Powerpoint Templates and Google slides for It Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
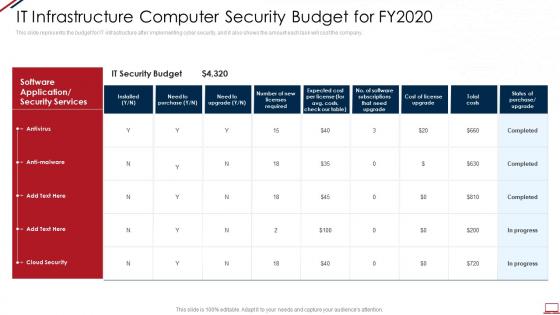 Computer system security it infrastructure computer security budget for fy2020
Computer system security it infrastructure computer security budget for fy2020This slide represents the budget for IT infrastructure after implementing cyber security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Computer System Security It Infrastructure Computer Security Budget For Fy2020. Use it as a tool for discussion and navigation on Cost, IT Security Budget, Software Application Or Security Services, Antivirus, Anti Malware. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it managing data security 60 days plan ppt slides introduction
Data security it managing data security 60 days plan ppt slides introductionThis slide represents the plan for 60 days after implementing the data security model in the organization. Present the topic in a bit more detail with this Data Security IT Managing Data Security 60 Days Plan Ppt Slides Introduction. Use it as a tool for discussion and navigation on Time to Detect Incident, Policy Violations, Data Loss Incidents, Infected Computers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it managing data security 90 days plan ppt slides icons
Data security it managing data security 90 days plan ppt slides iconsThis slide depicts the 90 days plan of the data security model in an organization and training compliance and methods used for communication. Deliver an outstanding presentation on the topic using this Data Security IT Managing Data Security 90 Days Plan Ppt Slides Icons. Dispense information and present a thorough explanation of Training Completion, Communication Methods, Policy Sign Off using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data security it timeline for the implementation of data security
Data security it timeline for the implementation of data securityThis slide shows the timeline for data security model implementation in an organization and the tasks to be performed every month. Present the topic in a bit more detail with this Data Security IT Timeline For The Implementation Of Data Security. Use it as a tool for discussion and navigation on Phishing Exercise, Risk Assessments, Security Documentation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it assessment matrix of cyber risks ppt slides outline
Data security it assessment matrix of cyber risks ppt slides outlineThis slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web or mobile applications, online payments, employee devices. Present the topic in a bit more detail with this Data Security IT Assessment Matrix Of Cyber Risks Ppt Slides Outline. Use it as a tool for discussion and navigation on Systems Involved, Owner Tenant, Mobile, Web Applications, Health Care. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it best practices for cloud security ppt slides portfolio
Data security it best practices for cloud security ppt slides portfolioThis slide represents the best practices for cloud security, such as the shared responsibility model, operations management, building controls, and processes and data encryption. Deliver an outstanding presentation on the topic using this Data Security IT Best Practices For Cloud Security Ppt Slides Portfolio. Dispense information and present a thorough explanation of Operations Management, Building Controls And Processes, Data Encryption, Security And Compliance Monitoring using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
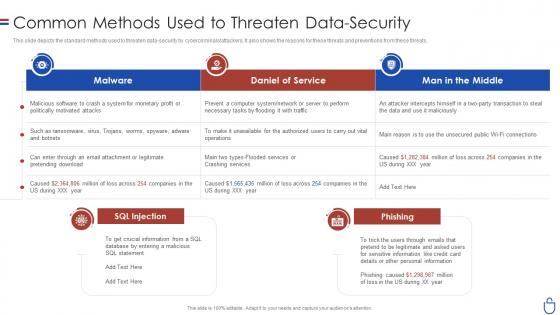 Data security it common methods used to threaten data security
Data security it common methods used to threaten data securityThis slide depicts the standard methods used to threaten data-security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Present the topic in a bit more detail with this Data Security IT Common Methods Used To Threaten Data Security. Use it as a tool for discussion and navigation on Malware, Daniel Service, Man Middle, SQL Injection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
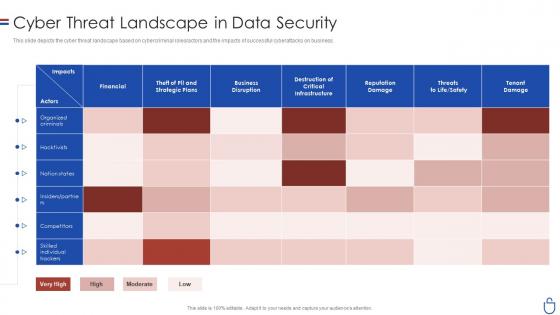 Data security it cyber threat landscape in data security
Data security it cyber threat landscape in data securityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Present the topic in a bit more detail with this Data Security IT Cyber Threat Landscape In Data Security. Use it as a tool for discussion and navigation on Financial, Business Disruption, Reputation Damage, Tenant Damage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
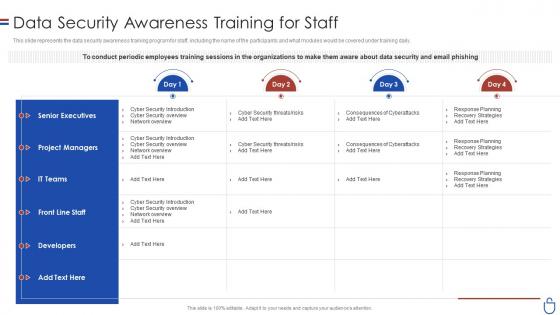 Data security it data security awareness training for staff
Data security it data security awareness training for staffThis slide represents the data security awareness training program for staff, including the name of the participants and what modules would be covered under training daily. Present the topic in a bit more detail with this Data Security IT Data Security Awareness Training For Staff. Use it as a tool for discussion and navigation on Senior Executives, Project Managers, IT Teams, Developers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
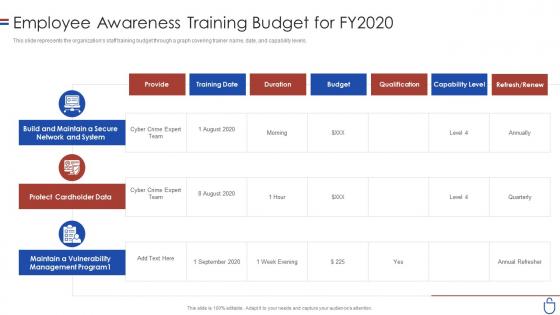 Data security it employee awareness training budget for fy2020
Data security it employee awareness training budget for fy2020This slide represents the organizations staff training budget through a graph covering trainer name, date, and capability levels. Present the topic in a bit more detail with this Data Security IT Employee Awareness Training Budget For FY2020. Use it as a tool for discussion and navigation on Provide, Protect Cardholder Data, Capability Level, Budget, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
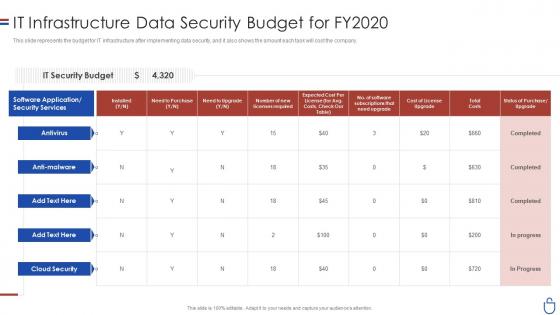 Data security it infrastructure data security budget for fy2020
Data security it infrastructure data security budget for fy2020This slide represents the budget for IT infrastructure after implementing data security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Data Security IT Infrastructure Data Security Budget For FY2020. Use it as a tool for discussion and navigation on IT Security Budget, Need To Purchase, Total Cost, Cost License Upgrade. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IT Security Awareness Communication Plan
IT Security Awareness Communication PlanThe slide showcases communication plan used by companies to ensure proper employee participation in security awareness programs. It contains points such as stakeholder, communication, objective, frequency, assigned to etc. Presenting our well structured IT Security Awareness Communication Plan. The topics discussed in this slide are Communication, Frequency, Additional. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Improving Security By Green Computing Technology Green IT
Improving Security By Green Computing Technology Green ITThis slide outlines how green computing can improve security. The purpose of this slide is to showcase the pillars of data security, security concerns and solution, and different antivirus software that can help users to protect their computers and networks. Deliver an outstanding presentation on the topic using this Improving Security By Green Computing Technology Green IT. Dispense information and present a thorough explanation of Technology, Computing, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IT Department Cyber Security Strategy Action Plan
IT Department Cyber Security Strategy Action PlanThe slide presents IT department cyber security strategy action plan, which assist to evaluate action steps to be taken for effective implementation of plan in a quarter. It contains points such as assigned department, resources needed, benchmark, etc. Introducing our IT Department Cyber Security Strategy Action Plan set of slides. The topics discussed in these slides are Assigned, Department, Resources. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 ERP Security Integration With It In Management
ERP Security Integration With It In ManagementThis slide showcases the IT methodology for ERP security management. Its aim is to strategize and align the team leads for a common goal. This slide contains planning project, build alignment, next steps, etc. Introducing our ERP Security Integration With It In Management set of slides. The topics discussed in these slides are Phase Steps, Phase Outcome. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 IT In Manufacturing Industry V2 Managing Cyber Security In Manufacturing 90 Days Plan
IT In Manufacturing Industry V2 Managing Cyber Security In Manufacturing 90 Days PlanThis slide depicts the next 90 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Deliver an outstanding presentation on the topic using this IT In Manufacturing Industry V2 Managing Cyber Security In Manufacturing 90 Days Plan. Dispense information and present a thorough explanation of Managing Cyber Security, Manufacturing Operations Plan, Security Training Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Cyber Security In Manufacturing 30 Days IT In Manufacturing Industry V2
Managing Cyber Security In Manufacturing 30 Days IT In Manufacturing Industry V2This slide describes the first 30 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Deliver an outstanding presentation on the topic using this Managing Cyber Security In Manufacturing 30 Days IT In Manufacturing Industry V2. Dispense information and present a thorough explanation of Phishing Awareness, Phishing Reporting, Phishing Repeat Offenders, Facility Physical Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Cyber Security In Manufacturing 60 Days IT In Manufacturing Industry V2
Managing Cyber Security In Manufacturing 60 Days IT In Manufacturing Industry V2This slide represents the next 60 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Present the topic in a bit more detail with this Managing Cyber Security In Manufacturing 60 Days IT In Manufacturing Industry V2. Use it as a tool for discussion and navigation on Managing Cyber Security, Manufacturing Operations Plan, Data Loss Incidents. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Classifying IT Audits For Network Security
Classifying IT Audits For Network SecurityThis slide represents categorization of IT Audit for evaluating systems and determining potential risks to establish effectiveness. It includes types such as technology progressive process audit, innovative contrasting audit, technology location audit, etc. Presenting our well structured Classifying IT Audits For Network Security. The topics discussed in this slide are Technology Progressive Process Audit, Innovative Contrasting Audit, Technological Location Audit. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 It Network Security Management Requirements
It Network Security Management RequirementsThis slide showcases the information technology network security management requirements which helps an organization to address ever expanding matrix of users and locations. It include details such as network deployment, configuration, security, etc. Presenting our well structured It Network Security Management Requirements. The topics discussed in this slide are Network Deployment, Feature Configuration, Network Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
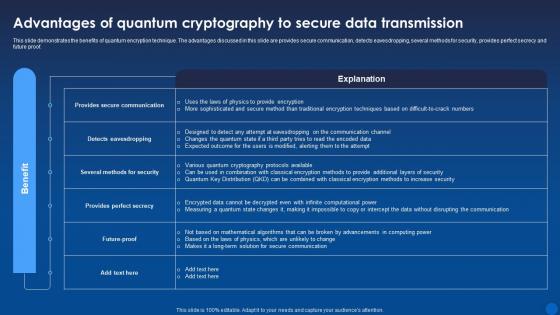 Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It
Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age ItThis slide demonstrates the benefits of quantum encryption technique. The advantages discussed in this slide are provides secure communication, detects eavesdropping, several methods for security, provides perfect secrecy and future proof. Present the topic in a bit more detail with this Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Quantum, Cryptography, Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages and disadvantages of Internet protocol Security IPsec technology. The various benefits explained in this slide are strong security, broad compatibility, flexibility, scalability and efficient network performance. Deliver an outstanding presentation on the topic using this Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Key Management, Performance Impact, Compatibility Issues using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide talks about the Hypertext Transfer Protocol Secure HTTPS, which is an advance version of HTTP. The purpose of this slide is to discuss the importance of using HTTPS to encrypt communication between browser and server. Present the topic in a bit more detail with this Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Introduction, Overview, Protocol Secure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss the main components of Internet Protocol Security IPsec architecture. These three components are Encapsulating Security Payload ESP, Authentication Header AH, and Internet Key Exchange IKE. Deliver an outstanding presentation on the topic using this Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Authentication Header, Internet Key Exchange, Encapsulating Security Payload using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age It
Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to highlight the benefits and capabilities of Hardware Security Modules HSMs. The key components included are cloud server, private key, encrypted request, encrypted data, HSM isolated environment, etc. Deliver an outstanding presentation on the topic using this Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Relationship, Hardware, Cryptographic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age It
Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the role of HTTPS in encrypting web communication and use of the Secure Sockets Layer SSL protocol for secure connections. This slide also discusses the incorporation of symmetric and asymmetric encryption during the SSL handshake. Deliver an outstanding presentation on the topic using this Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Technology, Asymmetric, Symmetric using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age It
Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the working steps of Internet Protocol Security connections. These are key exchange, packet headers and trailers, packet authentication, encryption, data transmission and decryption of data packets. Deliver an outstanding presentation on the topic using this Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Connections, Protocol Security, Data Transmission using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThis slide talks about the distinction between the two methods of protecting information transmission. The purpose of this slide is to explain the concepts of transport mode and tunnel mode in the context of securing data during communication. Present the topic in a bit more detail with this Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Transport Mode, Protocol Security, Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide illustrates the flow of several components in the working of Hypertext Transfer Protocol Secure HTTPS. The purpose of this slide is to showcase how data is encrypted in transit and transferred to the user using public and private keys. Present the topic in a bit more detail with this Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric Encryption, Symmetric Encryption, Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementing Effective Software Testing Existing IT Security Infrastructure Constituents
Implementing Effective Software Testing Existing IT Security Infrastructure ConstituentsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. These constituents are regulatory and compliance, budget, complex integration, and so on. Present the topic in a bit more detail with this Implementing Effective Software Testing Existing IT Security Infrastructure Constituents. Use it as a tool for discussion and navigation on Complex Integration, Strict Compliance Requirements, Functional Disrupt, IT Security Infrastructure Constituents. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Existing IT Security Strategic Implementation Of Regression Testing
Existing IT Security Strategic Implementation Of Regression TestingThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. These constituents are vulnerability scanners, improper functioning, functional disrupt, and so on. Deliver an outstanding presentation on the topic using this Existing IT Security Strategic Implementation Of Regression Testing. Dispense information and present a thorough explanation of Existing IT Security, Infrastructure Constituents using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Application Security Training Schedule For IT Teams
Application Security Training Schedule For IT TeamsThis slide represents the training schedule for IT teams in an organization to efficiently implementing application security. Deliver an outstanding presentation on the topic using this Application Security Training Schedule For IT Teams. Dispense information and present a thorough explanation of Application Security Fundamentals, Application Security Deployment, Application Security Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Implementing Effective Tokenization Existing IT Security Infrastructure Threats
Implementing Effective Tokenization Existing IT Security Infrastructure ThreatsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. Present the topic in a bit more detail with this Implementing Effective Tokenization Existing IT Security Infrastructure Threats. Use it as a tool for discussion and navigation on Compliance Challenges, Resource Intensiveness, Faced Security Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Tokenization For Improved Data Security Training Schedule For It Teams To Conduct Tokenization
Tokenization For Improved Data Security Training Schedule For It Teams To Conduct TokenizationThis slide represents the training schedule for IT teams in an organization to efficiently carry out tokenization. It includes the time slots for training, total days of training, and the modules to be covered in the training. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Training Schedule For IT Teams To Conduct Tokenization. Dispense information and present a thorough explanation of Tokenization Implementation, Tokenization Architecture, Tokenization Fundamentals using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Application Security Implementation Plan Application Security Training Program For IT Team
Application Security Implementation Plan Application Security Training Program For IT TeamThis slide highlights the comprehensive training program for software testers which aims to train beginners about application security. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Application Security Training Program For IT Team. Dispense information and present a thorough explanation of Understanding Functionalities, Application Security, Training Program using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Application Security Implementation Plan Existing IT Security Infrastructure Threats
Application Security Implementation Plan Existing IT Security Infrastructure ThreatsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Existing IT Security Infrastructure Threats. Dispense information and present a thorough explanation of Broken Authentication, Cross Site Scripting, Denial Of Service, Infrastructure Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparison Between Secure Web Internet Gateway Security IT
Comparison Between Secure Web Internet Gateway Security ITThis slide demonstrates the concept of cloud security gateways and Secure Web Gateways. The purpose of this slide is to compare cloud security gateways and SWGs on the basis of various factors such as scope, deployment, architecture, features and cost. Present the topic in a bit more detail with this Comparison Between Secure Web Internet Gateway Security IT. Use it as a tool for discussion and navigation on Parameter, Scope, Deployment, Architecture, Features, Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Internet Gateway Security IT Before Vs After Implementing Secure Web
Internet Gateway Security IT Before Vs After Implementing Secure WebThis slide compares the scenario after integrating SWG in organizational network. The purpose of this slide is to represent before and after situation based on several parameters. The factors used to do the comparison are cost, security, productivity, etc. Present the topic in a bit more detail with this Internet Gateway Security IT Before Vs After Implementing Secure Web. Use it as a tool for discussion and navigation on Security, Visibility, Compliance, Productivity, Costs. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Internet Gateway Security IT Checklist To Implement Secure Web Gateway
Internet Gateway Security IT Checklist To Implement Secure Web GatewayThis slide represents the checklist to implement Secure Web Gateway for application security. The key components included are determine use case, select best solution, plan deployment, configure solution, test and improve, roll out and monitor. Present the topic in a bit more detail with this Internet Gateway Security IT Checklist To Implement Secure Web Gateway. Use it as a tool for discussion and navigation on Determine Use Case, Select Best Solution, Plan Deployment, Configure Solution, Test And Improve, Roll Out And Monitor. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Internet Gateway Security IT Comparison Between Secure Web Gateway
Internet Gateway Security IT Comparison Between Secure Web GatewayThis slide demonstrates the concept of two security technologies named firewalls and Secure Web Gateways. The purpose of this slide is to compare firewalls and SWGs on the basis of various factors such as function, scope, granularity, features and deployment. Present the topic in a bit more detail with this Internet Gateway Security IT Comparison Between Secure Web Gateway. Use it as a tool for discussion and navigation on Function, Scope, Granularity, Features, Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Internet Gateway Security IT Estimated Budget Of Secure Web Gateway
Internet Gateway Security IT Estimated Budget Of Secure Web GatewayThis slide represents the budget of integrating Secure Web Gateway in organization. The purpose of this slide is to showcase the estimated and actual cost for installing SWG. These include hardware and software, maintenance and support, training, etc. Present the topic in a bit more detail with this Internet Gateway Security IT Estimated Budget Of Secure Web Gateway. Use it as a tool for discussion and navigation on Hardware And Software, Maintenance And Support, Training, Third Party Services, Deployment Team. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Internet Gateway Security IT Impact Of Secure Web Gateway On Application
Internet Gateway Security IT Impact Of Secure Web Gateway On ApplicationThis slide represents the various factors which showcase the improvement of application security after adopting SWG. The parameters discussed are enhanced protection against web-based attacks, content filtering, policy enforcement, Data Loss Prevention, etc. Present the topic in a bit more detail with this Internet Gateway Security IT Impact Of Secure Web Gateway On Application. Use it as a tool for discussion and navigation on Parameters, Content Filtering, Policy Enforcement, Data Loss Prevention. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Internet Gateway Security IT Methods To Implement Security Policies
Internet Gateway Security IT Methods To Implement Security PoliciesThis slide demonstrates the different ways to enforce policies on remote and on-site employees using SWG. These are data loss prevention, encrypted traffic examination, protocol support, integration with anti-malware zero-day products, location flexibility, etc. Present the topic in a bit more detail with this Internet Gateway Security IT Methods To Implement Security Policies. Use it as a tool for discussion and navigation on Data Loss Prevention, Encrypted Traffic Examination, Protocol Support, Constant Security Monitoring. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Internet Gateway Security IT Secure Web Gateway Challenges And Solutions
Internet Gateway Security IT Secure Web Gateway Challenges And SolutionsThis slide outlines the limitations of Secure Web Gateway such as increasingly sophisticated threats, encrypted traffic, cloud-based applications and mobile devices. This purpose of this slide is to explain the possible solutions to these challenges. Present the topic in a bit more detail with this Internet Gateway Security IT Secure Web Gateway Challenges And Solutions. Use it as a tool for discussion and navigation on Increasingly, Sophisticated Threats, Encrypted Traffic, Cloud-Based Applications, Mobile Devices. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Internet Gateway Security IT Secure Web Gateway Training Program
Internet Gateway Security IT Secure Web Gateway Training ProgramThis slide represents the training program for the Secure Web Gateway. The main components of training program are agenda, system requirements, mode such as online, offline or recorded videos, and cost. Present the topic in a bit more detail with this Internet Gateway Security IT Secure Web Gateway Training Program. Use it as a tool for discussion and navigation on Agenda, System Requirements, Mode, Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 OT Cyber Security Training Schedule For It Employees
OT Cyber Security Training Schedule For It EmployeesThis slide represents training plan that assist companies to educate their IT employee for enhancing operational technology cyber security effectively. It includes various elements such as course, details, timings, modules, mode, etc. Introducing our OT Cyber Security Training Schedule For It Employees set of slides. The topics discussed in these slides are Details, Timings, ModulesThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Penetration Testing Implementation Plan Existing It Security Infrastructure Constituants
Penetration Testing Implementation Plan Existing It Security Infrastructure ConstituantsThis slide highlights the components of the current IT security infrastructure, which are prone to several security concerns. These constituents are access control, application security, firewalls, virtual private networks VPN, antivirus, etc. Deliver an outstanding presentation on the topic using this Penetration Testing Implementation Plan Existing It Security Infrastructure Constituants. Dispense information and present a thorough explanation of Access Control, Application Security, Antivirus Or Antimalware Systems, Password Auditing Tools using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Penetration Testing Implementation Plan Key Challenges Of Existing It Security
Penetration Testing Implementation Plan Key Challenges Of Existing It SecurityThis slide discusses the security issues faced by the organization due to a lack of security in infrastructure. These concerns are unauthorized access, data breaches, malware and ransomware, phishing attacks, data loss or corruption, compliance, etc. Deliver an outstanding presentation on the topic using this Penetration Testing Implementation Plan Key Challenges Of Existing It Security. Dispense information and present a thorough explanation of Unauthorized Access, Data Breaches, Malware And Ransomware, Phishing Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Existing It Security Infrastructure Constituent Vpn Implementation Plan
Existing It Security Infrastructure Constituent Vpn Implementation PlanThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns.Deliver an outstanding presentation on the topic using this Existing It Security Infrastructure Constituent Vpn Implementation Plan. Dispense information and present a thorough explanation of Constituent, Problems Observed, Incidents Observed using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Web Security Upgradation Web Security Training Program For It Team
Web Security Upgradation Web Security Training Program For It TeamThis slide highlights the comprehensive training program for IT teams which aims to train beginners about web security. Present the topic in a bit more detail with this Web Security Upgradation Web Security Training Program For It Team. Use it as a tool for discussion and navigation on Modules, Training Hours, Hands-On Application Security Basics. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Budget Plan For IT Security Awareness Training Program Cybersecurity SS
Budget Plan For IT Security Awareness Training Program Cybersecurity SSThis slide represents the budget prepared to predict cash flows and allocate required resources for IT security awareness training program. It includes parameters such as mooc courses etc. Deliver an outstanding presentation on the topic using this Budget Plan For IT Security Awareness Training Program Cybersecurity SS. Dispense information and present a thorough explanation of External Trainers Fee, Ransomware Management, Social Engineering Management, Password Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist To Ensure Effective Completion Of IT Security Awareness Training Cybersecurity SS
Checklist To Ensure Effective Completion Of IT Security Awareness Training Cybersecurity SSThis slide represents checklist for promoting strategy adopted by security professionals for preventing and mitigating cyber security risks. It includes activities such as gain executive buy-in etc. Present the topic in a bit more detail with this Checklist To Ensure Effective Completion Of IT Security Awareness Training Cybersecurity SS. Use it as a tool for discussion and navigation on Organizational Activities, Security Awareness Training, Ensure Effective Completion. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparative Assessment Of IT Security Awareness Training Tools Cybersecurity SS
Comparative Assessment Of IT Security Awareness Training Tools Cybersecurity SSThis slide represents comparison between IT security awareness training tools based on features such as audio mixing, text animation, time mapping, titles and captions etc. Deliver an outstanding presentation on the topic using this Comparative Assessment Of IT Security Awareness Training Tools Cybersecurity SS. Dispense information and present a thorough explanation of Time Mapping, Text Animation, Tram Reviews, Security Awareness Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Incident Management Team Roles IT Security Awareness Training Cybersecurity SS
Cyber Security Incident Management Team Roles IT Security Awareness Training Cybersecurity SSThis slide represents the duties performed by the various members of the cyber incident management team. It includes roles and responsivities of ICT technical support staff, crisis manager etc. Deliver an outstanding presentation on the topic using this Cyber Security Incident Management Team Roles IT Security Awareness Training Cybersecurity SS. Dispense information and present a thorough explanation of Cyber Security Incident Response, Management, Roles And Responsibilities, Network Management Capabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IT Security Awareness Training Defense Against Cyber Threats Cybersecurity SS
IT Security Awareness Training Defense Against Cyber Threats Cybersecurity SSThis slide represents details related to ways security awareness training helps in preventing and mitigating common threats faced by organization such as data breaches, phishing attacks etc. Deliver an outstanding presentation on the topic using this IT Security Awareness Training Defense Against Cyber Threats Cybersecurity SS. Dispense information and present a thorough explanation of Data Breaches, Phishing Attacks, Insider Threats, Social Engineering using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Robust Password Management Training For End Users IT Security Awareness Training Cybersecurity SS
Robust Password Management Training For End Users IT Security Awareness Training Cybersecurity SSThis slide represents training plan for robust management of verifying identity of user accessing a digital system. It includes details related to training modules such as beyond passwords etc. Present the topic in a bit more detail with this Robust Password Management Training For End Users IT Security Awareness Training Cybersecurity SS. Use it as a tool for discussion and navigation on Beyond Passwords, Multi Factor Authentication, Password Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategic Password Authentication Training Plan IT Security Awareness Training Cybersecurity SS
Strategic Password Authentication Training Plan IT Security Awareness Training Cybersecurity SSThis slide represents training plan for verifying identity of user accessing a digital system. It includes details related to password authentication methods, training sessions etc. Deliver an outstanding presentation on the topic using this Strategic Password Authentication Training Plan IT Security Awareness Training Cybersecurity SS. Dispense information and present a thorough explanation of Token Authentication, Biometric Authentication, Strategic Password, Authentication Training Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Training Plan For Detecting Phishing Attacks IT Security Awareness Training Cybersecurity SS
Training Plan For Detecting Phishing Attacks IT Security Awareness Training Cybersecurity SSThis slide represents details related to training plan to assist employees in detecting phishing attacks. It includes details related to training topics such as general signs of phishing attacks etc. Present the topic in a bit more detail with this Training Plan For Detecting Phishing Attacks IT Security Awareness Training Cybersecurity SS. Use it as a tool for discussion and navigation on Manufactured Rapport Or History, Manufactured Urgency, Sensitive Questions As Standard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Training Plan For Detecting Ransomware Attacks IT Security Awareness Training Cybersecurity SS
Training Plan For Detecting Ransomware Attacks IT Security Awareness Training Cybersecurity SSThis slide represents training plan for detecting to malware that is designed to deny a user or organization access to files on their computer or networks. It includes details related to detection techniques etc. Deliver an outstanding presentation on the topic using this Training Plan For Detecting Ransomware Attacks IT Security Awareness Training Cybersecurity SS. Dispense information and present a thorough explanation of Signature Based Detection, Detection Based On Traffic, Detection By Data Behavior using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Training Plan For Preventing Phishing Attacks IT Security Awareness Training Cybersecurity SS
Training Plan For Preventing Phishing Attacks IT Security Awareness Training Cybersecurity SSThis slide represents training plan to assist employees in effectively preventing phishing attacks. It includes details related to training topics such as email communication and hyperlinks etc. Present the topic in a bit more detail with this Training Plan For Preventing Phishing Attacks IT Security Awareness Training Cybersecurity SS. Use it as a tool for discussion and navigation on Report Phishing Attempts, Email Communications And Hyperlinks, Best Practices For Handling Mails. This template is free to edit as deemed fit for your organization. Therefore download it now.



