Powerpoint Templates and Google slides for Safeguards
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 E mail safeguard industry report key players ppt slides design ideas
E mail safeguard industry report key players ppt slides design ideasA comparative analysis of the key players if E Mail Security Industry are displayed in this slide. Deliver an outstanding presentation on the topic using this E Mail Safeguard Industry Report Key Players Ppt Slides Design Ideas. Dispense information and present a thorough explanation of Proofpoint, Headquarters, Market Share, Geographical Presence, Employees using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Terrorism Threats And Safeguard Assessment Matrix
Cyber Terrorism Threats And Safeguard Assessment MatrixThis slide represents the assessment matrix for cyber terrorism threats and its functions and safeguards. It includes functions such as identify, protect, detect, respond and recover and threats such as phishing, ransomware, web app attacks and vendor and partner data loss. Presenting our well structured Cyber Terrorism Threats And Safeguard Assessment Matrix. The topics discussed in this slide are Phishing, Ransomware, Deception Technology. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 IT Risk Management Strategies IT Risks Safeguard Implementation Plan With Recommended
IT Risk Management Strategies IT Risks Safeguard Implementation Plan With RecommendedThis slide highlights the information technology safeguard implementation plan in tabular format which includes risks, recommended controls, selected controls. Required resources and risk level. Present the topic in a bit more detail with this IT Risk Management Strategies IT Risks Safeguard Implementation Plan With Recommended. Use it as a tool for discussion and navigation on Risks or Threat, Risk Level, Priority, Recommended Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise Risk Management IT Risks Safeguard Implementation Plan With Recommended
Enterprise Risk Management IT Risks Safeguard Implementation Plan With RecommendedThis slide highlights the information technology safeguard implementation plan in tabular format which includes risks, recommended controls, selected controls. Required resources and risk level. Deliver an outstanding presentation on the topic using this Enterprise Risk Management IT Risks Safeguard Implementation Plan With Recommended. Dispense information and present a thorough explanation of Risks or Threat, Risk Level, Priority, Recommended Controls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IT Risks Safeguard Implementation Plan With Recommended Controls
IT Risks Safeguard Implementation Plan With Recommended ControlsThis slide highlights the information technology safeguard implementation plan in tabular format which includes risks, recommended controls, selected controls. Required resources and risk level. Present the topic in a bit more detail with this IT Risks Safeguard Implementation Plan With Recommended Controls. Use it as a tool for discussion and navigation on Risk Level, Recommended Controls, Required Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
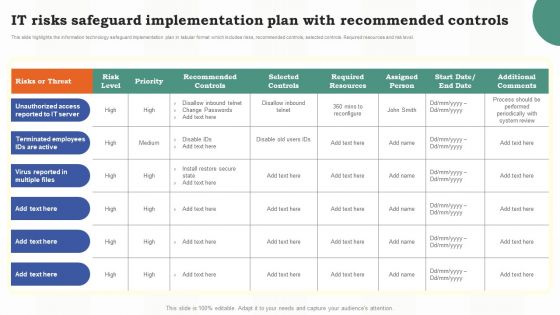 Risk Assessment Of It Systems It Risks Safeguard Implementation Plan With Recommended Controls
Risk Assessment Of It Systems It Risks Safeguard Implementation Plan With Recommended ControlsThis slide highlights the information technology safeguard implementation plan in tabular format which includes risks, recommended controls, selected controls. Required resources and risk level. Present the topic in a bit more detail with this Risk Assessment Of It Systems It Risks Safeguard Implementation Plan With Recommended Controls. Use it as a tool for discussion and navigation on Implementation, Information, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Competitive Defense Plan To Safeguard Existing Brand Position Toolkit To Handle Brand Identity
Competitive Defense Plan To Safeguard Existing Brand Position Toolkit To Handle Brand IdentityThis slide provides information regarding competitive defense plan in order to protect current brands position across existing market. It involves components such as defense strategy, target, brand idea, desired response and program. Deliver an outstanding presentation on the topic using this Competitive Defense Plan To Safeguard Existing Brand Position Toolkit To Handle Brand Identity. Dispense information and present a thorough explanation of Competitive, Desired Response, Defense Strategy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Competitive Defense Plan To Safeguard Existing Brand Position Marketing Guide To Manage Brand
Competitive Defense Plan To Safeguard Existing Brand Position Marketing Guide To Manage BrandThis slide provides information regarding competitive defense plan in order to protect current brands position across existing market. It involves components such as defense strategy, target, brand idea, desired response and program. Present the topic in a bit more detail with this Competitive Defense Plan To Safeguard Existing Brand Position Marketing Guide To Manage Brand. Use it as a tool for discussion and navigation on Competitive, Advertisement, Consumers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Essential Initiatives To Safeguard Addressing Employee Crisis Prevention
Essential Initiatives To Safeguard Addressing Employee Crisis PreventionThe crisis management team should assist employees so that they can avoid the crisis before it hits. The firm should ensure that employee behave loyally and lawfully, refraining from any kind of misconduct. Present the topic in a bit more detail with this Essential Initiatives To Safeguard Addressing Employee Crisis Prevention. Use it as a tool for discussion and navigation on Communication Mode, Addressing Employee, Crisis Prevention This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Essential Initiatives To Safeguard Crisis Management Team Training Schedule
Essential Initiatives To Safeguard Crisis Management Team Training ScheduleThe crisis management team needs to have strong critical thinking skills and capable in taking key decisions without complete or conflicting information under immense tensed situations. The team will be trained by experts who will also use scenario based activities and costing will be per employee basis. Present the topic in a bit more detail with this Essential Initiatives To Safeguard Crisis Management Team Training Schedule. Use it as a tool for discussion and navigation on Hypotheticals, Workshops, Simulations, Team Training Schedule This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Essential Initiatives To Safeguard Role Of Management In Effective Corporate Security Governance
Essential Initiatives To Safeguard Role Of Management In Effective Corporate Security GovernanceThis slide portrays information regarding the responsibilities that are to be performed by board of directors, senior executives, steering committees and chief security office in order to ensure the effective corporate security governance. Deliver an outstanding presentation on the topic using this Essential Initiatives To Safeguard Role Of Management In Effective Corporate Security Governance. Dispense information and present a thorough explanation of Measuring Performance, Risk Management, Strategic Alignment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Essential Initiatives To Safeguard Selecting Suitable It Department Activities Monitoring Tool
Essential Initiatives To Safeguard Selecting Suitable It Department Activities Monitoring ToolThis slide provides information regarding selection of potential IT infrastructure monitoring tool through comparative assessment based on various features such as real time visibility, capacity planning, network infrastructure monitoring, etc. along with costs. Deliver an outstanding presentation on the topic using this Essential Initiatives To Safeguard Selecting Suitable It Department Activities Monitoring Tool. Dispense information and present a thorough explanation of Network Infrastructure Monitoring, Virtual Machine Monitoring, Real Time Visibility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Essential Initiatives To Safeguard Various It Threats Risk Management Plan
Essential Initiatives To Safeguard Various It Threats Risk Management PlanThis slide provides information regarding several IT threats risk management plan including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Essential Initiatives To Safeguard Various It Threats Risk Management Plan. Use it as a tool for discussion and navigation on Malicious Human Attack, Vulnerability, It Threats, Risk Management Plan This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Case Study Citrix Solutions To Safeguard Network Security Using Secure Web Gateway
Case Study Citrix Solutions To Safeguard Network Security Using Secure Web GatewayThis slide depicts the services offered by Citrix solutions to protect networks from web-based threats. These are comprehensive SWG, more private architecture based on instances and cloud delivery. This slide also talks about the benefits of SWG to IT directors. Present the topic in a bit more detail with this Case Study Citrix Solutions To Safeguard Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Organizational, Solutions, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Healthcare Cybersecurity And Multipurpose Safeguards Plan
Healthcare Cybersecurity And Multipurpose Safeguards PlanThis slide presents healthcare physical safeguards and cybersecurity plan, helpful in identifying required measures taken for safety of various components through their effective applicability. It includes administrative safeguards, technical safeguards and security policies. Presenting our well structured Healthcare Cybersecurity And Multipurpose Safeguards Plan. The topics discussed in this slide are Physical Safeguards, Technical Safeguards. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Encryption Implementation Strategies Encryption As A Service Providers To Safeguard Network
Encryption Implementation Strategies Encryption As A Service Providers To Safeguard NetworkThis slide outlines the companies which provide EaaS services to secure data in a network. The purpose of this slide is to demonstrate the services and benefits of several EaaS providers such as CloudHesive, FortKnoxter, Hashicrop, Identos, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Encryption As A Service Providers To Safeguard Network. Dispense information and present a thorough explanation of Encryption As A Service, Safeguard Network Communication, Internal Revocation System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption To Safeguard Network Communication Encryption For Data Privacy In Digital Age It
Encryption To Safeguard Network Communication Encryption For Data Privacy In Digital Age ItThis slide outlines the companies which provide EaaS services to secure data in a network. The purpose of this slide is to demonstrate the services and benefits of several EaaS providers such as CloudHesive, FortKnoxter, Hashicrop, Identos, etc. Deliver an outstanding presentation on the topic using this Encryption To Safeguard Network Communication Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Service, Communication, Demonstrate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Safeguarding User Identity Using Multi Factor Authentication Tools
Safeguarding User Identity Using Multi Factor Authentication ToolsThis slide displays multi factor tools for enhancing authentication processes by requiring users to provide multiple forms of identification before granting access to system. It includes basis such as software tools, outline, pricing and rating. Introducing our Safeguarding User Identity Using Multi Factor Authentication Tools set of slides. The topics discussed in these slides are Identity, Tools, Safeguarding. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cybersecurity Checklist To Safeguard Saas Applications
Cybersecurity Checklist To Safeguard Saas ApplicationsThis slide depicts the cybersecurity checklist to safeguard SaaS applications. The purpose of this slide is to help guarantee all the tasks are completed. It includes elements such as employees, development, etc. Introducing our Cybersecurity Checklist To Safeguard Saas Applications set of slides. The topics discussed in these slides are Employees, Development, Security Testing This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Blockchain Use Cases In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SS
Blockchain Use Cases In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SSThis slide showcases blockchain use cases in IoT systems that ensure all connected devices are secure and protected from cyber threats. It include industries such as supply chain and logistics, smart city, smart homes, and pharmacy.Deliver an outstanding presentation on the topic using this Blockchain Use Cases In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Security Functions, Enhance Trackability, Enhance Mobility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Categorization Of IoT Architecture Security Concerns IoT Security And Privacy Safeguarding IoT SS
Categorization Of IoT Architecture Security Concerns IoT Security And Privacy Safeguarding IoT SSThis slide consists of security concerns in each IoT architecture layer that helps to deploy a more secure security framework. It includes various security concerns such as insecure web interface, insufficient data authentication, insecure network services, etc. Present the topic in a bit more detail with this Categorization Of IoT Architecture Security Concerns IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Insecure Cloud Interface, Insecure Mobile Interface, Insecure Security Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Processing And Storage System Security Measures IoT Security And Privacy Safeguarding IoT SS
Data Processing And Storage System Security Measures IoT Security And Privacy Safeguarding IoT SSThis slide includes security measures to address security and data privacy concerns of IoT architecture processing layer. It includes three elements such as cloud storage, data center, and web services. Deliver an outstanding presentation on the topic using this Data Processing And Storage System Security Measures IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Data Tampering, Strong Authentications, Regular Hardware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SS
Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SSThis slide exhibits key activities and tools for monitoring and diagnostics of IoT device security. It includes activities such as continuous monitoring, anomaly detection, vulnerability scanning, auditing and reporting, etc. Present the topic in a bit more detail with this Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Vulnerability Scanning, Auditing Reporting, Anomaly Detection . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IoT Communication Protocol Security Concerns IoT Security And Privacy Safeguarding IoT SS
IoT Communication Protocol Security Concerns IoT Security And Privacy Safeguarding IoT SSThis slide outlines key communication protocols that facilitate data exchange within IoT devices. It covers communication protocols such as wireless frequencies, Bluetooth, Zigbee, and LPWAN. Present the topic in a bit more detail with this IoT Communication Protocol Security Concerns IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Wearables Devices, Personal Devices, Jamming Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IoT Device Management Platforms Comparison IoT Security And Privacy Safeguarding IoT SS
IoT Device Management Platforms Comparison IoT Security And Privacy Safeguarding IoT SSThis slide displays the most popular IoT device management platforms that help to automate connected device monitoring. It includes platforms such as Bytebeam, Cico IoT, Azure IoT Hub, and AWS IoT Core. Deliver an outstanding presentation on the topic using this IoT Device Management Platforms Comparison IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Cloud Integration, Device Connectivity, Pricing Flexibility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IoT Device Updates And Maintenance Schedule IoT Security And Privacy Safeguarding IoT SS
IoT Device Updates And Maintenance Schedule IoT Security And Privacy Safeguarding IoT SSThis slide exhibits device updates and maintenance task schedules that help to protect systems from vulnerabilities. It includes various tasks such as software updates, battery replacement, data backup, security audit, etc. Present the topic in a bit more detail with this IoT Device Updates And Maintenance Schedule IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Determine Vulnerabilities, Utilise Scanning, Software Update. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IoT Incident Response Management Process IoT Security And Privacy Safeguarding IoT SS
IoT Incident Response Management Process IoT Security And Privacy Safeguarding IoT SSThis slide contains a checklist that helps organisations to effectively manage and recover from security incidents. It includes steps such as preparation, identification, containment, eradication, recovery, and re testing. Present the topic in a bit more detail with this IoT Incident Response Management Process IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Disconnect Infected, Mitigate Malicious, Infected Systems. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Real Life Examples Of IoT Security Breaches Incident IoT Security And Privacy Safeguarding IoT SS
Real Life Examples Of IoT Security Breaches Incident IoT Security And Privacy Safeguarding IoT SSThis slide exhibits real life examples of IoT security breaches and their potential consequences including Mirai botnet, Stuxnet, and Jeep Cherokee hack. It includes elements such as security attack, year of occurrence, targeted device, attack method, and impact. Deliver an outstanding presentation on the topic using this Real Life Examples Of IoT Security Breaches Incident IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Exploited Default, Extensive Internet, Disrupted Industrial Operations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Attacks At Various Stages Of IoT Process IoT Security And Privacy Safeguarding IoT SS
Security Attacks At Various Stages Of IoT Process IoT Security And Privacy Safeguarding IoT SSThis slide showcases various types of attacks categorised for IoT data processes. It includes phases such as data perception, data storage, intelligent processing, data transmission, and end to end delivery. Present the topic in a bit more detail with this Security Attacks At Various Stages Of IoT Process IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Intelligent Processing, Data Transmission, Transmission Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Concerns And Solutions For Interconnected IoT Security And Privacy Safeguarding IoT SS
Security Concerns And Solutions For Interconnected IoT Security And Privacy Safeguarding IoT SSThis slide exhibits security solution to safeguard interconnected devices against security attacks in order to enhance overall productivity. It includes devices such as smart cameras, RFID tags, Smart GPS systems, and smart home devices, smart meters. Deliver an outstanding presentation on the topic using this Security Concerns And Solutions For Interconnected IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Manipulating Video Streams, Creating Unauthorized, Network Segmentation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cybersecurity Crisis Leadership To Safeguard Digital Assets
Cybersecurity Crisis Leadership To Safeguard Digital AssetsThe purpose of this slide is to highlight how cybersecurity crisis leadership safeguards digital assets with proactive strategies, incident response protocols, and fostering organizational resilience against cyber threats. Deliver an outstanding presentation on the topic using this Cybersecurity Crisis Leadership To Safeguard Digital Assets. Dispense information and present a thorough explanation of Tone For Preparedness, Culture Of Vigilance, Adequate Resources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vital Record Safeguarding Emergency Management Plan
Vital Record Safeguarding Emergency Management PlanThis slide showcases the record safekeeping management plan by using cloud drive, HR database and safety vault. Presenting our well structured Vital Record Safeguarding Emergency Management Plan The topics discussed in this slide are Alternate Backup, Backup Status, Safeguarding Emergency This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Comparative Assessment Of Platforms Based On Dlp Safeguarding Business With Data Loss Cybersecurity SS
Comparative Assessment Of Platforms Based On Dlp Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding the comparative analysis of various data loss prevention platforms based on features such as cloud app protection, optical character recognition, database discovery support, etc.Deliver an outstanding presentation on the topic using this Comparative Assessment Of Platforms Based On Dlp Safeguarding Business With Data Loss Cybersecurity SS. Dispense information and present a thorough explanation of Database Discovery Support, Data Discovery Across, Native Endpoint Behavioral Analytics using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Determining Data Loss Impact Due To Cyber Threat Safeguarding Business With Data Loss Cybersecurity SS
Determining Data Loss Impact Due To Cyber Threat Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding impact of data loss due to threat agents such as insider threat, social engineering, malware, specific enterprise cyber threats, etc.Present the topic in a bit more detail with this Determining Data Loss Impact Due To Cyber Threat Safeguarding Business With Data Loss Cybersecurity SS. Use it as a tool for discussion and navigation on Insider Threat, Social Engineering, Maintenance Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Email Dlp And Encryption Prevent Potential Data Safeguarding Business With Data Loss Cybersecurity SS
Email Dlp And Encryption Prevent Potential Data Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding email data loss prevention with exact data matching, email fraud prevention, deep analysis, fingerprinting, and automate regulatory compliance.Deliver an outstanding presentation on the topic using this Email Dlp And Encryption Prevent Potential Data Safeguarding Business With Data Loss Cybersecurity SS. Dispense information and present a thorough explanation of Focus Areas, Activities Performed, Overall Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Training Program For Workforce Safeguarding Business With Data Loss Cybersecurity SS
Information Security Training Program For Workforce Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding training program to ensure information security at workplace by considering focus areas such as data security and encryption, network security, incident response, etc.Deliver an outstanding presentation on the topic using this Information Security Training Program For Workforce Safeguarding Business With Data Loss Cybersecurity SS. Dispense information and present a thorough explanation of Duration, Delivery Method, Assessment, Cost, Modules using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Phase 1 Of Dlp Success Develop Information Risk Safeguarding Business With Data Loss Cybersecurity SS
Phase 1 Of Dlp Success Develop Information Risk Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding the development of an information risk profile for successful data loss prevention execution. It will include a statement of potential consequences, a description of data types in scope, etc.Present the topic in a bit more detail with this Phase 1 Of Dlp Success Develop Information Risk Safeguarding Business With Data Loss Cybersecurity SS. Use it as a tool for discussion and navigation on Risk Likelihood, Risk Level, Remedies, Risk Severity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Phase 2 Assess Incident Response Based On Severity Safeguarding Business With Data Loss Cybersecurity SS
Phase 2 Assess Incident Response Based On Severity Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding the assessment of incident response in context with severity and channel opted for. The channels include web, email, FTTP, network printer, cloud applications, etc.Deliver an outstanding presentation on the topic using this Phase 2 Assess Incident Response Based On Severity Safeguarding Business With Data Loss Cybersecurity SS. Dispense information and present a thorough explanation of Channels, Objective, Comments, Cloud Applications using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Phase 2 Of Dlp Success Map Data Incident Severity And Safeguarding Business With Data Loss Cybersecurity SS
Phase 2 Of Dlp Success Map Data Incident Severity And Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding the mapping of data incident severity and response chart for successful data loss prevention execution. It will include personal identifiable information, financial information, etc.Present the topic in a bit more detail with this Phase 2 Of Dlp Success Map Data Incident Severity And Safeguarding Business With Data Loss Cybersecurity SS. Use it as a tool for discussion and navigation on Impact Rating Legend, Regulations, Objective. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Phase 3 Of Dlp Success Build Technical Framework Safeguarding Business With Data Loss Cybersecurity SS
Phase 3 Of Dlp Success Build Technical Framework Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding the development of technical framework for successful data loss prevention execution. It will include key initiatives such as install or tune, monitor, risk mitigation, endpoint deployment, etc.Deliver an outstanding presentation on the topic using this Phase 3 Of Dlp Success Build Technical Framework Safeguarding Business With Data Loss Cybersecurity SS. Dispense information and present a thorough explanation of Risk Mitigation, Executive Update, Endpoints Deployment, Program Update using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Roles And Responsibilities Associated With Safeguarding Business With Data Loss Cybersecurity SS
Roles And Responsibilities Associated With Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding essential roles aligned with firms security team in terms of administrator, incident manager, investigator and auditor.Deliver an outstanding presentation on the topic using this Roles And Responsibilities Associated With Safeguarding Business With Data Loss Cybersecurity SS. Dispense information and present a thorough explanation of Incident Manager, Administrator, Investigator, Auditor using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Suitable Data Loss Prevention Vendor Selection Safeguarding Business With Data Loss Cybersecurity SS
Suitable Data Loss Prevention Vendor Selection Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding selection of suitable vendor by firms size, platform suitability, deployment scenario, ratings, etc.Deliver an outstanding presentation on the topic using this Suitable Data Loss Prevention Vendor Selection Safeguarding Business With Data Loss Cybersecurity SS. Dispense information and present a thorough explanation of Description, Platforms, Deployment, Ratings using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Dlp Approaches Enterprise Vs Integrated Data Loss Safeguarding Business With Data Loss Cybersecurity SS
Dlp Approaches Enterprise Vs Integrated Data Loss Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding the comparison of DLP approaches namely enterprise and integrated data loss prevention on various parameters such as deployment, policy management, use case, etc.Deliver an outstanding presentation on the topic using this Dlp Approaches Enterprise Vs Integrated Data Loss Safeguarding Business With Data Loss Cybersecurity SS. Dispense information and present a thorough explanation of Deployment, Policy Management, Management, Vendor Ecosystem using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Sustainability Report Safeguarding Products Bearing Animated Characters Sustainability SS
Social Sustainability Report Safeguarding Products Bearing Animated Characters Sustainability SSThis slide covers details related to initiatives taken by media and entertainment company to safeguard products bearing brands animated characters. It includes details related to chemical management policies, supply chain code of conduct etc. Present the topic in a bit more detail with this Social Sustainability Report Safeguarding Products Bearing Animated Characters Sustainability SS. Use it as a tool for discussion and navigation on Centralized Oversight, Chemical Management Policies, Supply Chain Code Of Conduct, Testing And Review Procedures. This template is free to edit as deemed fit for your organization. Therefore download it now.


