Powerpoint Templates and Google slides for Plan Of Attack
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Security Plan To Prevent Cyber Summary Of Key Cyber Attacks Occurred
Security Plan To Prevent Cyber Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cybers Attacks, Phishing, Malware Attack, Denial Of Service, SQL Injections, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
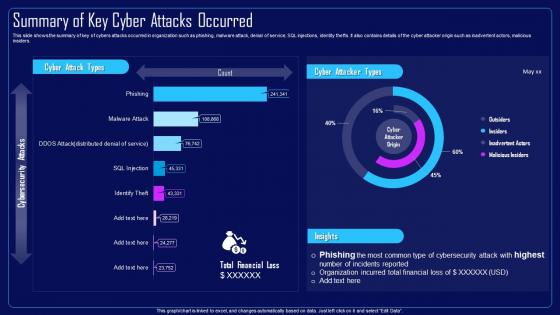 Action Plan To Combat Cyber Crimes Summary Of Key Cyber Attacks Occurred
Action Plan To Combat Cyber Crimes Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Action Plan To Combat Cyber Crimes Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cybers Attacks Occurred In Organization, Malware Attack, Denial Of Service, SQL Injections, Inadvertent Actors, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Compressive Planning Guide Summary Of Key Cyber Attacks Occurred
Compressive Planning Guide Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Compressive Planning Guide Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cybers Attacks Occurred, Malware Attack, Denial Of Service, Inadvertent Actors, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Statistics Of Existing It Infrastructure Attacks Vpn Implementation Plan
Statistics Of Existing It Infrastructure Attacks Vpn Implementation PlanThis slide discusses the issues faced by the organization due to existing IT infrastructure such as data interception, unauthorized access, etc.Present the topic in a bit more detail with this Statistics Of Existing It Infrastructure Attacks Vpn Implementation Plan. Use it as a tool for discussion and navigation on Sales, Finance, Marketing, Analytics. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Penetration Testing Implementation Plan Statistics Of It Infrastructure Attacks In Organization
Penetration Testing Implementation Plan Statistics Of It Infrastructure Attacks In OrganizationThis slide summarizes security attacks across different organizational departments, such as network operations centres, security operations centres, etc. The outlined departments such as network operations centre, security operation centre and so on. Deliver an outstanding presentation on the topic using this Penetration Testing Implementation Plan Statistics Of It Infrastructure Attacks In Organization. Dispense information and present a thorough explanation of Security Operations Center, Network Operations Center, Security Concerns using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat Map
Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat MapThis slide shows the mapping of cyber attacks based on the likelihood of risk occurrence and its impact. It also contains details of attacks segmentation and the control actions that must be taken such as track, monitor and mitigate against such cyber attacks. Deliver an outstanding presentation on the topic using this Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat Map. Dispense information and present a thorough explanation of Cyber Attacks, Risk Occurrence, Attacks Segmentation, Monitor And Mitigate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents For Security Plan To Prevent Cyber Attacks
Table Of Contents For Security Plan To Prevent Cyber AttacksIntroducing Table Of Contents For Security Plan To Prevent Cyber Attacks to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Risk Assessment Program, Cyber Attacks Identification, Cyber Attacks Faced By Organization, Cyber Attacks Risk Assessment, using this template. Grab it now to reap its full benefits.
-
 Action Plan To Combat Cyber Crimes Mapping Of Multiple Cyber Attacks Using Risk Heat Map
Action Plan To Combat Cyber Crimes Mapping Of Multiple Cyber Attacks Using Risk Heat MapThis slide shows the mapping of cyber attacks based on the likelihood of risk occurrence and its impact. It also contains details of attacks segmentation and the control actions that must be taken such as track, monitor and mitigate against such cyber attacks. Present the topic in a bit more detail with this Action Plan To Combat Cyber Crimes Mapping Of Multiple Cyber Attacks Using Risk Heat Map. Use it as a tool for discussion and navigation on Mapping Of Multiple Cyber Attacks, Risk Heat Map, Risk Occurrence, Attacks Segmentation And The Control Actions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Compressive Planning Guide Mapping Of Multiple Cyber Attacks Using Risk Heat Map
Compressive Planning Guide Mapping Of Multiple Cyber Attacks Using Risk Heat MapThis slide shows the mapping of cyber attacks based on the likelihood of risk occurrence and its impact. It also contains details of attacks segmentation and the control actions that must be taken such as track, monitor and mitigate against such cyber attacks. Deliver an outstanding presentation on the topic using this Compressive Planning Guide Mapping Of Multiple Cyber Attacks Using Risk Heat Map. Dispense information and present a thorough explanation of Cyber Attacks Segmentation, Phishing Attack, Fraudulently Obtain Sensitive Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Response Plan Possible Causes Of Data Breach Attack
Data Breach Response Plan Possible Causes Of Data Breach AttackThis slide highlights the reasons behind the success of data breach attack. These include phishing attacks, unpatched software, malware, insider threats, third-party vulnerabilities, SQL Structured Query Language injections, unsecured APIs, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Possible Causes Of Data Breach Attack. Dispense information and present a thorough explanation of Phishing Attacks, Unpatched Software, Third Party Vulnerabilities, Structured Query Language using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Application Security Implementation Plan Statistics Of It Infrastructure Attacks On Organization
Application Security Implementation Plan Statistics Of It Infrastructure Attacks On OrganizationThis slide summarizes security attacks across different organizational departments, such as IT, HR, Sales, Finance, etc. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Statistics Of IT Infrastructure Attacks On Organization. Dispense information and present a thorough explanation of Statistics Of IT Infrastructure, Attacks On Organization, Organizational Departments, Finance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Rising Number Of Information Security Attacks Risk Assessment And Management Plan For Information Security
Rising Number Of Information Security Attacks Risk Assessment And Management Plan For Information SecurityThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection Present the topic in a bit more detail with this Rising Number Of Information Security Attacks Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Organizations, Information, Cybersecurity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
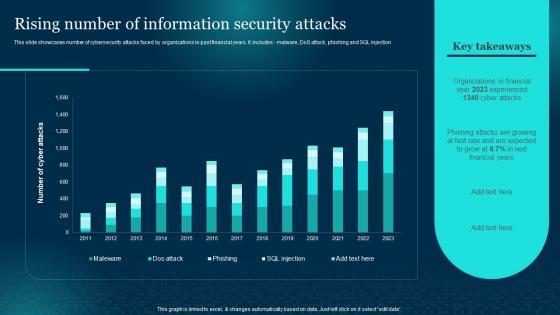 Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan
Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management PlanThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection Present the topic in a bit more detail with this Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Information, Security Attacks, Organizations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Rising Number Of Information Security Attacks Formulating Cybersecurity Plan
Rising Number Of Information Security Attacks Formulating Cybersecurity PlanThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection. Deliver an outstanding presentation on the topic using this Rising Number Of Information Security Attacks Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Rising Number, Information Security, Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization
Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By OrganizationThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization. Use it as a tool for discussion and navigation on Consequences, Data Breaches, Unintended Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Financial Impact Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan
Financial Impact Of Information Security Attacks Cybersecurity Risk Analysis And Management PlanThis slide showcases financial impact of different cyber security attacks on organizations. Its key elements are business disruption, information loss, revenue loss, equipment damage and total cost by attack type Present the topic in a bit more detail with this Financial Impact Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Financial, Information, Organizations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Financial Impact Of Information Security Attacks Formulating Cybersecurity Plan
Financial Impact Of Information Security Attacks Formulating Cybersecurity PlanThis slide showcases financial impact of different cyber security attacks on organizations. Its key elements are business disruption, information loss, revenue loss, equipment damage and total cost by attack type. Present the topic in a bit more detail with this Financial Impact Of Information Security Attacks Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Financial Impact, Information, Security Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Benefits Of Implementing Web Application Firewall
Cyber Security Attacks Response Plan Benefits Of Implementing Web Application FirewallThis slide represents the advantages of implementing a software which protects web applications from variety of application layer attacks. It includes key benefits of implementing web application firewall such as defense, fights vulnerabilities etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Benefits Of Implementing Web Application Firewall. Use it as a tool for discussion and navigation on Fights Vulnerabilities, Application Firewall, Confidential Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Common Sources Of Precursors And Indicators
Cyber Security Attacks Response Plan Common Sources Of Precursors And IndicatorsThis slide represents the common sources of signs which indicates that an incident may occur in the future. It includes details related to common sources of precursors and indicators such as IDPSs, SIEMs, network device logs etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Common Sources Of Precursors And Indicators. Use it as a tool for discussion and navigation on Precursors And Indicators, Suspicious Data, Identify Malicious Activity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Comparative Analysis Of Web Application Firewall Products
Cyber Security Attacks Response Plan Comparative Analysis Of Web Application Firewall ProductsThis slide represents the comparison between various web application firewall products based on multiple parameters to help organization select the best web application firewall for their organization. It includes comparison between WAF products based on features such as cookie tampering etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Comparative Analysis Of Web Application Firewall Products. Dispense information and present a thorough explanation of Comparative Analysis, Web Application, Firewall Products using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Attacks Response Plan Cyber Security Attacks Response Plan For Table Of Contents
Cyber Security Attacks Response Plan Cyber Security Attacks Response Plan For Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Cyber Security Attacks Response Plan Cyber Security Attacks Response Plan For Table Of Contents. This template helps you present information on one stages. You can also present information on Cyber Security Attacks, Response Plan, Incident Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Attacks Response Plan Five Phases Of Cybersecurity Incident Management
Cyber Security Attacks Response Plan Five Phases Of Cybersecurity Incident ManagementThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc. Introducing Cyber Security Attacks Response Plan Five Phases Of Cybersecurity Incident Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Plan And Prepare, Post Incident Activity, Assess And Design, Incident Management, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Attacks Response Plan Impact Of Cybersecurity Incidents On Organization
Cyber Security Attacks Response Plan Impact Of Cybersecurity Incidents On OrganizationThis slide represents the impact of events which indicates that organizations data has been compromised for unlawful activities. It includes impact of cyber security events such as increased costs, operational disruption, reputational damage etc. Increase audience engagement and knowledge by dispensing information using Cyber Security Attacks Response Plan Impact Of Cybersecurity Incidents On Organization. This template helps you present information on six stages. You can also present information on Reputational Damage, Stolen Intellectual Property, Altered Business Practices, Operational Disruption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Cyber Security Attacks Response Plan Ppt Infographic Template Deck
Table Of Contents For Cyber Security Attacks Response Plan Ppt Infographic Template DeckIntroducing Table Of Contents For Cyber Security Attacks Response Plan Ppt Infographic Template Deck to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Dashboards, Cyber Security, Incident Management, Incident Response Management, using this template. Grab it now to reap its full benefits.



