Powerpoint Templates and Google slides for Security Process
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Automated security information collection process diagram ppt slides
Automated security information collection process diagram ppt slidesPresenting automated security information collection process diagram ppt slides. This is a automated security information collection process diagram ppt slides. This is a five stage process. The stages in this process are hazard identification, exposure assessment, report progress, fix worst first, triage and analyze result.
-
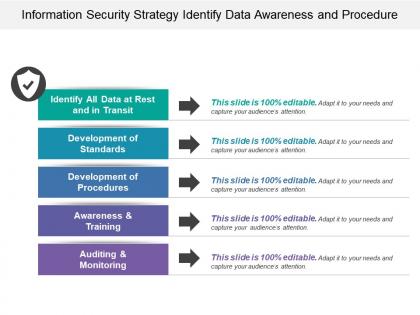 Information security strategy identify data awareness and procedure
Information security strategy identify data awareness and procedurePresenting this set of slides with name - Information Security Strategy Identify Data Awareness And Procedure. This is a five stage process. The stages in this process are Information Security Strategy, Information Security Plan, Information Protection Strategy.
-
 Management experience process control advanced training privacy security
Management experience process control advanced training privacy securityPresenting this set of slides with name - Management Experience Process Control Advanced Training Privacy Security. This is an editable four graphic that deals with topics like Management Experience, Process Control, Advanced Training, Privacy Security to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security econometric system process ppt powerpoint presentation deck cpb
Cyber security econometric system process ppt powerpoint presentation deck cpbPresenting this set of slides with name Cyber Security Econometric System Process Ppt Powerpoint Presentation Deck Cpb. This is an editable Powerpoint ten stages graphic that deals with topics like Cyber Security Econometric System Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Network security fundamentals ppt powerpoint presentation show rules cpb
Network security fundamentals ppt powerpoint presentation show rules cpbPresenting this set of slides with name Network Security Fundamentals Ppt Powerpoint Presentation Show Rules Cpb. This is an editable Powerpoint seven stages graphic that deals with topics like Network Security Fundamentals to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security log management process ppt powerpoint presentation professional graphics cpb
Security log management process ppt powerpoint presentation professional graphics cpbPresenting this set of slides with name Security Log Management Process Ppt Powerpoint Presentation Professional Graphics Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Security Log Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Standard security management process ppt powerpoint presentation pictures graphic images cpb
Standard security management process ppt powerpoint presentation pictures graphic images cpbPresenting this set of slides with name Standard Security Management Process Ppt Powerpoint Presentation Pictures Graphic Images Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Standard Security Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Process transformation compliance security risk management ppt powerpoint presentation file format ideas cpb
Process transformation compliance security risk management ppt powerpoint presentation file format ideas cpbPresenting this set of slides with name Process Transformation Compliance Security Risk Management Ppt Powerpoint Presentation File Format Ideas Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Process Transformation Compliance Security Risk Management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Computer security trends information security ppt powerpoint presentation icon rules cpb
Computer security trends information security ppt powerpoint presentation icon rules cpbPresenting this set of slides with name Computer Security Trends Information Security Ppt Powerpoint Presentation Icon Rules Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Computer Security Trends Information Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security audit procedures ppt powerpoint presentation infographics slides cpb
Cyber security audit procedures ppt powerpoint presentation infographics slides cpbPresenting this set of slides with name Cyber Security Audit Procedures Ppt Powerpoint Presentation Infographics Slides Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Cyber Security Audit Procedures to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security vulnerability scanning ppt powerpoint presentation inspiration rules cpb
Security vulnerability scanning ppt powerpoint presentation inspiration rules cpbPresenting this set of slides with name Security Vulnerability Scanning Ppt Powerpoint Presentation Inspiration Rules Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Security Vulnerability Scanning to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Incident management process cyber security ppt powerpoint presentation infographics show cpb
Incident management process cyber security ppt powerpoint presentation infographics show cpbPresenting this set of slides with name Incident Management Process Cyber Security Ppt Powerpoint Presentation Infographics Show Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Incident Management Process Cyber Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Process flow for company online database security ppt gallery
Process flow for company online database security ppt galleryPresenting this set of slides with name Process Flow For Company Online Database Security Ppt Gallery. This is a four stage process. The stages in this process are Project Kickoff, Planning, Development And Implementation, Maintain And Train. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Security processing ppt powerpoint presentation file design ideas cpb
Security processing ppt powerpoint presentation file design ideas cpbPresenting this set of slides with name Security Processing Ppt Powerpoint Presentation File Design Ideas Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Security Processing to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Computer security cyber security quotes ppt powerpoint presentation show rules cpb
Computer security cyber security quotes ppt powerpoint presentation show rules cpbPresenting our Computer Security Cyber Security Quotes Ppt Powerpoint Presentation Show Rules Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Computer Security Cyber Security Quotes This PPT slide can be easily accessed in standard screen 4.3 and widescreen 16.9 aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Wireless security protocols ppt powerpoint presentation infographic template sample cpb
Wireless security protocols ppt powerpoint presentation infographic template sample cpbPresenting our Wireless Security Protocols Ppt Powerpoint Presentation Infographic Template Sample Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Wireless Security Protocols This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Essential pillars of cloud security cloud security it ppt rules
Essential pillars of cloud security cloud security it ppt rulesThis slide shows the four essential pillars of cloud security, namely visibility and consistency, process based security, network security, and identity security.Introducing Essential Pillars Of Cloud Security Cloud Security IT Ppt Rules to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Visibility And Consistency, Process Based Security, Network Security, using this template. Grab it now to reap its full benefits.
-
 Information security process to manage firms sensitive data contd management to improve project safety it
Information security process to manage firms sensitive data contd management to improve project safety itThis slide provides information about information security process in order to manage firms sensitive data in terms of firewall audit checklist, VPN configuration, penetrating testing. Introducing Information Security Process To Manage Firms Sensitive Data Contd Management To Improve Project Safety IT to increase your presentation threshold. Encompassed with Firewall Audit Checklist, VPN Configuration, Penetrating Testing stages, this template is a great option to educate and entice your audience. Dispence information on Firewall Audit Checklist,VPN Configuration,Penetrating Testing, using this template. Grab it now to reap its full benefits.
-
 Information security process to manage firms sensitive data management to improve project safety it
Information security process to manage firms sensitive data management to improve project safety itThis slide provides information about information security process in order to manage firms sensitive data in terms of privileged password management, network security audit checklist, etc. Increase audience engagement and knowledge by dispensing information using Information Security Process To Manage Firms Sensitive Data Management To Improve Project Safety IT. This template helps you present information on three stages. You can also present information on Privileged Password Management, Daily Tasks Performed By Network Administrator, Network Security Audit Checklist using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Pitchbook for security underwriting deal share allocation process ppt file gallery
Pitchbook for security underwriting deal share allocation process ppt file galleryThe slide provides the methods of share allocation in different subscription cases oversubscription and under subscription. Key methods include lottery basis, pro rata basis, and combination of both. Introducing Pitchbook For Security Underwriting Deal Share Allocation Process Ppt File Gallery to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on In Case Undersubscription, In Case Of Oversubscription, using this template. Grab it now to reap its full benefits.
-
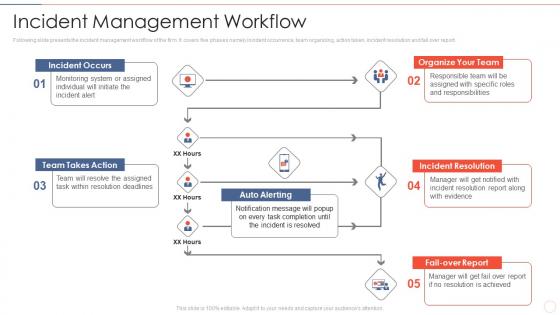 Incident management workflow effective information security risk management process
Incident management workflow effective information security risk management processFollowing slide presents the incident management workflow of the firm. It covers five phases namely incident occurrence, team organizing, action taken, incident resolution and fail over report.Introducing Incident Management Workflow Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Organize Your Team, Incident Resolution, Team Takes Action, using this template. Grab it now to reap its full benefits.
-
 Information security decision effective information security risk management process
Information security decision effective information security risk management processIncrease audience engagement and knowledge by dispensing information using Information Security Decision Effective Information Security Risk Management Process. This template helps you present information on eight stages. You can also present information on Risk Management, Implementation Responsiveness, Prioritization Weighting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Multitiered risk effective information security risk management process
Multitiered risk effective information security risk management processIntroducing Multitiered Risk Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Orgnization, Mission Or Business Processes, Information Systems, using this template. Grab it now to reap its full benefits.
-
 Workplace security policy procedures ppt powerpoint presentation outline images cpb
Workplace security policy procedures ppt powerpoint presentation outline images cpbPresenting our Workplace Security Policy Procedures Ppt Powerpoint Presentation Outline Images Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Workplace Security Policy Procedures This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber threat security planning process with risk tolerance and threats
Cyber threat security planning process with risk tolerance and threatsThis following slide illustrates the cyber security threat program planning which include steps like identify key personnel, risk tolerance strategy and developing frequency. Presenting our set of slides with Cyber Threat Security Planning Process With Risk Tolerance And Threats. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Built Risk Tolerance, Identify And Document, Establish Governance.
-
 Computer Security Technical Assessment Process
Computer Security Technical Assessment ProcessThis slide signifies the technical assessment process on company security. It steps include identify, analyse, prioritize and monitoring. Introducing our premium set of slides with Computer Security Technical Assessment Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify, Analyse, Prioritize, Monitoring. So download instantly and tailor it with your information.
-
 Automatic Technology Steps To Ensure Robotic Process Automation Security
Automatic Technology Steps To Ensure Robotic Process Automation SecurityThis slide defines steps to ensure the security of robotic process automation, and it covers guarantee accountability for bot activities, protection from abuse, frauds, logs and bot development. Introducing Automatic Technology Steps To Ensure Robotic Process Automation Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Guarantee Accountability, Protect Log Respectability, RPA Development, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Process For Cloud Services
Cyber Security Process For Cloud ServicesThe following slide highlights the cyber security process for cloud computing, cloud storage and cloud analytics storage. It depict identification, network security, data safety, application safety, monitoring and policy control to govern, protect and control the cloud services. Introducing our premium set of slides with name Cyber Security Process For Cloud Services. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network Security, Policy Control, Monitoring. So download instantly and tailor it with your information.
-
 PCI Certification For Increasing Security Of Online Transactions Improving Financial Management Process
PCI Certification For Increasing Security Of Online Transactions Improving Financial Management ProcessThis slide depicts payment card industry PCI certification for increasing security of online transactions. It provides information about authorization, 2 way authentication, one time password OTP, repository, cyber attacks, compliance, data breach, etc. Increase audience engagement and knowledge by dispensing information using PCI Certification For Increasing Security Of Online Transactions Improving Financial Management Process. This template helps you present information on three stages. You can also present information on Before PCI Integration, PCI Integration, After Integration Impact using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
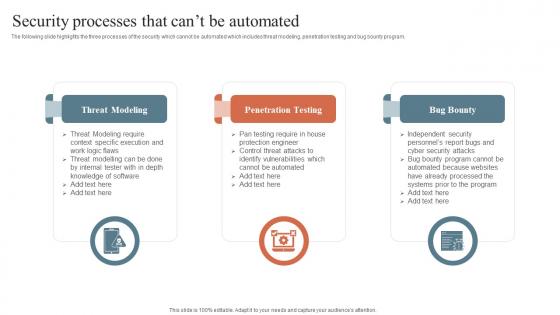 Security Processes That Cant Be Automated Security Orchestration Automation And Response Guide
Security Processes That Cant Be Automated Security Orchestration Automation And Response GuideThe following slide highlights the three processes of the security which cannot be automated which includes threat modeling, penetration testing and bug bounty program. Introducing Security Processes That Cant Be Automated Security Orchestration Automation And Response Guide to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Modeling, Penetration Testing, Bug Bounty, using this template. Grab it now to reap its full benefits.
-
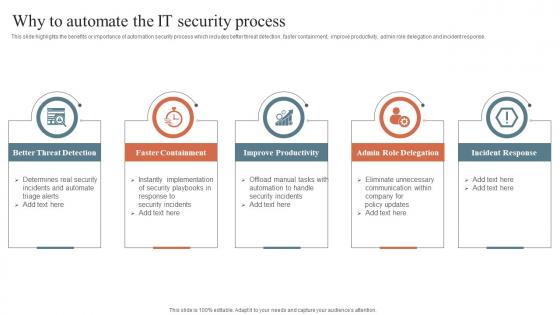 Why To Automate The It Security Process Security Orchestration Automation And Response Guide
Why To Automate The It Security Process Security Orchestration Automation And Response GuideThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Security Orchestration Automation And Response Guide. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Threat Modeling Process For Secure Data Assets
Threat Modeling Process For Secure Data AssetsThis slide shows threat modeling to protect business assets from risks. It contains two phases discovery and implementation that includes steps such as identify assets, analyze attack surface, attack vectors, analyze, prioritize and develop controls. Introducing our premium set of slides with name Threat Modeling Process For Secure Data Assets. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Hackers Path, Identified Assets, Threat Routes. So download instantly and tailor it with your information.
-
 Cyber Security Transformation Process Flow
Cyber Security Transformation Process FlowThis slide provides a cyber security process for transformation of business operations which can be used by managers for risk mitigation by resolving security issues. The steps relate to assessment of current cyber security posture, set objectives, implement strategies, train employees etc. Introducing our premium set of slides with Cyber Security Transformation Process Flow. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Set Objectives, Implement Strategies, Train Employees. So download instantly and tailor it with your information.
-
 Five Step Process To Create Cyber Security Raising Cyber Security Awareness In Organizations
Five Step Process To Create Cyber Security Raising Cyber Security Awareness In OrganizationsThe purpose of this slide is to outline a multistep process that can assist IT managers in drafting a cyber security awareness roadmap. The various steps are assessing, building, choosing, deploying, educating employees and retesting. Increase audience engagement and knowledge by dispensing information using Five Step Process To Create Cyber Security Raising Cyber Security Awareness In Organizations. This template helps you present information on six stages. You can also present information on Assess, Build, Choose, Deploy, Educate, Retest using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ensuring Security Compliance For Banking Systems With Patch Management Process
Ensuring Security Compliance For Banking Systems With Patch Management ProcessFollowing slide showcases process of patch management to ensure security of banking systems. The purpose of this slide is to outline a series of steps to align with industry regulations while maintaining the security and stability of financial operations. It includes steps such as regulatory framework, etc.Presenting our set of slides with Ensuring Security Compliance For Banking Systems With Patch Management Process. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vulnerability Management, Compliance Validation, Documentation Improvement
-
 Benefits Social Security Disability Appeal Process In Powerpoint And Google Slides Cpb
Benefits Social Security Disability Appeal Process In Powerpoint And Google Slides CpbPresenting Benefits Social Security Disability Appeal Process In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Benefits Social Security Disability Appeal Process. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cloud Access Security Broker Working Process Cloud Security Model
Cloud Access Security Broker Working Process Cloud Security ModelThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Working Process Cloud Security Model. This template helps you present information on three stages. You can also present information on Discovery, Classification, Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Security Year Rules Jobs In Powerpoint And Google Slides Cpb
Social Security Year Rules Jobs In Powerpoint And Google Slides CpbPresenting our Social Security Year Rules Jobs In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Social Security Year Rules Jobs This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security Protocols Recovery Resolution Plan In Powerpoint And Google Slides Cpb
Security Protocols Recovery Resolution Plan In Powerpoint And Google Slides CpbPresenting Security Protocols Recovery Resolution Plan In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Protocols Recovery Resolution Plan. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Security Deposit Rules In Powerpoint And Google Slides Cpb
Security Deposit Rules In Powerpoint And Google Slides CpbPresenting our Security Deposit Rules In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Security Deposit Rules. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Process To Determine Adequate Cyber Security Control
Process To Determine Adequate Cyber Security ControlThis slide represents the process to identifying adequate cyber security control for business to prevent online threats and implement necessary steps. It includes various steps such as evaluate size of the company, identify scope of IT infrastructure, etc. Presenting our set of slides with Process To Determine Adequate Cyber Security Control This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify Scope Of It Infrastructure, Evaluate Size Of Company, Investment In Cyber Security
-
 Utilization Of Triage Cyber Security Process In It
Utilization Of Triage Cyber Security Process In ItThis slide represents utilization of triage cyber security process in IT which assists to handle large number of tickets and increases help desk efficiency. It includes utilization of triage cyber security process in IT such as IT operations, email, etc Presenting our set of slides with name Utilization Of Triage Cyber Security Process In It This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Software Testing, Agile Software Development, IT Operations
-
 Cyber Security Gap Analysis Process
Cyber Security Gap Analysis ProcessThis slide covers procedure for cyber security gap analysis such as establishing security goal, assembling skilled team, and gathering documentation to identify and address vulnerabilities and shortcomings in an organizations security measures to enhance overall resilience against cyber threats. Presenting our set of slides with name Cyber Security Gap Analysis Process. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Establish Security Goal, Assemble Skilled Team, Gather Necessary Documentation.
-
 Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SS
Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SSThis slide showcases procedure that can help organization to implement mobile device management solution. Its key steps are current scenario assessment, policy development, choose solution etc. Increase audience engagement and knowledge by dispensing information using Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SS This template helps you present information on Five stages. You can also present information on Estimated Budget, Phase Duration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Framework Of Identity And Access Management Process Securing Systems With Identity
Framework Of Identity And Access Management Process Securing Systems With IdentityThis slide discusses the Identity and Access Management framework. The purpose of this slide is to highlight the procedure that includes outlining how IAM architecture components work together, define user access to resources, and so on. Increase audience engagement and knowledge by dispensing information using Framework Of Identity And Access Management Process Securing Systems With Identity This template helps you present information on Eight stages. You can also present information on Employee Movements, Security Threat Reduction, Standard Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


