Powerpoint Templates and Google slides for Security Plan
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
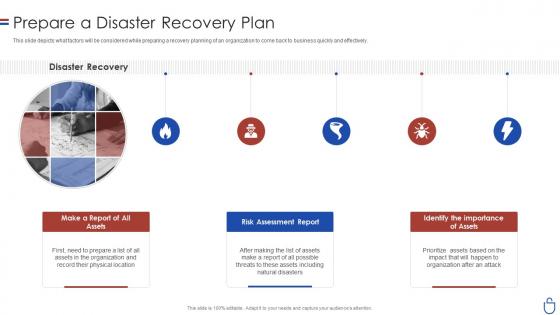
 Prepare a disaster recovery plan computer system security ppt powerpoint tipswd
Prepare a disaster recovery plan computer system security ppt powerpoint tipswdThis slide depicts what factors will be considered while preparing a recovery planning of an organization to come back to business quickly and effectively. Introducing Prepare A Disaster Recovery Plan Computer System Security Ppt Powerpoint Tipswd to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Make A Report Of All Assets, Risk Assessment Report, Identify The Importance Of Assets, using this template. Grab it now to reap its full benefits.
-
 Data security it prepare a disaster recovery plan ppt slides rules
Data security it prepare a disaster recovery plan ppt slides rulesThis slide depicts what factors will be considered while preparing a recovery planning of an organization to come back to business quickly and effectively. Introducing Data Security IT Prepare A Disaster Recovery Plan Ppt Slides Rules to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Disaster Recovery, Make Report Assets, Risk Assessment Report Assets, Identify importance, using this template. Grab it now to reap its full benefits.
-
 30 60 90 days plan for security guard services proposal ppt slides backgrounds
30 60 90 days plan for security guard services proposal ppt slides backgroundsIntroducing 30 60 90 Days Plan For Security Guard Services Proposal Ppt Slides Backgrounds to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Days Plan, Security Guard Services, using this template. Grab it now to reap its full benefits.
-
 Cyber security risk management contingency plan for cyber threat handling
Cyber security risk management contingency plan for cyber threat handlingThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Introducing Cyber Security Risk Management Contingency Plan For Cyber Threat Handling to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Contingency Solutions, Contingency Considerations, System Backups, Vendors Coordination, using this template. Grab it now to reap its full benefits.
-
 Addressing physical security at workplace building organizational security strategy plan
Addressing physical security at workplace building organizational security strategy planThis slide provides information about physical security at workplace in terms of workplace surveillance, employee monitoring, and factors to consider while implementing physical security such as industry guidelines, authority codes. Increase audience engagement and knowledge by dispensing information using Addressing Physical Security At Workplace Building Organizational Security Strategy Plan. This template helps you present information on two stages. You can also present information on Physical, Workplace, Surveillance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda for advanced security monitoring plan to remove cybersecurity threat and data infraction
Agenda for advanced security monitoring plan to remove cybersecurity threat and data infractionIncrease audience engagement and knowledge by dispensing information using Agenda For Advanced Security Monitoring Plan To Remove Cybersecurity Threat And Data Infraction. This template helps you present information on seven stages. You can also present information on Agenda using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Security Risk Treatment Action Plan Icon
Data Security Risk Treatment Action Plan IconPresenting our set of slides with Data Security Risk Treatment Action Plan Icon. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Security Risk Treatment, Action Plan Icon.
-
 Data Breach Prevention 30 60 90 Days Plan To Secure Businesses From Data Breaches
Data Breach Prevention 30 60 90 Days Plan To Secure Businesses From Data BreachesThis slide represents 30-60-90 plan to protect companies and their employees from data breach attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Increase audience engagement and knowledge by dispensing information using Data Breach Prevention 30 60 90 Days Plan To Secure Businesses From Data Breaches. This template helps you present information on three stages. You can also present information on Strengthen Access Controls, Implement Continuous Monitoring, Implement Data Encryption, Continue Employee Awareness Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Community Building Plan To Boost Conversions Security Token Offerings BCT SS
Community Building Plan To Boost Conversions Security Token Offerings BCT SSThe following slide depicts the community building program to build connections and develop trust. It includes elements such as objectives, target audience, platforms, initiatives, update about progress, encourage feedbacks, host events, etc. Introducing Community Building Plan To Boost Conversions Security Token Offerings BCT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Objectives, Target Audience, Platforms, Initiatives, using this template. Grab it now to reap its full benefits.
-
 Develop Token Distribution And Allocation Plan Security Token Offerings BCT SS
Develop Token Distribution And Allocation Plan Security Token Offerings BCT SSThe following slide depicts sample security token distribution plan to enhance community participation and engagement. It includes components such as number of tokens allocated, vesting period, utility offered, distribution timeline, etc. Increase audience engagement and knowledge by dispensing information using Develop Token Distribution And Allocation Plan Security Token Offerings BCT SS. This template helps you present information on two stages. You can also present information on Token Allocation, Vesting Period, Distribution Timeline using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Employee Security Awareness And Communication Plan Icon
Employee Security Awareness And Communication Plan IconIntroducing our premium set of slides with Employee Security Awareness And Communication Plan Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security, Employee, Communication. So download instantly and tailor it with your information.
-
 Security Awareness Training And Communication Plan Icon
Security Awareness Training And Communication Plan IconIntroducing our premium set of slides with Security Awareness Training And Communication Plan Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security, Training, Communication. So download instantly and tailor it with your information.
-
 Security Plan To Prevent Cyber Cybersecurity Risk Assessment Program For Table Of Contents
Security Plan To Prevent Cyber Cybersecurity Risk Assessment Program For Table Of ContentsIntroducing Security Plan To Prevent Cyber Cybersecurity Risk Assessment Program For Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Risk, Assessment Program, Conduct Cybersecurity, Risk Assessment, using this template. Grab it now to reap its full benefits.
-
 Security Plan To Prevent Cyber Strategic Plan To Mitigate Cyber Attacks
Security Plan To Prevent Cyber Strategic Plan To Mitigate Cyber AttacksThe slide indicates the risk mitigation plan for the multiple cyber attacks. It also includes details of cost involved and implementation time required for each mitigation approach. Increase audience engagement and knowledge by dispensing information using Security Plan To Prevent Cyber Strategic Plan To Mitigate Cyber Attacks. This template helps you present information on four stages. You can also present information on Cybersecurity Attacks, Recommended Mitigation Strategy, Strategy Implementation Time Required using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 30 60 90 Days Plan To Integrate Secure Web Network Network Security Using Secure Web Gateway
30 60 90 Days Plan To Integrate Secure Web Network Network Security Using Secure Web GatewayThis slide represents 30-60-90 plan to implement Secure Web Gateway into firm. The purpose of this slide is to illustrate the plans of the first 90 days from the start, including steps to be followed at interval of one month. Introducing 30 60 90 Days Plan To Integrate Secure Web Network Network Security Using Secure Web Gateway to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Compatible, Performance, Production, using this template. Grab it now to reap its full benefits.
-
 3 Pillars Of Successful Project Security Management Plan
3 Pillars Of Successful Project Security Management PlanThis slide highlights the 3 pillars of a successful management plan for ensuring business project security. The purpose of this slide is to help the project manager ensure the optimized running of business processes through the use of an appropriately designed and installed security plan along with its maintenance.Presenting our set of slides with 3 Pillars Of Successful Project Security Management Plan. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Comprehensive Reviewing, Industry Standards, System Schematics.
-
 Communication Plan For Cyber Security Technology Initiatives
Communication Plan For Cyber Security Technology InitiativesThis slide shows communication plan for tackling with different types of cyber attacks that can affect organization security in several ways. It include cyber attacks, initiates and owner, etc. Introducing our premium set of slides with Communication Plan For Cyber Security Technology Initiatives. Ellicudate the one stage and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ransom Ware, Denial Of Services, Malicious Insider. So download instantly and tailor it with your information.
-
 Cyber Security Data Capture Plan Icon
Cyber Security Data Capture Plan IconIntroducing our premium set of slides with Cyber Security Data Capture Plan Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data, Capture, Security. So download instantly and tailor it with your information.
-
 Information Security Plan Icon For Employees
Information Security Plan Icon For EmployeesPresenting our set of slides with Information Security Plan Icon For Employees. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Security, Plan Icon For Employees.
-
 Roadmap For Robust Information Security Plan
Roadmap For Robust Information Security PlanThis slide highlights roadmap for strategic information plan to manage threat and to avoid misuse of critical information of business. It involves building recovery plan, developing compliance plan, managing data, assessing risk and creating security team. Presenting our set of slides with Roadmap For Robust Information Security Plan. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Build Strong Recovery Plan, Assess Risk, Create Security Team.
-
 Strategic Plan To Implement Best Practices For Effective Endpoint Security Strategy SS V
Strategic Plan To Implement Best Practices For Effective Endpoint Security Strategy SS VThis slide represents best practices for effective endpoint security. It covers educating users, finding and tracking business-owned devices, and installation maintenance of operating systems. Increase audience engagement and knowledge by dispensing information using Strategic Plan To Implement Best Practices For Effective Endpoint Security Strategy SS V This template helps you present information on Three stages. You can also present information on Educate Users, Find And Track Devices using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Training And Development Plan Icon For IT Security Staff
Training And Development Plan Icon For IT Security StaffPresenting our set of slides with Training And Development Plan Icon For IT Security Staff. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Training, Development, Security.
-
 Cyber Security Risk Mitigation Strategy Action Plan Icon
Cyber Security Risk Mitigation Strategy Action Plan IconIntroducing our premium set of slides with Cyber Security Risk Mitigation Strategy Action Plan Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Mitigation, Strategy, Action. So download instantly and tailor it with your information.
-
 IT Cyber Security Strategy Action Plan Icon
IT Cyber Security Strategy Action Plan IconIntroducing our premium set of slides with IT Cyber Security Strategy Action Plan Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber, Action, Strategy. So download instantly and tailor it with your information.
-
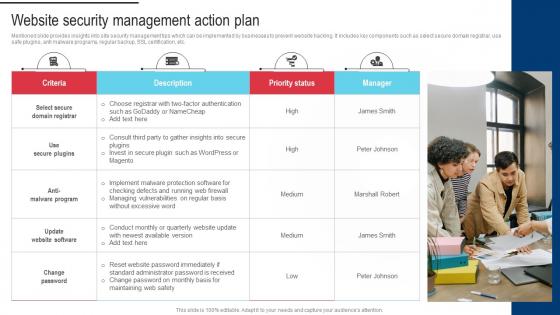 Procedure For Successful Website Security Management Action Plan
Procedure For Successful Website Security Management Action PlanMentioned slide provides insights into site security management tips which can be implemented by businesses to prevent website hacking. It includes key components such as select secure domain registrar, use safe plugins, anti malware programs, regular backup, SSL certification, etc. Introducing Procedure For Successful Website Security Management Action Plan to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Leverage Themes And Plugin, Improve Loading Time, Implement CSS using this template. Grab it now to reap its full benefits.
-
 Phishing Attacks And Strategies To Mitigate Them V2 30 60 90 Days Plan To Secure Organizations
Phishing Attacks And Strategies To Mitigate Them V2 30 60 90 Days Plan To Secure OrganizationsThis slide represents 30-60-90 plan to protect companies and their employees from phishing attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Increase audience engagement and knowledge by dispensing information using Phishing Attacks And Strategies To Mitigate Them V2 30 60 90 Days Plan To Secure Organizations. This template helps you present information on three stages. You can also present information on Phishing Attacks, Implement Continuous Monitoring, Conduct Vulnerability Assessments using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 30 60 90 Days Plan To Deploy CASB Model
Cloud Access Security Broker CASB V2 30 60 90 Days Plan To Deploy CASB ModelThis slide represents the 30-0-90 days plan to implement the Cloud Access Security Broker model in an organization. The purpose of this slide is to showcase the various steps to be taken to deploy CASB at the interval every 30 days. Introducing Cloud Access Security Broker CASB V2 30 60 90 Days Plan To Deploy CASB Model to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Scope, Current Security Architecture, Security Operations Center Functions, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure 30 60 90 Days Plan For Devsecops Implementation
Devsecops Best Practices For Secure 30 60 90 Days Plan For Devsecops ImplementationThis slide represents the 30-60-90-day plan for DevSecOps implementation. The purpose of this slide is to showcase the approaches that need to be followed as short-term, medium, and long-term goals to implement the DevSecOps. Introducing Devsecops Best Practices For Secure 30 60 90 Days Plan For Devsecops Implementation to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Devsecops Implementation, Vulnerability Scanning, Relevant Security Standards, using this template. Grab it now to reap its full benefits.
-
 Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data Breaches
Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data BreachesThis slide represents 30-60-90 plan to protect companies and their employees from data breach attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Increase audience engagement and knowledge by dispensing information using Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data Breaches. This template helps you present information on three stages. You can also present information on Strengthen Access Controls, Conduct Regular Security Audits, Provide Data Security Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Plan Implementation Timeline Cyber Risk Assessment
Cyber Security Plan Implementation Timeline Cyber Risk AssessmentThe following slide presents the cyber security program execution timeline to organize tasks and ensure timely execution. It includes activities such as updating systems and passwords, performing penetration test, checking disaster recovery system, conducting training etc. Introducing Cyber Security Plan Implementation Timeline Cyber Risk Assessment to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Systems And Passwords, Cyber Security Plan, Implementation Timeline using this template. Grab it now to reap its full benefits.
-
 Cyber Security Plan Implementation Timeline Implementing Strategies To Mitigate Cyber Security Threats
Cyber Security Plan Implementation Timeline Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide presents the cyber security program execution timeline to organize tasks and ensure timely execution. It includes activities such as updating systems and passwords, performing penetration test, checking disaster recovery system, conducting training etc. Increase audience engagement and knowledge by dispensing information using Cyber Security Plan Implementation Timeline Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on one stages. You can also present information on Update Systems And Passwords, Perform Simulated Phishing Exercise, Perform Penetration Test using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Advantages Of Early Strategic Retirement Planning To Build Secure Future Fin SS
Key Advantages Of Early Strategic Retirement Planning To Build Secure Future Fin SSIntroducing Key Advantages Of Early Strategic Retirement Planning To Build Secure Future Fin SS to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Key Advantages, Early Retirement Planning, using this template. Grab it now to reap its full benefits.
-
 Overview Of Retirement Planning Strategic Retirement Planning To Build Secure Future Fin SS
Overview Of Retirement Planning Strategic Retirement Planning To Build Secure Future Fin SSThis slide shows information which can be used to get basic understanding of retirement planning. It includes details about various elements of retirement planning such as assessing financial situation, setting retirement goals, etc. Increase audience engagement and knowledge by dispensing information using Overview Of Retirement Planning Strategic Retirement Planning To Build Secure Future Fin SS. This template helps you present information on four stages. You can also present information on Setting Retirement Goals, Retirement Planning Involves, Key Insights using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Strategic Retirement Planning To Build Secure Future Fin SS
Table Of Contents For Strategic Retirement Planning To Build Secure Future Fin SSIntroducing Table Of Contents For Strategic Retirement Planning To Build Secure Future Fin SS to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Introduction, Regulatory Framework, Planning, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents Strategic Retirement Planning To Build Secure Future Fin SS
Table Of Contents Strategic Retirement Planning To Build Secure Future Fin SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents Strategic Retirement Planning To Build Secure Future Fin SS. This template helps you present information on one stages. You can also present information on Savings Options, Types, Traditional Individual using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Timeline Representing Strategic Retirement Planning To Build Secure Future Fin SS
Timeline Representing Strategic Retirement Planning To Build Secure Future Fin SSThis slide shows roadmap which contains detailed information about history and evolution of retirement planning over time. It includes details such as first private pension plan introduction, establishment of social security system, etc. Increase audience engagement and knowledge by dispensing information using Timeline Representing Strategic Retirement Planning To Build Secure Future Fin SS. This template helps you present information on nine stages. You can also present information on Pension Plan, Contribution Plans, Older Workers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Roadmap For Robust Information Security System Plan
Roadmap For Robust Information Security System PlanThis slide highlights roadmap for a strategic information system plan to manage threats and to avoid misuse of critical information of business. Presenting our set of slides with Roadmap For Robust Information Security System Plan. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Build Strong Recovery Plan, Manage Data, Assess Risk.
-
 30 60 90 Day Plan For Cyber Security Framework Implementation
30 60 90 Day Plan For Cyber Security Framework ImplementationThis slide discusses the 30-60-90-day plan for cyber security framework implementation which include stakeholder alignment, awareness training and so on. Introducing 30 60 90 Day Plan For Cyber Security Framework Implementation to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Stakeholder Alignment, Conduct Initial Gap Analysis, Conduct Awareness Training, using this template. Grab it now to reap its full benefits.
-
 Mitigation Plan For Cyber Security Frameworks
Mitigation Plan For Cyber Security FrameworksThis slide depicts the mitigation plan for cyber security frameworks which include identify and prioritize vulnerabilities, allocate budget and skilled personnel. Increase audience engagement and knowledge by dispensing information using Mitigation Plan For Cyber Security Frameworks. This template helps you present information on five stages. You can also present information on Cyber Security Frameworks, Prioritize Vulnerabilities, Allocate Budget, Skilled Personnel using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 30 60 90 Days Plan For Security Testing Implementation
30 60 90 Days Plan For Security Testing ImplementationThis slide showcases the 30-60-90 plan for Wireless LAN controller installation. The purpose of this slide is to highlight the plan for installation such as planning and preparations, implementations and configurations, optimization, and documentation, etc. Introducing 30 60 90 Days Plan For Security Testing Implementation to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Assess And Plan, Skill And Tool Acquisition, Implementation And Integration, using this template. Grab it now to reap its full benefits.
-
 Agenda For Application Security Implementation Plan
Agenda For Application Security Implementation PlanIntroducing Agenda For Application Security Implementation Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Application Security, Implementation Plan, Authentication, Authorization, using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Five Step Roadmap To Implement Application Security
Application Security Implementation Plan Five Step Roadmap To Implement Application SecurityThis slide outlines the steps to deploy application security in organization such as defining objectives, planning, monitoring, etc. Introducing Application Security Implementation Plan Five Step Roadmap To Implement Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Monitoring And Logging, Incident Response, Education And Planning, Application Security, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Application Security Implementation Plan
Table Of Contents For Application Security Implementation PlanIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Application Security Implementation Plan. This template helps you present information on fifteen stages. You can also present information on Implementation Process, Project Roadmap, Risks And Mitigation Strategies, Project Implementation Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint Security 30 60 90 Day Plan For Endpoint Security
Endpoint Security 30 60 90 Day Plan For Endpoint SecurityThis slide depicts the 30 60 90 days plan for endpoint security which includes tasks such as assessment, policy development, etc. Increase audience engagement and knowledge by dispensing information using Endpoint Security 30 60 90 Day Plan For Endpoint Security. This template helps you present information on three stages. You can also present information on Endpoint Security, Outline Process, Implementing Approaches using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
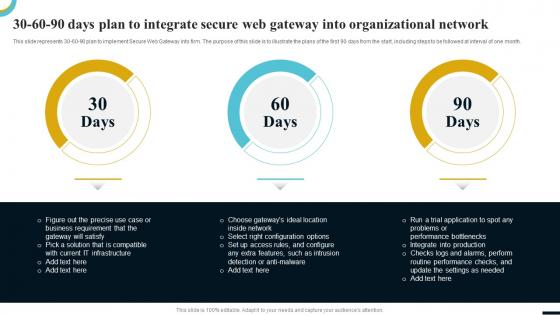 Internet Gateway Security IT 30 60 90 Days Plan To Integrate Secure Web
Internet Gateway Security IT 30 60 90 Days Plan To Integrate Secure WebThis slide represents 30-60-90 plan to implement Secure Web Gateway into firm. The purpose of this slide is to illustrate the plans of the first 90 days from the start, including steps to be followed at interval of one month. Introducing Internet Gateway Security IT 30 60 90 Days Plan To Integrate Secure Web to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Days Plan, using this template. Grab it now to reap its full benefits.
-
 Critical Teams During Security Incident Response Planning
Critical Teams During Security Incident Response PlanningThis slide highlights the critical teams required during security incident response planning. The purpose of this slide is to help ensure suitable teams and stakeholders are engaged to manage the security incident. It includes manager for incident response plan, security officer, etc. Introducing our premium set of slides with Critical Teams During Security Incident Response Planning. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Outsourced Cybersecurity, Key Decision, Analyzing Incidents. So download instantly and tailor it with your information.
-
 Implementation Checklist Plan For Security Incident
Implementation Checklist Plan For Security IncidentPresenting our set of slides with Implementation Checklist Plan For Security Incident. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation Checklist Plan, Security Incident.
-
 Security Incident Response Plan Checklist Icon
Security Incident Response Plan Checklist IconIntroducing our premium set of slides with Security Incident Response Plan Checklist Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Incident, Response Plan Checklist. So download instantly and tailor it with your information.
-
 30 60 90 Days Plan To Deploy CASB Model CASB Cloud Security
30 60 90 Days Plan To Deploy CASB Model CASB Cloud SecurityThis slide represents the 30-60-90 days plan to implement the cloud access security broker model in an organization. The purpose of this slide is to showcase the various steps to be taken to deploy CASB at the interval every 30 days. Introducing 30 60 90 Days Plan To Deploy CASB Model CASB Cloud Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Days Plan, Cloud Access Security Broker, Connect To Current Security Architecture, Security Operations Center Functions, using this template. Grab it now to reap its full benefits.
-
 Agenda Business Recovery Plan To Overcome Cyber Security Threat
Agenda Business Recovery Plan To Overcome Cyber Security ThreatIntroducing Agenda Business Recovery Plan To Overcome Cyber Security Threat to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Business, Financial, Operations, using this template. Grab it now to reap its full benefits.
-
 Business Plan To Overcome Cyber Security Threat Table Of Contents
Business Plan To Overcome Cyber Security Threat Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Business Plan To Overcome Cyber Security Threat Table Of Contents. This template helps you present information on one stages. You can also present information on Business, Communication, External Stakeholders using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Forecasted Cyber Business Performance Business Recovery Plan To Overcome Cyber Security Threat
Forecasted Cyber Business Performance Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about the impact of cyber response plan applications on business performance. It includes key areas of impact such as reputation, operations, and market value of company Increase audience engagement and knowledge by dispensing information using Forecasted Cyber Business Performance Business Recovery Plan To Overcome Cyber Security Threat. This template helps you present information on three stages. You can also present information on Operational Impact, Reputation Impact, Legal Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents Business Recovery Plan To Overcome Cyber Security Threat
Table Of Contents Business Recovery Plan To Overcome Cyber Security ThreatIntroducing Table Of Contents Business Recovery Plan To Overcome Cyber Security Threat to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Current Scenario, Potential Solutions, Business Recovery Plan , using this template. Grab it now to reap its full benefits.
-
 30 60 90 Days Plan For IAM Implementation Securing Systems With Identity
30 60 90 Days Plan For IAM Implementation Securing Systems With IdentityThis slide represents the 30-60-90-day plan for Identity and Access Management implementation. The purpose of this slide is to showcase the approaches that need to be followed as short-term, medium, and long-term goals to implement the IAM process. Introducing 30 60 90 Days Plan For IAM Implementation Securing Systems With Identity to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Implementation Plan, Policies And Procedures using this template. Grab it now to reap its full benefits.
-
 30 60 90 Days Plan For Mobile Security Implementation Mobile Security
30 60 90 Days Plan For Mobile Security Implementation Mobile SecurityThis slide discusses the 30-60-90 day plan for the implementation of mobile security which include assessment and planning, security awareness, review and update. Introducing 30 60 90 Days Plan For Mobile Security Implementation Mobile Security to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Assessment And Planning, Security Awareness, Review And Update using this template. Grab it now to reap its full benefits.
-
 30 60 90 Days Plan For Web Security Solution
30 60 90 Days Plan For Web Security SolutionThis slide depicts the activities undertaking on different days which include conducting security audit, configuring web application firewall, etc. Introducing 30 60 90 Days Plan For Web Security Solution to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Days Plan, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Project Improvement Plan For Organizational Security Improvement Plan SS
Cybersecurity Project Improvement Plan For Organizational Security Improvement Plan SSThe purpose of this slide is to present a cybersecurity project improvement plan focused on enhancing organizational security by targeted vulnerability mitigation. It includes objectives, action plan, and urgent problems, etc. Presenting our set of slides with Cybersecurity Project Improvement Plan For Organizational Security Improvement Plan SS This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Objective, Action Plan, Urgent Problems
-
 Agenda For Web Security Upgradation Plan
Agenda For Web Security Upgradation PlanIntroducing Agenda For Web Security Upgradation Plan to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Web Security, Performance Gap Analysis, Vulnerability Scanners, Service Providers, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Web Security Upgradation Plan
Table Of Contents For Web Security Upgradation PlanIntroducing Table Of Contents For Web Security Upgradation Plan to increase your presentation threshold. Encompassed with Fifteen stages, this template is a great option to educate and entice your audience. Dispence information on Key Challenges, Performance Gap Analysis, Project Summary, Web Security Technologies, using this template. Grab it now to reap its full benefits.
-
 Email Security Best Practices 30 60 90 Days Plan To Secure Email Accounts
Email Security Best Practices 30 60 90 Days Plan To Secure Email AccountsThis slide represents 30-60-90 plan to implement email security measures. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Introducing Email Security Best Practices 30 60 90 Days Plan To Secure Email Accounts to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30-60-90 Days Plan, using this template. Grab it now to reap its full benefits.



