Powerpoint Templates and Google slides for Security Risks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Security risk analysis security laboratory data patient homes
Security risk analysis security laboratory data patient homesPresenting this set of slides with name - Security Risk Analysis Security Laboratory Data Patient Homes. This is an editable four stages graphic that deals with topics like Security Risk Analysis, Security Laboratory Data, Patient Homes to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security risks virtualization ppt powerpoint presentation icon backgrounds cpb
Security risks virtualization ppt powerpoint presentation icon backgrounds cpbPresenting this set of slides with name Security Risks Virtualization Ppt Powerpoint Presentation Icon Backgrounds Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Security Risks Virtualization to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security risk management determine threat management team
Cyber security risk management determine threat management teamThe threat management team generally comprise of senior management personnel that have authority and resources to accelerate the companys internal incident response. They will be responsible in managing human impacts both employees and community, company reputation, share values, and corporate assets. Introducing Cyber Security Risk Management Determine Threat Management Team to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Management Head, Security Manager, Crisis Management Advisor, Medical Advisor, using this template. Grab it now to reap its full benefits.
-
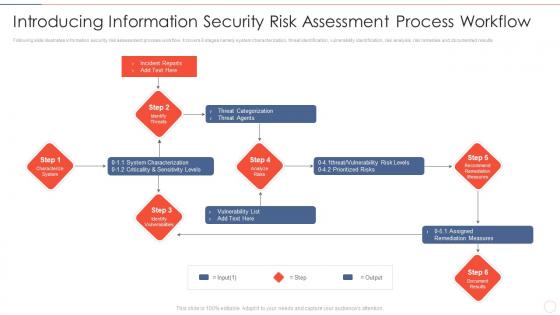 Effective information security introducing information security risk assessment process
Effective information security introducing information security risk assessment processFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results Increase audience engagement and knowledge by dispensing information using Effective Information Security Introducing Information Security Risk Assessment Process. This template helps you present information on six stages. You can also present information on Incident Reports, Threat Categorization, Vulnerability List, Assigned Remediation Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risk Management Framework For Information Security Introducing Information Security Risk
Risk Management Framework For Information Security Introducing Information Security RiskFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results. Increase audience engagement and knowledge by dispensing information using Risk Management Framework For Information Security Introducing Information Security Risk. This template helps you present information on six stages. You can also present information on Identify Threats, Incident Reports, Identify Vulnerabilities, Characterize System, Recommend Remediation Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
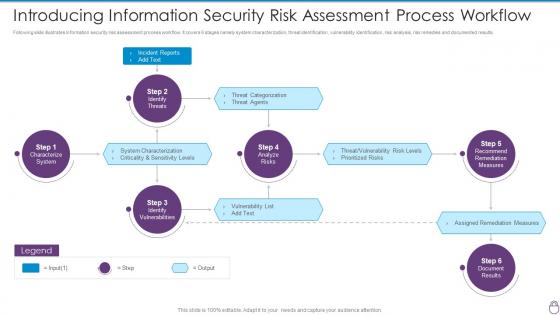 Cybersecurity Risk Management Framework Introducing Information Security Risk Assessment
Cybersecurity Risk Management Framework Introducing Information Security Risk AssessmentFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results. Increase audience engagement and knowledge by dispensing information using Cybersecurity Risk Management Framework Introducing Information Security Risk Assessment. This template helps you present information on six stages. You can also present information on Incident Reports, Characterize System, Identify Vulnerabilities, Identify Threats, Analyze Risks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
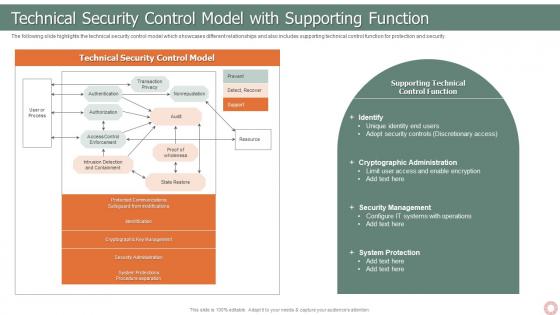 IT Risk Management Strategies Technical Security Control Model With Supporting Function
IT Risk Management Strategies Technical Security Control Model With Supporting FunctionThe following slide highlights the technical security control model which showcases different relationships and also includes supporting technical control function for protection and security. Introducing IT Risk Management Strategies Technical Security Control Model With Supporting Function to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Technical Security, Control Model, Transaction Privacy, State Restore, using this template. Grab it now to reap its full benefits.
-
 Enterprise Risk Management Technical Security Control Model With Supporting Function
Enterprise Risk Management Technical Security Control Model With Supporting FunctionThe following slide highlights the technical security control model which showcases different relationships and also includes supporting technical control function for protection and security. Introducing Enterprise Risk Management Technical Security Control Model With Supporting Function to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Identify, Cryptographic Administration, Security Management, System Protection, using this template. Grab it now to reap its full benefits.
-
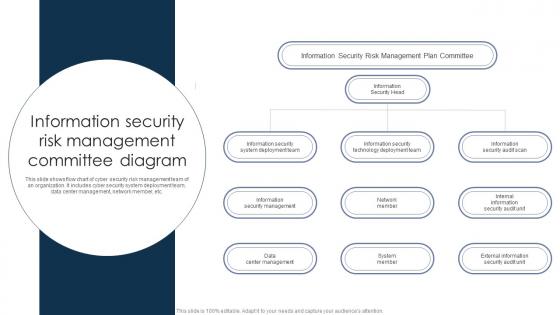 Information Security Risk Management Committee Diagram
Information Security Risk Management Committee DiagramThis slide shows flow chart of cyber security risk management team of an organization. It includes cyber security system deployment team, data center management, network member, etc. Presenting our set of slides with Information Security Risk Management Committee Diagram. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Security Head, Network Member, System Member.
-
 Prioritize Cyber Security Risks With Matrix Improving Cyber Security Risks Management
Prioritize Cyber Security Risks With Matrix Improving Cyber Security Risks ManagementThe following slide presents cyber security risks exposure grid to determine and plan mitigation actions. It includes elements such as restricting permissions, remediating constantly, postponing remediation, tracking risk escalation etc. Introducing Prioritize Cyber Security Risks With Matrix Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Restrict Permissions, Postpone Remediation, Track Risk Escalation, using this template. Grab it now to reap its full benefits.


