Powerpoint Templates and Google slides for Security Process
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Process of analytics and security intelligence ppt powerpoint shapes
Process of analytics and security intelligence ppt powerpoint shapesPresenting process of analytics and security intelligence ppt powerpoint shapes. This is a process of analytics and security intelligence ppt powerpoint shapes. This is a four stage process. The stages in this process are security devices, database activity, application activity, mitigate and project, define and detect.
-
 Network security optimization process template powerpoint presentation
Network security optimization process template powerpoint presentationPresenting network security optimization process template powerpoint presentation. Presenting network security optimization process template powerpoint presentation. This is a network security optimization process template powerpoint presentation. This is a four stage process. The stages in this process are attack, business impact, document the threats, identify assets.
-
 Billing customer security e source control circular process with icon in centre
Billing customer security e source control circular process with icon in centrePresenting billing customer security e source control circular process with icon in centre. This is a billing customer security e source control circular process with icon in centre. This is a seven stage process. The stages in this process are billing process, billing procedure, billing cycle.
-
 Operating system memory process management security
Operating system memory process management securityPresenting this Operating System Memory Process Management Security PowerPoint presentation. Add charts and graphs for a wonderful representation of information. The PPT also supports the standard (4:3) and widescreen (16:9) aspect ratios. It is compatible with Google Slides. Convert this into popular images or document formats such as JPEG, PNG or PDF. High-quality graphics ensure that graphics quality is maintained at every stage of presentation.
-
 Hotel safety and security emergency process with 5 boxes
Hotel safety and security emergency process with 5 boxesPresenting hotel safety and security emergency process with 5 boxes. This is a hotel safety and security emergency process with 5 boxes. This is a five stage process. The stages in this process are hotel safety and security, guest house safety, lodge safety.
-
 Cloud governance define roles security policies and processes
Cloud governance define roles security policies and processesPresenting this set of slides with name - Cloud Governance Define Roles Security Policies And Processes. This is a five stage process. The stages in this process are Cloud Governance, Cloud Computing, Cloud Management.
-
 Process integration oversight security policy management corporate strategic plan
Process integration oversight security policy management corporate strategic planPresenting this set of slides with name - Process Integration Oversight Security Policy Management Corporate Strategic Plan. This is an editable three stages graphic that deals with topics like Process Integration Oversight, Security Policy Management, Corporate Strategic Plan to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Digital media management network security business process transformation cpb
Digital media management network security business process transformation cpbPresenting this set of slides with name - Digital Media Management Network Security Business Process Transformation Cpb. This is an editable five stages graphic that deals with topics like Digital Media Management, Network Security, Business Process Transformation to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Latest cyber security technology ppt powerpoint presentation gallery rules cpb
Latest cyber security technology ppt powerpoint presentation gallery rules cpbPresenting this set of slides with name Latest Cyber Security Technology Ppt Powerpoint Presentation Gallery Rules Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Latest Cyber Security Technology to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Encryption security ppt powerpoint presentation icon rules cpb
Encryption security ppt powerpoint presentation icon rules cpbPresenting this set of slides with name Encryption Security Ppt Powerpoint Presentation Icon Rules Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Encryption Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security essentials ppt powerpoint presentation model rules cpb
Cyber security essentials ppt powerpoint presentation model rules cpbPresenting this set of slides with name Cyber Security Essentials Ppt Powerpoint Presentation Model Rules Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Cyber Security Essentials to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information security management process ppt powerpoint presentation model cpb
Information security management process ppt powerpoint presentation model cpbPresenting this set of slides with name Information Security Management Process Ppt Powerpoint Presentation Model Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Information Security Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security people process technology ppt powerpoint presentation file graphics template cpb
Cyber security people process technology ppt powerpoint presentation file graphics template cpbPresenting this set of slides with name Cyber Security People Process Technology Ppt Powerpoint Presentation File Graphics Template Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Cyber Security People Process Technology to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security people process technology framework
Cyber security people process technology frameworkPresenting this set of slides with name Cyber Security People Process Technology Framework. This is a six stage process. The stages in this process are Information Risk Management, Incident Response And Forensic Investigation, Architecture, Applications And Network Security, Threat And Vulnerability Assessment, Compliance And Awareness, Security Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Process flow for cyber security service ppt powerpoint presentation files
Process flow for cyber security service ppt powerpoint presentation filesPresenting this set of slides with name Process Flow For Cyber Security Service Ppt Powerpoint Presentation Files. This is a three stage process. The stages in this process are Project Kickoff, Planning, Development And Implementation, Maintain And Train. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cyber security process with identify and react
Cyber security process with identify and reactPresenting this set of slides with name Cyber Security Process With Identify And React. This is a four stage process. The stages in this process are Identify, Protect, Detect, React. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Multistep process for continuous system security
Multistep process for continuous system securityPresenting this set of slides with name Multistep Process For Continuous System Security. This is a four stage process. The stages in this process are Predict, Prevent, Detect, Respond. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Security implementation process with strategize and plan
Security implementation process with strategize and planPresenting this set of slides with name Security Implementation Process With Strategize And Plan. This is a three stage process. The stages in this process are Assess And Learn, Strategize And Plan, Implement And Support. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Step 1 2 3 of network security process
Step 1 2 3 of network security processPresenting our set of slides with name Step 1 2 3 Of Network Security Process. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Step 1 2 3 Network, Security, Process.
-
 Application security review process ppt powerpoint presentation icon ideas cpb
Application security review process ppt powerpoint presentation icon ideas cpbPresenting our Application Security Review Process Ppt Powerpoint Presentation Icon Ideas Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Application Security Review Process This PPT slide can be easily accessed in standard screen 4.3 and widescreen 16.9 aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security incident management process ppt powerpoint presentation visual aids styles cpb
Security incident management process ppt powerpoint presentation visual aids styles cpbPresenting our Security Incident Management Process Ppt Powerpoint Presentation Visual Aids Styles Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Security Incident Management Process This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security content automation protocol ppt powerpoint presentation ideas model cpb
Security content automation protocol ppt powerpoint presentation ideas model cpbPresenting our Security Content Automation Protocol Ppt Powerpoint Presentation Ideas Model Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Security Content Automation Protocol This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Smart criteria software security ppt powerpoint presentation show rules cpb
Smart criteria software security ppt powerpoint presentation show rules cpbPresenting Smart Criteria Software Security Ppt Powerpoint Presentation Show Rules Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Smart Criteria Software Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 How does cloud security work governance cloud security it ppt rules
How does cloud security work governance cloud security it ppt rulesThis slide depicts the governance policy under the cloud security system and how users, processes, and technology are monitored.Increase audience engagement and knowledge by dispensing information using How Does Cloud Security Work Governance Cloud Security IT Ppt Rules. This template helps you present information on five stages. You can also present information on Knowledge, Owner Ship, Accessibility using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information security risk scorecard circular process ppt file background images
Information security risk scorecard circular process ppt file background imagesIncrease audience engagement and knowledge by dispensing information using Information Security Risk Scorecard Circular Process Ppt File Background Images. This template helps you present information on six stages. You can also present information on Circular Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Loss security performance ppt powerpoint presentation layouts rules cpb
Loss security performance ppt powerpoint presentation layouts rules cpbPresenting our Loss Security Performance Ppt Powerpoint Presentation Layouts Rules Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Low Investment Business Ideas. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Computer system security process of disaster recovery planning
Computer system security process of disaster recovery planningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Introducing Computer System Security Process Of Disaster Recovery Planning to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Plan Testing, Approval, Recovery Plans, Data Collection, Forming Data Recovery Plan, using this template. Grab it now to reap its full benefits.
-
 Data security it process of disaster recovery planning ppt slides download
Data security it process of disaster recovery planning ppt slides downloadThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Introducing Data Security IT Process Of Disaster Recovery Planning Ppt Slides Download to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Approval, Create Disaster, Recovery Team, Perform, Risk Analysis, Prioritize Procedures And Operations, Define Recovery Plans, using this template. Grab it now to reap its full benefits.
-
 Security guard services proposal specializing in ppt slides rules
Security guard services proposal specializing in ppt slides rulesIntroducing Security Guard Services Proposal Specializing In Ppt Slides Rules to increase your presentation threshold. Encompassed with twelve stages, this template is a great option to educate and entice your audience. Dispence information on Apartment Complexes, Construction Sites, Entertainment Facilities, Security Consulting, Investigations, Special Events, Communication Hotline, using this template. Grab it now to reap its full benefits.
-
 Electronic information security process of disaster recovery planning
Electronic information security process of disaster recovery planningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Increase audience engagement and knowledge by dispensing information using Electronic Information Security Process Of Disaster Recovery Planning. This template helps you present information on eight stages. You can also present information on Create Disaster, Recovery Team, Approval, Plan Testing, Forming Data Recovery Plan, Data Collection, Define Recovery Plans, Disaster Recovery Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social security retirement age ppt powerpoint presentation styles rules cpb
Social security retirement age ppt powerpoint presentation styles rules cpbPresenting our Social Security Retirement Age Ppt Powerpoint Presentation Styles Rules Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Three Major Steps Requirements Specification This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Ways for integrating security in application development process
Ways for integrating security in application development processIntroducing our premium set of slides with Ways For Integrating Security In Application Development Process. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Evaluation, Development Process, Applications. So download instantly and tailor it with your information.
-
 6 step process to implement data availability security
6 step process to implement data availability securityThis slide represents 6 step process to implement data availability security illustrating simplified recording, on-site maintenance and online security, training, record disposal and plan. Presenting our set of slides with 6 Step Process To Implement Data Availability Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Management, Implement, Organization.
-
 Network Security Process Of Disaster Recovery Planning
Network Security Process Of Disaster Recovery PlanningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Introducing Network Security Process Of Disaster Recovery Planning to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Operations, Processes, Assessment, Perform, using this template. Grab it now to reap its full benefits.
-
 Information Technology Security Process Of Disaster Recovery Planning
Information Technology Security Process Of Disaster Recovery PlanningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Introducing Information Technology Security Process Of Disaster Recovery Planning to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Process Of Disaster Recovery Planning, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Technical Assessment Process
Cyber Security Technical Assessment ProcessThis slide signifies the technical assessment process of cyber security. It include stages like identify, planning, execution, monitor and closure. Presenting our set of slides with Cyber Security Technical Assessment Process. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Execution, Closure, Planning, Monitor.
-
 Information Security Process Of Disaster Recovery Planning
Information Security Process Of Disaster Recovery PlanningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Increase audience engagement and knowledge by dispensing information using Information Security Process Of Disaster Recovery Planning. This template helps you present information on eight stages. You can also present information on Plan Testing, Approval, Prioritize Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Steps Of Saas Security Process
Key Steps Of Saas Security ProcessThe following slide depicts the SaaS security process to acknowledge the gap and have proactive approach. It mainly constitutes of three phases discover, monitor and protect. Presenting our set of slides with name Key Steps Of Saas Security Process. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ascertain Threats And Attacks, Encrypt Sensitive Data, Review Log Activities.
-
 Incident Management Process In Cyber Security
Incident Management Process In Cyber SecurityThis slide covers incident management process in cyber security. It involves steps such as engage team, identify incidents, assessment, investigation and documentation. Presenting our set of slides with name Incident Management Process In Cyber Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Incident Response Team, Monitoring And Evaluation, Investigation Or Resolving.
-
 Key Steps Cyber Security Incident Response Plan Process
Key Steps Cyber Security Incident Response Plan ProcessThis slide covers key steps cyber incident response plan process. It involves six stages such as preparation, detection, analysis, containment, eradication and recovery. Presenting our set of slides with name Key Steps Cyber Security Incident Response Plan Process. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Preparation, Detection, Containment, Eradication.
-
 4 Step Process To Improve Safety And Security
4 Step Process To Improve Safety And SecurityThis slide shows the four stage process to increase safety and security. It includes firewall installation, separate network for payment, passwords change and vulnerabilities test. Presenting our set of slides with 4 Step Process To Improve Safety And Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Separate Network For Payment, Passwords Change, Firewall Installation.
-
 Implementation Process Of Network Infra Security
Implementation Process Of Network Infra SecurityThe following slide showcases process to implement network infra security to ensure that underlying infrastructure remains protected. It presents information related to segmentation networks, validation of hardware, etc. Introducing Implementation Process Of Network Infra Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Segmentation, Hardware, Software, using this template. Grab it now to reap its full benefits.
-
 Reducing Downtime With Security Patch Management Process
Reducing Downtime With Security Patch Management ProcessFollowing slide showcases security patch management process for minimizing downtime. The purpose of this slide is to aid businesses in striking a balance between secure environment and smooth business operations for minimizing downtime. It includes steps such as patch testing, automated deployment, etc.Presenting our set of slides with Reducing Downtime With Security Patch Management Process. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Regular Maintenance, Performance Testing, Monitoring Alerting.
-
 Role Of Risk Assessment In Security Patch Management Process For Financial Software
Role Of Risk Assessment In Security Patch Management Process For Financial SoftwareFollowing slide highlights the importance of risk assessment in security patch management process. The purpose of this template is to help financial institutions allocate resources effectively and maintain the trust of regulatory bodies. It includes elements such as cost benefit analysis, contingency planning, etc.Introducing our premium set of slides with Role Of Risk Assessment In Security Patch Management Process For Financial Software. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Contingency Planning, Communication Transparency, Monitoring Auditing. So download instantly and tailor it with your information.
-
 Security Patch Management Process For Healthcare IT Systems
Security Patch Management Process For Healthcare IT SystemsFollowing slide showcases the healthcare industry security patch management process. The purpose of this slide is to help healthcare organizations in ensuring that their IT systems are patched safely and effectively. It includes steps such as define, identify and prioritize, etc.Presenting our set of slides with Security Patch Management Process For Healthcare IT Systems. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Roles Responsibilities, Ensure Introduced, Deployment Depends.
-
 Unique Security Patch Management Process For Online Retailers
Unique Security Patch Management Process For Online RetailersThis slide highlights the e commerce business security patch management process. The purpose of this slide is to help businesses in ensuring a smooth e commerce experience while maintaining industry standards. It includes steps such as regulatory focus, risk assessment, etc.Introducing our premium set of slides with Unique Security Patch Management Process For Online Retailers. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Automated Deployment, Effective Communication, Thorough Testing. So download instantly and tailor it with your information.
-
 Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process
Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management ProcessThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Increase audience engagement and knowledge by dispensing information using Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process. This template helps you present information on five stages. You can also present information on Malware Infection, Systems With Passwords, Employees Feels, Allow Official Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Global Cyber Security Trend Analysis Implementing Cyber Risk Management Process
Global Cyber Security Trend Analysis Implementing Cyber Risk Management ProcessThe following slide depicts the key statistics about cyber security trends to project future performance. It mainly includes elements such as increase in ransomware attacks, average data breach costs, approximate number of businesses prone to cyber-attacks etc. Introducing Global Cyber Security Trend Analysis Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Businesses Targeted, Ransomware Attack, Cyber Attacks, using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Process Phases For Effective Authentication Implementation
Application Security Implementation Plan Process Phases For Effective Authentication ImplementationThis slide showcases the steps for deploying effective authentication which include defining requirements, selecting authentication method, etc. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Process Phases For Effective Authentication Implementation. This template helps you present information on seven stages. You can also present information on Implement Login Mechanism, Choose Authentication Method, Secure Storage Of Credentials using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint Security Implementation Process Of Endpoint Security Solutions
Endpoint Security Implementation Process Of Endpoint Security SolutionsThis slide highlights the process stages of endpoint security which include information gathering, choosing security solutions, etc. Increase audience engagement and knowledge by dispensing information using Endpoint Security Implementation Process Of Endpoint Security Solutions. This template helps you present information on three stages. You can also present information on Gather Information, Deploy Selected Solutions, Select Security Solutions, Endpoint Security Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
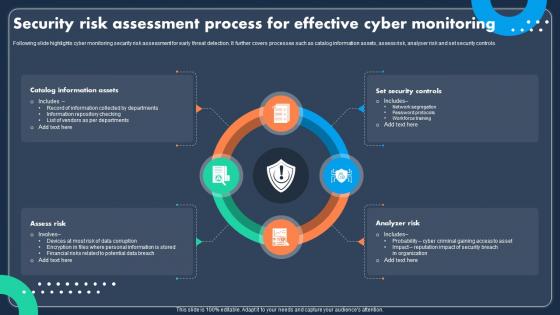 Security Risk Assessment Process For Effective Cyber Monitoring
Security Risk Assessment Process For Effective Cyber MonitoringFollowing slide highlights cyber monitoring security risk assessment for early threat detection. It further covers processes such as catalog information assets, assess risk, analyser risk and set security controls. Introducing our premium set of slides with Security Risk Assessment Process For Effective Cyber Monitoring Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Assets, Security Controls, Analyzer Risk. So download instantly and tailor it with your information.
-
 Step By Step Process Of E Commerce Security
Step By Step Process Of E Commerce SecurityThis slide shows e-commerce transactions and data integrity through comprehensive multi-layer security measures. The steps are regular back of database, set up strong passwords, use malware softwwares,etc. Presenting our set of slides with Step By Step Process Of E Commerce Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Process, Ecommerce Security, Security Measures.
-
 Cyber Security Process In Industry 4 0 Icon
Cyber Security Process In Industry 4 0 IconPresenting our set of slides with Cyber Security Process In Industry 4 0 Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Process, Industry 4 0, Icon.
-
 Streamlining Identity Management Process Within IAM Securing Systems With Identity
Streamlining Identity Management Process Within IAM Securing Systems With IdentityThis slide discusses the identity management of the Identity and Access Management process. The purpose of this slide is to explain identity management that relies on a combination of process, organizational structure, and enabling technologies. Introducing Streamlining Identity Management Process Within IAM Securing Systems With Identity to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Organization Structure, Processes, Technology using this template. Grab it now to reap its full benefits.
-
 Working Process Of Security Operations Center
Working Process Of Security Operations CenterThe below slide highlights the various steps involved in the working of security operations center that helps to safeguard sensitive data from cyber attacks. The major steps are asset discovery, behavioral monitoring, etc. Presenting our set of slides with name Working Process Of Security Operations Center. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Compliance Management, Incident Response, Alert Ranking.
-
 Software Security Patch Management Process
Software Security Patch Management ProcessThe purpose of this slide is to optimize software security through efficient patch management. It covers steps such as information retrieval, vulnerability scanning and patch testing. Presenting our set of slides with name Software Security Patch Management Process. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Retrieval, Vulnerability Scanning, Patch Testing.
-
 Process To Implement Gamified Cyber Security Training
Process To Implement Gamified Cyber Security TrainingThe purpose of this slide is to create a gamified cybersecurity training program that captures attention of users also achieves specific, measurable improvements in cybersecurity awareness and skills including steps such as identifying learning objectives, structuring activities and challenges, etc. Introducing our premium set of slides with name Process To Implement Gamified Cyber Security Training. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Learning Objectives, Structure Activities And Challenges, Cyber Security Training. So download instantly and tailor it with your information.
-
 Five Steps Process To Address Chatbot Security
Five Steps Process To Address Chatbot SecurityThis slide shows the processes organizations can use to improve or enhance the security of their chatbots. It includes stages such as assessment, minimizing data exposure, implementation, testing, and training. Introducing our premium set of slides with Five Steps Process To Address Chatbot Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Implement, Minimize Data Exposure, Test. So download instantly and tailor it with your information.
-
 Email Security Best Practices Components Of Email Account Security Process
Email Security Best Practices Components Of Email Account Security ProcessThis slide highlights the process of incorporating email security policies in an organization. The purpose of this slide is to illustrate the flow of email security implementation. The components are isolate, prevent, prepare, integrate, etc. Introducing Email Security Best Practices Components Of Email Account Security Process to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Prevent, Isolate, Respond, Prepare, Integrate, using this template. Grab it now to reap its full benefits.
-
 Email Security Best Practices Understanding The Concept Of Email Security Process
Email Security Best Practices Understanding The Concept Of Email Security ProcessThis slide demonstrates the email account security process. The purpose of this slide is to highlight the main components of securing email communication, such as email gateway, update, action, continuously reprocess, email provider, etc. Introducing Email Security Best Practices Understanding The Concept Of Email Security Process to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Email Gateway, Email Sent For Security Check, Directs Email To Email Provider, using this template. Grab it now to reap its full benefits.



