Powerpoint Templates and Google slides for Manage Identities
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
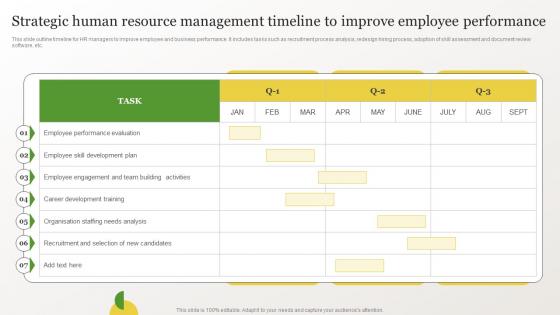 Identifying Gaps In Workplace Strategic Human Resource Management Timeline To Improve
Identifying Gaps In Workplace Strategic Human Resource Management Timeline To ImproveThis slide outline timeline for HR managers to improve employee and business performance.It includes tasks such as recruitment process analysis, redesign hiring process, adoption of skill assessment and document review software, etc. Present the topic in a bit more detail with this Identifying Gaps In Workplace Strategic Human Resource Management Timeline To Improve Use it as a tool for discussion and navigation on Performance Evaluation, Skill Development Plan This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Workforce Management Techniques Conflict Identification And Resolution Action Plan
Workforce Management Techniques Conflict Identification And Resolution Action PlanThis slide provides glimpse about analyzing annual costs incurred in the new workforce management process. It includes costs such as planning costs, recruitment costs, learning and development costs, employee engagement costs, etc. Present the topic in a bit more detail with this Workforce Management Techniques Conflict Identification And Resolution Action Plan Use it as a tool for discussion and navigation on Planning Costs, Recruitment Costs This template is free to edit as deemed fit for your organization. Therefore download it now.
-
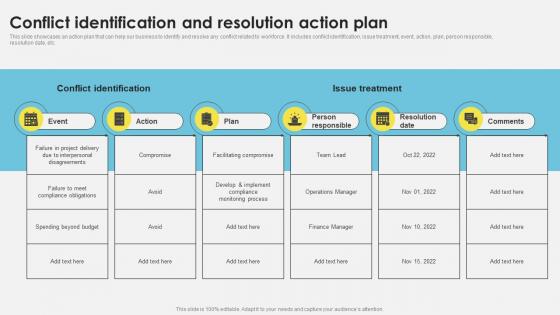
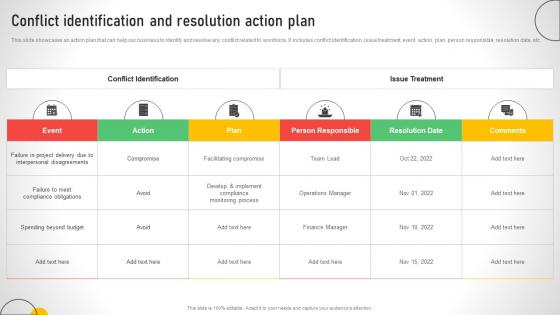 Conflict Identification And Resolution Action Plan Efficient Talent Acquisition And Management
Conflict Identification And Resolution Action Plan Efficient Talent Acquisition And ManagementThis slide showcases an action plan that can help our business to identify and resolve any conflict related to workforce. It includes conflict identification, issue treatment, event, action, plan, person responsible, resolution date, etc. Present the topic in a bit more detail with this Conflict Identification And Resolution Action Plan Efficient Talent Acquisition And Management. Use it as a tool for discussion and navigation on Identification, Resolution, Action. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Critical Roles And High Potential Employees Identified Talent Management And Succession
Critical Roles And High Potential Employees Identified Talent Management And SuccessionThis slide showcases critical roles and high potential employees that are identified for succession planning. Its key elements are position, candidates ready today, near term candidates and future candidates. Present the topic in a bit more detail with this Critical Roles And High Potential Employees Identified Talent Management And Succession. Use it as a tool for discussion and navigation on Production Supervisor, Quality Manager, Sales Manager, Technology Director. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Matrix To Identify Top Talent In Organization Talent Management And Succession
Matrix To Identify Top Talent In Organization Talent Management And SuccessionThis slide showcases matrix that can help organization to identify top talent in organization on the basis of high potential and performance. Its key elements are grade, timeline and characteristics. Present the topic in a bit more detail with this Matrix To Identify Top Talent In Organization Talent Management And Succession. Use it as a tool for discussion and navigation on Contributor, Transitional, Timeline, Characteristics. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Questionnaire For Critical Role Identification Talent Management And Succession
Questionnaire For Critical Role Identification Talent Management And SuccessionThis slide showcases questionnaire that can help to organization to identify critical role in different departments and plan for succession. Its key elements are urgency, impact, skills, external plus internal talent. Deliver an outstanding presentation on the topic using this Questionnaire For Critical Role Identification Talent Management And Succession. Dispense information and present a thorough explanation of Marketing Executive, Accounts Executive, Marketing Manager using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Business Competitive Assessment To Identify Marketing Strategy Guide For Business Management MKT SS V
Business Competitive Assessment To Identify Marketing Strategy Guide For Business Management MKT SS VThe slide displays a competitive analysis matrix based on various factors to identify opportunities to grow in business. It includes factors such as pricing, quality, brand awareness, branding strategies, advertising spend and quick delivery. Present the topic in a bit more detail with this Business Competitive Assessment To Identify Marketing Strategy Guide For Business Management MKT SS V. Use it as a tool for discussion and navigation on Factors, Your Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Talent Management And Potential Employee Role Succession Planning To Identify Talent And Critical Job Roles
Talent Management And Potential Employee Role Succession Planning To Identify Talent And Critical Job RolesThis slide showcases checklist that can help talent management committee to ensure fulfillment of succession planning responsibilities. It also shows role of high potential employee in succession plan. Deliver an outstanding presentation on the topic using this Talent Management And Potential Employee Role Succession Planning To Identify Talent And Critical Job Roles. Dispense information and present a thorough explanation of Management, Potential, Aspirations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
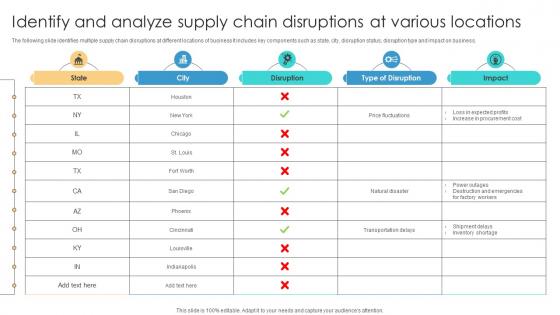 Risk Management Process Identify And Analyze Supply Chain Disruptions At Various Locations
Risk Management Process Identify And Analyze Supply Chain Disruptions At Various LocationsThe following slide identifies multiple supply chain disruptions at different locations of business It includes key components such as state, city, disruption status, disruption type and impact on business. Deliver an outstanding presentation on the topic using this Risk Management Process Identify And Analyze Supply Chain Disruptions At Various Locations Dispense information and present a thorough explanation of Price Fluctuations, Natural Disaster using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Identification Checklist To Identify And Manage Strategic Sourcing In Supply Chain Strategy SS V
Risk Identification Checklist To Identify And Manage Strategic Sourcing In Supply Chain Strategy SS VThis slide provides an overview of the checklist created to identify potential risks. The risks covered are inaccurate need analysis, inadequate vendor management, lack od automation, poor supplier management, overspending, etc. Deliver an outstanding presentation on the topic using this Risk Identification Checklist To Identify And Manage Strategic Sourcing In Supply Chain Strategy SS V. Dispense information and present a thorough explanation of Status, Responsible, Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
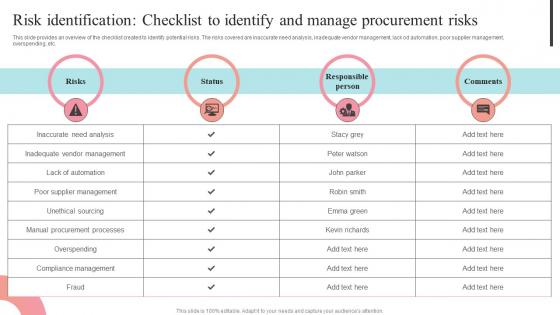 Risk Identification Checklist To Identify And Manage Supplier Negotiation Strategy SS V
Risk Identification Checklist To Identify And Manage Supplier Negotiation Strategy SS VThis slide provides an overview of the checklist created to identify potential risks. The risks covered are inaccurate need analysis, inadequate vendor management, lack od automation, poor supplier management, overspending, etc. Present the topic in a bit more detail with this Risk Identification Checklist To Identify And Manage Supplier Negotiation Strategy SS V. Use it as a tool for discussion and navigation on Responsible Person, Inaccurate Need Analysis, Procurement Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Identification Checklist To Identify And Manage Steps To Create Effective Strategy SS V
Risk Identification Checklist To Identify And Manage Steps To Create Effective Strategy SS VThis slide provides an overview of the checklist created to identify potential risks. The risks covered are inaccurate need analysis, inadequate vendor management, lack od automation, poor supplier management, overspending, etc. Present the topic in a bit more detail with this Risk Identification Checklist To Identify And Manage Steps To Create Effective Strategy SS V. Use it as a tool for discussion and navigation on Inaccurate Need Analysis, Lack Of Automation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cost Reduction Strategies Risk Identification Checklist To Identify And Manage Procurement Strategy SS V
Cost Reduction Strategies Risk Identification Checklist To Identify And Manage Procurement Strategy SS VThis slide provides an overview of the checklist created to identify potential risks. The risks covered are inaccurate need analysis, inadequate vendor management, lack od automation, poor supplier management, overspending, etc. Present the topic in a bit more detail with this Cost Reduction Strategies Risk Identification Checklist To Identify And Manage Procurement Strategy SS V. Use it as a tool for discussion and navigation on Inaccurate Need Analysis, Supplier Management, Unethical Sourcing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Procurement Negotiation Strategies Risk Identification Checklist To Identify And Manage Strategy SS V
Procurement Negotiation Strategies Risk Identification Checklist To Identify And Manage Strategy SS VThis slide provides an overview of the checklist created to identify potential risks. The risks covered are inaccurate need analysis, inadequate vendor management, lack od automation, poor supplier management, overspending, etc. Present the topic in a bit more detail with this Procurement Negotiation Strategies Risk Identification Checklist To Identify And Manage Strategy SS V. Use it as a tool for discussion and navigation on Risks, Responsible Person, Comments. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Identification Checklist To Identify And Manage Risk Management And Mitigation
Risk Identification Checklist To Identify And Manage Risk Management And MitigationThis slide provides an overview of the checklist created to identify potential risks. The risks covered are inaccurate need analysis, inadequate vendor management, lack od automation, poor supplier management, overspending, etc. Present the topic in a bit more detail with this Risk Identification Checklist To Identify And Manage Risk Management And Mitigation. Use it as a tool for discussion and navigation on Inaccurate, Management, Procurement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Auto Identification And Dependency Ai For Effective It Operations Management AI SS V
Auto Identification And Dependency Ai For Effective It Operations Management AI SS VThe following slide showcases how AIOps helps in auto detection and mapping of data. It includes elements such as automatic scaling, topology mapping etc.Present the topic in a bit more detail with this Auto Identification And Dependency Ai For Effective It Operations Management AI SS V. Use it as a tool for discussion and navigation on Allows Anomaly Detection, Algorithms Comprising, Manages Data Processing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Chatgpt For Identifying Basis Unleash Power Of Chatgpt Game Changer Management ChatGPT SS
Chatgpt For Identifying Basis Unleash Power Of Chatgpt Game Changer Management ChatGPT SSThis slide represents details related to use cases of AI chatbot which uses natural language processing capabilities for creating human like conversational dialogue for project management. It includes details related to use case of ChatGPT for identifying basis of new project. Present the topic in a bit more detail with this Chatgpt For Identifying Basis Unleash Power Of Chatgpt Game Changer Management ChatGPT SS. Use it as a tool for discussion and navigation on Competitors, Identifying, Capabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Process To Identify Change Champions Change Management Plan For Organizational Transitions CM SS
Process To Identify Change Champions Change Management Plan For Organizational Transitions CM SSThis slide covers information about selecting the right change champions and leaders who are strategic decision-makers significantly impacting the success of organizational change efforts. It consists of details related to factors considered while choosing individuals with the necessary skills, commitment, and values for change management Present the topic in a bit more detail with this Process To Identify Change Champions Change Management Plan For Organizational Transitions CM SS. Use it as a tool for discussion and navigation on Organizations, Responsibilities, Organizational. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Leveraging Risk Management Process Identification Of Various Types Of Business Risks PM SS
Leveraging Risk Management Process Identification Of Various Types Of Business Risks PM SSThis slide shows identification methods for different types of risks associated with business directly or indirectly. It include different risks such as legal risks, environmental risks and market risks, etc. Present the topic in a bit more detail with this Leveraging Risk Management Process Identification Of Various Types Of Business Risks PM SS. Use it as a tool for discussion and navigation on Business Risks, Performance Risks, External Project Risks, Financial Forecasting, Budget Analysis. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Leveraging Risk Management Process Sample Risk Register For Identifying Project Risks PM SS
Leveraging Risk Management Process Sample Risk Register For Identifying Project Risks PM SSThis slide shows sample risk register format for noting down potential risks related to project. It include different risks such as vendor delays, technological risks and scheduling risks, etc. Present the topic in a bit more detail with this Leveraging Risk Management Process Sample Risk Register For Identifying Project Risks PM SS. Use it as a tool for discussion and navigation on Sample Risk Register, Identifying Project Risks, Technological Risks, Scheduling Risks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Fulfillment Center Optimization Identifying The Need For Effective Fleet Management
Fulfillment Center Optimization Identifying The Need For Effective Fleet ManagementThis slide presents an overview of fleet management and its benefits for business. It also identifies issuesin various fleet management processes and possible bottleneck and impact. Deliver an outstanding presentation on the topic using this Fulfillment Center Optimization Identifying The Need For Effective Fleet Management Dispense information and present a thorough explanation of Optimized Transportation, Reduced Delivery Times using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process
Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management ProcessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Present the topic in a bit more detail with this Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Vulnerability, Threat, Threat Source. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identifying The Need For Effective Fleet Management Implementing Cost Effective Warehouse Stock
Identifying The Need For Effective Fleet Management Implementing Cost Effective Warehouse StockThis slide presents an overview of fleet management and its benefits for business. It also identifies issues in various fleet management processes and possible bottleneck and impact. Deliver an outstanding presentation on the topic using this Identifying The Need For Effective Fleet Management Implementing Cost Effective Warehouse Stock. Dispense information and present a thorough explanation of Loading, Routing, Driver Availability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identify And Assign The Project Management Team Mastering Project Management PM SS
Identify And Assign The Project Management Team Mastering Project Management PM SSThe purpose of the mentioned slide is to outline a strategic plan for assigning delegation to project management team members. It includes various attributes such as role, objective, and team members.Deliver an outstanding presentation on the topic using this Identify And Assign The Project Management Team Mastering Project Management PM SS. Dispense information and present a thorough explanation of Stakeholder Liaison, Support Maintenance, Communication Coordination using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Identification Checklist To Create Mitigation Plan Mastering Project Management PM SS
Risk Identification Checklist To Create Mitigation Plan Mastering Project Management PM SSThis slide provides an overview of the risk identification checklist to determine and mitigate common project risks. The risks included are resources, finance, schedules, people and others.Present the topic in a bit more detail with this Risk Identification Checklist To Create Mitigation Plan Mastering Project Management PM SS. Use it as a tool for discussion and navigation on Predetermined Financial, Positions Responsibilities, Predetermined Financial Restrictions This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Stakeholder Identification And Analysis For Project Mastering Project Management PM SS
Stakeholder Identification And Analysis For Project Mastering Project Management PM SSThe mentioned slide showcases a strategic plan for evaluating various stakeholders for the project based on various factors. It includes multiple parameters such as stakeholder name, role, interest, influence, impact, engagement strategy, etc.Present the topic in a bit more detail with this Stakeholder Identification And Analysis For Project Mastering Project Management PM SS. Use it as a tool for discussion and navigation on Technical Specifications, Frequent Updates, Communication Needs This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Approaches For Effective Business Risk Identification Effective Risk Management Strategies Risk SS
Approaches For Effective Business Risk Identification Effective Risk Management Strategies Risk SSThis slide defines the significance of team collaboration, structured risk breakdown, and effective documentation through project risk logs and ongoing databases in managing organizational risk. Present the topic in a bit more detail with this Approaches For Effective Business Risk Identification Effective Risk Management Strategies Risk SS. Use it as a tool for discussion and navigation on Team Collaboration, Risk Breakdown Structure, Project Risk Log. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IAM Process For Effective Access About Identity And Access Management Controls
IAM Process For Effective Access About Identity And Access Management ControlsThis slide discusses the various controls of Identity and Access Management. The purpose of this slide is to explain the controls of IAM, which include unique IDs, devices, services, application accounts, access approval, and account management. Present the topic in a bit more detail with this IAM Process For Effective Access About Identity And Access Management Controls. Use it as a tool for discussion and navigation on Service And Application Accounts, Account Management, Applicable Data Protection Categorization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IAM Process For Effective Access Before Vs After Impact Of Identity And Access Management Implementation
IAM Process For Effective Access Before Vs After Impact Of Identity And Access Management ImplementationThis slide showcases the comparative analysis of the before versus after IAM implementation. The purpose of this slide is to discuss the different performance aspects and how IAM has proved beneficial for these aspects. Deliver an outstanding presentation on the topic using this IAM Process For Effective Access Before Vs After Impact Of Identity And Access Management Implementation. Dispense information and present a thorough explanation of Credential Management, Identity Provisioning, Policy Enforcement using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IAM Process For Effective Access Essential Principles Of Identity And Access Management
IAM Process For Effective Access Essential Principles Of Identity And Access ManagementThis slide discusses the principles of a successful Identity and Access Management program. The purpose of this slide is to explain the various principles of IAM these include IAM impacts everyone and everything, simplifies the user experiences, enables research and collaboration, and so on. Deliver an outstanding presentation on the topic using this IAM Process For Effective Access Essential Principles Of Identity And Access Management. Dispense information and present a thorough explanation of Simplifies The User Experience, Facilitates Technology Innovation, Protects University Resources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IAM Process For Effective Access Impact Of Identity And Access Management On Business
IAM Process For Effective Access Impact Of Identity And Access Management On BusinessThis slide represents the Identity and Access Management impact on organization. The purpose of this slide is to highlight the impact associated with IAM for business which are enhances security, regularity compliance and so on. Present the topic in a bit more detail with this IAM Process For Effective Access Impact Of Identity And Access Management On Business. Use it as a tool for discussion and navigation on Regulatory Compliance, Improved Productivity, Enhanced Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IAM Process For Effective Access Primary Identity And Access Management Software
IAM Process For Effective Access Primary Identity And Access Management SoftwareThis slide discusses the primary software used in the Identity and Access Management process. The purpose of this slide is to explain the software of IAM, which are Okta, JumpCloud, Rippling, Auth0, and OneLogin. Deliver an outstanding presentation on the topic using this IAM Process For Effective Access Primary Identity And Access Management Software. Dispense information and present a thorough explanation of Customizable Regional Settings, Access Management Software, Flawless Integration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
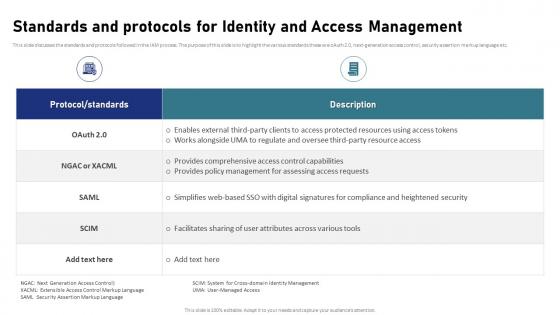 IAM Process For Effective Access Standards And Protocols For Identity And Access Management
IAM Process For Effective Access Standards And Protocols For Identity And Access ManagementThis slide discusses the standards and protocols followed in the IAM process. The purpose of this slide is to highlight the various standards these are oAuth 2.0, next-generation access control, security assertion markup language etc. Present the topic in a bit more detail with this IAM Process For Effective Access Standards And Protocols For Identity And Access Management. Use it as a tool for discussion and navigation on Next Generation Access Control, Security Assertion Markup Language, Access Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identity And Access Management And Compliance Regulation IAM Process For Effective Access
Identity And Access Management And Compliance Regulation IAM Process For Effective AccessThis slide showcases the Identity and Access Management and compliance regulations. The purpose of this slide is to discuss the compliances adopting the IAM system, enhancing data security and privacy, simplifying compliance, etc. Deliver an outstanding presentation on the topic using this Identity And Access Management And Compliance Regulation IAM Process For Effective Access. Dispense information and present a thorough explanation of Adoption Of IAM Systems, Automation For Reporting Compliance, Regulatory Documentation Requirements using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identity And Access Management Challenges And Solutions IAM Process For Effective Access
Identity And Access Management Challenges And Solutions IAM Process For Effective AccessThis slide highlights the challenges associated with IAM. The purpose of this slide is to discuss the solutions provided to different challenges related to IAM. These include distributed workforce, distributed application, productive provisioning, BYOD, etc. Deliver an outstanding presentation on the topic using this Identity And Access Management Challenges And Solutions IAM Process For Effective Access. Dispense information and present a thorough explanation of Productive Provisioning, Distributed Applications, Password Problems, Access Management Challenges using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identity And Access Management Ease Of Use Issue IAM Process For Effective Access
Identity And Access Management Ease Of Use Issue IAM Process For Effective AccessThis slide discusses the ease of use issue of the Identity and Access Management process. The purpose of this slide is to explain the ease of use challenges of IAM these include the increasing authentication complexity, demand for self-service, and so on. Deliver an outstanding presentation on the topic using this Identity And Access Management Ease Of Use Issue IAM Process For Effective Access. Dispense information and present a thorough explanation of Authentication Complexity, Demand For Self Service, Financial Consequences using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identity And Access Management Financial Issue IAM Process For Effective Access
Identity And Access Management Financial Issue IAM Process For Effective AccessThis slide discusses the financial issue of the Identity and Access Management process. The purpose of this slide is to explain the economic challenges of IAM these include low user productivity, redundant tasks, many password calls, and slow provisioning. Deliver an outstanding presentation on the topic using this Identity And Access Management Financial Issue IAM Process For Effective Access. Dispense information and present a thorough explanation of Redundant Tasks, Many Password Calls, Identity And Access Management, Financial Issue using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identity And Access Management Function As Security Tool IAM Process For Effective Access
Identity And Access Management Function As Security Tool IAM Process For Effective AccessThis slide showcases function of Identity and Access Management as a security tool. The purpose of this slide is to explain the function of IAM as an essential security tool these include context awareness, identity and access governance, and so on. Present the topic in a bit more detail with this Identity And Access Management Function As Security Tool IAM Process For Effective Access. Use it as a tool for discussion and navigation on Context Awareness, Identity And Access Governance, Management Function. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identity And Access Management Provisioning Service IAM Process For Effective Access
Identity And Access Management Provisioning Service IAM Process For Effective AccessThis slide discusses the provisioning service of Identity and Access Management. The purpose of this slide is to explain the provisioning services that ensure the users have timely access to all required resources and IAM challenges targeted by provisioning. Deliver an outstanding presentation on the topic using this Identity And Access Management Provisioning Service IAM Process For Effective Access. Dispense information and present a thorough explanation of Identity And Access Management, Provisioning Service, Inconsistent Identity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identity And Access Management Regulatory Compliance Issue IAM Process For Effective Access
Identity And Access Management Regulatory Compliance Issue IAM Process For Effective AccessThis slide discusses the regulatory compliance issue of the Identity and Access Management process. The purpose of this slide is to explain the regulatory challenges of IAM these include the need for auditing, privacy control, and segregation of duties, etc. Present the topic in a bit more detail with this Identity And Access Management Regulatory Compliance Issue IAM Process For Effective Access. Use it as a tool for discussion and navigation on Identity And Access Management, Regulatory Compliance Issue, Segregation Of Duties, Privacy Control. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identity And Access Management Security Issue IAM Process For Effective Access
Identity And Access Management Security Issue IAM Process For Effective AccessThis slide discusses the security issue of the Identity and Access Management process. The purpose of this slide is to explain the security challenges of IAM these include impractical security policies, inconsistent security policies, slow de-provision, etc. Deliver an outstanding presentation on the topic using this Identity And Access Management Security Issue IAM Process For Effective Access. Dispense information and present a thorough explanation of Impractical Security Policies, Inconsistent Security Policies, Inconsistent Identity Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Hotel Property Management To Streamline Identifying Gaps In Current Property Management System CRP DK SS
Hotel Property Management To Streamline Identifying Gaps In Current Property Management System CRP DK SSThis slide showcases gap analysis in current and desired property management system in aspects such as reservation handling, and front desk operations. Present the topic in a bit more detail with this Hotel Property Management To Streamline Identifying Gaps In Current Property Management System CRP DK SS. Use it as a tool for discussion and navigation on Reservation Handling, Front Desk Operations, Housekeeping Management, Inventory Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identification Of Procurement Costs Procurement Management And Improvement Strategies PM SS
Identification Of Procurement Costs Procurement Management And Improvement Strategies PM SSThe slide presents classification of costs involved in procurement of multi-projects such as direct material costs, labor costs, equipment costs, overhead costs etc. Present the topic in a bit more detail with this Identification Of Procurement Costs Procurement Management And Improvement Strategies PM SS. Use it as a tool for discussion and navigation on Direct Material Costs, Equipment Costs, Identification Of Procurement Costs. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Identification Common Types Of Procurement Management And Improvement Strategies PM SS
Risk Identification Common Types Of Procurement Management And Improvement Strategies PM SSThe slide showcases common types of risks occurred during procurement process such as price instability, contract management, overspending, supplier selection etc. Deliver an outstanding presentation on the topic using this Risk Identification Common Types Of Procurement Management And Improvement Strategies PM SS. Dispense information and present a thorough explanation of Risk Impact Assessment, Checklist To Manage Risks, Price Instability, Poor Supplier Selection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Identification Procurement And Supply Procurement Management And Improvement Strategies PM SS
Risk Identification Procurement And Supply Procurement Management And Improvement Strategies PM SSThe slide presents assessment matrix to evaluate procurement risks such as security breach, supplier disruptions, revenue stability, hurdles to qualify alternate supplies etc. Present the topic in a bit more detail with this Risk Identification Procurement And Supply Procurement Management And Improvement Strategies PM SS. Use it as a tool for discussion and navigation on Inadequately Administering Contract, Risk Identification, Procurement And Supply Chain, Risk Assessment Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Identification Procurement Risk Procurement Management And Improvement Strategies PM SS
Risk Identification Procurement Risk Procurement Management And Improvement Strategies PM SSThe slide exhibits checklist to identify procurement risks such as inaccurate need analysis, lack of automation, unethical sourcing, inadequate vendor management, etc. Deliver an outstanding presentation on the topic using this Risk Identification Procurement Risk Procurement Management And Improvement Strategies PM SS. Dispense information and present a thorough explanation of Inadequate Vendor Management, Poor Supplier Management, Compliance Management, Manual Procurement Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Organizational Change Management Overview Identifying Barriers To Change Process CM SS
Organizational Change Management Overview Identifying Barriers To Change Process CM SSThis slide presents information about recognizing and addressing the barriers faced while implementing significant changes. It consists of details related to logical, psychological, and sociological barriers. Present the topic in a bit more detail with this Organizational Change Management Overview Identifying Barriers To Change Process CM SS. Use it as a tool for discussion and navigation on Logical and Rational Barriers, Psychological Barriers, Sociological Barriers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identifying And Classifying Different Credit Risk Management To Streamline Capital CRP DK SS
Identifying And Classifying Different Credit Risk Management To Streamline Capital CRP DK SSThis slide showcases segregating different risks associated with credit management including default risk, creditworthiness, industry and business risk, etc. Present the topic in a bit more detail with this Identifying And Classifying Different Credit Risk Management To Streamline Capital CRP DK SS. Use it as a tool for discussion and navigation on Borrower-Specific Risks, Portfolio Risks, Industry And Business Risk. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Various Identified For Rem Systems Effective Guide For Real Estate Management System Implementation
Various Identified For Rem Systems Effective Guide For Real Estate Management System ImplementationFollowing slide outlines key features or requirements recognised for real estate management system selection by different types. It includes features by types such as residential, commercial, and hotel management system. Deliver an outstanding presentation on the topic using this Various Identified For Rem Systems Effective Guide For Real Estate Management System Implementation. Dispense information and present a thorough explanation of Lease And Tenant Management, Maintenance Request, Property Listing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Basic Capabilities Of Identity And Access Management System Securing Systems With Identity
Basic Capabilities Of Identity And Access Management System Securing Systems With IdentityThis slide discusses the Identity and Access Management basic capabilities. The purpose of this slide is to explain the various capabilities of IAM these are identity management, user provisioning and de-provisioning, authentication, and so on. Deliver an outstanding presentation on the topic using this Basic Capabilities Of Identity And Access Management System Securing Systems With Identity Dispense information and present a thorough explanation of Identity Management, User Provisioning using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Before Vs After Impact Of Identity And Access Management Securing Systems With Identity
Before Vs After Impact Of Identity And Access Management Securing Systems With IdentityThis slide showcases the comparative analysis of the before versus after IAM implementation. The purpose of this slide is to discuss the different performance aspects and how IAM has proved beneficial for these aspects. Present the topic in a bit more detail with this Before Vs After Impact Of Identity And Access Management Securing Systems With Identity Use it as a tool for discussion and navigation on Aspect, Self Registration, Policy Enforcement This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Benefits Of Identity And Access Management System Securing Systems With Identity
Benefits Of Identity And Access Management System Securing Systems With IdentityThis slide highlights the Identity and Access Management benefits. The purpose of this slide is to discuss the various advantages these include proper access for the right people, unhindered productivity, protection from data breaches, data encryption, etc. Deliver an outstanding presentation on the topic using this Benefits Of Identity And Access Management System Securing Systems With Identity Dispense information and present a thorough explanation of Collaboration And Efficiency, Data Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist To Implement Identity And Access Management Securing Systems With Identity
Checklist To Implement Identity And Access Management Securing Systems With IdentityThis slide represents the checklist to implement the Identity and Access Management plan in an organization. The purpose of this slide is to provide key functional requirements for implementing and deploying IAM in an enterprise environment. Deliver an outstanding presentation on the topic using this Checklist To Implement Identity And Access Management Securing Systems With Identity Dispense information and present a thorough explanation of Iam Policy And Strategy, User Lifecycle Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Customer Identity And Access Management Vs IAM Securing Systems With Identity
Customer Identity And Access Management Vs IAM Securing Systems With IdentityThis slide showcases the comparison of Customer Identity and Access Management and the Identity and Access Management process. The purpose of this slide is to highlight the purpose and features of the CIAM and IAM process. Deliver an outstanding presentation on the topic using this Customer Identity And Access Management Vs IAM Securing Systems With Identity Dispense information and present a thorough explanation of Ciam Software, Iam Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Features Of Identity And Access Management Process Securing Systems With Identity
Features Of Identity And Access Management Process Securing Systems With IdentityThis slide discusses the Identity and Access Management features. The purpose of this slide is to explain the various features, including stored information authentication and authorization, external user registration, and so on. Present the topic in a bit more detail with this Features Of Identity And Access Management Process Securing Systems With Identity Use it as a tool for discussion and navigation on Stored Information, External User Registration This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identity And Access Management Challenges And Solutions Securing Systems With Identity
Identity And Access Management Challenges And Solutions Securing Systems With IdentityThis slide highlights the challenges associated with IAM. The purpose of this slide is to discuss the solutions provided to different challenges related to IAM. These include distributed workforce, distributed application, productive provisioning, BYOD, etc. Present the topic in a bit more detail with this Identity And Access Management Challenges And Solutions Securing Systems With Identity Use it as a tool for discussion and navigation on Challenges, Description, Solutions This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identity And Access Management Technologies And Tools Securing Systems With Identity
Identity And Access Management Technologies And Tools Securing Systems With IdentityThis slide discusses the tools and technologies used in the Identity and Access Management process. The purpose of this slide is to highlight the various tools, which are security assertion markup language, open ID connect, and a system for cross-domain identity management. Present the topic in a bit more detail with this Identity And Access Management Technologies And Tools Securing Systems With Identity Use it as a tool for discussion and navigation on Saml, Oidc, Scim This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Register Identify And Manage Construction Risks Effective Risk Management In Construction Projects Risk Ss
Risk Register Identify And Manage Construction Risks Effective Risk Management In Construction Projects Risk SsThis slide depicts that effectively managing safety, financial, and legal risks in construction projects requires proactive measures such as rigorous safety training, accurate budgeting, legal compliance, etc. Deliver an outstanding presentation on the topic using this Risk Register Identify And Manage Construction Risks Effective Risk Management In Construction Projects Risk Ss. Dispense information and present a thorough explanation of Safety Risk, Financial Risk, Legal Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Pricing Summary For IAM Implementation Proposal Identity And Access Management
Pricing Summary For IAM Implementation Proposal Identity And Access ManagementThis slide represents the estimated and actual cost of implementing an IAM plan in an organization the cost categories are IAM software licensing, hardware cost, etc. Present the topic in a bit more detail with this Pricing Summary For IAM Implementation Proposal Identity And Access Management Use it as a tool for discussion and navigation on Hardware And Infrastructure, Testing And Quality Assurance This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Project Context For Identity And Access Management Proposal Identity And Access Management
Project Context For Identity And Access Management Proposal Identity And Access ManagementThis slide highlights the project context for the Identity and Access Management proposal which includes the requirements and the key deliverables by the service provider. Deliver an outstanding presentation on the topic using this Project Context For Identity And Access Management Proposal Identity And Access Management Dispense information and present a thorough explanation of Centralized Identity Management, Self Service Portal using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



