Powerpoint Templates and Google slides for Security And Operational
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Security incidents operations dashboard with status and priority
Security incidents operations dashboard with status and priorityIntroducing our Security Incidents Operations Dashboard With Status And Priority set of slides. The topics discussed in these slides are Priority Moderate, Priority Critical, Priority Resolving. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 It security operations essential roles and responsibilities involved in secops ppt pictures portfolio
It security operations essential roles and responsibilities involved in secops ppt pictures portfolioThis slide portrays information regarding the roles and responsibilities, qualification associated to staff available at Tier1, 2, 3, and 4 level at SOC structure. Present the topic in a bit more detail with this IT Security Operations Essential Roles And Responsibilities Involved In Secops Ppt Pictures Portfolio. Use it as a tool for discussion and navigation on Security Engineers, Business, Communication Skills, Management, Training. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It security operations insider attacker method and behaviour assessment ppt graphics tutorials
It security operations insider attacker method and behaviour assessment ppt graphics tutorialsThis slide portrays information regarding the insider attacker assessment in security operations system by addressing the method they use to attack and analyzing insider behavior. Present the topic in a bit more detail with this IT Security Operations Insider Attacker Method And Behaviour Assessment Ppt Graphics Tutorials. Use it as a tool for discussion and navigation on Insider Attacker Method And Behaviour Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It security operations security and operational tasks maintenance checklist ppt example file
It security operations security and operational tasks maintenance checklist ppt example fileThis slide provides information regarding security and operational task maintenance checklist with activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Present the topic in a bit more detail with this IT Security Operations Security And Operational Tasks Maintenance Checklist Ppt Example File. Use it as a tool for discussion and navigation on System Monitoring, Executive Reporting, Planning Meeting, Preventive Maintenance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Essential roles and responsibilities involved in secops security operations integration
Essential roles and responsibilities involved in secops security operations integrationThis slide portrays information regarding the roles and responsibilities, qualification associated to staff available at Tier1, 2, 3, and 4 level at SOC structure. Present the topic in a bit more detail with this Essential Roles And Responsibilities Involved In Secops Security Operations Integration. Use it as a tool for discussion and navigation on Qualification Required, Responsibilities, Roles Assigned. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security and operational tasks maintenance checklist security operations integration ppt elements
Security and operational tasks maintenance checklist security operations integration ppt elementsThis slide provides information regarding security and operational task maintenance checklist with activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Present the topic in a bit more detail with this Security And Operational Tasks Maintenance Checklist Security Operations Integration Ppt Elements. Use it as a tool for discussion and navigation on System Monitoring Real Time, Backup Monitoring, Preventive Maintenance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise security operations essential roles and responsibilities involved in secops ppt styles styles
Enterprise security operations essential roles and responsibilities involved in secops ppt styles stylesThis slide portrays information regarding the roles and responsibilities, qualification associated to staff available at Tier1, 2, 3, and 4 level at SOC structure. Present the topic in a bit more detail with this Enterprise Security Operations Essential Roles And Responsibilities Involved In Secops Ppt Styles Styles. Use it as a tool for discussion and navigation on Security Engineers, Business, Communication Skills, Management, Training. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise security operations insider attacker method and behavior assessment ppt gridlines
Enterprise security operations insider attacker method and behavior assessment ppt gridlinesThis slide portrays information regarding the insider attacker assessment in security operations system by addressing the method they use to attack and analyzing insider behavior. Present the topic in a bit more detail with this Enterprise Security Operations Insider Attacker Method And Behavior Assessment Ppt Gridlines. Use it as a tool for discussion and navigation on Insider Attacker Method And Behaviour Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise security operations security and operational tasks maintenance checklist ppt maker
Enterprise security operations security and operational tasks maintenance checklist ppt makerThis slide provides information regarding security and operational task maintenance checklist with activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Present the topic in a bit more detail with this Enterprise Security Operations Security And Operational Tasks Maintenance Checklist Ppt Maker. Use it as a tool for discussion and navigation on System Monitoring, Executive Reporting, Planning Meeting, Preventive Maintenance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enhanced security event management security and operational tasks maintenance checklist ppt aids
Enhanced security event management security and operational tasks maintenance checklist ppt aidsThis slide provides information regarding security and operational task maintenance checklist with activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Present the topic in a bit more detail with this Enhanced Security Event Management Security And Operational Tasks Maintenance Checklist Ppt Aids. Use it as a tool for discussion and navigation on System Monitoring, Executive Reporting, Planning Meeting, Preventive Maintenance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Competitive Operations And Financials Performance Security Alarm And Monitoring Systems Company Profile
Competitive Operations And Financials Performance Security Alarm And Monitoring Systems Company ProfileThis slide highlights the security company competitive analysis which includes founding year, recurring monthly revenue, CSR initiatives, revenue, net profit and employee count. Deliver an outstanding presentation on the topic using this Competitive Operations And Financials Performance Security Alarm And Monitoring Systems Company Profile. Dispense information and present a thorough explanation of Competitive, Operations, Performance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Smart Home Operating System Integration Security Alarm And Monitoring Systems Company Profile
Smart Home Operating System Integration Security Alarm And Monitoring Systems Company ProfileThis slide highlights the security company smart home operating system integration with all smart devices which includes real time event processing, and AI powered automation. Deliver an outstanding presentation on the topic using this Smart Home Operating System Integration Security Alarm And Monitoring Systems Company Profile. Dispense information and present a thorough explanation of Integration, Automation, Processing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Competitive Operations And Financials Performance Analysis Smart Security Systems Company Profile
Competitive Operations And Financials Performance Analysis Smart Security Systems Company ProfileThis slide highlights the security company competitive analysis which includes founding year, recurring monthly revenue, CSR initiatives, revenue, net profit and employee count. Deliver an outstanding presentation on the topic using this Competitive Operations And Financials Performance Analysis Smart Security Systems Company Profile. Dispense information and present a thorough explanation of Competitive, Operations, Performance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Securing Operations Of Logistics Through Integrated Enabling Smart Shipping And Logistics Through Iot
Securing Operations Of Logistics Through Integrated Enabling Smart Shipping And Logistics Through IotThis slide showcases securing operations of logistics through integrated internet of things IoT. It provides details such as field network, automation network, process network, operations, operating system, remote access, etc. Deliver an outstanding presentation on the topic using this Securing Operations Of Logistics Through Integrated Enabling Smart Shipping And Logistics Through Iot. Dispense information and present a thorough explanation of Potential Impact, Iot Security System, Securing Operations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Measure Security Automation Metrics For Operations Security Automation To Investigate And Remediate Cyberthreats
Measure Security Automation Metrics For Operations Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the security automation metrics for operation efficiency which includes time to remediation, operation performance improvements, sensor value and workflow effectiveness metrics. Present the topic in a bit more detail with this Measure Security Automation Metrics For Operations Security Automation To Investigate And Remediate Cyberthreats. Use it as a tool for discussion and navigation on Measure, Automation, Operations Efficiency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Criteria To Automate Security Analysis And Response Enabling Automation In Cyber Security Operations
Criteria To Automate Security Analysis And Response Enabling Automation In Cyber Security OperationsThis slide highlight the key criteria to automate the IT security which covers different questions related to tools deployment, set of activities, high time for security threat investigation and pressure from security threats. Present the topic in a bit more detail with this Criteria To Automate Security Analysis And Response Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Intervention, Malware Analysis, Automate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security Operations
Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security OperationsThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Present the topic in a bit more detail with this Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Security Information, Management, Automation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security Operations
Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security OperationsThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Present the topic in a bit more detail with this Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Security Automation, Integrates, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
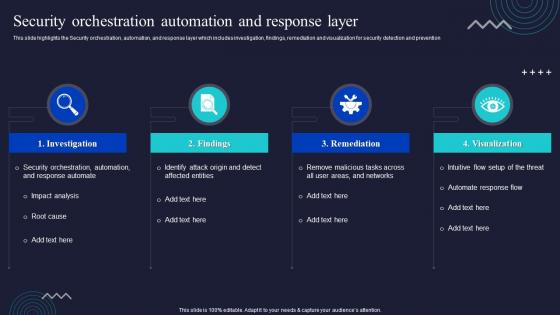 Security Orchestration Automation And Response Layer Enabling Automation In Cyber Security Operations
Security Orchestration Automation And Response Layer Enabling Automation In Cyber Security OperationsThis slide highlights the Security orchestration, automation, and response layer which includes investigation, findings, remediation and visualization for security detection and prevention Deliver an outstanding presentation on the topic using this Security Orchestration Automation And Response Layer Enabling Automation In Cyber Security Operations. Dispense information and present a thorough explanation of Investigation, Remediation, Visualization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enterprise Security Operation Center Team Roles And Responsibilities
Enterprise Security Operation Center Team Roles And ResponsibilitiesThis slide covers enterprise security operation center team roles and responsibilities. It involves key roles such as incident responder, security investigator, advanced security analyst and SOC manager. Introducing our Enterprise Security Operation Center Team Roles And Responsibilities set of slides. The topics discussed in these slides are Security Investigator, Incident Responder, Advanced Security Analyst. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 SecOps Challenges And Solutions Of Security Operations Centres Ppt Download
SecOps Challenges And Solutions Of Security Operations Centres Ppt DownloadThis slide outlines the key challenges and solutions of security operations centers. The purpose of this slide is to highlight the problems faced by SOC teams and methods to overcome those problems. The main challenges include talent gaps, sophisticated attackers, increased data and network traffic, etc. Deliver an outstanding presentation on the topic using this SecOps Challenges And Solutions Of Security Operations Centres Ppt Download. Dispense information and present a thorough explanation of Talent Gap, Sophisticated Attackers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SecOps Tools And Technologies Used In Security Operations Center Ppt Summary
SecOps Tools And Technologies Used In Security Operations Center Ppt SummaryThis slide highlights the crucial tools and technologies used in the SecOps environment. The purpose of this slide is to showcase the various tools and techniques a SOC requires. The main tools include log collection and management, vulnerability management, security information, and event management, etc. Deliver an outstanding presentation on the topic using this SecOps Tools And Technologies Used In Security Operations Center Ppt Summary. Dispense information and present a thorough explanation of Features, Technologies, Description using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Response Plan Secure Operations Data Breach Prevention And Mitigation
Data Breach Response Plan Secure Operations Data Breach Prevention And MitigationThis slide represents actions to be taken, the responsible team, the deadline, and tasks for securing operations after a data breach. The action items include secure physical areas, assemble expert team, consult with legal counsel, secure website and contact search engines, etc. Present the topic in a bit more detail with this Data Breach Response Plan Secure Operations Data Breach Prevention And Mitigation. Use it as a tool for discussion and navigation on Assemble Expert Team, Consult With Legal Counsel, Secure Physical Areas. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Role Of ZTNA To Improve Business Operations And Security Zero Trust Security Model
Role Of ZTNA To Improve Business Operations And Security Zero Trust Security ModelThis slide talks about the ways in which ZTNA improves the business operations and security. The purpose of this slide is to showcase the various domains that zero trust network access improves, including increased user experience, remote workforce protection, improve data protection, and network visibility. Deliver an outstanding presentation on the topic using this Role Of ZTNA To Improve Business Operations And Security Zero Trust Security Model. Dispense information and present a thorough explanation of Enhanced User Experience, Remote Workforce Protection, Improve Data Protection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Step 6 And 7 Define Operational Changes And Implement Rinse Repeat Zero Trust Security Model
Step 6 And 7 Define Operational Changes And Implement Rinse Repeat Zero Trust Security ModelThis slide outlines the sixth and seventh steps for ZTNA implementation, which are defining operational changes and implementing, rinsing and repeating the process. The purpose of this slide is to showcase the following steps in zero trust model deployment. Deliver an outstanding presentation on the topic using this Step 6 And 7 Define Operational Changes And Implement Rinse Repeat Zero Trust Security Model. Dispense information and present a thorough explanation of Operational, Implement, Performance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secops V2 Challenges And Solutions Of Security Operations Centres
Secops V2 Challenges And Solutions Of Security Operations CentresThis slide outlines the key challenges and solutions of security operations centers. The purpose of this slide is to highlight the problems faced by SOC teams and methods to overcome those problems. The main challenges include talent gaps, sophisticated attackers, increased data and network traffic, etc. Present the topic in a bit more detail with this Secops V2 Challenges And Solutions Of Security Operations Centres. Use it as a tool for discussion and navigation on Challenges And Solutions, Security Operations Centres, Sophisticated Attackers, Data And Network Traffic. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Secops V2 Tools And Technologies Used In Security Operations Center
Secops V2 Tools And Technologies Used In Security Operations CenterThis slide highlights the crucial tools and technologies used in the SecOps environment. The purpose of this slide is to showcase the various tools and techniques a SOC requires. The main tools include log collection and management, vulnerability management, security information, and event management, etc. Deliver an outstanding presentation on the topic using this Secops V2 Tools And Technologies Used In Security Operations Center. Dispense information and present a thorough explanation of Vulnerability Management, Log Collection And Management Tool, Security Information And Event Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Overview And Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Overview And Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases overview of streamlining security operations which can help organization to prevent cyber attacks in organization. It also highlight various benefits of streamlining security operations such as timely incident response, vulnerability assessment, reduction in cyber attacks etc. Deliver an outstanding presentation on the topic using this Overview And Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Dispense information and present a thorough explanation of Overview, Streamlining, Operations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Overview And Importance Of Streamlining Security Operations Leveraging ChatGPT AI SS V
Overview And Importance Of Streamlining Security Operations Leveraging ChatGPT AI SS VThis slide showcases overview of streamlining security operations which can help organization to prevent cyber attacks in organization. It also highlight various benefits of streamlining security operations such as timely incident response, vulnerability assessment, reduction in cyber attacks etc. Present the topic in a bit more detail with this Overview And Importance Of Streamlining Security Operations Leveraging ChatGPT AI SS V Use it as a tool for discussion and navigation on Threat Intelligence, Overview Of Threat, Importance Of Threat This template is free to edit as deemed fit for your organization. Therefore download it now.


