Powerpoint Templates and Google slides for Security Risks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Information security risk management development investment analytics framework
Information security risk management development investment analytics frameworkIf you require a professional template with great design, then this Information Security Risk Management Development Investment Analytics Framework is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using twelve slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well-structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
 Blockchain security data protection risk control incident management
Blockchain security data protection risk control incident managementEngage buyer personas and boost brand awareness by pitching yourself using this prefabricated set. This Blockchain Security Data Protection Risk Control Incident Management is a great tool to connect with your audience as it contains high-quality content and graphics. This helps in conveying your thoughts in a well-structured manner. It also helps you attain a competitive advantage because of its unique design and aesthetics. In addition to this, you can use this PPT design to portray information and educate your audience on various topics. With twelve slides, this is a great design to use for your upcoming presentations. Not only is it cost-effective but also easily pliable depending on your needs and requirements. As such color, font, or any other design component can be altered. It is also available for immediate download in different formats such as PNG, JPG, etc. So, without any further ado, download it now.
-
 Risk Management Maturity Model Information Security Data Technology Culture
Risk Management Maturity Model Information Security Data Technology CultureDeliver a credible and compelling presentation by deploying this Risk Management Maturity Model Information Security Data Technology Culture. Intensify your message with the right graphics, images, icons, etc. presented in this complete deck. This PPT template is a great starting point to convey your messages and build a good collaboration. The twenty eight slides added to this PowerPoint slideshow helps you present a thorough explanation of the topic. You can use it to study and present various kinds of information in the form of stats, figures, data charts, and many more. This Risk Management Maturity Model Information Security Data Technology Culture PPT slideshow is available for use in standard and widescreen aspects ratios. So, you can use it as per your convenience. Apart from this, it can be downloaded in PNG, JPG, and PDF formats, all completely editable and modifiable. The most profound feature of this PPT design is that it is fully compatible with Google Slides making it suitable for every industry and business domain.
-
 Computer system security assessment matrix of cyber risks ppt grid
Computer system security assessment matrix of cyber risks ppt gridThis slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web or mobile applications, online payments, employee devices. Increase audience engagement and knowledge by dispensing information using Computer System Security Assessment Matrix Of Cyber Risks Ppt Grid. This template helps you present information on one stages. You can also present information on Industrial, Data Center, Multifamily, Retail, Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer system security detail impact computer security plan can reduce the risk of data breach in organization
Computer system security detail impact computer security plan can reduce the risk of data breach in organizationThis slide represents the current status of the cyber attacks in an organization after implementing the cyber security model. Present the topic in a bit more detail with this Computer System Security Detail Impact Computer Security Plan Can Reduce The Risk Of Data Breach In Organization. Use it as a tool for discussion and navigation on System Misconfiguration, Network Intrusion, Automated Information Exfiltration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Computer system security strategies to manage cyber risks
Computer system security strategies to manage cyber risksThis slide depicts the importance of cyber risk management strategy and procedures and factors that needs to consider while establishing a risk management strategy. Introducing Computer System Security Strategies To Manage Cyber Risks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Secure, Vigilant, Resilient, Implementation, Awareness, using this template. Grab it now to reap its full benefits.
-
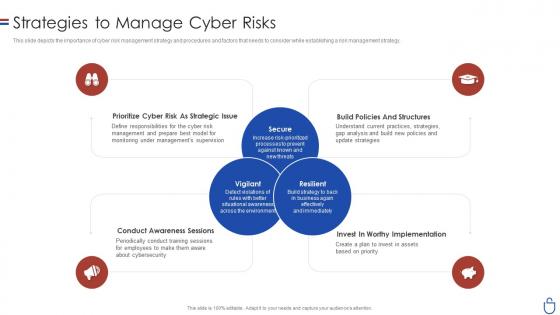 Data security it strategies to manage cyber risks ppt slides clipart images
Data security it strategies to manage cyber risks ppt slides clipart imagesThis slide depicts the importance of cyber risk management strategy and procedures and factors that needs to consider while establishing a risk management strategy. Introducing Data Security IT Strategies To Manage Cyber Risks Ppt Slides Clipart Images to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prioritize Cyber Risk As Strategic Issue, Conduct Awareness Sessions, Invest Worthy Implementation, Build Policies And Structures, using this template. Grab it now to reap its full benefits.
-
 Data security it assessment matrix of cyber risks ppt slides outline
Data security it assessment matrix of cyber risks ppt slides outlineThis slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web or mobile applications, online payments, employee devices. Present the topic in a bit more detail with this Data Security IT Assessment Matrix Of Cyber Risks Ppt Slides Outline. Use it as a tool for discussion and navigation on Systems Involved, Owner Tenant, Mobile, Web Applications, Health Care. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
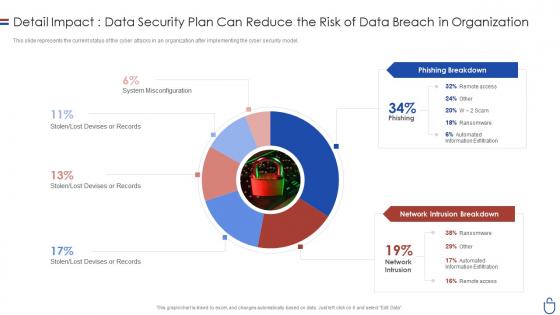 Data security it detail impactdata security plan can reduce the risk of data
Data security it detail impactdata security plan can reduce the risk of dataThis slide represents the current status of the cyber attacks in an organization after implementing the cyber security model. Deliver an outstanding presentation on the topic using this Data Security IT Detail Impactdata Security Plan Can Reduce The Risk Of Data. Dispense information and present a thorough explanation of System Misconfiguration, Lost Devises Or Records, Stolen, Lost Devises Or Records, Phishing Breakdown, Network Intrusion Breakdown using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Steps For Digital Security Risk Assessment And Evaluation
Steps For Digital Security Risk Assessment And EvaluationThis slide showcase cyber risk assessment with standard risk identification to align organizational objective. It includes context establishment, risk identification, risk assessment and risk evaluation. Introducing our premium set of slides with Steps For Digital Security Risk Assessment And Evaluation. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security, Calculate, Penetration. So download instantly and tailor it with your information.
-
 Types Security Risk Assessments Exists In Powerpoint And Google Slides Cpb
Types Security Risk Assessments Exists In Powerpoint And Google Slides CpbPresenting our Types Security Risk Assessments Exists In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Types Security Risk Assessments Exists. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Risk Management Cyber Security In Powerpoint And Google Slides Cpb
Risk Management Cyber Security In Powerpoint And Google Slides CpbPresenting our Risk Management Cyber Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Risk Management Cyber Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Data Security Risk Treatment Action Plan Icon
Data Security Risk Treatment Action Plan IconPresenting our set of slides with Data Security Risk Treatment Action Plan Icon. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Security Risk Treatment, Action Plan Icon.
-
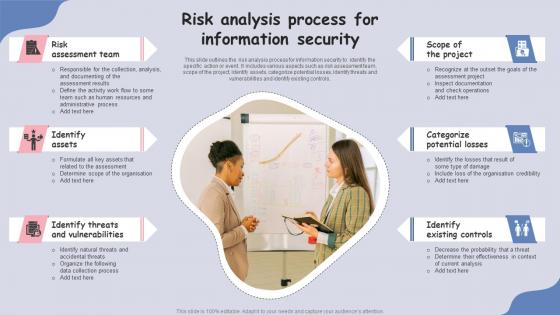 Risk Analysis Process For Information Security
Risk Analysis Process For Information SecurityThis slide outlines the risk analysis process for information security to identify the specific action or event. It includes various aspects such as risk assessment team, scope of the project, identify assets, categorize potential losses, identify threats and vulnerabilities and identify existing controls.Presenting our set of slides with Risk Analysis Process For Information Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Assessment Team, Identify Assets, Identify Threats.
-
 Risk Analysis Process In Cyber Security
Risk Analysis Process In Cyber SecurityThis slide outlines the risk analysis process for cyber security to effectively and efficiently protect their department assets. It includes key steps such as conduct risk assessment survey, identify risks, analyse risks, develop a risk management plan, implement risk management plan and monitor risks.Introducing our premium set of slides with Risk Analysis Process In Cyber Security. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Assessment Survey, Identify Risks, Analyze Risks. So download instantly and tailor it with your information.
-
 Information Security Risk Categories In Powerpoint And Google Slides Cpb
Information Security Risk Categories In Powerpoint And Google Slides CpbPresenting Information Security Risk Categories In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase Three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Information Security Risk Categories. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Compressive Planning Guide Cyber Security Risk Assessment Program Implementation Impact
Compressive Planning Guide Cyber Security Risk Assessment Program Implementation ImpactThe purpose of the following slide is to highlight the impact of impact of risk assessment on cyber crime attacks. It compares the number of security incident occurred in two consecutive months and highlight the prevailing trend in terms of going up, remaining same or going down. Present the topic in a bit more detail with this Compressive Planning Guide Cyber Security Risk Assessment Program Implementation Impact. Use it as a tool for discussion and navigation on Cyber Security, Risk Assessment Program, Attacks Frequency, Distributed Denial Of Service Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Action Plan To Combat Cyber Crimes Cyber Security Risk Assessment Program Implementation Impact
Action Plan To Combat Cyber Crimes Cyber Security Risk Assessment Program Implementation ImpactThe purpose of the following slide is to highlight the impact of impact of risk assessment on cyber crime attacks. It compares the number of security incident occurred in two consecutive months and highlight the prevailing trend in terms of going up, remaining same or going down. Present the topic in a bit more detail with this Action Plan To Combat Cyber Crimes Cyber Security Risk Assessment Program Implementation Impact. Use it as a tool for discussion and navigation on Cyber Security, Risk Assessment, Program Implementation, Attacks Frequency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Plan To Prevent Cyber Cybersecurity Risk Assessment Program For Table Of Contents
Security Plan To Prevent Cyber Cybersecurity Risk Assessment Program For Table Of ContentsIntroducing Security Plan To Prevent Cyber Cybersecurity Risk Assessment Program For Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Risk, Assessment Program, Conduct Cybersecurity, Risk Assessment, using this template. Grab it now to reap its full benefits.
-
 Security Plan To Prevent Cyber Dashboard For Tracking Cyber Attack Risk Levels
Security Plan To Prevent Cyber Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Dashboard For Tracking Cyber Attack Risk Levels. Use it as a tool for discussion and navigation on Infrastructure Controls, Preventive Controls, Detective Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Plan To Prevent Cyber Framework For Cybersecurity Risk Management
Security Plan To Prevent Cyber Framework For Cybersecurity Risk ManagementThis slide indicates the framework for cybersecurity risk management. The major sub components of model are data sources, cyber intelligence and monitoring, threat and vulnerabilities, executive board and IT governance. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Framework For Cybersecurity Risk Management. Use it as a tool for discussion and navigation on Cyber Security Communities, Information Sharing, Private Organizations, IT Governance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Plan To Prevent Cyber Key Approaches To Minimize Cyber Attacks Risks
Security Plan To Prevent Cyber Key Approaches To Minimize Cyber Attacks RisksThis slide indicates the key approaches to minimize the risk associated with cyber attacks. The approaches discussed are update and upgrade outdated software, control accounts access, introduce signed software execution policies, regularly track network intrusions and use multifactor authentication. Increase audience engagement and knowledge by dispensing information using Security Plan To Prevent Cyber Key Approaches To Minimize Cyber Attacks Risks. This template helps you present information on five stages. You can also present information on Use Multifactor Authentication, Regularly Track Network Intrusions, Control Accounts Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat Map
Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat MapThis slide shows the mapping of cyber attacks based on the likelihood of risk occurrence and its impact. It also contains details of attacks segmentation and the control actions that must be taken such as track, monitor and mitigate against such cyber attacks. Deliver an outstanding presentation on the topic using this Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat Map. Dispense information and present a thorough explanation of Cyber Attacks, Risk Occurrence, Attacks Segmentation, Monitor And Mitigate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Plan To Prevent Cyber Multistep Approach To Conduct Cybersecurity Risk Assessment
Security Plan To Prevent Cyber Multistep Approach To Conduct Cybersecurity Risk AssessmentThis slide indicates the multistep approach to conduct cybersecurity risk assessment in business organization. The major steps of process are risk identification, quantification, evaluation, mitigation and monitoring. Increase audience engagement and knowledge by dispensing information using Security Plan To Prevent Cyber Multistep Approach To Conduct Cybersecurity Risk Assessment. This template helps you present information on four stages. You can also present information on Risk Identification, Risk Mapping, Risk Evaluation, Risk Mitigation And Monitoring using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks Vulnerabilities
Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Financial Transactions, Credentials Compromised, Cloud Network, Compromised. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Plan To Prevent Cyber Security Risk Assessment Program Implementation Impact
Security Plan To Prevent Cyber Security Risk Assessment Program Implementation ImpactThe purpose of the following slide is to highlight the impact of impact of risk assessment on cyber crime attacks. It compares the number of security incident occurred in two consecutive months and highlight the prevailing trend in terms of going up, remaining same or going down. Deliver an outstanding presentation on the topic using this Security Plan To Prevent Cyber Security Risk Assessment Program Implementation Impact. Dispense information and present a thorough explanation of Cyber Security, Risk Assessment, Program Implementation, Attacks Frequency using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Storage Area Network San Storage Area Network Security Risks And Solutions
Storage Area Network San Storage Area Network Security Risks And SolutionsThis slide represents the SAN security challenges and solutions. The purpose of this slide is to showcase the various risks of SAN storage and how to overcome those challenges. These challenges include lateral movement attacks, physical threats to data and network configuration and protocol vulnerabilities. Present The Topic In A Bit More Detail With This Storage Area Network San Storage Area Network Security Risks And Solutions. Use It As A Tool For Discussion And Navigation On Solutions, Configuration, Vulnerabilities. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
 Analyse Cyber Security With KPI Dashboard Improving Cyber Security Risks Management
Analyse Cyber Security With KPI Dashboard Improving Cyber Security Risks ManagementThe following slide showcases the cyber security vulnerability overview to better plan actions. It includes elements such as domains, subdomains, discovered assets, schedule assets, , issues found etc. Present the topic in a bit more detail with this Analyse Cyber Security With KPI Dashboard Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Entry Point Breakdown, Scheduled Assets, Discovered Assets. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Dashboard Of Network Security For Identifying Risks
Dashboard Of Network Security For Identifying RisksThis slide showcase dashboard of network security. The main purpose of this slide is for identifying risks that can damage security of network. This includes different types of theft, Malware, authentication etc. Introducing our Dashboard Of Network Security For Identifying Risks set of slides. The topics discussed in these slides are Authentication, Theft Rate. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Credit Risk Transfer Securities In Powerpoint And Google Slides Cpb
Credit Risk Transfer Securities In Powerpoint And Google Slides CpbPresenting our Credit Risk Transfer Securities In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Credit Risk Transfer Securities. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Understanding Security Risk Related With Dark Data Dark Data And Its Utilization
Understanding Security Risk Related With Dark Data Dark Data And Its UtilizationThis slide focuses on the security risks associated with dark data. Some of the risks associated with dark data include vulnerability to hacking, negative impact on the business, and an increased workload for IT teams, etc. Introducing Understanding Security Risk Related With Dark Data Dark Data And Its Utilization to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability To Hacking, Negative Impact On Business, Increased Workload For IT Teams, using this template. Grab it now to reap its full benefits.
-
 Icon For Security Risk Management Plan
Icon For Security Risk Management PlanIntroducing our Icon For Security Risk Management Plan set of slides. The topics discussed in these slides are Icon Security, Risk Management Plan. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Matrix For Cyber Security Risk Management Plan
Matrix For Cyber Security Risk Management PlanThis slide highlights the matrix for prioritizing a cyber security risk management plan. This slide aims to help the IT business firm ensure proper practices are implemented to prevent and mitigate risks through analysis of the risk based on factors such as intensity of impact, probability of occurrence, etc.Introducing our Matrix For Cyber Security Risk Management Plan set of slides. The topics discussed in these slides are Moderate Consequences, Major Consequences, Catastrophic Consequences. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Step Wise Security Risk Management Plan
Step Wise Security Risk Management PlanThis slide depicts the step wise process for a security management plan. The purpose of this slide is to help enterprises successfully identify, assess, and mitigate risk through the use of suitable techniques and strategies. It includes steps such as risk identification, risk assessment, risk analysis, risk mitigation and management, etc.Introducing our premium set of slides with Step Wise Security Risk Management Plan. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Determine Objectives, Risk Identification, Risk Assessment. So download instantly and tailor it with your information.
-
 Open Data Security Risks In Powerpoint And Google Slides Cpb
Open Data Security Risks In Powerpoint And Google Slides CpbPresenting our Open Data Security Risks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Open Data Security Risks. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Backed Securities Risks In Powerpoint And Google Slides Cpb
Backed Securities Risks In Powerpoint And Google Slides CpbPresenting Backed Securities Risks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Backed Securities Risks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Risks Mortgage Backed Securities In Powerpoint And Google Slides Cpb
Risks Mortgage Backed Securities In Powerpoint And Google Slides CpbPresenting our Risks Mortgage Backed Securities In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Risks Mortgage Backed Securities This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Top Security Risks In Powerpoint And Google Slides Cpb
Top Security Risks In Powerpoint And Google Slides CpbPresenting our Top Security Risks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Top Security Risks This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Risks Challenges In Powerpoint And Google Slides Cpb
Cyber Security Risks Challenges In Powerpoint And Google Slides CpbPresenting our Cyber Security Risks Challenges In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cyber Security Risks Challenges. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Risk Transfer Cyber Security In Powerpoint And Google Slides Cpb
Risk Transfer Cyber Security In Powerpoint And Google Slides CpbPresenting Risk Transfer Cyber Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase two stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Risk Transfer Cyber Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber Security Risk Assessment And Technology Deployment Plan To Improve Organizations
Cyber Security Risk Assessment And Technology Deployment Plan To Improve OrganizationsThis slide represents the assessment of vulnerability and consequences of the cyber security incidents on the operations of the company. It includes details related to threat, vulnerability, consequences, risk and solution Deliver an outstanding presentation on the topic using this Cyber Security Risk Assessment And Technology Deployment Plan To Improve Organizations. Dispense information and present a thorough explanation of Consequences, Vulnerability, Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Risk Management Company In Powerpoint And Google Slides Cpb
Cyber Security Risk Management Company In Powerpoint And Google Slides CpbPresenting Cyber Security Risk Management Company In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Risk Management Company. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber Security Risk Management Jobs In Powerpoint And Google Slides Cpb
Cyber Security Risk Management Jobs In Powerpoint And Google Slides CpbPresenting our Cyber Security Risk Management Jobs In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cyber Security Risk Management Jobs This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security Risk Outsourcing In Powerpoint And Google Slides Cpb
Security Risk Outsourcing In Powerpoint And Google Slides CpbPresenting Security Risk Outsourcing In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Risk Outsourcing. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cloud Access Security Broker CASB V2 Emerging Cloud Security Risks And Threats
Cloud Access Security Broker CASB V2 Emerging Cloud Security Risks And ThreatsThis slide represents the emerging cloud security risks, and threats organizations can encounter. The purpose of this slide is to highlight the various threats that CASB deployment can help overcome, including VPNs, system misconfiguration, non-zero security permissions, and so on. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Emerging Cloud Security Risks And Threats. Dispense information and present a thorough explanation of System Misconfigurations, Continuous Integration And Development, Supply Chain Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Kpi Dashboard To Monitor Security Compliance Risk
Kpi Dashboard To Monitor Security Compliance RiskThis slide shows security compliance checklists KPI dashboard to track and analyze risk related to security and to mitigate it efficiently. It further includes details such as top offenders, violation trends etc. Presenting our well structured Kpi Dashboard To Monitor Security Compliance Risk. The topics discussed in this slide are Violation Trends, Selected Period.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Security Compliance Audits For Risk Assessment
Security Compliance Audits For Risk AssessmentThis slide shows risk and assessment audits of security compliance which helps to make penetration tests and vulnerability assessments. It further includes requirements such as performing regular risk assessments, carrying out audits and establishing remedition plan etc. Introducing our premium set of slides with Security Compliance Audits For Risk Assessment. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Performing Regular, Carrying Out Internal. So download instantly and tailor it with your information.
-
 Quarterly Loss Incurred Due To Blockchain Frauds Hands On Blockchain Security Risk BCT SS V
Quarterly Loss Incurred Due To Blockchain Frauds Hands On Blockchain Security Risk BCT SS VThe following slide depicts the amount of loss incurred due to blockchain frauds and scams to securely encrypt financial transactions. It includes elements such as loss amount, number of incidents along with key insights, etc. Present the topic in a bit more detail with this Quarterly Loss Incurred Due To Blockchain Frauds Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Quarterly Loss Incurred Due. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Top Ten Cryptocurrency Thefts Incidents By Amount Hands On Blockchain Security Risk BCT SS V
Top Ten Cryptocurrency Thefts Incidents By Amount Hands On Blockchain Security Risk BCT SS VThe following slide represents the number of cryptocurrencies theft incidents by total amount to prevent attackers from unauthorized access. It includes elements such as Ronin, poly network, wormhole, BITMART, Venus, cream finance, along with key insights, etc. Present the topic in a bit more detail with this Top Ten Cryptocurrency Thefts Incidents By Amount Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Top Ten Cryptocurrency, Thefts Incidents By Amount. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Total Cryptocurrency Stolen By Victim Type Hands On Blockchain Security Risk BCT SS V
Total Cryptocurrency Stolen By Victim Type Hands On Blockchain Security Risk BCT SS VThe following slide depicts the total amount of cryptocurrencies stolen. It includes elements such as centralized exchange, decentralized finance protocol, etc. Deliver an outstanding presentation on the topic using this Total Cryptocurrency Stolen By Victim Type Hands On Blockchain Security Risk BCT SS V. Dispense information and present a thorough explanation of Total Cryptocurrency, Stolen By Victim Type using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Various Types Of Honeypot Technologies In Blockchain Hands On Blockchain Security Risk BCT SS V
Various Types Of Honeypot Technologies In Blockchain Hands On Blockchain Security Risk BCT SS VThe following slide depicts some honeypot technologies to identify and reduce hacking attempts. It includes elements such as clients, malware, honeynets, database, honeypots, etc. Increase audience engagement and knowledge by dispensing information using Various Types Of Honeypot Technologies In Blockchain Hands On Blockchain Security Risk BCT SS V. This template helps you present information on two stages. You can also present information on Client Honeyspot, Malware Honeypots using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Year Over Year Blockchain Fraud Trends Hands On Blockchain Security Risk BCT SS V
Year Over Year Blockchain Fraud Trends Hands On Blockchain Security Risk BCT SS VThe following slide depicts change in blockchain frauds over years to analyze trends and minimize frauds. It includes elements such as hacks, thefts, frauds, misappropriation along with key insights, etc. Present the topic in a bit more detail with this Year Over Year Blockchain Fraud Trends Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Year Over Year, Blockchain Fraud Trends. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategic Roadmap To Implement DevSecOps Statistics Of Devops Security Risks In Organization
Strategic Roadmap To Implement DevSecOps Statistics Of Devops Security Risks In OrganizationThis slide summarizes DevOps security risks across different organizational departments, such as sales, IT department, finance, marketing, operations, etc. The outlined issues are container security, sever less security issues, cloud deployment risks etc. Deliver an outstanding presentation on the topic using this Strategic Roadmap To Implement DevSecOps Statistics Of Devops Security Risks In Organization. Dispense information and present a thorough explanation of Devops Security Risks Across, Organizational Departments, Finance, Marketing, Operations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 KPI Dashboard For Cyber Security Risk Management Evaluation
KPI Dashboard For Cyber Security Risk Management EvaluationFollowing slide represents cyber security risk management and evaluation KPI dashboard for prevention of cyberattacks. It further covers total risks, severe risks, top risks in industry cyber security, controls assess, average control gap, etc. Presenting our well structured KPI Dashboard For Cyber Security Risk Management Evaluation. The topics discussed in this slide are Identity-Based Cloud Security Threats, Remote Working Risks, Mobile Security Attacks. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 KPI Dashboard For Tracking Risk Management In IP Security
KPI Dashboard For Tracking Risk Management In IP SecurityThis slide showcases dashboard for tracking IP security. The main purpose of this template is to showcase risk and analysis of risk. This includes analysis of risk, response of risk, vulnerabilities, entities, etc. Presenting our well structured KPI Dashboard For Tracking Risk Management In IP Security. The topics discussed in this slide are KPI Dashboard, Tracking Risk, Management, IP Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
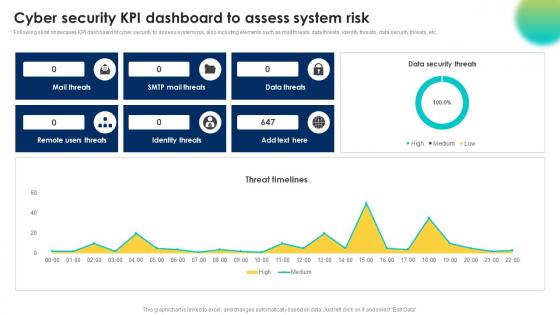 Cyber Security Kpi Dashboard To Assess System Risk
Cyber Security Kpi Dashboard To Assess System RiskFollowing slide showcases KPI dashboard of cyber security to assess system risk, also including elements such as mail threats, data threats, identity threats, data security threats, etc. Presenting our well structured Cyber Security Kpi Dashboard To Assess System Risk. The topics discussed in this slide are Identity Threats, Remote Users Threats, Data Threats. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
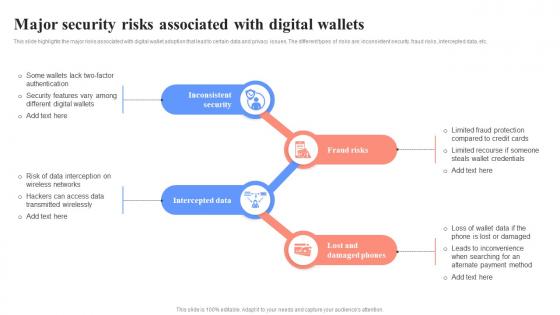 Major Security Risks Associated With Digital Wallets Unlocking Digital Wallets All You Need Fin SS
Major Security Risks Associated With Digital Wallets Unlocking Digital Wallets All You Need Fin SSThis slide highlights the major risks associated with digital wallet adoption that lead to certain data and privacy issues. The different types of risks are inconsistent security, fraud risks, intercepted data, etc. Introducing Major Security Risks Associated With Digital Wallets Unlocking Digital Wallets All You Need Fin SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Inconsistent Security, Intercepted Data, Lost And Damaged Phones, using this template. Grab it now to reap its full benefits.
-
 Statistical Representation Of Risk Level In Application Security
Statistical Representation Of Risk Level In Application SecurityPresenting our well structured Statistical Representation Of Risk Level In Application Security The topics discussed in this slide are Assessment Phase, Establish Security PoliciesThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Security Operation Center Risk Assessment Dashboard
Security Operation Center Risk Assessment DashboardThe following slide illustrates a risk assessment dashboard helps to understand the risk rating breakdown, action plan, top vulnerabilities, etc. of a business. Introducing our Security Operation Center Risk Assessment Dashboard set of slides. The topics discussed in these slides are Risk Assessment Progress, Solved, Action Plan, Risk Rating Breakdown. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Analyzing High Risk Employees And Departments IT Security Awareness Training Cybersecurity SS
Analyzing High Risk Employees And Departments IT Security Awareness Training Cybersecurity SSThis slide represents report for analyzing high risk participants and departments that requires continuous IT security awareness training. It includes details related to high risk participants etc. Present the topic in a bit more detail with this Analyzing High Risk Employees And Departments IT Security Awareness Training Cybersecurity SS. Use it as a tool for discussion and navigation on Analyzing High Risk, Employees And Departments, Marketing Team, Operations. This template is free to edit as deemed fit for your organization. Therefore download it now.



