Powerpoint Templates and Google slides for Secure Systems
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
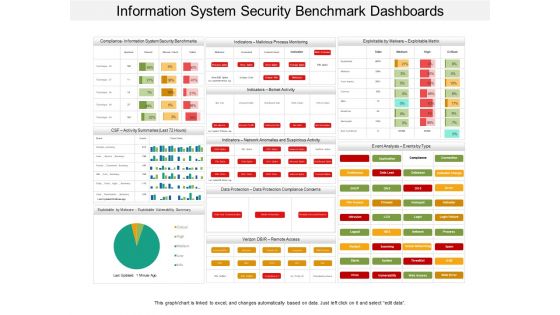 Information system security benchmark dashboards
Information system security benchmark dashboardsPresenting this set of slides with name - Information System Security Benchmark Dashboards. This is a three stage process. The stages in this process are Information Security Strategy, Information Security Plan, Information Protection Strategy.
-
 Computer system security comparison ppt powerpoint presentation slides visuals
Computer system security comparison ppt powerpoint presentation slides visualsIntroducing Computer System Security Comparison Ppt Powerpoint Presentation Slides Visuals to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Male Users, Female Users, using this template. Grab it now to reap its full benefits.
-
 Computer system security impact on organization after implementing computer security strategy and training
Computer system security impact on organization after implementing computer security strategy and trainingThis slide depicts the impact of cyber security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Increase audience engagement and knowledge by dispensing information using Computer System Security Impact On Organization After Implementing Computer Security Strategy And Training. This template helps you present information on five stages. You can also present information on Phishing, Network Intrusion, Inadvertent Disclosure, Stolen Or Lost Devises Or Records, System Misconfiguration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 About Us Information System Security And Risk Administration Plan Ppt Styles Gallery
About Us Information System Security And Risk Administration Plan Ppt Styles GalleryIncrease audience engagement and knowledge by dispensing information using About Us Information System Security And Risk Administration Plan Ppt Styles Gallery. This template helps you present information on three stages. You can also present information on Target Audiences, Creative, Value Clients using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Virtual Currency Icon For Secured Payment System
Virtual Currency Icon For Secured Payment SystemIntroducing our premium set of slides with name Virtual Currency Icon For Secured Payment System Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Virtual Currency Icon, Secured Payment System. So download instantly and tailor it with your information.
-
 Comparative Analysis Of Wired And Wireless Security System
Comparative Analysis Of Wired And Wireless Security SystemThis slide highlights wireless and wired system comparative analysis for performance. This further includes pros and cons for both wired and wireless system such as reliable, support large systems, smarter and flexible etc. Presenting our set of slides with Comparative Analysis Of Wired And Wireless Security System. This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Wired Security System, Comparative Analysis.
-
 Firewall Network Security Pros And Cons Of Cloud Firewall Systems
Firewall Network Security Pros And Cons Of Cloud Firewall SystemsThis slide highlights the advantages and disadvantages of cloud-based firewall systems. The purpose of this slide is to showcase the pros and cons of cloud firewalls, and the pros include deployment and scalability, access and identity management, updates, and availability. Introducing Firewall Network Security Pros And Cons Of Cloud Firewall Systems to increase your presentation threshold. Encompassed with Two stages, this template is a great option to educate and entice your audience. Dispence information on Pros, Cons, Speed, Embedded Malware using this template. Grab it now to reap its full benefits.
-
 Access Management Components Authentication Securing Systems With Identity
Access Management Components Authentication Securing Systems With IdentityThis slide gives an overview of access management of the Identity and Access Management process. The purpose of this slide is to explain access management that primarily focuses on authentication and authorization. Increase audience engagement and knowledge by dispensing information using Access Management Components Authentication Securing Systems With Identity This template helps you present information on Two stages. You can also present information on Authentication, Authorization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 IAM Authentication And Authorization Workflow Process Securing Systems With Identity
IAM Authentication And Authorization Workflow Process Securing Systems With IdentityThis slide showcases the workflow of IAM authentication and authorization. The purpose of this slide is to explain the process, starting with user authentication and authorization, that often uses a single sign-on solution that incorporates multi-factor authentication and assigns access rights to resources. Increase audience engagement and knowledge by dispensing information using IAM Authentication And Authorization Workflow Process Securing Systems With Identity This template helps you present information on Two stages. You can also present information on Authentication, Authorization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Identity And Access Management Working Functions Securing Systems With Identity
Identity And Access Management Working Functions Securing Systems With IdentityThis slide discusses the working process of Identity and Access Management . The purpose of this slide is to explain the workflow of the IAM this includes identity management that validates login attempts and access management that manages the entitys access. Introducing Identity And Access Management Working Functions Securing Systems With Identity to increase your presentation threshold. Encompassed with Two stages, this template is a great option to educate and entice your audience. Dispence information on Identity Management, Access Management using this template. Grab it now to reap its full benefits.
-
 Traditional Vs Modern IAM Security Landscape Securing Systems With Identity
Traditional Vs Modern IAM Security Landscape Securing Systems With IdentityThis slide compares traditional vs. modern Identity and Access Management security landscape. The purpose of this slide is to highlight the difference between conventional and contemporary Identity and Access Management systems. Increase audience engagement and knowledge by dispensing information using Traditional Vs Modern IAM Security Landscape Securing Systems With Identity This template helps you present information on Two stages. You can also present information on Authorization, Central User Repository, User Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Use Cases Of Identity And Access Management Securing Systems With Identity
Use Cases Of Identity And Access Management Securing Systems With IdentityThis slide highlights the Identity and Access Management process use cases. The purpose of this slide is to discuss the cases these include IAM for zero trust at better.com and IAM for streamlined onboarding at hearst. Introducing Use Cases Of Identity And Access Management Securing Systems With Identity to increase your presentation threshold. Encompassed with Two stages, this template is a great option to educate and entice your audience. Dispence information on Loss Prevention, Compromising Security using this template. Grab it now to reap its full benefits.



