Powerpoint Templates and Google slides for Implementing Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Internet security electronic payment system eviction ec implementation
Internet security electronic payment system eviction ec implementationPresenting this set of slides with name - Internet Security Electronic Payment System Eviction Ec Implementation. This is an editable seven stages graphic that deals with topics like Internet Security Electronic Payment System, Eviction Ec Implementation to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security implementation ppt powerpoint presentation infographic template outfit cpb
Security implementation ppt powerpoint presentation infographic template outfit cpbPresenting this set of slides with name Security Implementation Ppt Powerpoint Presentation Infographic Template Outfit Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Security Implementation to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Steps for developing and implementing it security controls
Steps for developing and implementing it security controlsIntroducing our premium set of slides with Steps For Developing And Implementing IT Security Controls. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access, Eventuality, Training. So download instantly and tailor it with your information.
-
 Information security governance management implementation model
Information security governance management implementation modelPresenting our set of slides with name Information Security Governance Management Implementation Model. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Organizational Structure, Strategic Planning For Risk Mitigation, Security Management, Roles And Responsibilities.
-
 Key advantage bottom approach security implementation ppt powerpoint presentation pictures example topics cpb
Key advantage bottom approach security implementation ppt powerpoint presentation pictures example topics cpbPresenting our Key Advantage Bottom Approach Security Implementation Ppt Powerpoint Presentation Pictures Example Topics Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Key Advantage Bottom Approach Security Implementation This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 It security operations facilities offered by successful implementation ppt powerpoint download
It security operations facilities offered by successful implementation ppt powerpoint downloadThis slide portrays information regarding the various facilities that are offered by successful implementation of SecOps in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Introducing IT Security Operations Facilities Offered By Successful Implementation Ppt Powerpoint Download to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Malware Detection And Investigation, Phishing Detection And Prevention, Investigations By Hr, Risk Mitigation Of Left Employees, using this template. Grab it now to reap its full benefits.
-
 Enterprise security operations facilities offered by successful implementation ppt powerpoint guide
Enterprise security operations facilities offered by successful implementation ppt powerpoint guideThis slide portrays information regarding the various facilities that are offered by successful implementation of SecOps in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Introducing Enterprise Security Operations Facilities Offered By Successful Implementation Ppt Powerpoint Guide to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Malware Detection And Investigation, Phishing Detection And Prevention, Investigations By Hr, Risk Mitigation Of Left Employees, using this template. Grab it now to reap its full benefits.
-
 Enhanced security event management facilities offered by successful implementation ppt images
Enhanced security event management facilities offered by successful implementation ppt imagesThis slide portrays information regarding the various facilities that are offered by successful implementation of SecOps in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Introducing Enhanced Security Event Management Facilities Offered By Successful Implementation Ppt Images to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Malware Detection And Investigation, Phishing Detection And Prevention, Investigations By Hr, Risk Mitigation Of Left Employees, using this template. Grab it now to reap its full benefits.
-
 Implementing security management plan security risk management checklist
Implementing security management plan security risk management checklistThis slide shows a security risk management assessment checklist with multiple categories. Introducing Implementing Security Management Plan Security Risk Management Checklist to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Policy Document, Risks, Security, Incidents, using this template. Grab it now to reap its full benefits.
-
 Measures management challenges implementing security management plan
Measures management challenges implementing security management planSecurity Breaches, Mitigate Challenges, Assessments Increase audience engagement and knowledge by dispensing information using Measures Management Challenges Implementing Security Management Plan. This template helps you present information on seve stages. You can also present information on Security Breaches, Mitigate Challenges, Assessments using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Facilities rendered by security centre implementation management to improve project safety it
Facilities rendered by security centre implementation management to improve project safety itThis slide provides information regarding the various facilities that are offered by successful implementation of security center in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Increase audience engagement and knowledge by dispensing information using Facilities Rendered By Security Centre Implementation Management To Improve Project Safety IT. This template helps you present information on four stages. You can also present information on Malware Detection And Investigation, Phishing Detection And Prevention, Investigations By HR, Risk Mitigation Of Left Employees using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Electronic information security implementation strong password policy
Electronic information security implementation strong password policyThis slide depicts the importance of having strong passwords for different online accounts. It also shows the number of users who use the same password across other accounts. Introducing Electronic Information Security Implementation Strong Password Policy to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Special Characters, Employees, Protected Accounts, using this template. Grab it now to reap its full benefits.
-
 Implement traffic monitoring to secure redis server ppt portfolio information
Implement traffic monitoring to secure redis server ppt portfolio informationThis slide describes implementing traffic monitoring to check the usage patterns and raise flags to incase anything unusual happens. Introducing Implement Traffic Monitoring To Secure Redis Server Ppt Portfolio Information to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Implement Traffic Monitoring To Secure Redis Server, using this template. Grab it now to reap its full benefits.
-
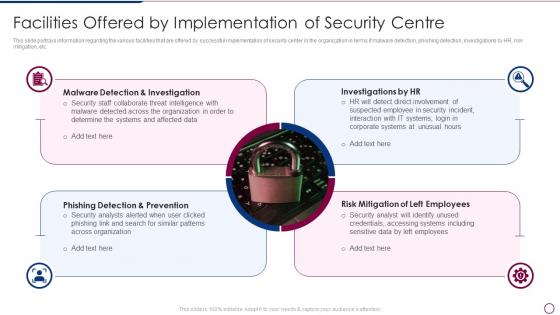 Unlocking Business Infrastructure Capabilities Facilities Offered By Implementation Of Security Centre
Unlocking Business Infrastructure Capabilities Facilities Offered By Implementation Of Security CentreThis slide portrays information regarding the various facilities that are offered by successful implementation of security center in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Increase audience engagement and knowledge by dispensing information using Unlocking Business Infrastructure Capabilities Facilities Offered By Implementation Of Security Centre. This template helps you present information on four stages. You can also present information on Investigation, Implementation, Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategies We Will Implement To Make Building A Security Awareness Program
Strategies We Will Implement To Make Building A Security Awareness ProgramThe purpose of this slide is to exhibit variety of strategies which can be used to engage employees in the security awareness training plan. The strategies highlighted in the slide are gamification, personalization, high quality content and variety. Increase audience engagement and knowledge by dispensing information using Strategies We Will Implement To Make Building A Security Awareness Program. This template helps you present information on four stages. You can also present information on Gamification, Personalization, High Quality Content using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Conducting Security Awareness Strategies We Will Implement To Make Security Awareness
Conducting Security Awareness Strategies We Will Implement To Make Security AwarenessThe purpose of this slide is to exhibit variety of strategies which can be used to engage employees in the security awareness training plan. The strategies highlighted in the slide are gamification, personalization, high-quality content and variety. Introducing Conducting Security Awareness Strategies We Will Implement To Make Security Awareness to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Gamification, Personalization, High Quality Content, using this template. Grab it now to reap its full benefits.
-
 Strategies We Will Implement To Make Security Awareness Training Interactive Developing Cyber Security Awareness
Strategies We Will Implement To Make Security Awareness Training Interactive Developing Cyber Security AwarenessThe purpose of this slide is to exhibit variety of strategies which can be used to engage employees in the security awareness training plan. The strategies highlighted in the slide are gamification, personalization, high quality content and variety. Introducing Strategies We Will Implement To Make Security Awareness Training Interactive Developing Cyber Security Awareness to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Gamification, Personalization, High Quality Content, Variety, using this template. Grab it now to reap its full benefits.
-
 Managing Mobile Device Solutions For Workforce Implementing Mobile Device Security Framework Roadmap
Managing Mobile Device Solutions For Workforce Implementing Mobile Device Security Framework RoadmapThis slide portrays information regarding optimization of current mobile device security framework. The IT department will require to fulfill crucial activities in specific timeframe. Increase audience engagement and knowledge by dispensing information using Managing Mobile Device Solutions For Workforce Implementing Mobile Device Security Framework Roadmap. This template helps you present information on three stages. You can also present information on Security Program, Control Environment, Security Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Stakeholders Of Cyber Security Awareness Training Implementing Security Awareness Training
Key Stakeholders Of Cyber Security Awareness Training Implementing Security Awareness TrainingIncrease audience engagement and knowledge by dispensing information using Key Stakeholders Of Cyber Security Awareness Training Implementing Security Awareness Training. This template helps you present information on three stages. You can also present information on Senior Mangers, Line Managers, Employees using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Statistics Highlighting Lack Of Cyber Security Awareness Implementing Security Awareness Training
Statistics Highlighting Lack Of Cyber Security Awareness Implementing Security Awareness TrainingThe purpose of this slide is to outline various statistics showing the lack of security awareness amongst the employees. The statistics covered in the slide is related to malware infection, using personal cloud server, malicious attachment etc. Introducing Statistics Highlighting Lack Of Cyber Security Awareness Implementing Security Awareness Training to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Statistics Highlighting, Security Awareness, Amongst Employees, using this template. Grab it now to reap its full benefits.
-
 Strategies We Will Implement To Make Security Awareness Implementing Security Awareness Training
Strategies We Will Implement To Make Security Awareness Implementing Security Awareness TrainingThe purpose of this slide is to exhibit variety of strategies which can be used to engage employees in the security awareness training plan. The strategies highlighted in the slide are gamification, personalization, high-quality content and variety. Increase audience engagement and knowledge by dispensing information using Strategies We Will Implement To Make Security Awareness Implementing Security Awareness Training. This template helps you present information on four stages. You can also present information on Gamification, Personalization, High Quality Content using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategies We Will Implement To Make Security Awareness Preventing Data Breaches Through Cyber Security
Strategies We Will Implement To Make Security Awareness Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to exhibit variety of strategies which can be used to engage employees in the security awareness training plan. The strategies highlighted in the slide are gamification, personalization, high quality content and variety. Increase audience engagement and knowledge by dispensing information using Strategies We Will Implement To Make Security Awareness Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Gamification, Personalization, High Quality Content using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Managing Mobile Devices For Optimizing Implementing Mobile Device Security Framework Roadmap
Managing Mobile Devices For Optimizing Implementing Mobile Device Security Framework RoadmapThis slide portrays information regarding optimization of current mobile device security framework. The IT department will require to fulfill crucial activities in specific timeframe. Increase audience engagement and knowledge by dispensing information using Managing Mobile Devices For Optimizing Implementing Mobile Device Security Framework Roadmap. This template helps you present information on three stages. You can also present information on Enterprise Security Program, Control Environment, Security Processes, Security Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementing Cyber Security Awareness Raising Cyber Security Awareness In Organizations
Implementing Cyber Security Awareness Raising Cyber Security Awareness In OrganizationsThe purpose of this slide is to delineate a comprehensive security awareness training program that can assist corporates to mitigate cyber attacks and reduce downtime. Information covered in this slide is related to training goals, major topics to cover and projected result. Introducing Implementing Cyber Security Awareness Raising Cyber Security Awareness In Organizations to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Training Objective, Topics To Cover, Expected Result, using this template. Grab it now to reap its full benefits.
-
 Strategies We Will Implement To Make Security Raising Cyber Security Awareness In Organizations
Strategies We Will Implement To Make Security Raising Cyber Security Awareness In OrganizationsThe purpose of this slide is to exhibit variety of strategies which can be used to engage employees in the security awareness training plan. The strategies highlighted in the slide are gamification, personalization, high quality content and variety. Introducing Strategies We Will Implement To Make Security Raising Cyber Security Awareness In Organizations to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Gamification, Personalization, High Quality Content, using this template. Grab it now to reap its full benefits.
-
 Various Key Levels In Implementing Infrastructure Security
Various Key Levels In Implementing Infrastructure SecurityThe following slide showcases different levels of infra security which aims to boost safety measures and minimize downtime. It presents information related to physical, network, application and data level. Introducing Various Key Levels In Implementing Infrastructure Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Physical, Network, Application, using this template. Grab it now to reap its full benefits.
-
 Impact Of Cybersecurity Incidents On Organization Development And Implementation Of Security Incident
Impact Of Cybersecurity Incidents On Organization Development And Implementation Of Security IncidentThis slide represents the impact of events which indicates that organizations data has been compromised for unlawful activities. It includes impact of cyber security events such as increased costs, operational disruption, reputational damage etc. Increase audience engagement and knowledge by dispensing information using Impact Of Cybersecurity Incidents On Organization Development And Implementation Of Security Incident. This template helps you present information on five stages. You can also present information on Increased Costs, Operational Disruption, Reputational Damage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Most Commonly Types Of ICT Securities Used Implementation Of ICT Strategic Plan Strategy SS
Most Commonly Types Of ICT Securities Used Implementation Of ICT Strategic Plan Strategy SSThis slide represents various types of information and communication technology ICT securities used by businesses. It covers network security, endpoint security, access security, and data encryption.Introducing Most Commonly Types Of ICT Securities Used Implementation Of ICT Strategic Plan Strategy SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Network Security, End Point Security, Access Security, using this template. Grab it now to reap its full benefits.
-
 Principles Of Enterprise Blockchain Security Implementation
Principles Of Enterprise Blockchain Security ImplementationThis slide highlights principles for blockchain security implementation aimed at implementing technology to strengthen platform by aligning with current trends. It covers open source, permissioning, governance, security and standards. Introducing our premium set of slides with Principles Of Enterprise Blockchain Security Implementation. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Permissioning, Security, Open Source, Governance. So download instantly and tailor it with your information.
-
 Advantages Of Blockchain Implementing Blockchain Security Solutions
Advantages Of Blockchain Implementing Blockchain Security SolutionsThis slide represents the various advantages of blockchain technology based on information security, digital freedom, privacy, and lower transaction fees.Introducing Advantages Of Blockchain Implementing Blockchain Security Solutions to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Immutable Information, Anonymity Privacy, No Intermediaries, using this template. Grab it now to reap its full benefits.
-
 Bitcoin Vs Blockchain Technology Implementing Blockchain Security Solutions
Bitcoin Vs Blockchain Technology Implementing Blockchain Security SolutionsThis slide defines the difference between bitcoin and blockchain technology based on goal, trade, scope, strategy and status.Increase audience engagement and knowledge by dispensing information using Bitcoin Vs Blockchain Technology Implementing Blockchain Security Solutions. This template helps you present information on five stages. You can also present information on Efficiently Government Restrictions, Numerical Sequence, Property Currency using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How Fraudsters Attack Implementing Blockchain Security Solutions
How Fraudsters Attack Implementing Blockchain Security SolutionsThis slide describes the primary attacks that hackers can use to exploit blockchain technology networks. The purpose of this slide is to showcase some basic threats that hackers can use to manipulate a blockchain network, such as phishing attacks, routing attacks, sybil, and 51 precent.Increase audience engagement and knowledge by dispensing information using How Fraudsters Attack Implementing Blockchain Security Solutions. This template helps you present information on four stages. You can also present information on Phishing Attacks, Routing Attacks, Sybil Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies Transport Layer Security Implementation Using Handshake
Encryption Implementation Strategies Transport Layer Security Implementation Using HandshakeThis slide discusses a cryptographic system known as transport layer security TLS. The purpose of this slide is to explain how TLS enables safe communication over computer networks using handshake protocol and record protocol. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Transport Layer Security Implementation Using Handshake. This template helps you present information on two stages. You can also present information on Transport Layer Security Implementation, Handshake And Record Protocol, Computer Networks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Build Cyber Security Team Structure Implementing Strategies To Mitigate Cyber Security Threats
Build Cyber Security Team Structure Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the organizational cyber security team hierarchy to prevent sensitive data loss and damage. It mainly includes elements such as security manager, engineer, analyst, chief information security officer etc Increase audience engagement and knowledge by dispensing information using Build Cyber Security Team Structure Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on four stages. You can also present information on Security Manager, Security Engineer, Security Analyst using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementing Wireless Internet Security For Smart Home
Implementing Wireless Internet Security For Smart HomeThe following slide illustrates the implementation of wireless internet security in smart homes, emphasizing router setup, strong passwords, separate networks for IoT devices, 2FA, and NGFW, providing valuable guidance for securing connected environments Introducing our premium set of slides with Implementing Wireless Internet Security For Smart Home. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Set Up Router Correctly, Use Super Strong Passwords, Implementing. So download instantly and tailor it with your information.
-
 Internet Gateway Security IT Secure Web Gateway Implementation Scenarios
Internet Gateway Security IT Secure Web Gateway Implementation ScenariosThis slide represents the different types of Secure Web Gateway deployment methods. The purpose of this slide is to outline SWG implementation methodologies. These are inline, explicit, transparent and SPAN Switched Port Analyzer port. Introducing Internet Gateway Security IT Secure Web Gateway Implementation Scenarios to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Inline, Transparent, Explicit, SPAN, using this template. Grab it now to reap its full benefits.
-
 Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SS
Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SSThis slide showcases procedure that can help organization to implement mobile device management solution. Its key steps are current scenario assessment, policy development, choose solution etc. Increase audience engagement and knowledge by dispensing information using Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SS This template helps you present information on Five stages. You can also present information on Estimated Budget, Phase Duration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps To Implement Identity And Access Management In Enterprises Securing Systems With Identity
Steps To Implement Identity And Access Management In Enterprises Securing Systems With IdentityThis slide discusses the Identity and Access Management implementing process in enterprises. The purpose of this slide is to highlight the implementation process, including usage assessment, environment understanding, key IAM considerations, and so on. Introducing Steps To Implement Identity And Access Management In Enterprises Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Usage Assessment, Environment Understanding using this template. Grab it now to reap its full benefits.
-
 Penetration Testing Implementation Plan Performance Analysis Of Existing It Security
Penetration Testing Implementation Plan Performance Analysis Of Existing It SecurityThe purpose of this slide is to indicate the performance analysis of the organizations current security infrastructure. The key components include where we are, the gap, where we want to be, and recommended solutions. Increase audience engagement and knowledge by dispensing information using Penetration Testing Implementation Plan Performance Analysis Of Existing It Security. This template helps you present information on Four stages. You can also present information on Ideal Testing, Organization, Penetration Testing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


