Powerpoint Templates and Google slides for Protect Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Server Storage Icons Network Technology Protection Database Symbol
Server Storage Icons Network Technology Protection Database SymbolIt covers all the important concepts and has relevant templates which cater to your business needs. This complete deck has PPT slides on Server Storage Icons Network Technology Protection Database Symbol with well suited graphics and subject driven content. This deck consists of total of twelve slides. All templates are completely editable for your convenience. You can change the colour, text and font size of these slides. You can add or delete the content as per your requirement. Get access to this professionally designed complete deck presentation by clicking the download button below.
-
 Cyber Security Icon Network Protection Threat Server Database Software
Cyber Security Icon Network Protection Threat Server Database SoftwareKeep your audience glued to their seats with professionally designed PPT slides. This deck comprises of total of twelve slides. It has PPT templates with creative visuals and well researched content. Not just this, our PowerPoint professionals have crafted this deck with appropriate diagrams, layouts, icons, graphs, charts and more. This content ready presentation deck is fully editable. Just click the DOWNLOAD button below. Change the colour, text and font size. You can also modify the content as per your need. Get access to this well crafted complete deck presentation and leave your audience stunned.
-
 Cloud Security Icon Security Computing Data Protection Digital Access
Cloud Security Icon Security Computing Data Protection Digital AccessKeep your audience glued to their seats with professionally designed PPT slides. This deck comprises of total of twelve slides. It has PPT templates with creative visuals and well researched content. Not just this, our PowerPoint professionals have crafted this deck with appropriate diagrams, layouts, icons, graphs, charts and more. This content ready presentation deck is fully editable. Just click the DOWNLOAD button below. Change the colour, text and font size. You can also modify the content as per your need. Get access to this well crafted complete deck presentation and leave your audience stunned.
-
 Privacy Technology Database Protection Organizations Information
Privacy Technology Database Protection Organizations InformationIf you require a professional template with great design, then this Privacy Technology Database Protection Organizations Information is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using twelve slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well-structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
 Implementing security management plan to reduce threats and protect sensitive company data complete deck
Implementing security management plan to reduce threats and protect sensitive company data complete deckThis complete deck covers various topics and highlights important concepts. It has PPT slides which cater to your business needs. This complete deck presentation emphasizes Implementing Security Management Plan To Reduce Threats And Protect Sensitive Company Data Complete Deck and has templates with professional background images and relevant content. This deck consists of total of fourty two slides. Our designers have created customizable templates, keeping your convenience in mind. You can edit the colour, text and font size with ease. Not just this, you can also add or delete the content if needed. Get access to this fully editable complete presentation by clicking the download button below.
-
 Blockchain security data protection risk control incident management
Blockchain security data protection risk control incident managementEngage buyer personas and boost brand awareness by pitching yourself using this prefabricated set. This Blockchain Security Data Protection Risk Control Incident Management is a great tool to connect with your audience as it contains high-quality content and graphics. This helps in conveying your thoughts in a well-structured manner. It also helps you attain a competitive advantage because of its unique design and aesthetics. In addition to this, you can use this PPT design to portray information and educate your audience on various topics. With twelve slides, this is a great design to use for your upcoming presentations. Not only is it cost-effective but also easily pliable depending on your needs and requirements. As such color, font, or any other design component can be altered. It is also available for immediate download in different formats such as PNG, JPG, etc. So, without any further ado, download it now.
-
 Ways protect ecommerce customer data ppt powerpoint presentation professional diagrams cpb
Ways protect ecommerce customer data ppt powerpoint presentation professional diagrams cpbPresenting our Ways Protect Ecommerce Customer Data Ppt Powerpoint Presentation Professional Diagrams Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Ways Protect Ecommerce Customer Data This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
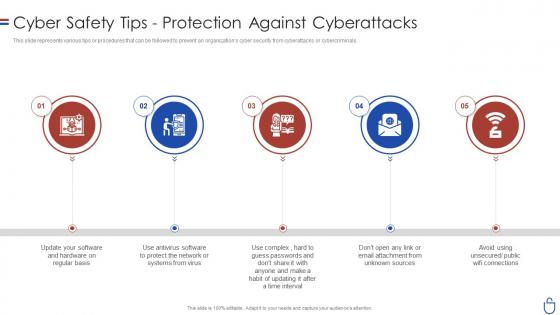 Data security it cyber safety tips protection against cyberattacks
Data security it cyber safety tips protection against cyberattacksThis slide represents various tips or procedures that can be followed to prevent an organizations cyber security from cyberattacks or cybercriminals. Increase audience engagement and knowledge by dispensing information using Data Security IT Cyber Safety Tips Protection Against Cyberattacks. This template helps you present information on five stages. You can also present information on Sources, Public Wifi Connections, Time Interval, Protect Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Protection Audit Schedule Lifecycle
Data Protection Audit Schedule LifecycleThe slide showcases a data protection audit process that involves a number of activities and phases that may occur over an extended period of time. The slide includes elements such as audit planning, eternal audit, internal audit, risk assessment scheduling, internal audit schedule creation, etc. Introducing our Data Protection Audit Schedule Lifecycle set of slides. The topics discussed in these slides are External Audit, Audit Planning, Internal Audit. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Confidential Computing Hardware Technologies Used To Protect Data In Use
Confidential Computing Hardware Technologies Used To Protect Data In UseThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Present the topic in a bit more detail with this Confidential Computing Hardware Technologies Used To Protect Data In Use. Use it as a tool for discussion and navigation on Protect The Information In Processing, Security And Scalability, Homomorphic Encryption, Multi Party Computation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention Security Software To Protect Business From Data Breach
Data Breach Prevention Security Software To Protect Business From Data BreachThe purpose of this slide is to highlight the available security tools to stay safe from data breaches. The popular security software are access control solutions, Security Information And Event Management SIEM tools, and antivirus software. Increase audience engagement and knowledge by dispensing information using Data Breach Prevention Security Software To Protect Business From Data Breach. This template helps you present information on three stages. You can also present information on Security Information And Event Management, Amends Permissions As Needed, Security Software To Protect Business using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Confidential Computing Market Technologies Used To Protect Data In Use
Confidential Computing Market Technologies Used To Protect Data In UseThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Present the topic in a bit more detail with this Confidential Computing Market Technologies Used To Protect Data In Use. Use it as a tool for discussion and navigation on Technologies, Demonstrates, Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Datafication Of HR Measures Taken For Data Protection In Cloud Globally
Datafication Of HR Measures Taken For Data Protection In Cloud GloballyThis slide represents the measures taken for data protection in the cloud worldwide, covering multi-factor authentication, cloud backup, encryption, employee training, auditing of user activity, review of access rights, data classification, and removing sensitive data from the cloud. Deliver an outstanding presentation on the topic using this Datafication Of HR Measures Taken For Data Protection In Cloud Globally. Dispense information and present a thorough explanation of Measures, Protection, Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Datafication Framework Measures Taken For Data Protection In Cloud Globally
Datafication Framework Measures Taken For Data Protection In Cloud GloballyThis slide represents the measures taken for data protection in the cloud worldwide, covering multi-factor authentication, cloud backup, encryption, employee training, auditing of user activity, review of access rights, data classification, and removing sensitive data from the cloud. Present the topic in a bit more detail with this Datafication Framework Measures Taken For Data Protection In Cloud Globally. Use it as a tool for discussion and navigation on Measures, Information, Enterprises. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Datafication In Data Science Measures Taken For Data Protection In Cloud Globally
Datafication In Data Science Measures Taken For Data Protection In Cloud GloballyThis slide represents the measures taken for data protection in the cloud worldwide, covering multi factor authentication, cloud backup, encryption, employee training, auditing of user activity, review of access rights, data classification, and removing sensitive data from the cloud.Deliver an outstanding presentation on the topic using this Datafication In Data Science Measures Taken For Data Protection In Cloud Globally. Dispense information and present a thorough explanation of Digital Platforms, Encryption Features, Security Measures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing Consortium Technologies Used To Protect Data In Use
Confidential Computing Consortium Technologies Used To Protect Data In UseThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Deliver an outstanding presentation on the topic using this Confidential Computing Consortium Technologies Used To Protect Data In Use. Dispense information and present a thorough explanation of Protecting Technologies, Security And Scalability, Technologies Homomorphic Encryption, Multi Party Computation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Network Security Challenges And Solution For Protecting Data
Network Security Challenges And Solution For Protecting DataThis slide showcase solution and challenges for network security. The main purpose for this template is to save company data from getting into hands of rival businesses. This includes data theft, insider threat, password attack, etc. Presenting our set of slides with Network Security Challenges And Solution For Protecting Data. This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Challenges, Solution.
-
 Network Security Highlighting Important Steps For Protecting Data
Network Security Highlighting Important Steps For Protecting DataThis slide showcase steps of network security. The main reason for this slide is showcasing management of network without any uninterrupted operations. This includes internal networks, protection security, cyber security, etc. Presenting our well structured Network Security Highlighting Important Steps For Protecting Data. The topics discussed in this slide are Internal Network, Protected Payment.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Network Security Icon For Protecting Data From Theft
Network Security Icon For Protecting Data From TheftIntroducing our Network Security Icon For Protecting Data From Theft set of slides. The topics discussed in these slides are Network Security Protecting Data. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Network Security Icon For Protecting Database
Network Security Icon For Protecting DatabasePresenting our well structured Network Security Icon For Protecting Database. The topics discussed in this slide are Network Security Protecting Database.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Network Security Tips For Protecting Important Data
Network Security Tips For Protecting Important DataThese slide showcase ways of protecting network security. The main purpose of this template is how to keep office data safe from any kind of theft, this includes careful grant access, strong password, secure servers, text security. Presenting our set of slides with Network Security Tips For Protecting Important Data. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Careful Grant Access, Strong Password.
-
 Impact Of Digital Therapeutics On Data Protection Digital Therapeutics Regulatory
Impact Of Digital Therapeutics On Data Protection Digital Therapeutics RegulatoryThis slide talks about the positive and negative impact of digital therapeutics on information protection. The negative includes the regular patient observation and profiling, the significant impact of personal information breaches, and security issues due to complexity. Introducing Impact Of Digital Therapeutics On Data Protection Digital Therapeutics Regulatory to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Positive, Negative, using this template. Grab it now to reap its full benefits.
-
 Icon For Ensuring Data Protection In Digital Transformation For Local Government
Icon For Ensuring Data Protection In Digital Transformation For Local GovernmentIntroducing our Icon For Ensuring Data Protection In Digital Transformation For Local Government set of slides. The topics discussed in these slides are Icon Ensuring, Data Protection, Digital Transformation. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Impact analysis of data protection to meet GDPR requirements
Impact analysis of data protection to meet GDPR requirementsThis slide highlights data protection impact assessment to meet GDPR requirements. The purpose of this slide is to support businesses in meeting GDPR compliance requirements. It provides details changes, sources of data risk, probability and degree of harm, etc. Presenting our well structured Impact analysis of data protection to meet GDPR requirements. The topics discussed in this slide are Inadequate Documentation, Comprehensive Inventory, Update Privacy. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Corporate Data Protection Policy In Powerpoint And Google Slides Cpb
Corporate Data Protection Policy In Powerpoint And Google Slides CpbPresenting Corporate Data Protection Policy In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Corporate Data Protection Policy. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Digital Therapeutics Development Impact Of Digital Therapeutics On Data Protection
Digital Therapeutics Development Impact Of Digital Therapeutics On Data ProtectionThis slide talks about the positive and negative impact of digital therapeutics on information protection. The negative includes the regular patient observation and profiling, the significant impact of personal information breaches, and security issues due to complexity. Introducing Digital Therapeutics Development Impact Of Digital Therapeutics On Data Protection to increase your presentation threshold. Encompassed with Two stages, this template is a great option to educate and entice your audience. Dispence information on Positive, Negative, using this template. Grab it now to reap its full benefits.
-
 Ensure Compliance With Data Protection Laws Developing Shareholder Trust With Efficient Strategy SS V
Ensure Compliance With Data Protection Laws Developing Shareholder Trust With Efficient Strategy SS VThis slide presents an overview of data protection regulations. It includes aspects such as regulation , purpose, applicability and key points. Introducing Ensure Compliance With Data Protection Laws Developing Shareholder Trust With Efficient Strategy SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Regulation, Purpose, Applicability, using this template. Grab it now to reap its full benefits.
-
 Ensure Compliance With Data Protection Laws And Regulations Strategies To Comply Strategy SS V
Ensure Compliance With Data Protection Laws And Regulations Strategies To Comply Strategy SS VThis slide presents an overview of data protection regulations. It includes aspects such as regulation , purpose, applicability and key points. Present the topic in a bit more detail with this Ensure Compliance With Data Protection Laws And Regulations Strategies To Comply Strategy SS V. Use it as a tool for discussion and navigation on Regulation, Purpose, Applicability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Guidelines For Implementing Data Protection Regulations Strategies To Comply Strategy SS V
Guidelines For Implementing Data Protection Regulations Strategies To Comply Strategy SS VThis slide presents data protection policies and procedures to ensure data compliance in the company. It includes information about data classification, access control, incident response and data privacy policy. Present the topic in a bit more detail with this Guidelines For Implementing Data Protection Regulations Strategies To Comply Strategy SS V. Use it as a tool for discussion and navigation on Data Classification Policy, Access Control Policy, Incident Response Policy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Protection Privacy In Powerpoint And Google Slides Cpb
Data Protection Privacy In Powerpoint And Google Slides CpbPresenting Data Protection Privacy In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Data Protection Privacy. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
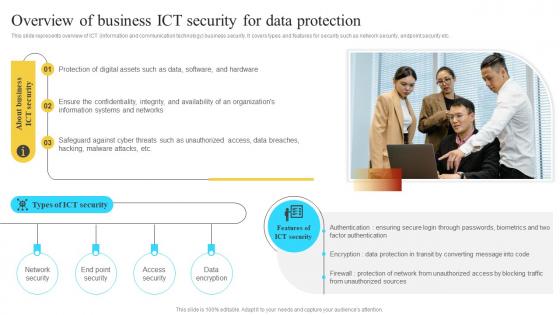 Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V
Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Protection Of Digital, Safeguard Against Cyber, using this template. Grab it now to reap its full benefits.
-
 Ensure Compliance With Data Protection Corporate Regulatory Compliance Strategy SS V
Ensure Compliance With Data Protection Corporate Regulatory Compliance Strategy SS VThis slide presents an overview of data protection regulations. It includes aspects such as regulation, purpose, applicability and key points. Present the topic in a bit more detail with this Ensure Compliance With Data Protection Corporate Regulatory Compliance Strategy SS V. Use it as a tool for discussion and navigation on Regulation, Purpose. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Guidelines For Implementing Data Protection Corporate Regulatory Compliance Strategy SS V
Guidelines For Implementing Data Protection Corporate Regulatory Compliance Strategy SS VThis slide presents data protection policies and procedures to ensure data compliance in the company. It includes information about data classification, access control, incident response and data privacy policy. Present the topic in a bit more detail with this Guidelines For Implementing Data Protection Corporate Regulatory Compliance Strategy SS V. Use it as a tool for discussion and navigation on Data Classification Policy, Access Control Policy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Client Side Encryption To Protect Cloud Data Cloud Data Encryption
Client Side Encryption To Protect Cloud Data Cloud Data EncryptionThis slide discusses client side encryption to protect the data after storing it in the cloud network. This slide also highlights the importance of client side encryption in different scenarios, such as secure collaboration, protection against cloud provider vulnerabilities, etc. Introducing Client Side Encryption To Protect Cloud Data Cloud Data Encryption to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Following Scenarios, Encrypted, using this template. Grab it now to reap its full benefits.
-
 Server Side Encryption To Protect Cloud Data Cloud Data Encryption
Server Side Encryption To Protect Cloud Data Cloud Data EncryptionThis slide discusses server side encryption to protect the data after storing it in the cloud network. This slide also highlights the importance of server side encryption in different scenarios, such as compliance and regulatory requirements, data backup, etc. Present the topic in a bit more detail with this Server Side Encryption To Protect Cloud Data Cloud Data Encryption. Use it as a tool for discussion and navigation on Readable, Overview. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Secured Data Protection For Online Security System Icon
Secured Data Protection For Online Security System IconPresenting our set of slides with Secured Data Protection For Online Security System Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Secured Data Protection, Online Security System Icon.
-
 Technologies Used To Protect Data In Use Confidential Computing System Technology
Technologies Used To Protect Data In Use Confidential Computing System TechnologyThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Deliver an outstanding presentation on the topic using this Technologies Used To Protect Data In Use Confidential Computing System Technology. Dispense information and present a thorough explanation of Technologies, Security Comparison, Scalability Comparison using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ensure Compliance With Data Protection Laws And Regulations Effective Business Risk Strategy SS V
Ensure Compliance With Data Protection Laws And Regulations Effective Business Risk Strategy SS VThis slide represents techniques to effectively engaging employees and stakeholders in the compliance process. It includes strategies such as training programs, communication channels, feedback mechanisms, incentives and recognition and compliance committees. Increase audience engagement and knowledge by dispensing information using Ensure Compliance With Data Protection Laws And Regulations Effective Business Risk Strategy SS V. This template helps you present information on six stages. You can also present information on Training Programs, Communication Channels using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Protection Impact Assessment Under Gdpr Transforming Healthcare BCT SS
Data Protection Impact Assessment Under Gdpr Transforming Healthcare BCT SSThis slide showcases data protection impact assessment checklist used by healthcare providers or companies to investigate potential vulnerabilities and improve data privacy and compliance status. It include various requirements that are evaluated on the basis of their current stage. Present the topic in a bit more detail with this Data Protection Impact Assessment Under Gdpr Transforming Healthcare BCT SS. Use it as a tool for discussion and navigation on Describe The Processing, Identify And Assess Risks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Employee And Workplace Ensure Compliance With Data Protection Laws And Regulations Strategy SS V
Employee And Workplace Ensure Compliance With Data Protection Laws And Regulations Strategy SS VThis slide presents an overview of data protection regulations. It includes aspects such as regulation , purpose, applicability and key points. Deliver an outstanding presentation on the topic using this Employee And Workplace Ensure Compliance With Data Protection Laws And Regulations Strategy SS V Dispense information and present a thorough explanation of Regulatory Requirement, Training Objectives, Training Method using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Employee And Workplace Guidelines For Implementing Data Protection Regulations Strategy SS V
Employee And Workplace Guidelines For Implementing Data Protection Regulations Strategy SS VThis slide presents data protection policies and procedures to ensure data compliance in the company. It includes information about data classification, access control, incident response and data privacy policy.Increase audience engagement and knowledge by dispensing information using Employee And Workplace Guidelines For Implementing Data Protection Regulations Strategy SS V This template helps you present information on Four stages. You can also present information on Internal Review, External Audit, Compliance Surveys using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS V
Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Introducing Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Usage Policy, Data Encryption, using this template. Grab it now to reap its full benefits.
-
 Corporate Compliance Strategy Ensure Compliance With Data Protection Laws Strategy SS V
Corporate Compliance Strategy Ensure Compliance With Data Protection Laws Strategy SS VThis slide presents an overview of data protection regulations. It includes aspects such as regulation , purpose, applicability and key points. Present the topic in a bit more detail with this Corporate Compliance Strategy Ensure Compliance With Data Protection Laws Strategy SS V Use it as a tool for discussion and navigation on Implement RiskAccountability, Conduct Timely RiskAssessments This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Corporate Compliance Strategy Guidelines For Implementing Data Protection Regulations Strategy SS V
Corporate Compliance Strategy Guidelines For Implementing Data Protection Regulations Strategy SS VThis slide presents data protection policies and procedures to ensure data compliance in the company. It includes information about data classification, access control, incident response and data privacy policy. Introducing Corporate Compliance Strategy Guidelines For Implementing Data Protection Regulations Strategy SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Workplace Safety Compliance, Recordkeeping Compliance, Employment Law Compliance using this template. Grab it now to reap its full benefits.
-
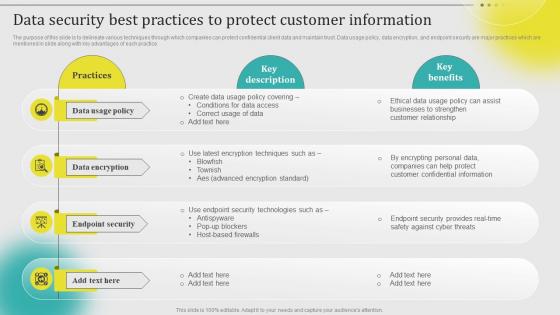 Data Security Best Practices To Protect Customer Information Leveraging Customer Data MKT SS V
Data Security Best Practices To Protect Customer Information Leveraging Customer Data MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Introducing Data Security Best Practices To Protect Customer Information Leveraging Customer Data MKT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Usage Policy, Data Encryption, Endpoint Security, using this template. Grab it now to reap its full benefits.
-
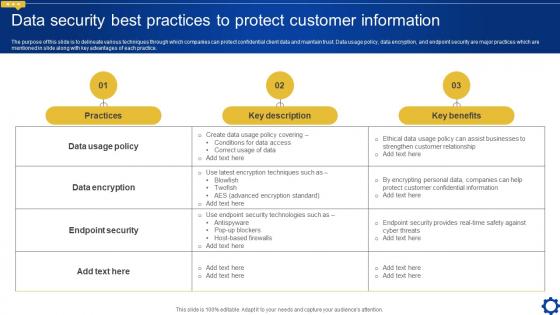 Data Security Best Practices To Protect Customer Creating Personalized Marketing Messages MKT SS V
Data Security Best Practices To Protect Customer Creating Personalized Marketing Messages MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Present the topic in a bit more detail with this Data Security Best Practices To Protect Customer Creating Personalized Marketing Messages MKT SS V. Use it as a tool for discussion and navigation on Practices, Key Description, Key Benefits. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Protect Customers Data In Powerpoint And Google Slides Cpb
Protect Customers Data In Powerpoint And Google Slides CpbPresenting Protect Customers Data In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Protect Customers Data. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Data Security Best Practices To Protect Complete Introduction To Database MKT SS V
Data Security Best Practices To Protect Complete Introduction To Database MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Increase audience engagement and knowledge by dispensing information using Data Security Best Practices To Protect Complete Introduction To Database MKT SS V. This template helps you present information on four stages. You can also present information on Policy, Encryption, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions
Encryption Implementation Strategies Challenges Of Data In Use Protection And SolutionsThis slide outlines the various limitations of data in use protection and their possible solutions. These include limited control after data access, unauthorized copying or sharing of data, limitations of collaboration platforms, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions. Use it as a tool for discussion and navigation on Limitations Of Collaboration Platforms, Unauthorized Copying Or Sharing Of Data, Limited Control After Data Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use
Encryption Implementation Strategies Data Protection Technologies To Secure Information In UseThis slide compares different data in use protection methods, and their working and associated cost. These methods are IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use. Use it as a tool for discussion and navigation on Identity Management Tools, Digital Rights Protection, Data Protection Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Different States Of Data Which Requires Protection
Encryption Implementation Strategies Different States Of Data Which Requires ProtectionThis slide discusses various customer demands to ensure data privacy and authenticity. The purpose of this slide is to highlight the various states of data that require encryption, such as data-at-rest, data-in-transit, and data-in-use. Introducing Encryption Implementation Strategies Different States Of Data Which Requires Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Customer Demands, Data Privacy And Authenticity, Require Encryption, Collaboration Software, using this template. Grab it now to reap its full benefits.
-
 Encryption Implementation Strategies Top Regulatory Compliance Frameworks For Data Protection
Encryption Implementation Strategies Top Regulatory Compliance Frameworks For Data ProtectionThe purpose of this slide is to summarize several relevant regulations. These are GDPR General Data Protection Regulation, CCPA California Consumer Privacy Act, PCI DSS Payment Card Industry Data Security Standard, NIST, and HIPAA, along with their descriptions and scopes. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Top Regulatory Compliance Frameworks For Data Protection. Dispense information and present a thorough explanation of General Data Protection Regulation, California Consumer Privacy Act, Health Insurance Portability And Accountability Act using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 File Protection And Data Theft Prevention Icon
File Protection And Data Theft Prevention IconPresenting our well structured File Protection And Data Theft Prevention Icon. The topics discussed in this slide are Protection, Data, Prevention. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Overview Cybersecurity And Data Protection Elevating Small And Medium Enterprises Digital Transformation DT SS
Overview Cybersecurity And Data Protection Elevating Small And Medium Enterprises Digital Transformation DT SSThis slide presents an overview into the landscape of cybersecurity and data protection with its advantages. It also presents a survey analysis on share of SMEs that have implemented essential and basic IT security initiatives. Deliver an outstanding presentation on the topic using this Overview Cybersecurity And Data Protection Elevating Small And Medium Enterprises Digital Transformation DT SS. Dispense information and present a thorough explanation of Digital Technologies, Organizations Digital, Digital Transformation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 US Cyber Security Solution Market Trend For Data Protection
US Cyber Security Solution Market Trend For Data ProtectionThis slide graphically represents market trend of US cyber security solutions for enhancing data protection and mitigating cyber attacks. It includes various growth drivers of solutions such as rising remote work culture, increasing cyber threats, etc. Introducing our US Cyber Security Solution Market Trend For Data Protection set of slides. The topics discussed in these slides are Key Insights, Market Size, Cybersecurity Solutions. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Deception Dashboard For Modern Data Protection
Cyber Deception Dashboard For Modern Data ProtectionThe purpose of this slide is to introduce a cyber deception dashboard for modern data protection, providing visual insights into threat activity by analyzing traps data, events timelines, etc. Introducing our Cyber Deception Dashboard For Modern Data Protection set of slides. The topics discussed in these slides are Statistics For Threat, Trap Events, Network Intelligence Events. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Protection Dashboard To Track Data Loss Safeguarding Business With Data Loss Cybersecurity SS
Cyber Protection Dashboard To Track Data Loss Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding cybersecurity dashboard to track activities such as malware blocked, vulnerabilities detected, patches ready to install, protection status, active alerts, to ensure minimum data loss.Present the topic in a bit more detail with this Cyber Protection Dashboard To Track Data Loss Safeguarding Business With Data Loss Cybersecurity SS. Use it as a tool for discussion and navigation on Protection Status, Active Alerts Summary, Activities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
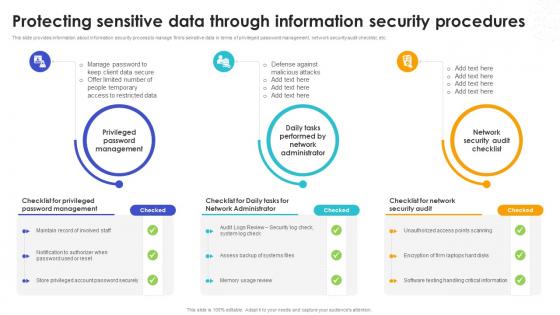 Protecting Sensitive Data Through Information Security Safeguarding Business With Data Loss Cybersecurity SS
Protecting Sensitive Data Through Information Security Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information about information security process to manage firms sensitive data in terms of privileged password management, network security audit checklist, etc.Introducing Protecting Sensitive Data Through Information Security Safeguarding Business With Data Loss Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Network Security Audit, Privileged Password Management, Network Administrator, using this template. Grab it now to reap its full benefits.
-
 Dashboard For Supply Chain Attack Management For Data Protection
Dashboard For Supply Chain Attack Management For Data ProtectionThis slide represents dashboard that helps companies to manage supply chain attacks for improving security management measures. It includes various components such a policy and compliance, resource security hygiene, and threat protection. Presenting our well structured Dashboard For Supply Chain Attack Management For Data Protection. The topics discussed in this slide are Policy And Compliance, Resource Security Hygiene, Threat Protection. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Tools To Address Supply Chain Cybersecurity Attacks For Data Protection
Tools To Address Supply Chain Cybersecurity Attacks For Data ProtectionThis slide graphically represents use of various tools and approaches that assist companies in addressing various supply chain cybersecurity attacks and optimizing data protection. It includes tools such as IT vendor risk management tools, supply chain risk management tools, etc. Presenting our well structured Tools To Address Supply Chain Cybersecurity Attacks For Data Protection. The topics discussed in this slide are Audits Of Suppliers, Manufacturers, Logistics Partners. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.



