Cyber Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Focus Areas, Actual Access Violations, Access Rights Authorized, using this template. Grab it now to reap its full benefits.
-
 Agenda of effective information security risk management process
Agenda of effective information security risk management processIncrease audience engagement and knowledge by dispensing information using Agenda Of Effective Information Security Risk Management Process. This template helps you present information on three stages. You can also present information on Agenda using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Setting scenario security control effective information security risk management process
Setting scenario security control effective information security risk management processFollowing slide displays security control scenario setting. It includes scenario detail, category of security controls and controls description.Introducing Setting Scenario Security Control Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Controls, Operational Controls, Technical Controls, using this template. Grab it now to reap its full benefits.
-
 How financial risk can be controlled managing critical threat vulnerabilities and security threats
How financial risk can be controlled managing critical threat vulnerabilities and security threatsThis slide provides details regarding various ways through financial risks can be controlled by handling liquidity risk, foreign exchange risk and credit exchange risk. Increase audience engagement and knowledge by dispensing information using How Financial Risk Can Be Controlled Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on three stages. You can also present information on Liquidity Risk, Exchange Risk, Credit Exchange Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security risk assessment project analysis templates bundle ppt diagrams
Security risk assessment project analysis templates bundle ppt diagramsIntroducing Security Risk Assessment Project Analysis Templates Bundle Ppt Diagrams to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Threat, Vulnerability, Asset And Consequences, Risk, Solution, using this template. Grab it now to reap its full benefits.
-
 Agenda Security Program For Effective Cybersecurity Risk Management
Agenda Security Program For Effective Cybersecurity Risk ManagementIntroducing Agenda Security Program For Effective Cybersecurity Risk Management to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Digitalization, Cybersecurity, Business, using this template. Grab it now to reap its full benefits.
-
 Agenda For Risk Management Framework For Information Security
Agenda For Risk Management Framework For Information SecurityIntroducing Agenda For Risk Management Framework For Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threats And Vulnerabilities, Organizational Risks, Information Security, using this template. Grab it now to reap its full benefits.
-
 Risk Management Framework For Information Security Roles And Responsibilities For Managing
Risk Management Framework For Information Security Roles And Responsibilities For ManagingFollowing slide demonstrates various roles and responsibilities for information security management. Responsibilities covered are security policy development, asset classification and security framework development. Increase audience engagement and knowledge by dispensing information using Risk Management Framework For Information Security Roles And Responsibilities For Managing. This template helps you present information on two stages. You can also present information on Chief Information Officer, Information Management Manager, IT Manger, Risk Management Officer using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risk Management Framework For Information Security Table Of Contents
Risk Management Framework For Information Security Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Risk Management Framework For Information Security Table Of Contents. This template helps you present information on one stages. You can also present information on Incident Management, Incident Management Workflow, Incidents Logging Process, Incident Prioritization Matrix, Tool We Will Use using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents Risk Management Framework For Information Security
Table Of Contents Risk Management Framework For Information SecurityIntroducing Table Of Contents Risk Management Framework For Information Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Present Scenario, Training And Budget, Dashboards, Information Security System Checklists, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Risk Management Framework Budget For Information Security Management
Cybersecurity Risk Management Framework Budget For Information Security ManagementMentioned slide shows budget for managing information security. It includes information such as functional area, software name, training duration, training cost, number of employees and total training cost. Introducing Cybersecurity Risk Management Framework Budget For Information Security Management to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Functional Area, Training Duration, Training Cost Per Employee, Employees To Be Trained, Total Cost Of Implementation, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Risk Management Framework Setting Scenario For Security Control
Cybersecurity Risk Management Framework Setting Scenario For Security ControlFollowing slide displays security control scenario setting. It includes scenario detail, category of security controls and controls description. Increase audience engagement and knowledge by dispensing information using Cybersecurity Risk Management Framework Setting Scenario For Security Control. This template helps you present information on three stages. You can also present information on Technical Controls, Management Controls, Operational Controls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Solution Recommendation For Common Business Cyber Security Risks
Solution Recommendation For Common Business Cyber Security RisksThis slide covers the major IT support skills that could potentially help organizations to solve the most common IT problems. It includes solutions for common cyber risks such as poor network security, data backup issues, etc. Introducing our premium set of slides with Solution Recommendation For Common Business Cyber Security Risks. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risks, Solution Recommendation, Network Security. So download instantly and tailor it with your information.
-
 Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach
Checklist For Effectively Managing Asset Security Introducing A Risk Based ApproachFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Introducing Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on System Monitoring, Virus Scanning, System Monitoring using this template. Grab it now to reap its full benefits.
-
 Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber Security
Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber SecurityMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security.Increase audience engagement and knowledge by dispensing information using Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber Security This template helps you present information on one stage. You can also present information on Internet Of Things, Artificial Intelligence, Human Machine Interface using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda For Risk Assessment And Management Plan For Information Security
Agenda For Risk Assessment And Management Plan For Information SecurityIntroducing Agenda For Risk Assessment And Management Plan For Information Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Assessment, Management, Information, using this template. Grab it now to reap its full benefits.
-
 Current Information Security Issues Faced Risk Assessment And Management Plan For Information Security
Current Information Security Issues Faced Risk Assessment And Management Plan For Information SecurityIncrease audience engagement and knowledge by dispensing information using Current Information Security Issues Faced Risk Assessment And Management Plan For Information Security. This template helps you present information on four stages. You can also present information on Untrained Employees, Frequent Data Breaches, Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Process For Information Security Risk Assessment And Management Plan For Information Security
Process For Information Security Risk Assessment And Management Plan For Information SecurityThis slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets Introducing Process For Information Security Risk Assessment And Management Plan For Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Process, Information, Assessment, using this template. Grab it now to reap its full benefits.
-
 Business Cyber Security Risk Assessment Process
Business Cyber Security Risk Assessment ProcessThe slide shows cyber threat detection and protection measures in order to eliminate the potential risks to the business. The steps include identifying, detecting, responding, protecting, and recovering. Presenting our set of slides with Business Cyber Security Risk Assessment Process. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Detect, Respond, Protect.
-
 Determining Roles And Responsibilities For Risk Handling Android Device Security Management
Determining Roles And Responsibilities For Risk Handling Android Device Security ManagementThis slide provides information regarding the roles and responsibilities of management in handling mobile device security risks. Key people involved in risk handling are chief risk officer, chief information security officer, senior management and executives and line managers. Introducing Determining Roles And Responsibilities For Risk Handling Android Device Security Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Line Management, Senior Management, Chief Information Security Officer, using this template. Grab it now to reap its full benefits.
-
 Agenda Enterprise Risk Management And Information Technology Security
Agenda Enterprise Risk Management And Information Technology SecurityIntroducing Agenda Enterprise Risk Management And Information Technology Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Organization, IT Networks, IT Risk Management, using this template. Grab it now to reap its full benefits.
-
 Enterprise Risk Management And Information Technology Security Table Of Contents
Enterprise Risk Management And Information Technology Security Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Enterprise Risk Management And Information Technology Security Table Of Contents. This template helps you present information on one stages. You can also present information on Security Criteria, Control Measures, IT System Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Enterprise Risk Management And Information Technology Security
Table Of Contents For Enterprise Risk Management And Information Technology SecurityIntroducing Table Of Contents For Enterprise Risk Management And Information Technology Security to increase your presentation threshold. Encompassed with eleven stages, this template is a great option to educate and entice your audience. Dispence information on IT Risks, Threat Evaluation, IT Risk Management, Cost Estimation, using this template. Grab it now to reap its full benefits.
-
 Information Security Risk Indicators Examples In Powerpoint And Google Slides Cpb
Information Security Risk Indicators Examples In Powerpoint And Google Slides CpbPresenting our Information Security Risk Indicators Examples In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Information Security Risk Indicators Examples This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Key Risk Indicators Examples Information Security In Powerpoint And Google Slides Cpb
Key Risk Indicators Examples Information Security In Powerpoint And Google Slides CpbPresenting our Key Risk Indicators Examples Information Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Key Risk Indicators Examples Information Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Risk Remediation Framework
Cyber Security Risk Remediation FrameworkThe following slide showcases the risk remediation framework to plan preventive and reactive actions. It includes elements such as categorize, select, implement, assess, authorize and monitor etc. Introducing our premium set of slides with Cyber Security Risk Remediation Framework. Elucidate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Categorize System, Implement Security Controls, Assess Security Controls, Authorize System. So download instantly and tailor it with your information.
-
 Risks Cyber Security In Powerpoint And Google Slides Cpb
Risks Cyber Security In Powerpoint And Google Slides CpbPresenting our Risks Cyber Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Risks Cyber Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Agenda For Information Security Risk Management And Mitigation Plan Ppt Tips
Agenda For Information Security Risk Management And Mitigation Plan Ppt TipsIntroducing Agenda For Information Security Risk Management And Mitigation Plan Ppt Tips to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Organization, Information Security, Risk Management, using this template. Grab it now to reap its full benefits.
-
 Allocating Budget For Information Security Risk Management Programme
Allocating Budget For Information Security Risk Management ProgrammeThis slide showcase budget to be allocated for conducting training for information security risk management. It showcases budget for area like cybersecurity awareness, threat detection and risk management. Increase audience engagement and knowledge by dispensing information using Allocating Budget For Information Security Risk Management Programme. This template helps you present information on three stages. You can also present information on Functional Areas, Description, Training Cost using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Assigning Criticality Rating To Information Assets Information Security Risk Management
Assigning Criticality Rating To Information Assets Information Security Risk ManagementThis slide showcases criticality rating that can be allocation to assets for identifying critical assets. Its key elements are asset, failure cost, failure impact and criticality rating. Introducing Assigning Criticality Rating To Information Assets Information Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Sales Records, Customer Database, Product Database, using this template. Grab it now to reap its full benefits.
-
 Budget For Information Security Risk Management Ppt Microsoft
Budget For Information Security Risk Management Ppt MicrosoftThis slide showcases budget that can should be allocated for different information security risk management activities. It provides information about employees training, software implementation, risk monitoring and data backup. Increase audience engagement and knowledge by dispensing information using Budget For Information Security Risk Management Ppt Microsoft. This template helps you present information on one stage. You can also present information on Budget, Information Security, Risk Management using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Challenges And Solutions In Information Security Risk Management
Challenges And Solutions In Information Security Risk ManagementThis slide showcases challenges involved in formulating risk management program for information security. It also shows solutions to tackle the challenges and impact of implementing them. Introducing Challenges And Solutions In Information Security Risk Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Fighting Frauds, Internal Vulnerabilities, Employee Awareness, using this template. Grab it now to reap its full benefits.
-
 G9 Table Of Contents For Information Security Risk Management And Mitigation Plan
G9 Table Of Contents For Information Security Risk Management And Mitigation PlanIntroducing G9 Table Of Contents For Information Security Risk Management And Mitigation Plan to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Information Security Risk, Management Plan, Process, using this template. Grab it now to reap its full benefits.
-
 Gap Assessment Of Organization Information Security Information Security Risk Management
Gap Assessment Of Organization Information Security Information Security Risk ManagementThis slide showcases gap assessment of information security capabilities of organization. It also provides solutions to tackle the problems faced by company like frequent malware attacks and lack of awareness among employees. Increase audience engagement and knowledge by dispensing information using Gap Assessment Of Organization Information Security Information Security Risk Management. This template helps you present information on three stages. You can also present information on Gap Assessment, Organization Information Security, Ransomware Attacks using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Identifying Employees For Information Information Security Risk Management
Identifying Employees For Information Information Security Risk ManagementThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner. Introducing Identifying Employees For Information Information Security Risk Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Threat Scanning, Identifying Employees, Security Training Programme, using this template. Grab it now to reap its full benefits.
-
 Identifying Information Security Threats And Impact Information Security Risk Management
Identifying Information Security Threats And Impact Information Security Risk ManagementThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization. Increase audience engagement and knowledge by dispensing information using Identifying Information Security Threats And Impact Information Security Risk Management. This template helps you present information on one stage. You can also present information on Errors And Omissions, Employee Sabotage, Physical Infrastructure Loss using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Matrix For Threat Solution And Risk Management Information Security Risk Management
Matrix For Threat Solution And Risk Management Information Security Risk ManagementThis slide showcases matrix that can help organization to formulate solutions for different types of information security attacks. It can help organization to mitigate the risks and safeguard information in case of any attack. Introducing Matrix For Threat Solution And Risk Management Information Security Risk Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Monitor Database Activity, Validate Database Protocols, Capture Detailed Transactions, using this template. Grab it now to reap its full benefits.
-
 Process For Information Security Risk Assessment Information Security Risk Management
Process For Information Security Risk Assessment Information Security Risk ManagementThis slide showcases process that can help organization to perform information security risk assessment. It can help to identify security threats and allocate vulnerability rating to information assets. Introducing Process For Information Security Risk Assessment Information Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Information Security Threats, Allocating Vulnerability, Risk Assessment, using this template. Grab it now to reap its full benefits.
-
 Types Security Risk Assessments Exists In Powerpoint And Google Slides Cpb
Types Security Risk Assessments Exists In Powerpoint And Google Slides CpbPresenting our Types Security Risk Assessments Exists In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Types Security Risk Assessments Exists. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Data Security Risk Treatment Action Plan Icon
Data Security Risk Treatment Action Plan IconPresenting our set of slides with Data Security Risk Treatment Action Plan Icon. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Security Risk Treatment, Action Plan Icon.
-
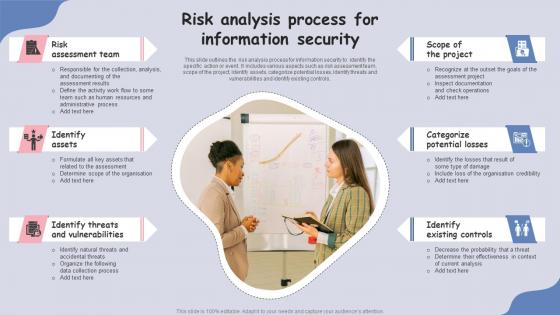 Risk Analysis Process For Information Security
Risk Analysis Process For Information SecurityThis slide outlines the risk analysis process for information security to identify the specific action or event. It includes various aspects such as risk assessment team, scope of the project, identify assets, categorize potential losses, identify threats and vulnerabilities and identify existing controls.Presenting our set of slides with Risk Analysis Process For Information Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Assessment Team, Identify Assets, Identify Threats.
-
 Security Plan To Prevent Cyber Cybersecurity Risk Assessment Program For Table Of Contents
Security Plan To Prevent Cyber Cybersecurity Risk Assessment Program For Table Of ContentsIntroducing Security Plan To Prevent Cyber Cybersecurity Risk Assessment Program For Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Risk, Assessment Program, Conduct Cybersecurity, Risk Assessment, using this template. Grab it now to reap its full benefits.
-
 Analyse Consequences Of Cyber Security Threats Improving Cyber Security Risks Management
Analyse Consequences Of Cyber Security Threats Improving Cyber Security Risks ManagementThe following slide depicts the negative impact of cyber-crimes on business to build control actions and strategies. It includes elements such as reputational damage, theft, financial losses, fines etc. Introducing Analyse Consequences Of Cyber Security Threats Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reputational Damage, Financial Losses, Security Threats, using this template. Grab it now to reap its full benefits.
-
 Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management
Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks ManagementThe following slide showcases the various types of cyber-attacks faced by employees to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service etc. Introducing Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Spear Phishing, Advanced Persistent Threats, Ransomware, Phishing, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Risk Mitigation Strategy Action Plan Icon
Cyber Security Risk Mitigation Strategy Action Plan IconIntroducing our premium set of slides with Cyber Security Risk Mitigation Strategy Action Plan Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Mitigation, Strategy, Action. So download instantly and tailor it with your information.
-
 Fully Paid Securities Lending Program Risks In Powerpoint And Google Slides Cpb
Fully Paid Securities Lending Program Risks In Powerpoint And Google Slides CpbPresenting our Fully Paid Securities Lending Program Risks PowerPoint template design. This PowerPoint slide showcases Four stages. It is useful to share insightful information on Fully Paid Securities Lending Program Risks This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Agenda For Hands On Blockchain Security Risk Management And Best Practices BCT SS V
Agenda For Hands On Blockchain Security Risk Management And Best Practices BCT SS VIntroducing Agenda For Hands On Blockchain Security Risk Management And Best Practices BCT SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Market Insights, Blockchain Technology, Threats And Attacks, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents Hands On Blockchain Security Risk Management And Best Practices BCT SS V
Table Of Contents Hands On Blockchain Security Risk Management And Best Practices BCT SS VIncrease audience engagement and knowledge by dispensing information using Table Of Contents Hands On Blockchain Security Risk Management And Best Practices BCT SS V. This template helps you present information on one stages. You can also present information on Industry Overview, Blockchain Cybersecurity, Blockchain Cyber Security Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Y196 Hands On Blockchain Security Risk Management And Best Practices Table Of Contents BCT SS V
Y196 Hands On Blockchain Security Risk Management And Best Practices Table Of Contents BCT SS VIntroducing Y196 Hands On Blockchain Security Risk Management And Best Practices Table Of Contents BCT SS V to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Blockchain Cyber Security, Risk Management Process, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Awareness Facts And Statistics Cyber Risk Assessment
Cyber Security Awareness Facts And Statistics Cyber Risk AssessmentThe following slide showcases some facts and figures to generate awareness about cyber-crimes. It includes elements such as hike in ransomware attacks, more employees are expected to be target of malware attacks, increasing cost of data breaches etc. Increase audience engagement and knowledge by dispensing information using Cyber Security Awareness Facts And Statistics Cyber Risk Assessment This template helps you present information on four stages. You can also present information on Malware Attacks, Company, Social Engineering using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Plan Implementation Timeline Cyber Risk Assessment
Cyber Security Plan Implementation Timeline Cyber Risk AssessmentThe following slide presents the cyber security program execution timeline to organize tasks and ensure timely execution. It includes activities such as updating systems and passwords, performing penetration test, checking disaster recovery system, conducting training etc. Introducing Cyber Security Plan Implementation Timeline Cyber Risk Assessment to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Systems And Passwords, Cyber Security Plan, Implementation Timeline using this template. Grab it now to reap its full benefits.
-
 Impact Of Cyber Security Policies And Practices Cyber Risk Assessment
Impact Of Cyber Security Policies And Practices Cyber Risk AssessmentThe following slide focuses on drafting cyber security policies to manage data control and breach. It mainly includes elements such as impact of existing cyber safety policies, mitigation actions, Introducing Impact Of Cyber Security Policies And Practices Cyber Risk Assessment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security Guidelines, Management, Privacy Policies using this template. Grab it now to reap its full benefits.
-
 Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity Matrix
Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity MatrixThe following slide depicts cyber security risk assessment grid to prioritize and eliminate occurrence of threats. It includes elements such as moderate, severe, minor, negligible, rate, possible, likely, unlikely etc. Introducing Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity Matrix to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Very Severe, Severe, Moderate using this template. Grab it now to reap its full benefits.
-
 Mitigation Strategies For Chatbot Security Risks
Mitigation Strategies For Chatbot Security RisksThis slide shows information regarding various types of security risks associated with chatbots which are threats and vulnerabilities such as ransomware, malware, unencrypted communications, back-door access by hackers, etc. It also includes mitigation strategies to overcome these issues. Introducing our premium set of slides with Mitigation Strategies For Chatbot Security Risks. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Mitigation Strategies, Biometric Authentication, Two Factor Authentication. So download instantly and tailor it with your information.



