Powerpoint Templates and Google slides for Secure Systems
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Computer system security security framework in cloud computing
Computer system security security framework in cloud computingThis slide depicts how tasks are performed under cloud security through the framework. The framework consists of different stages such as identity, protection, detection, response, and recovery. Increase audience engagement and knowledge by dispensing information using Computer System Security Security Framework In Cloud Computing. This template helps you present information on five stages. You can also present information on Identify, Protect, Detect, Respond, Recover using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Elements of computer security end user education computer system security
Elements of computer security end user education computer system securityThis slide shows the end-user education within the cyber security model. It also represents various factors that effective training plans should involve. Introducing Elements Of Computer Security End User Education Computer System Security to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Social Media, Protection Measures, Security Threat, Cyber Security, using this template. Grab it now to reap its full benefits.
-
 Elements of computer security operational security computer system security
Elements of computer security operational security computer system securityThis slide defines the operational security element of cyber security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Increase audience engagement and knowledge by dispensing information using Elements Of Computer Security Operational Security Computer System Security. This template helps you present information on five stages. You can also present information on Change Management Processes, Deploy Automation, Plan For Disaster, Restrict Device Access, Implement Dual Control using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer system security common methods used to threaten computer security
Computer system security common methods used to threaten computer securityThis slide depicts the standard methods used to threaten cyber security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Increase audience engagement and knowledge by dispensing information using Computer System Security Common Methods Used To Threaten Computer Security. This template helps you present information on five stages. You can also present information on Malware, Daniel Of Service, Man In The Middle, SQL Injection, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
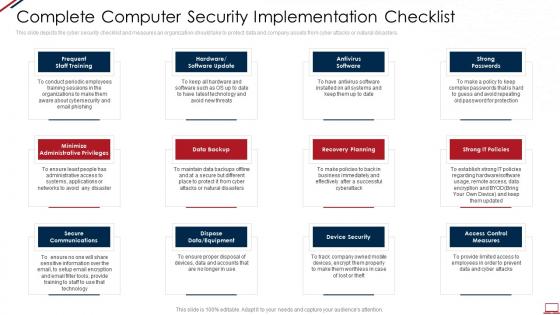 Computer system security complete computer security implementation checklist
Computer system security complete computer security implementation checklistThis slide depicts the cyber security checklist and measures an organization should take to protect data and company assets from cyber attacks or natural disasters. Increase audience engagement and knowledge by dispensing information using Computer System Security Complete Computer Security Implementation Checklist. This template helps you present information on twelve stages. You can also present information on Data Backup, Secure Communications, Recovery Planning, Strong Passwords, Device Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer system security elements of computer security cloud security
Computer system security elements of computer security cloud securityThis slide defines the cloud security element of cyber security and various threats that can breach cloud security, such as malware injection, malicious insiders, insecure APIs, etc. Introducing Computer System Security Elements Of Computer Security Cloud Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Insecure Apis, Account Hijacking, Malicious Insiders, Malware Injections, Data Breaches, using this template. Grab it now to reap its full benefits.
-
 Security issues payment system ppt powerpoint presentation slides visuals cpb
Security issues payment system ppt powerpoint presentation slides visuals cpbPresenting our Security Issues Payment System Ppt Powerpoint Presentation Slides Visuals Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Security Issues Payment System This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security Camera System Business In Powerpoint And Google Slides Cpb
Security Camera System Business In Powerpoint And Google Slides CpbPresenting Security Camera System Business In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Camera System Business. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Case Study Of Financial Institution And Cyber Security System
Case Study Of Financial Institution And Cyber Security SystemThis slide represents case study on use of cybersecurity system in financial institution. This further includes about client, challenges, solutions and results after using cyber security system. Presenting our set of slides with Case Study Of Financial Institution And Cyber Security System. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Financial Services, Customer Data, Management.
-
 Challenges And Solutions Associated With Security System
Challenges And Solutions Associated With Security SystemThis slide highlights security system challenges and solutions to overcome them. This further includes organization name, challenge and solutions such as server breach on main website of firm etc. Introducing our premium set of slides with Challenges And Solutions Associated With Security System. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Organization, Company, Security System. So download instantly and tailor it with your information.
-
 Futuristic Trends In Cyber Security System
Futuristic Trends In Cyber Security SystemThis slide represents cyber security system futuristic trends. This further includes remote work, automate, adopt zero trust principles, improve response capabilities and recognize supply chain risks. Presenting our set of slides with Futuristic Trends In Cyber Security System. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Remote Work, Trust Principles, Response Capabilities.
-
 IOT Solution Components In Cyber Security System
IOT Solution Components In Cyber Security SystemThis slide highlights cyber security system components for IOT solutions. This includes secure device, secure communication, secured cloud and further includes messaging control and device integrated connections. Presenting our set of slides with IOT Solution Components In Cyber Security System. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Secure Device, Secure Communication, Secured Cloud.
-
 Security System Issues Related With E Commerce Business
Security System Issues Related With E Commerce BusinessThis slide showcases e commerce business issues for security systems. This further includes security issues such as identity and success, risk advisory, threat management and digital security. Presenting our set of slides with Security System Issues Related With E Commerce Business. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Advisory, Identity And Access, Threat Management, Digital Security.
-
 Food Security System In Powerpoint And Google Slides Cpb
Food Security System In Powerpoint And Google Slides CpbPresenting Food Security System In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Five RMD Holding. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Security System Used In Smart IoT Remote Asset Monitoring And Management IoT SS
Security System Used In Smart IoT Remote Asset Monitoring And Management IoT SSThis slide provides an overview of the smart security systems used in houses to enhance safety. The slide includes components, types and features that are it allows access to authorized people, store data and provide protection against vulnerabilities. Increase audience engagement and knowledge by dispensing information using Security System Used In Smart IoT Remote Asset Monitoring And Management IoT SS. This template helps you present information on three stages. You can also present information on Components, Features, Detection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Home Security Surveillance System In Powerpoint And Google Slides Cpb
Home Security Surveillance System In Powerpoint And Google Slides CpbPresenting our Home Security Surveillance System In Powerpoint And Google Slides Cpb. PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Home Security Surveillance System. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 MAGAL Security Systems Stock In Powerpoint And Google Slides Cpb
MAGAL Security Systems Stock In Powerpoint And Google Slides CpbPresenting MAGAL Security Systems Stock In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like MAGAL Security Systems Stock. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS V
Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS VThe following slide showcases key phases of penetration testing to identify potential flaws and malware. It includes elements of discovery phase such as architecture, compliance readiness, readiness analysis, etc. Introducing Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Architecture Of Blockchain, Compliance Readiness, Readiness Analysis, using this template. Grab it now to reap its full benefits.
-
 Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SS
Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SSThis slide exhibits IoT security best practices that help in addressing potential security weaknesses. It includes best practices such as network segmentation, IoT incident response plan, intrusion detection system, and patching and remediation. Increase audience engagement and knowledge by dispensing information using Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on four stages. You can also present information on Network Segmentation, Intrusion Detection System, Patching Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Practices To Provision Devices And Systems IoT Security And Privacy Safeguarding IoT SS
Best Practices To Provision Devices And Systems IoT Security And Privacy Safeguarding IoT SSThis slide outlines best practices of device and system provisioning that aim to effectively integrate devices into the IoT ecosystem. It includes allocate unique identifies, set up access control, and backup and recovery. Introducing Best Practices To Provision Devices And Systems IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Unique Identifies, Systematic Backup Process, Reduce Downtime, using this template. Grab it now to reap its full benefits.
-
 Firewall Network Security Understanding Cloud Firewall Security Systems
Firewall Network Security Understanding Cloud Firewall Security SystemsThis slide gives an overview of cloud-based firewall security systems, including their importance, types, benefits, and working features. The purpose of this slide is to showcase the different aspects of cloud-based firewalls. The main types include Next Generation Firewall and SaaS firewalls. Introducing Firewall Network Security Understanding Cloud Firewall Security Systems to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Benefits, Working Functions, Types using this template. Grab it now to reap its full benefits.
-
 Firewall Network Security Unified Threat Management UTM Firewall System Overview
Firewall Network Security Unified Threat Management UTM Firewall System OverviewThis slide provides an introduction to the Unified Threat Management firewall system. The purpose of this slide is to showcase the features, benefits, and inspection methods of Unified Threat Management firewall systems, such as flow-based and proxy-based inspection. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Understanding Critical Risks Of Firewall Absence This template helps you present information on Three stages. You can also present information on Content Filtering, Faster Security, Flexibility And Adaptability using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Benefits Of Next Generation Firewall Protection System
Firewall Network Security Benefits Of Next Generation Firewall Protection SystemThis slide highlights the advantages of Next Generation Firewalls for network protection. The purpose of this slide is to showcase the different benefits of next-generation firewall, such as robust threat prevention, flexible deployment, app, and identity-based checking and control, etc. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Benefits Of Next Generation Firewall Protection System This template helps you present information on Four stages. You can also present information on Firewall Network Security Benefits Of Next Generation Firewall Protection System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Deployment Methods Of Firewall Security System
Firewall Network Security Deployment Methods Of Firewall Security SystemThis slide represents the key applications of firewall security systems. The purpose of this slide is to showcase the different deployment options of firewall security systems, such as software-based applications, hardware-based applications, and cloud-based applications. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Deployment Methods Of Firewall Security System This template helps you present information on Three stages. You can also present information on Software Based Applications, Hardware Based Applications, Cloud Based Applications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Features Of Distributed Firewall Management System
Firewall Network Security Features Of Distributed Firewall Management SystemThis slide represents the key characteristics of distributed firewall management system. The purpose of this slide is to showcase the different features of distributed firewalls, such as central management systems, security policy distribution, enhanced access control, and host-end execution. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Features Of Distributed Firewall Management System This template helps you present information on Four stages. You can also present information on Access Control, Concurrency Processing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Importance And Benefits Of Distributed Firewall Management System
Firewall Network Security Importance And Benefits Of Distributed Firewall Management SystemThis slide outlines the importance of distributed firewall management system. It also includes the various advantages of distributed firewalls, including security from insider threats, intrusion detection, service exposure, and port scanning. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Importance And Benefits Of Distributed Firewall Management System This template helps you present information on Three stages. You can also present information on Network Address Translation, Virtual Private Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Intrusion Prevention Systems Ipss Overview And Methods
Firewall Network Security Intrusion Prevention Systems Ipss Overview And MethodsThis slide talks about the Intrusion Prevention System and its various methods for analyzing traffic. The purpose of this slide is to give an overview of Intrusion Prevention Systems and their methods, such as signature-based detection, statistical anomaly detection, and stateful protocol analysis detection. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Intrusion Prevention Systems Ipss Overview And Methods This template helps you present information on Three stages. You can also present information on Spyware Protection, Against Viruses, Prevents Hacking using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Key Benefits Of Firewall Protection System
Firewall Network Security Key Benefits Of Firewall Protection SystemThis slide talks about the main advantages of a firewall security system. The purpose of this slide is to highlight the key benefits of a firewall for businesses, such as spyware protection, the significant barrier against viruses, protection against hacking, privacy promotion, and network traffic monitoring. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Key Benefits Of Firewall Protection System This template helps you present information on Five stages. You can also present information on Intelligent Protection, Traffic Filtering, Communication Protocol Administration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Key Components Of Firewall Management System
Firewall Network Security Key Components Of Firewall Management SystemThis slide talks about the important elements of the firewall management system. The purpose of this slide is to showcase the vital components of a firewall management system, such as a graphical interface, policy control, threat management, device management, third-party integrations, and scalability. Introducing Firewall Network Security Key Components Of Firewall Management System to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Access Service, Artificial Intelligence using this template. Grab it now to reap its full benefits.
-
 Elements Of Systems Applications And Products Cyber Security
Elements Of Systems Applications And Products Cyber SecurityThis slide depicts the components of SAP cybersecurity. The purpose of this template is to help understand the areas of business networks that can be safeguarded with the help of SAP cybersecurity elements. It includes data base security, infrastructure security, etc. Presenting our set of slides with Elements Of Systems Applications And Products Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Database Security, Operating System Security, Network Security, Infrastructure Security.
-
 Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS V
Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS VThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Increase audience engagement and knowledge by dispensing information using Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS V. This template helps you present information on four stages. You can also present information on Fraud Detection, Compliance Tracking, Risk Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Integrating ChatGPT With Other Systems Security And Compliance Glimpse About ChatGPT As AI ChatGPT SS V
Integrating ChatGPT With Other Systems Security And Compliance Glimpse About ChatGPT As AI ChatGPT SS VThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Introducing Integrating ChatGPT With Other Systems Security And Compliance Glimpse About ChatGPT As AI ChatGPT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Fraud Detection, Compliance Tracking, Risk Analysis, Cybersecurity, Security And Compliance Management, using this template. Grab it now to reap its full benefits.
-
 Security Systems Investment In Powerpoint And Google Slides Cpb
Security Systems Investment In Powerpoint And Google Slides CpbPresenting Security Systems Investment In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Systems Investment. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Multiple Cashless Payment Systems Leveraged By Business Enhancing Transaction Security With E Payment
Multiple Cashless Payment Systems Leveraged By Business Enhancing Transaction Security With E PaymentMentioned slide provides information about various payment systems which can be leveraged by businesses to increase cashless transactions. It includes payment systems such as virtual terminal, card reader, payment terminal and invoicing software. Increase audience engagement and knowledge by dispensing information using Multiple Cashless Payment Systems Leveraged By Business Enhancing Transaction Security With E Payment This template helps you present information on four stages. You can also present information on Virtual Terminal, Card Reader, Payment Terminal using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security System Used In Smart Monitoring Patients Health Through IoT Technology IoT SS V
Security System Used In Smart Monitoring Patients Health Through IoT Technology IoT SS VThis slide provides an overview of the smart security systems used in houses to enhance safety. The slide includes components, types and features that are it allows access to authorized people, store data and provide protection against vulnerabilities. Introducing Security System Used In Smart Monitoring Patients Health Through IoT Technology IoT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Interworking Devices, Wireless Cameras, Protects Data, using this template. Grab it now to reap its full benefits.
-
 Importance Of Cyber Security In Automotive Systems
Importance Of Cyber Security In Automotive SystemsThis slide highlights relevance of cyber security in vehicles. The purpose of this slide is to aid professionals in ensuring safety, privacy and functionality of automobiles against potential cyber threats and attacks. It includes elements such as safety, data protection, etc. Presenting our set of slides with Importance Of Cyber Security In Automotive Systems This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Vehicle Integrity, Financial Implications.
-
 Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting Systems
Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting SystemsThis slide discusses the concept of governance tokenization in data security. The purpose of this slide is to showcase the overview of governance tokenization which include usage, features, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting Systems. This template helps you present information on eight stages. You can also present information on Lack A Central Authority, Pivotal Decision Making, Widely Used Savings Protocol using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System
Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based SystemThis slide highlights the key functions within a cloud-based system in data security. The purpose of this slide is to outline the Process activities in a cloud-based system which include gathering, creating, retrieving data, etc. Introducing Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Tokenization Process Activities, Cloud Based System, Retrieving Data, using this template. Grab it now to reap its full benefits.
-
 Role Of Intrusion Prevention Systems In Wireless Internet Security
Role Of Intrusion Prevention Systems In Wireless Internet SecurityThe outlined slide covers essential aspects, including encryption, authentication, access control, device security, and intrusion detection prevention. It provides a comprehensive view of wireless internet security measures, crucial for thwarting data theft. Introducing our premium set of slides with Role Of Intrusion Prevention Systems In Wireless Internet Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Compliance Requirements, Increased Network Visibility, Cost Effective Security. So download instantly and tailor it with your information.
-
 ATP Cyber Security System Process
ATP Cyber Security System ProcessThis slide showcases the ATP cyber security process. Its aim is to help define the target and identify the anomalies. This slide includes researching target, acquiring tools, detection of virus, strengthening the system, remove virus, etc. Presenting our set of slides with name ATP Cyber Security System Process. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Plan, Intrusion, Getting Out, Sub Zero.
-
 Securing Voting Systems With Blockchain Decoding The Future Of Blockchain Technology BCT SS
Securing Voting Systems With Blockchain Decoding The Future Of Blockchain Technology BCT SSThis slide highlights how blockchain technology helps governments in ensuring secured voting mechanisms to reduce frauds. It includes protection against fraud, decentralized and trust, real time monitoring, eradication of double voting and elimination of intermediaries. Introducing Securing Voting Systems With Blockchain Decoding The Future Of Blockchain Technology BCT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Decentralization And Trust, Protection Against Fraud, Real-Time Monitoring And Auditing, using this template. Grab it now to reap its full benefits.
-
 Advantages Of Hids Based Cyber Security Systems
Advantages Of Hids Based Cyber Security SystemsThis slide represents advantages of HIDS based cyber security which assists organizations to monitor process and applications running on devices. It includes advantages such as monitor system activities, detects attacks, etc Presenting our set of slides with Advantages Of Hids Based Cyber Security Systems. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Monitors System Activities, Lowers Entry Cost, Verifies Success Or Failures Of Attacks.
-
 Physical Security System Protection Measures
Physical Security System Protection MeasuresThis slide showcases various layers that prevent unauthorized access and ensure security. The layers covered are deterrence, detection and access control. Presenting our set of slides with Physical Security System Protection Measures. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Deterrence, Detection, Access Control.
-
 Physical Security Systems To Enhance Data Safety
Physical Security Systems To Enhance Data SafetyThis slide showcases physical control systems to manage and safeguard crucial data. The systems covered are cable infrastructure, fire alarm, building management, etc. Introducing our premium set of slides with Physical Security Systems To Enhance Data Safety. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cable Infrastructure, Electronic Security Systems, Building Management. So download instantly and tailor it with your information.
-
 Components Of Identity And Access Management Process Securing Systems With Identity
Components Of Identity And Access Management Process Securing Systems With IdentityThis slide discusses the Identity and Access Management components. The purpose of this slide is to highlight the various components, including the IAM framework, access and roles, IAM system function, centralized directory services, and so on. Introducing Components Of Identity And Access Management Process Securing Systems With Identity to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Iam Framework Purpose, Access And Roles, Iam System Functions using this template. Grab it now to reap its full benefits.
-
 Core Services Of Identity And Access Management Securing Systems With Identity
Core Services Of Identity And Access Management Securing Systems With IdentityThis slide discusses the Identity and Access Management core services. The purpose of this slide is to highlight the core services of IAM these include identifying, authentication, authorizing, auditing, and verifying the accounts. Introducing Core Services Of Identity And Access Management Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Identification, Authentication, Authorization using this template. Grab it now to reap its full benefits.
-
 Data Analytics Importance In Identity And Access Management Securing Systems With Identity
Data Analytics Importance In Identity And Access Management Securing Systems With IdentityThis slide showcases the importance of Identity and Access Management based data analytics. The purpose of this slide is to explain the benefits, which are anomaly detection, account monitoring, policy violation detection, and so on. Increase audience engagement and knowledge by dispensing information using Data Analytics Importance In Identity And Access Management Securing Systems With Identity This template helps you present information on Five stages. You can also present information on Anomaly Detection, Identity Certification Campaigns using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Examples Of Identity And Access Management Securing Systems With Identity
Examples Of Identity And Access Management Securing Systems With IdentityThis slide highlights the Identity and Access Management examples. The purpose of this slide is to discuss the examples these include multi-factor authentication tools, access provisioning and de-provisioning, and user monitoring for access control. Introducing Examples Of Identity And Access Management Securing Systems With Identity to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Authentication Tools, Provisioning And Deprovisioning, Monitoring For Access Control using this template. Grab it now to reap its full benefits.
-
 Functions Of Identity And Access Management Process Securing Systems With Identity
Functions Of Identity And Access Management Process Securing Systems With IdentityThis slide discusses the Identity and Access Management process functions. The purpose of this slide is to highlight the various functions, including identification in the system, roles in the design, assigning access levels, protecting sensitive data, and so on. Introducing Functions Of Identity And Access Management Process Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Identification In System, Roles In System using this template. Grab it now to reap its full benefits.
-
 Fundamentals Of Identity And Access Management Securing Systems With Identity
Fundamentals Of Identity And Access Management Securing Systems With IdentityThis slide discusses the fundamentals of the Identity and Access Management process. The purpose of this slide is to highlight the fundamental concepts of IAM, including authentication, authorization, administration, and audit. Increase audience engagement and knowledge by dispensing information using Fundamentals Of Identity And Access Management Securing Systems With Identity This template helps you present information on Five stages. You can also present information on Authentication, Authorization, Administration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Identity And Access Management Process In Workplace Securing Systems With Identity
Identity And Access Management Process In Workplace Securing Systems With IdentityThis slide discusses the Identity and Access Management process in the workplace. The purpose of this slide is to highlight the various usages of IAM in the workplace these include increasing the number of applications, managing identity data, and complex access scenarios. Increase audience engagement and knowledge by dispensing information using Identity And Access Management Process In Workplace Securing Systems With Identity This template helps you present information on Three stages. You can also present information on Increasing Number Of Applications, Managing Identity Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Parameters Of IAM Implementation Process Securing Systems With Identity
Key Parameters Of IAM Implementation Process Securing Systems With IdentityThis slide highlights the key function of the Identity and Access Management implementation process. The purpose of this slide is to explain the various parameters of IAM implementation these include identity lifecycle management, access control, authentication, and so on. Introducing Key Parameters Of IAM Implementation Process Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Authorization, Identity Governance using this template. Grab it now to reap its full benefits.
-
 Major Focus Areas Of Identity And Access Management Securing Systems With Identity
Major Focus Areas Of Identity And Access Management Securing Systems With IdentityThis slide discusses the Identity and Access Management focus area. The purpose of this slide is to explain the focus area of IAM these include access management, privilege management, and identity governance. Increase audience engagement and knowledge by dispensing information using Major Focus Areas Of Identity And Access Management Securing Systems With Identity This template helps you present information on Three stages. You can also present information on Access Management, Privilege Management, Identity Governance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risk Associated With Identity And Access Management Process Securing Systems With Identity
Risk Associated With Identity And Access Management Process Securing Systems With IdentityThis slide outlines the potential hazards linked to the Identity and Access Management process. The purpose of this slide is to discuss the risks these include incorrectly defined roles and attributes, infrequent audits, and complex implementations. Introducing Risk Associated With Identity And Access Management Process Securing Systems With Identity to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Roles And Attributes, Infrequent Audits, Complex Implementations using this template. Grab it now to reap its full benefits.
-
 Roadmap For Identity And Access Management Implementation Securing Systems With Identity
Roadmap For Identity And Access Management Implementation Securing Systems With IdentityThis slide highlights the project roadmap to implement the Identity and Access Management process. The purpose of this slide is to showcase the different phases of the IAM implementation plan, such as implementing emerging IAM technologies, BYOI adoption, etc. Increase audience engagement and knowledge by dispensing information using Roadmap For Identity And Access Management Implementation Securing Systems With Identity This template helps you present information on Four stages. You can also present information on Iam Technologies, Byoi Adoption, Testing And Security Assurance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps To Implement Digital Authentication With IAM Securing Systems With Identity
Steps To Implement Digital Authentication With IAM Securing Systems With IdentityThis slide discusses the IAM implementing digital authentication. The purpose of this slide is to highlight the various types of digital authentication done by IAM, which are unique passwords, pre-shared keys, Behavioral authentication, and biometrics. Increase audience engagement and knowledge by dispensing information using Steps To Implement Digital Authentication With IAM Securing Systems With Identity This template helps you present information on Five stages. You can also present information on Unique Passwords, Biometrics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps To Implement Identity And Access Management Securing Systems With Identity
Steps To Implement Identity And Access Management Securing Systems With IdentityThis slide discusses the Identity and Access Management implementing program. The purpose of this slide is to highlight the implementation process of IAM, including scope identification, evaluating the right IAM approach, finding the best solution, and so on. Increase audience engagement and knowledge by dispensing information using Steps To Implement Identity And Access Management Securing Systems With Identity This template helps you present information on Six stages. You can also present information on Scope Identification, Define A Strategy, Assess Cost Factors using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Timeline To Implement Identity And Access Management Plan Securing Systems With Identity
Timeline To Implement Identity And Access Management Plan Securing Systems With IdentityThis slide shows the timeline for implementing the Identity and Access Management plan. The key steps include defining the project objective, identifying key stakeholders, determining compliance, integrating IAM with the existing system, etc. Introducing Timeline To Implement Identity And Access Management Plan Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Applications And Data, Public Cloud Platforms using this template. Grab it now to reap its full benefits.
-
 Uniting Identity And Access Management Processes Securing Systems With Identity
Uniting Identity And Access Management Processes Securing Systems With IdentityThis slide discusses the Identity and Access Management uniting process. The purpose of this slide is to explain the Identity and Access Management unit, which involves users, access management, resources, identity management, and ID sources. Increase audience engagement and knowledge by dispensing information using Uniting Identity And Access Management Processes Securing Systems With Identity This template helps you present information on Four stages. You can also present information on Key Takeaways, Iam Market Size using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ai Revolutionizing Network Security Systems In Organisation
Ai Revolutionizing Network Security Systems In OrganisationThis slide shows how AI benefits the organization in multiple ways. The major benefits are they provide real-time threat detection, increase automation, and behavioral analysis. Introducing our premium set of slides with Ai Revolutionizing Network Security Systems In Organisation. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Real Time Threat Detection, Email Filtering, Behavioural Analysis. So download instantly and tailor it with your information.




