Powerpoint Templates and Google slides for Security Plan
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Enabling data security risk management action plan key initiatives for project safety it
Enabling data security risk management action plan key initiatives for project safety itThis slide provide details about data security risk management action plan which will help in keeping the track of potential risks that are existing and what are their level, what are the resources required to handle them. Deliver an outstanding presentation on the topic using this NAMEEEE. Dispense information and present a thorough explanation of Required Resources, Risk, Communication, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ways to set up an advanced cybersecurity monitoring plan estimated security monitoring key performance
Ways to set up an advanced cybersecurity monitoring plan estimated security monitoring key performanceThis slide shows the estimated Cyber Security Monitoring Key Performance Indicators of the company after implementing an advanced security monitoring plan, adopting security monitoring best practices and implementing Cybersecurity Monitoring Tool Cain and Abel. Deliver an outstanding presentation on the topic using this Ways To Set Up An Advanced Cybersecurity Monitoring Plan Estimated Security Monitoring Key Performance. Dispense information and present a thorough explanation of Security Monitoring KPIs, Costs Per Security Incident, Security Monitoring Incidents Status using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ways to set up an advanced cybersecurity monitoring plan major reasons for poor security monitoring
Ways to set up an advanced cybersecurity monitoring plan major reasons for poor security monitoringThis slide shows some of the major reasons for poor security monitoring in the company along with tips in order to resolve the issue. Present the topic in a bit more detail with this Ways To Set Up An Advanced Cybersecurity Monitoring Plan Major Reasons For Poor Security Monitoring. Use it as a tool for discussion and navigation on Reasons Poor Security Monitoring, Reason Description, Improper Security Maintenance, Effects Ransomware, Evolving Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ways to set up an advanced cybersecurity monitoring plan measures and ways to mitigate security
Ways to set up an advanced cybersecurity monitoring plan measures and ways to mitigate securityThis slide provides information about the ways and measures through which the company and security monitoring managers can overcome the problems and issues related to Security Monitoring. Deliver an outstanding presentation on the topic using this Ways To Set Up An Advanced Cybersecurity Monitoring Plan Measures And Ways To Mitigate Security. Dispense information and present a thorough explanation of Malware Attacks, Pnishing Attacks, Lot Centric Breaches, Employee Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ways to set up an advanced cybersecurity monitoring plan ways through which security data
Ways to set up an advanced cybersecurity monitoring plan ways through which security dataThis slide provides information about some of the major ways through which security data can be compromised which could have a negative impact on security monitoring along with some measures to deal with them. Present the topic in a bit more detail with this Ways To Set Up An Advanced Cybersecurity Monitoring Plan Ways Through Which Security Data. Use it as a tool for discussion and navigation on Attack Description, Ways To Mitigate Attack, External Attacks, Insider Attacks, Supply Chain Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Managing electronic information security 30 days plan
Managing electronic information security 30 days planThis slide depicts how the cyber security model will work in the first 30 days and the tasks the organization should focus on. Present the topic in a bit more detail with this Managing Electronic Information Security 30 Days Plan. Use it as a tool for discussion and navigation on Phishing Awareness, Phishing Reporting, Phishing Repeat Offenders, Facility Physical Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Managing electronic information security 60 days plan
Managing electronic information security 60 days planThis slide represents the plan for 60 days after implementing the cyber security model in the organization. Deliver an outstanding presentation on the topic using this Managing Electronic Information Security 60 Days Plan. Dispense information and present a thorough explanation of Time To Detect An Incident, Policy Violations, Data Loss Incidents, Infected Computers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing electronic information security 90 days plan
Managing electronic information security 90 days planThis slide depicts the 90 days plan of the cyber security model in an organization and training compliance and methods used for communication. Present the topic in a bit more detail with this Managing Electronic Information Security 90 Days Plan. Use it as a tool for discussion and navigation on Training Completion, Communication Methods, Policy Sign Off, Measured, Metric. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementing advanced analytics system at workplace contingency plan for threat handling security
Implementing advanced analytics system at workplace contingency plan for threat handling securityThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an outstanding presentation on the topic using this Implementing Advanced Analytics System At Workplace Contingency Plan For Threat Handling Security. Dispense information and present a thorough explanation of Contingency Plan For Threat Handling In Security Centre using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Implementing advanced analytics system at workplace enabling data security risk management action plan
Implementing advanced analytics system at workplace enabling data security risk management action planThe data security risk management action plan will help in keeping the track of potential risks that are existing and what are their level, what are the resources required to handle them. Deliver an outstanding presentation on the topic using this Implementing Advanced Analytics System At Workplace Enabling Data Security Risk Management Action Plan. Dispense information and present a thorough explanation of Management, Resources, Enabling using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat management action plan cyber security risk management
Threat management action plan cyber security risk managementThe threat management action plan will help in keeping the track of potential threats that are existing and what are their level, what are the resources required to handle them. The person responsible in handling the threat will keep track of the threat resolve duration and will check whether the threat is treated or not. Present the topic in a bit more detail with this Threat Management Action Plan Cyber Security Risk Management. Use it as a tool for discussion and navigation on Potential Risk, Risk Level, Action, Responsible Person, Risk Treated. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Mitigation plan for threat effective information security risk management process
Mitigation plan for threat effective information security risk management processMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode.Deliver an outstanding presentation on the topic using this Mitigation Plan For Threat Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Resources Required, Expected Resolution Time, Communication Mode using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Building organizational security strategy plan information security process to manage firms sensitive
Building organizational security strategy plan information security process to manage firms sensitiveThis slide provides information about information security process in order to manage firms sensitive data in terms of firewall audit checklist, VPN configuration, penetrating testing. Present the topic in a bit more detail with this Building Organizational Security Strategy Plan Information Security Process To Manage Firms Sensitive. Use it as a tool for discussion and navigation on Information, Process, Sensitive. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Building organizational security strategy plan security process to manage firms
Building organizational security strategy plan security process to manage firmsThis slide provides information about information security process in order to manage firms sensitive data in terms of privileged password management, network security audit checklist, etc. Deliver an outstanding presentation on the topic using this Building Organizational Security Strategy Plan Security Process To Manage Firms. Dispense information and present a thorough explanation of Information, Process, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Performance indicators to determine security building organizational security strategy plan
Performance indicators to determine security building organizational security strategy planThis slide provides information about performance indicators in order to determine security standards at workplace in terms of staff and customer satisfaction, financial and staff. Deliver an outstanding presentation on the topic using this Performance Indicators To Determine Security Building Organizational Security Strategy Plan. Dispense information and present a thorough explanation of Performance, Satisfaction, Financial using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Progressive continuous monitoring plan estimated security monitoring
Progressive continuous monitoring plan estimated security monitoringThis slide shows the estimated Cyber Security Monitoring Key Performance Indicators of the company after implementing an advanced security monitoring plan, adopting security monitoring best practices and implementing Cybersecurity Monitoring Tool Cain and Abel. Present the topic in a bit more detail with this Progressive Continuous Monitoring Plan Estimated Security Monitoring. Use it as a tool for discussion and navigation on Estimated Security Monitoring Key Performance Indicators. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Progressive continuous monitoring plan major reasons for poor security
Progressive continuous monitoring plan major reasons for poor securityThis slide shows some of the major reasons for poor security monitoring in the company along with tips in order to resolve the issue. Deliver an outstanding presentation on the topic using this Progressive Continuous Monitoring Plan Major Reasons For Poor Security. Dispense information and present a thorough explanation of Improper Security Maintenance, Evolving Software, Effects Of Ransomware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Progressive continuous monitoring plan measures and ways to mitigate security
Progressive continuous monitoring plan measures and ways to mitigate securityThis slide provides information about the ways and measures through which the company and security monitoring managers can overcome the problems and issues related to Security Monitoring. Present the topic in a bit more detail with this Progressive Continuous Monitoring Plan Measures And Ways To Mitigate Security. Use it as a tool for discussion and navigation on Ransomware, Lot Centric Breaches, Employee Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Progressive continuous monitoring plan ways through which security
Progressive continuous monitoring plan ways through which securityThis slide provides information about some of the major ways through which security data can be compromised which could have a negative impact on security monitoring along with some measures to deal with them. Present the topic in a bit more detail with this Progressive Continuous Monitoring Plan Ways Through Which Security. Use it as a tool for discussion and navigation on External Attacks, Insider Attacks, Supply Chain Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
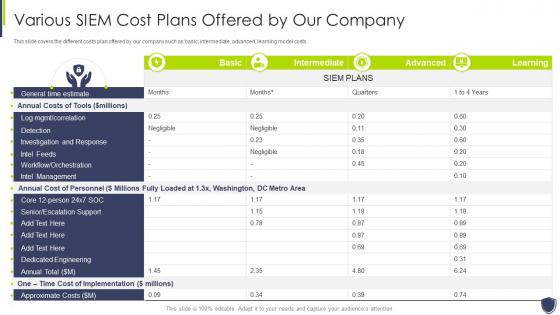 Improve it security with vulnerability management various siem cost plans offered company
Improve it security with vulnerability management various siem cost plans offered companyThis slide covers the different costs plan offered by our company such as basic, intermediate, advanced, learning model costs. Present the topic in a bit more detail with this Improve It Security With Vulnerability Management Various Siem Cost Plans Offered Company. Use it as a tool for discussion and navigation on Various SIEM Cost Plans Offered By Our Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
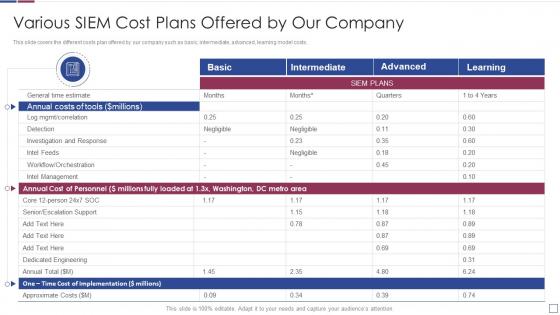 Real time analysis of security alerts various siem cost plans offered by our company
Real time analysis of security alerts various siem cost plans offered by our companyThis slide covers the different costs plan offered by our company such as basic, intermediate, advanced, learning model costs. Deliver an outstanding presentation on the topic using this Real Time Analysis Of Security Alerts Various Siem Cost Plans Offered By Our Company. Dispense information and present a thorough explanation of Various SIEM Cost Plans Offered By Our Company using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Effective information security mitigation plan for resolving encountered threat
Effective information security mitigation plan for resolving encountered threatMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode. Present the topic in a bit more detail with this Effective Information Security Mitigation Plan For Resolving Encountered Threat. Use it as a tool for discussion and navigation on Security Breach, System Failure, Risk Level, Mitigation Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Threat management action plan risk corporate security management
Threat management action plan risk corporate security managementThe threat management action plan will help in keeping the track of potential threats that are existing and what are their level, what are the resources required to handle them. The person responsible in handling the threat will keep track of the threat resolve duration and will check whether the threat is treated or not. Present the topic in a bit more detail with this Threat Management Action Plan Risk Corporate Security Management. Use it as a tool for discussion and navigation on Threat Management Action Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Essential elements of security monitoring plan ppt powerpoint presentation file ideas
Essential elements of security monitoring plan ppt powerpoint presentation file ideasThis slide provides information about some of the essential elements that must be a part of security monitoring plan in order to protect sensitive information. Deliver an outstanding presentation on the topic using this Essential Elements Of Security Monitoring Plan Ppt Powerpoint Presentation File Ideas. Dispense information and present a thorough explanation of Network Security, Critical Infrastructure, Cloud Security, Application Security, Ongoing Employee Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information and cyber security risk management plan
Information and cyber security risk management planMentioned slide showcase information security risk management plan. The template provides information about various risks such as DDoS, crypto jacking, malware and password theft and with other details like degree of risk involved, impact, strategies to be deployed. Introducing our Information And Cyber Security Risk Management Plan set of slides. The topics discussed in these slides are Degree Of Risk, Strategies, Devices. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
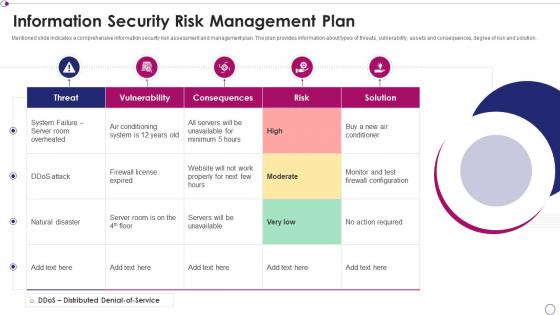 Information security risk management plan
Information security risk management planPresenting our well structured Information Security Risk Management Plan. The topics discussed in this slide are System, Risk, Required. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Network Security Managing Network Security 30 Days Plan
Network Security Managing Network Security 30 Days PlanThis slide depicts how the network security model will work in the first 30 days and the tasks the organization should focus on. Present the topic in a bit more detail with this Network Security Managing Network Security 30 Days Plan. Use it as a tool for discussion and navigation on Managing Network Security 30 Days Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Network Security Managing Network Security 60 Days Plan
Network Security Managing Network Security 60 Days PlanThis slide depicts how the network security model will work in the first 30 days and the tasks the organization should focus on. Deliver an outstanding presentation on the topic using this Network Security Managing Network Security 60 Days Plan. Dispense information and present a thorough explanation of Managing Network Security 60 Days Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Network Security Managing Network Security 60 Days Plan Methods
Network Security Managing Network Security 60 Days Plan MethodsThis slide depicts how the network security model will work in the first 30 days and the tasks the organization should focus on. Present the topic in a bit more detail with this Network Security Managing Network Security 60 Days Plan Methods. Use it as a tool for discussion and navigation on Managing Network Security 60 Days Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementation Add Roles And Enable Security Planning And Implementation Crm Software
Implementation Add Roles And Enable Security Planning And Implementation Crm SoftwareThis slide highlights the setting roles of new users and assigning roles, also highlights the enable security with field level and integration of lead generation with emails for contact management. Present the topic in a bit more detail with this Implementation Add Roles And Enable Security Planning And Implementation Crm Software. Use it as a tool for discussion and navigation on Implementation Add Roles And Enable Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Planning And Implementation Of Crm Software Securing Our Data With Crm
Planning And Implementation Of Crm Software Securing Our Data With CrmThis slide highlights the CRM data security model which includes the user based, profile based, group based, record sharing and login based security. Deliver an outstanding presentation on the topic using this Planning And Implementation Of Crm Software Securing Our Data With Crm. Dispense information and present a thorough explanation of User Role Based Security, Profile Based Security, Record Sharing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Securing Our Data With Crm Planning And Implementation Of Crm Software
Securing Our Data With Crm Planning And Implementation Of Crm SoftwareThis slide highlights the data security using CRM which incorporates IP restriction, two factor authentication, data storage, communication protection and data security. Present the topic in a bit more detail with this Securing Our Data With Crm Planning And Implementation Of Crm Software. Use it as a tool for discussion and navigation on Securing Our Data With CRM. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Technology Security 60 Days Plan
Information Technology Security 60 Days PlanThis slide represents the plan for 60 days after implementing the cyber security model in the organization. Present the topic in a bit more detail with this Information Technology Security 60 Days Plan. Use it as a tool for discussion and navigation on Managing, Information, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Technology Security Managing Information Technology Security 90 Days Plan
Information Technology Security Managing Information Technology Security 90 Days PlanThis slide depicts the 90 days plan of the cyber security model in an organization and training compliance and methods used for communication. Deliver an outstanding presentation on the topic using this Information Technology Security Managing Information Technology Security 90 Days Plan. Dispense information and present a thorough explanation of Managing, Information, Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Information Technology Security 30 Days Plan Information Technology Security
Managing Information Technology Security 30 Days Plan Information Technology SecurityThis slide depicts how the cyber security model will work in the first 30 days and the tasks the organization should focus on. Present the topic in a bit more detail with this Managing Information Technology Security 30 Days Plan Information Technology Security. Use it as a tool for discussion and navigation on Phishing Awareness, Phishing Reporting, Phishing Repeat Offenders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Siem For Security Analysis Various Siem Cost Plans Offered By Our Company
Siem For Security Analysis Various Siem Cost Plans Offered By Our CompanyThis slide covers the different costs plan offered by our company such as basic, intermediate, advanced, learning model costs. Deliver an outstanding presentation on the topic using this Siem For Security Analysis Various Siem Cost Plans Offered By Our Company. Dispense information and present a thorough explanation of Various SIEM Cost Plans Offered By Our Company using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Cybersecurity Action Plan In Case Of Breaches
Information Security Program Cybersecurity Action Plan In Case Of BreachesMentioned slide illustrates the mitigation plan of the company in case of any security breach. Sections covered are threat encountered, risk level, resources required and expected resolution time. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Action Plan In Case Of Breaches. Dispense information and present a thorough explanation of Action Plan In Case Of Breaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Cybersecurity Communication Plan For Cyber Breaches
Information Security Program Cybersecurity Communication Plan For Cyber BreachesMentioned slide portrays communication plan that company will use for effectively managing cyber breaches. Sections covered here are what to communicate, description, delivery method, frequency and responsible. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Communication Plan For Cyber Breaches. Dispense information and present a thorough explanation of Communication Plan For Cyber Breaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security 90 Days Plan Information Security
Information Security 90 Days Plan Information SecurityThis slide depicts the 90 days plan of the cyber security model in an organization and training compliance and methods used for communication. Deliver an outstanding presentation on the topic using this Information Security 90 Days Plan Information Security. Dispense information and present a thorough explanation of Managing, Information, Securityusing the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Information Security 60 Days Plan
Information Security Information Security 60 Days PlanThis slide represents the plan for 60 days after implementing the cyber security model in the organization. Deliver an outstanding presentation on the topic using this Information Security Information Security 60 Days Plan. Dispense information and present a thorough explanation of Managing, Information, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Information Security 30 Days Plan Information Security
Managing Information Security 30 Days Plan Information SecurityThis slide depicts how the cyber security model will work in the first 30 days and the tasks the organization should focus on. Deliver an outstanding presentation on the topic using this Managing Information Security 30 Days Plan Information Security. Dispense information and present a thorough explanation of Managing Information Security 30 Days Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security And Iso 27001 Communication Plan For Successful Implementation Of Isms
Information Security And Iso 27001 Communication Plan For Successful Implementation Of IsmsThis slide shows internal and external communication plan for successful implementation of ISMS. It includes sections namely reason for communication, initiator, recipient, frequency and medium. Present the topic in a bit more detail with this Information Security And Iso 27001 Communication Plan For Successful Implementation Of Isms. Use it as a tool for discussion and navigation on Successful, Implementation, Communication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security And Iso 27001 Mitigation Plan To Resolve Encountered Risk Events
Information Security And Iso 27001 Mitigation Plan To Resolve Encountered Risk EventsMentioned slide portrays mitigation plan to resolve the encountered risk events. It includes information of risk encountered, its description, threat level, mitigation plan, resources required, responsibility, resolution time and communication channel. Deliver an outstanding presentation on the topic using this Information Security And Iso 27001 Mitigation Plan To Resolve Encountered Risk Events. Dispense information and present a thorough explanation of Risk Encountered, Description, Threat Level using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Management Framework For Information Security Mitigation Plan For Resolving Encountered
Risk Management Framework For Information Security Mitigation Plan For Resolving EncounteredMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode. Present the topic in a bit more detail with this Risk Management Framework For Information Security Mitigation Plan For Resolving Encountered. Use it as a tool for discussion and navigation on Threat Encountered, Risk Level, Mitigation Plan, Resources Required. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enabling Data Security Risk Management Action Plan Building Business Analytics Architecture
Enabling Data Security Risk Management Action Plan Building Business Analytics ArchitectureThe data security risk management action plan will help in keeping the track of potential risks that are existing and what are their level, what are the resources required to handle them. Present the topic in a bit more detail with this Enabling Data Security Risk Management Action Plan Building Business Analytics Architecture. Use it as a tool for discussion and navigation on Potential Risk, Risk Level, Reason For Risk Rating, Communication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Unlocking Business Infrastructure Capabilities Enabling Data Security Risk Management Action Plan
Unlocking Business Infrastructure Capabilities Enabling Data Security Risk Management Action PlanThe data security risk management action plan will help in keeping the track of potential risks that are existing and what are their level, what are the resources required to handle them. Deliver an outstanding presentation on the topic using this Unlocking Business Infrastructure Capabilities Enabling Data Security Risk Management Action Plan. Dispense information and present a thorough explanation of Enabling Data Security Risk Management Action Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence Framework
Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence FrameworkThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations.Present the topic in a bit more detail with this Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence Framework Use it as a tool for discussion and navigation on Local Area Network, Mainframe Systems, Distributes Systems This template is free to edit as deemed fit for your organization. Therefore download it now.
-
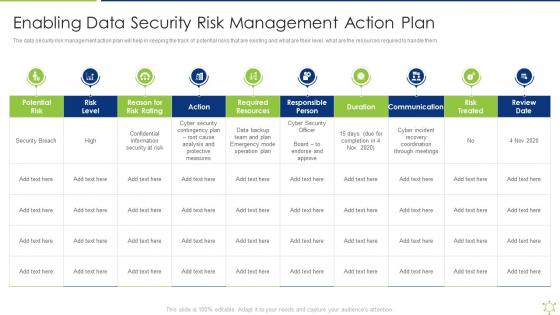 Enabling Data Security Risk Management Action Plan Enabling It Intelligence Framework
Enabling Data Security Risk Management Action Plan Enabling It Intelligence FrameworkThe data security risk management action plan will help in keeping the track of potential risks that are existing and what are their level, what are the resources required to handle them.Present the topic in a bit more detail with this Enabling Data Security Risk Management Action Plan Enabling It Intelligence Framework Use it as a tool for discussion and navigation on Required Resources, Responsible Person, Communication This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents Risk Assessment And Management Plan For Information Security
Table Of Contents Risk Assessment And Management Plan For Information SecurityDeliver an outstanding presentation on the topic using this Table Of Contents Risk Assessment And Management Plan For Information Security. Dispense information and present a thorough explanation of Assessment, Organization, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Addressing Performance Indicators To Determine Security Strategic Organizational Security Plan
Addressing Performance Indicators To Determine Security Strategic Organizational Security PlanThis slide provides information about performance indicators in order to determine security standards at workplace in terms of incidents, offender management, risk assessments. Deliver an outstanding presentation on the topic using this Addressing Performance Indicators To Determine Security Strategic Organizational Security Plan. Dispense information and present a thorough explanation of Incidents, Offender Management, Risk Assessments using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Incidents Tracking Dashboard Strategic Organizational Security Plan
Security Incidents Tracking Dashboard Strategic Organizational Security PlanThis slide portrays information regarding the dashboard that firm will track various incidents detected. These incidents will be managed in order to avoid security risks. Present the topic in a bit more detail with this Security Incidents Tracking Dashboard Strategic Organizational Security Plan. Use it as a tool for discussion and navigation on Security, Application Hardening, Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Process To Manage Firms Sensitive Data Defense Plan To Protect Firm Assets
Information Security Process To Manage Firms Sensitive Data Defense Plan To Protect Firm AssetsThis slide provides information about information security process in order to manage firms sensitive data in terms of privileged password management, network security audit checklist, etc. Present the topic in a bit more detail with this Information Security Process To Manage Firms Sensitive Data Defense Plan To Protect Firm Assets. Use it as a tool for discussion and navigation on Privileged Password Management, Network Administrator. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS V
Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding responsibilities managed by CIOs across firm in terms of task delegation to improve productivity, management of IT dept., Administer network and system deployment, etc. Present the topic in a bit more detail with this Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Responsibilities, Management, Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS V
Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding the key steps required to develop an application rationalization framework and their feasibility. The steps include determining business value, measuring application TCO, etc. Present the topic in a bit more detail with this Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Application, Rationalization, Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS V
Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS VPresent the topic in a bit more detail with this Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Strategic Business Alignment, Workforce And Cost Management, Deploy Application Rationalization . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Kpis To Track Mobile Security Management Plan Mobile Device Security Cybersecurity SS
Kpis To Track Mobile Security Management Plan Mobile Device Security Cybersecurity SSThis slide showcases metrics that can help to track the effectiveness of mobile security management plan. Various KPIs are mobile threat detection rate, incident response time etc. Deliver an outstanding presentation on the topic using this Kpis To Track Mobile Security Management Plan Mobile Device Security Cybersecurity SS Dispense information and present a thorough explanation of Phase, Key Tasks, Estimated Duration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Plan To Implement Different Mobile Biometric Techniques Mobile Device Security Cybersecurity SS
Plan To Implement Different Mobile Biometric Techniques Mobile Device Security Cybersecurity SSThis slide showcases plan that can help company to implement mobile biometric solutions. Its key components are biometric technique, team responsible, expected benefits, progress and budget allocated. Deliver an outstanding presentation on the topic using this Plan To Implement Different Mobile Biometric Techniques Mobile Device Security Cybersecurity SS Dispense information and present a thorough explanation of Policy Development, Choose Solution, Train Users using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Penetration Testing Implementation Plan Existing It Security Infrastructure Constituants
Penetration Testing Implementation Plan Existing It Security Infrastructure ConstituantsThis slide highlights the components of the current IT security infrastructure, which are prone to several security concerns. These constituents are access control, application security, firewalls, virtual private networks VPN, antivirus, etc. Deliver an outstanding presentation on the topic using this Penetration Testing Implementation Plan Existing It Security Infrastructure Constituants. Dispense information and present a thorough explanation of Access Control, Application Security, Antivirus Or Antimalware Systems, Password Auditing Tools using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Penetration Testing Implementation Plan Key Challenges Of Existing It Security
Penetration Testing Implementation Plan Key Challenges Of Existing It SecurityThis slide discusses the security issues faced by the organization due to a lack of security in infrastructure. These concerns are unauthorized access, data breaches, malware and ransomware, phishing attacks, data loss or corruption, compliance, etc. Deliver an outstanding presentation on the topic using this Penetration Testing Implementation Plan Key Challenges Of Existing It Security. Dispense information and present a thorough explanation of Unauthorized Access, Data Breaches, Malware And Ransomware, Phishing Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Investment Plan For Enhancing Network Security Implementing Strategies For Mitigating Cybersecurity SS
Investment Plan For Enhancing Network Security Implementing Strategies For Mitigating Cybersecurity SSThis slide details the costs associated with deploying network vulnerability management solutions for an enterprise. It includes expenses for implementing E2E software, IT talent acquisition costs etc.Deliver an outstanding presentation on the topic using this Investment Plan For Enhancing Network Security Implementing Strategies For Mitigating Cybersecurity SS. Dispense information and present a thorough explanation of Parameters, Forecasted Budget, Actual Costs, Variance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.




