Powerpoint Templates and Google slides for It Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 It security ppt powerpoint presentation ideas display cpb
It security ppt powerpoint presentation ideas display cpbPresenting this set of slides with name IT Security Ppt Powerpoint Presentation Ideas Display Cpb. This is an editable Powerpoint six stages graphic that deals with topics like IT Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Data security it prepare a disaster recovery plan ppt slides rules
Data security it prepare a disaster recovery plan ppt slides rulesThis slide depicts what factors will be considered while preparing a recovery planning of an organization to come back to business quickly and effectively. Introducing Data Security IT Prepare A Disaster Recovery Plan Ppt Slides Rules to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Disaster Recovery, Make Report Assets, Risk Assessment Report Assets, Identify importance, using this template. Grab it now to reap its full benefits.
-
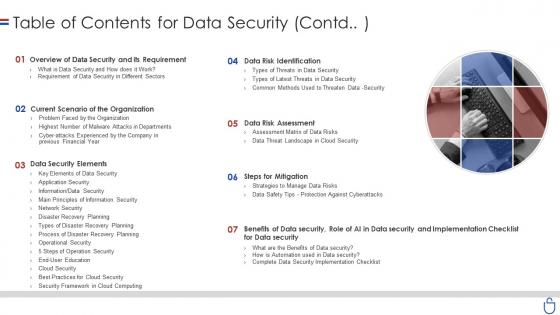 Data security it table of contents for data security contd
Data security it table of contents for data security contdIncrease audience engagement and knowledge by dispensing information using Data Security IT Table Of Contents For Data Security Contd. This template helps you present information on seven stages. You can also present information on Overview Data Security And Its Requirement, Current Scenario Organization, Data Security Elements, Steps Mitigation, Data Risk Assessment, Data Risk Identification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
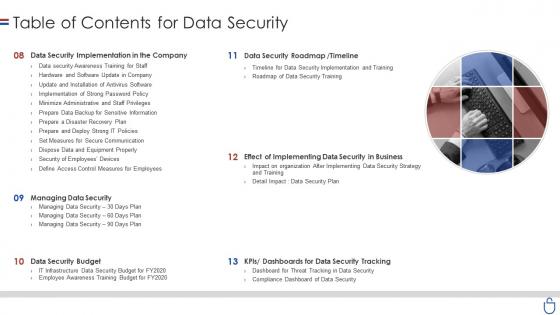 Data security it table of contents for data security ppt slides display
Data security it table of contents for data security ppt slides displayIntroducing Data Security IT Table Of Contents For Data Security Ppt Slides Display to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Data Security Implementation Company, Data Security Roadmap, Timeline, Managing Data Security, Data Security Budget, Dashboards Data Security Tracking, using this template. Grab it now to reap its full benefits.
-
 Data security it 30 60 90 days ppt slides infographic template
Data security it 30 60 90 days ppt slides infographic templateIntroducing Data Security IT 30 60 90 Days Ppt Slides Infographic Template to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Days, using this template. Grab it now to reap its full benefits.
-
 Data security it agenda for data security ppt slides gallery
Data security it agenda for data security ppt slides galleryIncrease audience engagement and knowledge by dispensing information using Data Security IT Agenda For Data Security Ppt Slides Gallery. This template helps you present information on five stages. You can also present information on Employees, Data And Information Systems, Strategies And Tools using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Facilities rendered by security centre implementation project safety management it
Facilities rendered by security centre implementation project safety management itThis slide provides information regarding the various facilities that are offered by successful implementation of security center in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Increase audience engagement and knowledge by dispensing information using Facilities Rendered By Security Centre Implementation Project Safety Management It. This template helps you present information on four stages. You can also present information on Analysts, Security, Organization, Data, Determine using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda for enhancing overall project security it
Agenda for enhancing overall project security itIncrease audience engagement and knowledge by dispensing information using Agenda For Enhancing Overall Project Security It. This template helps you present information on four stages. You can also present information on Implemented, Management, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enhancing overall project security it determine project safety management team structure
Enhancing overall project security it determine project safety management team structureThis slide provides information regarding project safety management team generally comprise of senior management personnel that have authority and resources to accelerate IT projects incident response. They will be responsible in managing human impacts both employees and community, company reputation, share values, and corporate assets. Introducing Enhancing Overall Project Security It Determine Project Safety Management Team Structure to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Management, Structure, Corporate, using this template. Grab it now to reap its full benefits.
-
 Hacking it roadmap to implement new security strategies
Hacking it roadmap to implement new security strategiesThis slide represents the roadmap to implement new security strategies, including hiring new professionals, new software or hardware installation, employee awareness sessions, etc. Increase audience engagement and knowledge by dispensing information using Hacking It Roadmap To Implement New Security Strategies. This template helps you present information on five stages. You can also present information on Roadmap To Implement New Security Strategies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda of improve it security with vulnerability management
Agenda of improve it security with vulnerability managementIntroducing Agenda Of Improve It Security With Vulnerability Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability, Management, Agenda, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management event management services
Improve it security with vulnerability management event management servicesThis slide covers the SIEM services offered by our company such as data aggregation, correlation, security alerts, dashboards, retention, forensic analysis, IT compliance, threat detection, etc. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Event Management Services. This template helps you present information on eight stages. You can also present information on Data Aggregation, Data Correlation, Security Alert using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve it security with vulnerability management log management services
Improve it security with vulnerability management log management servicesThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Introducing Improve It Security With Vulnerability Management Log Management Services to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Collection And Normalization, Search Speed, Real Time Analysis, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management need for siem software company
Improve it security with vulnerability management need for siem software companyThis slide covers the need for the SIEM software which focuses on detecting incidents, compliance regulations, and incident management Introducing Improve It Security With Vulnerability Management Need For Siem Software Company to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Detecting Incidents, Compliance With Regulations, Efficient Incident Management, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management threat intelligence services
Improve it security with vulnerability management threat intelligence servicesThis slide covers the threat intelligence services such as global intelligence, local intelligence, and other effective threat detection services. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Threat Intelligence Services. This template helps you present information on three stages. You can also present information on Global Intelligence, Local Intelligence, Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve it security with vulnerability management which hosting model is right for you
Improve it security with vulnerability management which hosting model is right for youThis slide helps in choosing the right hosting model for the client wherein a customer can decide acc. to his requirements which model one must consider. Introducing Improve It Security With Vulnerability Management Which Hosting Model Is Right For You to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Infrastructure, Premises, Management, using this template. Grab it now to reap its full benefits.
-
 Our management team improve it security with vulnerability management
Our management team improve it security with vulnerability managementIntroducing Our Management Team Improve It Security With Vulnerability Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Our Management Team, using this template. Grab it now to reap its full benefits.
-
 Table of contents improve it security with vulnerability management
Table of contents improve it security with vulnerability managementIncrease audience engagement and knowledge by dispensing information using Table Of Contents Improve It Security With Vulnerability Management. This template helps you present information on eleven stages. You can also present information on Vulnerability, Management, Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberterrorism it roadmap to implement cyber security to mitigate cyber terrorism
Cyberterrorism it roadmap to implement cyber security to mitigate cyber terrorismThis slide depicts the roadmap to implement strategies to mitigate cyber terrorism such as training employees about cyber terrorism, creating personal accounts. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Roadmap To Implement Cyber Security To Mitigate Cyber Terrorism. This template helps you present information on four stages. You can also present information on Creating Personal Accounts, Awareness Training Employees, Keep Hardware And Software Updated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Role Of Chief Information Security Officer It Strategy For Digitalization In Business
Role Of Chief Information Security Officer It Strategy For Digitalization In BusinessThis slide covers the role of chief information security officer which includes embed security information, stay informed, hire solid security staff, etc. Introducing Role Of Chief Information Security Officer It Strategy For Digitalization In Business to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Business Advisor, Team Members, Security Information, using this template. Grab it now to reap its full benefits.
-
 Cloud Computing Security Difference Between Cloud Security Solutions And Traditional IT Solutions
Cloud Computing Security Difference Between Cloud Security Solutions And Traditional IT SolutionsThis slide represents the difference between cloud security solutions and traditional IT solutions based on information centers, cost, scalability, and expenses. Increase audience engagement and knowledge by dispensing information using Cloud Computing Security Difference Between Cloud Security Solutions And Traditional IT Solutions. This template helps you present information on two stages. You can also present information on Cloud Security, Traditional It Security, Low Efficiency using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Computing Security Zero Trust Policy And Why You Should Embrace It
Cloud Computing Security Zero Trust Policy And Why You Should Embrace ItThis slide represents the zero trust policy and why organizations should embrace it, and how user access control is managed under the zero trust policy. Increase audience engagement and knowledge by dispensing information using Cloud Computing Security Zero Trust Policy And Why You Should Embrace It. This template helps you present information on three stages. You can also present information on Authentication, Device Validation, Restrict Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
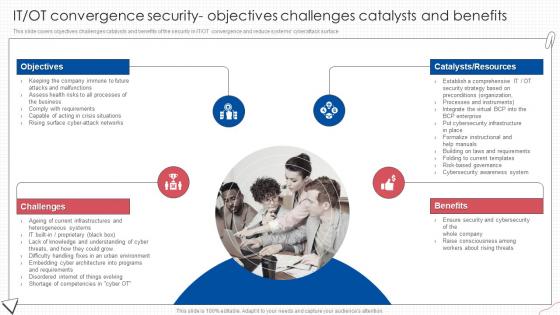 IT OT Convergence Security Objectives Digital Transformation Of Operational Industries
IT OT Convergence Security Objectives Digital Transformation Of Operational IndustriesThis slide covers objectives challenges catalysts and benefits of the security in IT OT convergence and reduce systems cyberattack surface.Introducing IT OT Convergence Security Objectives Digital Transformation Of Operational Industries to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Objectives, Benefits, Consciousness Among, using this template. Grab it now to reap its full benefits.
-
 Comparison Analysis Of Traditional Vs Cloud It Security
Comparison Analysis Of Traditional Vs Cloud It SecurityThis slide showcases the difference between the cloud computer security and standard computer security that enable manager to choose the best strategy. It shows the variation of data centers, initial cost investment, price, time to market and so on Introducing our premium set of slides with Comparison Analysis Of Traditional Vs Cloud It Security. Elucidate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Security, Traditional IT Security. So download instantly and tailor it with your information.
-
 Developing Cyber Security Awareness Cyber Security Awareness Checklist To Ensure It Asset Protection
Developing Cyber Security Awareness Cyber Security Awareness Checklist To Ensure It Asset ProtectionThe purpose of this slide is to outline a comprehensive checklist which can be used to ensure information technology IT asset protection. It cover points such as operating system is up to date, employees are using strong password policy etc. Introducing Developing Cyber Security Awareness Cyber Security Awareness Checklist To Ensure It Asset Protection to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Security, Awareness Checklist, IT Asset Protection, using this template. Grab it now to reap its full benefits.
-
 Icon For Traditional Vs Cloud IT Security
Icon For Traditional Vs Cloud IT SecurityPresenting our set of slides with Icon For Traditional Vs Cloud IT Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon Traditional, Cloud It Security .
-
 Icon For Traditional Vs Cloud Analysis It Security
Icon For Traditional Vs Cloud Analysis It SecurityPresenting our set of slides with Icon For Traditional Vs Cloud Analysis It Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon Traditional,Cloud It Security .
-
 Digital Ledger It Is Blockchain Technology Secure Ppt Styles Professional
Digital Ledger It Is Blockchain Technology Secure Ppt Styles ProfessionalThis slide defines the security of blockchain technology and how hash codes are helpful to maintain data integrity and security in blockchain. Increase audience engagement and knowledge by dispensing information using Digital Ledger It Is Blockchain Technology Secure Ppt Styles Professional. This template helps you present information on five stages. You can also present information on Blockchain Technology Secure, Secure Mechanism, Operations Database using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 GRC Icon To Manage IT And Security Risk
GRC Icon To Manage IT And Security RiskIntroducing our premium set of slides with GRC Icon To Manage IT And Security Risk. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like GRC Icon, IT And Security Risk. So download instantly and tailor it with your information.
-
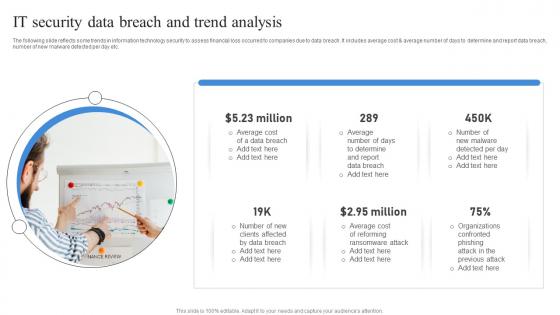 It Security Data Breach And Trend Analysis
It Security Data Breach And Trend AnalysisThe following slide reflects some trends in information technology security to assess financial loss occurred to companies due to data breach. It includes average cost and average number of days to determine and report data breach, number of new malware detected per day etc. Presenting our set of slides with It Security Data Breach And Trend Analysis. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Data, Breach, Analysis.
-
 It Security Threat And Weakness Analysis
It Security Threat And Weakness AnalysisThe following slide highlights the IT security assessment to verify the safety status of assets and networks. It includes elements such as threats, weakness, impact and level of risk, current and proposed controls etc. Introducing our premium set of slides with It Security Threat And Weakness Analysis. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk, Threats, Weakness. So download instantly and tailor it with your information.
-
 Monthly It Security Execution Plan
Monthly It Security Execution PlanThe following slide illustrates the information technology security implementation plan to secure privacy of company and prevent unauthorized users access. It includes activities such as updating system and passwords, organizing restore phishing activities etc. Presenting our set of slides with Monthly It Security Execution Plan. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Activity, Internal Security, Risk Assessment.
-
 What Role Does SDN Play In Customer Security Software Defined Networking IT
What Role Does SDN Play In Customer Security Software Defined Networking ITThis slide represents the role of software defined networking in customer security. It allows clients to have separate settings for each type of network traffic and permits a low-security public-facing network for regular information. Introducing What Role Does SDN Play In Customer Security Software Defined Networking IT to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Provides Several, Cybersecurity Advantages, Customer Security, using this template. Grab it now to reap its full benefits.
-
 Evaluating It System Security Using Swot Analysis Preventing Data Breaches Through Cyber Security
Evaluating It System Security Using Swot Analysis Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline the strength, weakness, opportunities and threat SWOT evaluation of organization cyber security. Organization can detect the potential risks and opportunities in the cyber security using SWOT model. Increase audience engagement and knowledge by dispensing information using Evaluating It System Security Using Swot Analysis Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Strength, Threats, Weaknesses using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Kaizen PDCA For IT Security Management
Kaizen PDCA For IT Security ManagementThis slide mentions Kaizen PDCA for workplace facility management. It involves Planning by facility manager, Conduct layer design, Checking information link and acting on improvements required. Presenting our set of slides with name Kaizen PDCA For IT Security Management. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Considering Metrics, Changes Required, Device Security.
-
 Various Cyber Security Incidents Detected By IT Department Incident Response Strategies Deployment
Various Cyber Security Incidents Detected By IT Department Incident Response Strategies DeploymentThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Introducing Various Cyber Security Incidents Detected By IT Department Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Insider, Phishing, Application, using this template. Grab it now to reap its full benefits.
-
 IT Policy Information Security Policy For Employees Ppt Professional
IT Policy Information Security Policy For Employees Ppt ProfessionalThis slide depicts the information security policy that critical topics covered in this policy. It also covers the reasons for frequent changes in the policy. Introducing IT Policy Information Security Policy For Employees Ppt Professional to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Company Infrastructure, Policy That Changes , Key Topics Covered, using this template. Grab it now to reap its full benefits.
-
 IT Policy Security Awareness And Training Policy Overview Ppt Diagrams
IT Policy Security Awareness And Training Policy Overview Ppt DiagramsThis slide represents the security awareness and training policy. It covers that the training program should be designed by management, and employees will sign a confidentiality agreement after getting the training. Introducing IT Policy Security Awareness And Training Policy Overview Ppt Diagrams to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Security Awareness, Training Policy, Training, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy Importance Of It Policies And Procedures
Cyber Security Policy Importance Of It Policies And ProceduresThis slide talks about the importance of information technology policies and procedures. It also includes how organizations could experience outages due to the lack of inadequate IT management. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Importance Of It Policies And Procedures. This template helps you present information on nine stages. You can also present information on Services, Operational, Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How Management Enables Effective Corporate Security IT Cost Optimization And Management Strategy SS
How Management Enables Effective Corporate Security IT Cost Optimization And Management Strategy SSThis slide portrays information regarding the management role in effective corporate security governance by highlight management level, strategic alignment, risk management, etc. Introducing How Management Enables Effective Corporate Security IT Cost Optimization And Management Strategy SS to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Corporate, Security Governance, Management, using this template. Grab it now to reap its full benefits.
-
 SD WAN IT How Does SD WAN Improve Security Ppt Layouts Slide Portrait
SD WAN IT How Does SD WAN Improve Security Ppt Layouts Slide PortraitThis slide depicts the various security benefits of the software defined wide area network. These advantages include centralized and scalable security, zero touch and segmentation, traffic prioritization from remote locations, traffic encryption and firewalls, cloud connectivity and threat detection and response. Increase audience engagement and knowledge by dispensing information using SD WAN IT How Does SD WAN Improve Security Ppt Layouts Slide Portrait. This template helps you present information on six stages. You can also present information on Centralised And Scalable Security, Segmentation, Traffic Prioritization, Remote Locations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SD WAN IT Secure Access Service Edge Vs SD WAN Ppt Summary Guide
SD WAN IT Secure Access Service Edge Vs SD WAN Ppt Summary GuideThis slide compares secure access service edge and software defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. Introducing SD WAN IT Secure Access Service Edge Vs SD WAN Ppt Summary Guide to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Deployment And Architecture, Traffic And Connectivity, Security, using this template. Grab it now to reap its full benefits.
-
 IT Risk Management Framework To Manage Security Threats Develop Business Aligned IT Strategy
IT Risk Management Framework To Manage Security Threats Develop Business Aligned IT StrategyThis slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Increase audience engagement and knowledge by dispensing information using IT Risk Management Framework To Manage Security Threats Develop Business Aligned IT Strategy. This template helps you present information on three stages. You can also present information on Enterprise Security Program, Control Environment, Security Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Various Cyber Security Incidents Detected By It Department Development And Implementation Of Security
Various Cyber Security Incidents Detected By It Department Development And Implementation Of SecurityThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Increase audience engagement and knowledge by dispensing information using Various Cyber Security Incidents Detected By It Department Development And Implementation Of Security. This template helps you present information on five stages. You can also present information on Insider Threat, Phishing Attack, Malware Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
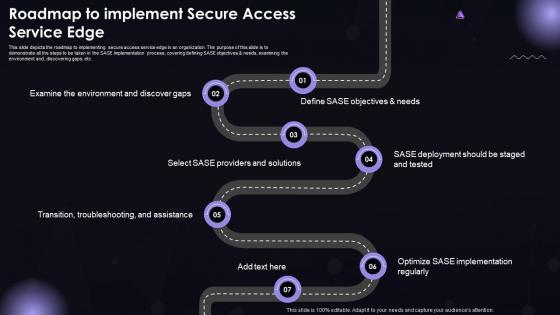 SASE IT Roadmap To Implement Secure Access Service Edge Ppt Powerpoint Formats
SASE IT Roadmap To Implement Secure Access Service Edge Ppt Powerpoint FormatsThis slide depicts the roadmap to implementing secure access service edge in an organization. The purpose of this slide is to demonstrate all the steps to be taken in the SASE implementation process, covering defining SASE objectives and needs, examining the environment and, discovering gaps, etc. Introducing SASE IT Roadmap To Implement Secure Access Service Edge Ppt Powerpoint Formats to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Transition, Troubleshooting, And Assistance, SASE Providers And Solutions, using this template. Grab it now to reap its full benefits.
-
 SASE IT Secure Web Gateways SWG Setup And Working Ppt Powerpoint Portrait
SASE IT Secure Web Gateways SWG Setup And Working Ppt Powerpoint PortraitThis slide depicts the methods to setup the secure web gateways and their working. The purpose of this slide is to demonstrate the various ways in which organizations can install the SWGs. It also caters to the working and functions performed by SWGs to protect data and safe browsing on the internet. Introducing SASE IT Secure Web Gateways SWG Setup And Working Ppt Powerpoint Portrait to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on URL Classifications, Users And Non-Users, Cost-Effective Alternative, using this template. Grab it now to reap its full benefits.
-
 IT Risk Management Framework To Manage Security Strategic Initiatives To Boost IT Strategy SS V
IT Risk Management Framework To Manage Security Strategic Initiatives To Boost IT Strategy SS VThis slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Increase audience engagement and knowledge by dispensing information using IT Risk Management Framework To Manage Security Strategic Initiatives To Boost IT Strategy SS V. This template helps you present information on three stages. You can also present information on Management, Threats, Manage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SDN Security IT Roadmap For Software Defined Network Implementation
SDN Security IT Roadmap For Software Defined Network ImplementationThis slide outlines the roadmap for software defined network implementation, including the steps to be performed, such as defining the use case, creating a cross functional team, testing, and reviewing. Increase audience engagement and knowledge by dispensing information using SDN Security IT Roadmap For Software Defined Network Implementation. This template helps you present information on four stages. You can also present information on Roadmap, Software, Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
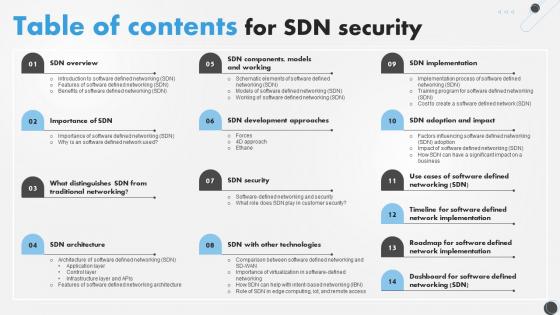 SDN Security IT Table Of Contents For SDN Security Ppt Grid
SDN Security IT Table Of Contents For SDN Security Ppt GridIncrease audience engagement and knowledge by dispensing information using SDN Security IT Table Of Contents For SDN Security Ppt Grid. This template helps you present information on one stages. You can also present information on Security, Models, Approaches using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Training And Development Plan Icon For IT Security Staff
Training And Development Plan Icon For IT Security StaffPresenting our set of slides with Training And Development Plan Icon For IT Security Staff. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Training, Development, Security.
-
 IT Cyber Security Strategy Action Plan Icon
IT Cyber Security Strategy Action Plan IconIntroducing our premium set of slides with IT Cyber Security Strategy Action Plan Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber, Action, Strategy. So download instantly and tailor it with your information.
-
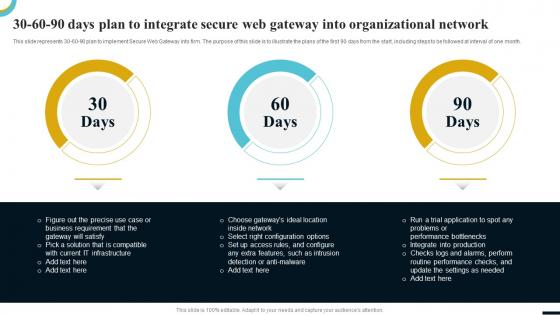 Internet Gateway Security IT 30 60 90 Days Plan To Integrate Secure Web
Internet Gateway Security IT 30 60 90 Days Plan To Integrate Secure WebThis slide represents 30-60-90 plan to implement Secure Web Gateway into firm. The purpose of this slide is to illustrate the plans of the first 90 days from the start, including steps to be followed at interval of one month. Introducing Internet Gateway Security IT 30 60 90 Days Plan To Integrate Secure Web to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Days Plan, using this template. Grab it now to reap its full benefits.
-
 Internet Gateway Security IT Reasons Behind Need For Secure Web Gateway
Internet Gateway Security IT Reasons Behind Need For Secure Web GatewayThis slide discusses the requirement of Secure Web Gateway in protecting organizations from various cyber crimes. The reasons behind need of Secure Web Gateway are protection against web-based threats, enforce security policies, controlled access, etc. Introducing Internet Gateway Security IT Reasons Behind Need For Secure Web Gateway to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Rise In Web-Based Threats, Non-Compliance To Security Policies, Need Of Access Control, Web Traffic Monitoring, Remote Worker Protection, using this template. Grab it now to reap its full benefits.
-
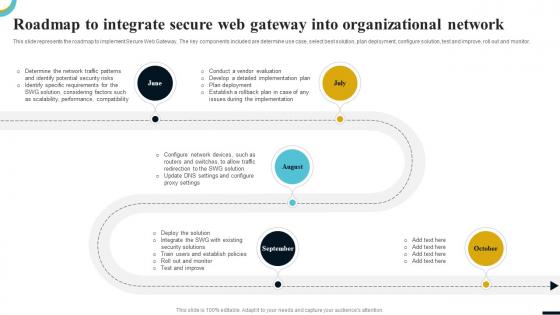 Internet Gateway Security IT Roadmap To Integrate Secure Web Gateway
Internet Gateway Security IT Roadmap To Integrate Secure Web GatewayThis slide represents the roadmap to implement Secure Web Gateway. The key components included are determine use case, select best solution, plan deployment, configure solution, test and improve, roll out and monitor. Introducing Internet Gateway Security IT Roadmap To Integrate Secure Web Gateway to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Scalability, Performance, Compatibility, Implementation, Plan Deployment, using this template. Grab it now to reap its full benefits.
-
 Internet Gateway Security IT Table Of Contents
Internet Gateway Security IT Table Of ContentsIntroducing Internet Gateway Security IT Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Secure Web Gateway Technology, Industries, using this template. Grab it now to reap its full benefits.
-
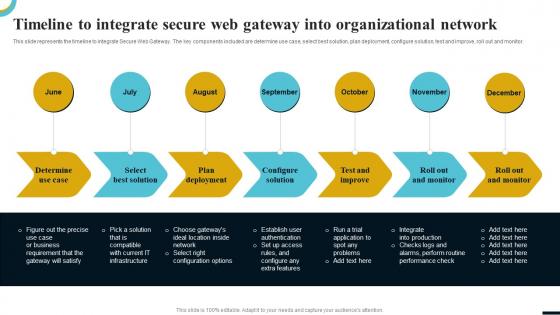 Internet Gateway Security IT Timeline To Integrate Secure Web Gateway
Internet Gateway Security IT Timeline To Integrate Secure Web GatewayThis slide represents the timeline to integrate Secure Web Gateway. The key components included are determine use case, select best solution, plan deployment, configure solution, test and improve, roll out and monitor. Introducing Internet Gateway Security IT Timeline To Integrate Secure Web Gateway to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Determine Use Case, Select Best Solution, Plan Deployment, Configure Solution, Test And Improve, using this template. Grab it now to reap its full benefits.
-
 Agenda IT Security Awareness Training Program Cybersecurity SS
Agenda IT Security Awareness Training Program Cybersecurity SSIntroducing Agenda IT Security Awareness Training Program Cybersecurity SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Financial Resources, Resilient Environment, Security Awareness, Training Program, using this template. Grab it now to reap its full benefits.
-
 Essential Components Of Effective IT Security Awareness Training Program Cybersecurity SS
Essential Components Of Effective IT Security Awareness Training Program Cybersecurity SSThis slide represents essential elements for developing training program which helps to mitigate cyber security risks. It include components such as educational content, testing etc. Introducing Essential Components Of Effective IT Security Awareness Training Program Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Educational Content, Metrics And Reporting, Testing, Security Awareness Training Program, using this template. Grab it now to reap its full benefits.
-
 Overview IT Security Awareness Training Modules Cybersecurity SS
Overview IT Security Awareness Training Modules Cybersecurity SSThis slide represents overview of training modules to be facilitated to organizational employees for effectively understanding, preventing and mitigating cyber security risks. Increase audience engagement and knowledge by dispensing information using Overview IT Security Awareness Training Modules Cybersecurity SS. This template helps you present information on six stages. You can also present information on Social Engineering, Insider Threats Awareness, Cloud Security, Ransomware Awareness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents IT Security Awareness Training Program Cybersecurity SS
Table Of Contents IT Security Awareness Training Program Cybersecurity SSIntroducing Table Of Contents IT Security Awareness Training Program Cybersecurity SS to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Team Roles And Responsibilities, Costs Incurred, Planning, Cloud Security, Social Engineering Program, using this template. Grab it now to reap its full benefits.



