Powerpoint Templates and Google slides for Security Process
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Seven staged circular process network security planning ppt slides
Seven staged circular process network security planning ppt slidesVisually stunning PowerPoint Presentation slides. Clearly describes the various security strategies which could be beneficial to cope up with the risks. Offers Wide screen view for more clarity and better vision. Compatible with Google Framework. Being spacious enough to Include Description of Security groups and other vital information. Easily amendable PPT patterns.The stages in this process are security.
-
 Operating system memory process management security
Operating system memory process management securityPresenting this Operating System Memory Process Management Security PowerPoint presentation. Add charts and graphs for a wonderful representation of information. The PPT also supports the standard (4:3) and widescreen (16:9) aspect ratios. It is compatible with Google Slides. Convert this into popular images or document formats such as JPEG, PNG or PDF. High-quality graphics ensure that graphics quality is maintained at every stage of presentation.
-
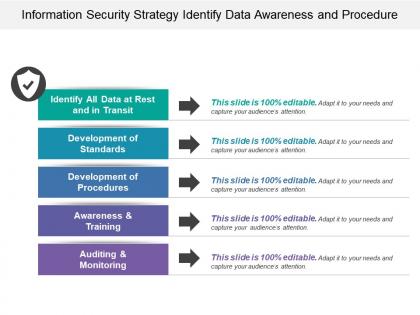 Information security strategy identify data awareness and procedure
Information security strategy identify data awareness and procedurePresenting this set of slides with name - Information Security Strategy Identify Data Awareness And Procedure. This is a five stage process. The stages in this process are Information Security Strategy, Information Security Plan, Information Protection Strategy.
-
 Business process automation standardise security collaboration consistency
Business process automation standardise security collaboration consistencyPresenting this set of slides with name - Business Process Automation Standardise Security Collaboration Consistency. This is a eight stage process. The stages in this process are Business Process Automation, Robotic Process Automation, Software Development.
-
 Cloud governance define roles security policies and processes
Cloud governance define roles security policies and processesPresenting this set of slides with name - Cloud Governance Define Roles Security Policies And Processes. This is a five stage process. The stages in this process are Cloud Governance, Cloud Computing, Cloud Management.
-
 Patch management process steps to secure business
Patch management process steps to secure businessPresenting this set of slides with name Patch Management Process Steps To Secure Business. This is a eight stage process. The stages in this process are Build An Inventory Of All It Assets, Categorize By Risk And Priority, Monitor And Evaluate Patch Updates, Create Backups, Implement Configuration Management, Implement Configuration Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Investment process security analysis ppt powerpoint presentation icon background images cpb
Investment process security analysis ppt powerpoint presentation icon background images cpbPresenting this set of slides with name Investment Process Security Analysis Ppt Powerpoint Presentation Icon Background Images Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Investment Process Security Analysis to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information security management process ppt powerpoint presentation model cpb
Information security management process ppt powerpoint presentation model cpbPresenting this set of slides with name Information Security Management Process Ppt Powerpoint Presentation Model Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Information Security Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Analysts discussing cyber security protocols against crime
Analysts discussing cyber security protocols against crimePresenting this set of slides with name Analysts Discussing Cyber Security Protocols Against Crime. This is a three stage process. The stages in this process are Analysts Discussing Cyber Security Protocols Against Crime. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Weakness icon for business process security
Weakness icon for business process securityPresenting this set of slides with name Weakness Icon For Business Process Security. This is a one stage process. The stages in this process are Weakness Icon For Business Process Security. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Risk migration process for enterprise information security management
Risk migration process for enterprise information security managementIntroducing our premium set of slides with Risk Migration Process For Enterprise Information Security Management. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk Migration, Process Enterprise, Information Security, Management. So download instantly and tailor it with your information.
-
 Process of disaster recovery planning cyber security it ppt powerpoint presentation styles
Process of disaster recovery planning cyber security it ppt powerpoint presentation stylesThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Introducing Process Of Disaster Recovery Planning Cyber Security IT Ppt Powerpoint Presentation Styles to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Approval, Plan Testing, Data Collection, Recovery Plans, Perform Risk Analysis, using this template. Grab it now to reap its full benefits.
-
 6 Stage Process For Implementation Of Risk Management In Cyber Security Project
6 Stage Process For Implementation Of Risk Management In Cyber Security ProjectThis This slide signifies the six step process for successful implementation of risk assessment in cyber security project. It covers information about stages like identify, analyse, evaluate, prioritize, treat and monitor. Presenting our set of slides with name 6 Stage Process For Implementation Of Risk Management In Cyber Security Project. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Analyse, Evaluate, Prioritize, Treat.
-
 Security Strategic Planning Process For Cps Collective Intelligence Systems
Security Strategic Planning Process For Cps Collective Intelligence SystemsThis slide represents the security strategic planning process for CPS, including business strategy, technology roadmap, vision statement environment trends, current state assessment, and so on. Increase audience engagement and knowledge by dispensing information using Security Strategic Planning Process For Cps Collective Intelligence Systems. This template helps you present information on one stages. You can also present information on Business Strategy, Environmental Trends, Gap Analysis, Prioritization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Securing Food Safety In Online Futuristic Food Delivery Trends To Transform Processes
Securing Food Safety In Online Futuristic Food Delivery Trends To Transform ProcessesThis slide covers futuristic food delivery trends to enhance processes such as integrating delivery robots, robotic chefs and stacked deliveries. Introducing Securing Food Safety In Online Futuristic Food Delivery Trends To Transform Processes to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Food Delivery Robots, Robotic Chefs, Stacked Deliveries, using this template. Grab it now to reap its full benefits.
-
 Process Phases Of Web Security In CS
Process Phases Of Web Security In CSIntroducing Process Phases Of Web Security In CS to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Process Phases, Web Security In Cs, using this template. Grab it now to reap its full benefits.
-
 Endpoint Security Process With Key Stages Building Next Generation Endpoint Security Cybersecurity SS
Endpoint Security Process With Key Stages Building Next Generation Endpoint Security Cybersecurity SSIntroducing Endpoint Security Process With Key Stages Building Next Generation Endpoint Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Gather Information, Choose Security Solutions, Implement Chosen Solutions, using this template. Grab it now to reap its full benefits.
-
 Key Network Security Policies And Procedures
Key Network Security Policies And ProceduresThis slide demonstrates network security policies including access control, device control, account management, network usage and remote access policy. Presenting our set of slides with name Key Network Security Policies And Procedures. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Access Control Policy, Device Control Policy, Account Management Policy.


