Powerpoint Templates and Google slides for Implementing Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Business security implementation ppt powerpoint presentation pictures background cpb
Business security implementation ppt powerpoint presentation pictures background cpbPresenting this set of slides with name Business Security Implementation Ppt Powerpoint Presentation Pictures Background Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Business Security Implementation to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Implement enterprise security ppt powerpoint presentation outline format ideas cpb
Implement enterprise security ppt powerpoint presentation outline format ideas cpbPresenting this set of slides with name Implement Enterprise Security Ppt Powerpoint Presentation Outline Format Ideas Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Implement Enterprise Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Implement security ppt presentation infographics slides cpb
Implement security ppt presentation infographics slides cpbPresenting this set of slides with name Implement Security Ppt Presentation Infographics Slides Cpb. This is an editable Powerpoint seven stages graphic that deals with topics like Implement Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security implementation process with strategize and plan
Security implementation process with strategize and planPresenting this set of slides with name Security Implementation Process With Strategize And Plan. This is a three stage process. The stages in this process are Assess And Learn, Strategize And Plan, Implement And Support. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Implement security system ppt powerpoint presentation gallery inspiration cpb
Implement security system ppt powerpoint presentation gallery inspiration cpbPresenting our Implement Security System Ppt Powerpoint Presentation Gallery Inspiration Cpbs PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Implement Security System This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security protection implementation ppt powerpoint presentation ideas model cpb
Security protection implementation ppt powerpoint presentation ideas model cpbPresenting Security Protection Implementation Ppt Powerpoint Presentation Ideas Model Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Protection Implementation. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Security awareness training roadmap implementing security awareness program ppt slides
Security awareness training roadmap implementing security awareness program ppt slidesThis slide covers the roadmap for training concepts and guidelines on security awareness to advise and plan the company for a comprehensive training program. Introducing Security Awareness Training Roadmap Implementing Security Awareness Program Ppt Slides to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Safe And Computing Best Practices, Ensuring Data Security, Ensuring Physical Security, using this template. Grab it now to reap its full benefits.
-
 It security operations current challenges faced by firm while implementing secops ppt infographics
It security operations current challenges faced by firm while implementing secops ppt infographicsThis slide portrays information regarding the present challenges faced by firm while implementing SecOps system including budget constraint, absence of pool of talent and expertise and lack of essential tools. Introducing IT Security Operations Current Challenges Faced By Firm While Implementing Secops Ppt Infographics to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Budget Tools, Pool Of Talent And Expertise, using this template. Grab it now to reap its full benefits.
-
 Current challenges faced by firm while implementing secops lack security operations integration
Current challenges faced by firm while implementing secops lack security operations integrationThis slide portrays information regarding the present challenges faced by firm while implementing SecOps system including budget constraint, absence of pool of talent and expertise and lack of essential tools. Introducing Current Challenges Faced By Firm While Implementing Secops Lack Security Operations Integration to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Budget, Pool Of Talent And Expertise, Essential Resources, using this template. Grab it now to reap its full benefits.
-
 Current challenges faced by firm while implementing secops tools security operations integration
Current challenges faced by firm while implementing secops tools security operations integrationThis slide portrays information regarding the present challenges faced by firm while implementing SecOps system including budget constraint, absence of pool of talent and expertise and lack of essential tools. Increase audience engagement and knowledge by dispensing information using Current Challenges Faced By Firm While Implementing Secops Tools Security Operations Integration. This template helps you present information on three stages. You can also present information on Essential Resources, Pool Of Talent And Expertise, Absence Of Comprehensive Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise security operations current challenges faced by firm while implementing secops ppt design
Enterprise security operations current challenges faced by firm while implementing secops ppt designThis slide portrays information regarding the present challenges faced by firm while implementing SecOps system including budget constraint, absence of pool of talent and expertise and lack of essential tools. Introducing Enterprise Security Operations Current Challenges Faced By Firm While Implementing Secops Ppt Design to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Budget Tools, Pool Of Talent And Expertise, using this template. Grab it now to reap its full benefits.
-
 Facilities rendered by security centre implementation key initiatives for project safety it
Facilities rendered by security centre implementation key initiatives for project safety itThis slide provides information regarding the various facilities that are offered by successful implementation of security center in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Increase audience engagement and knowledge by dispensing information using Enabling Data Security Risk Management Action Plan Key Initiatives For Project Safety It. This template helps you present information on four stages. You can also present information on Determine, Organization, Data, Security, Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 6 step process to implement data availability security
6 step process to implement data availability securityThis slide represents 6 step process to implement data availability security illustrating simplified recording, on-site maintenance and online security, training, record disposal and plan. Presenting our set of slides with 6 Step Process To Implement Data Availability Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Management, Implement, Organization.
-
 Cyber Security Transformation Strategy With Implementation
Cyber Security Transformation Strategy With ImplementationThe following slide highlights the cyber security transformation strategy with implementation illustrating benchmark, analysis, vision, roadmap, mobilization, and implementation which assists in transforming cyber security of organisation. Introducing our premium set of slides with name Cyber Security Transformation Strategy With Implementation. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Implementation, Mobilization, Vision, Analysis. So download instantly and tailor it with your information.
-
 Cloud Architecture And Security Multi Cloud It Environments After Implementing Solutions
Cloud Architecture And Security Multi Cloud It Environments After Implementing SolutionsThis slide covers the running all the workloads on a variety of clouds including public cloud, third party public clouds, hosted private clouds, and colocation servers while managing them. Increase audience engagement and knowledge by dispensing information using Cloud Architecture And Security Multi Cloud It Environments After Implementing Solutions. This template helps you present information on seven stages. You can also present information on Colocation, Hosted Private Cloud, Migration Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Business Security Program Implementation With Review
Business Security Program Implementation With ReviewThis slide covers business security program implementation with review which includes organizational facility security risk assessment with service vendors. Presenting our set of slides with name Business Security Program Implementation With Review. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Program Review, Security Option, Control Assessment.
-
 Impact Of Cyber Security Breach General Consequences Implementing Security Awareness Training
Impact Of Cyber Security Breach General Consequences Implementing Security Awareness TrainingThe purpose of this slide is to outline the impact of cyber security breach on the organization. The cyber attack make a significant impact on reputational damage, intellectual property IP theft, monetary penalty and operational disruption. Introducing Impact Of Cyber Security Breach General Consequences Implementing Security Awareness Training to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on V, using this template. Grab it now to reap its full benefits.
-
 Icon For Implementation Of Complete Digital Security Network
Icon For Implementation Of Complete Digital Security NetworkPresenting our set of slides with name Icon For Implementation Of Complete Digital Security Network. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Security Network.
-
 Implementation Process Of Network Infra Security
Implementation Process Of Network Infra SecurityThe following slide showcases process to implement network infra security to ensure that underlying infrastructure remains protected. It presents information related to segmentation networks, validation of hardware, etc. Introducing Implementation Process Of Network Infra Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Segmentation, Hardware, Software, using this template. Grab it now to reap its full benefits.
-
 Steps To Implement Cyber Security Automation In Secops
Steps To Implement Cyber Security Automation In SecopsThis slide outline the security operations automation process that enables to ease of the burden of cybersecurity organizations by automating repetitive tasks. It includes determine standard operating procedures SOPs , analyse tools, verify existing API connectors, etc. Presenting our set of slides with Steps To Implement Cyber Security Automation In Secops. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Analyse Tools, Progressive Automation, Enhance Processes.
-
 Best Practices For Cybersecurity Incident Management Development And Implementation Of Security
Best Practices For Cybersecurity Incident Management Development And Implementation Of SecurityThis slide represents the best practices to be adopted by the organizations which aim to minimize impact of cyber security incidents on business operations and prevent them from happening again. It includes best practices such as create cyber incident management plan etc. Increase audience engagement and knowledge by dispensing information using Best Practices For Cybersecurity Incident Management Development And Implementation Of Security. This template helps you present information on five stages. You can also present information on Create Cyber Incident, Management Plan, Establish Roles, Responsibilities Of Team Members using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementing Security System In Organization
Implementing Security System In OrganizationThis slide highlights implementing security system in organization process. This further includes business model, threat assessment, security policies, incident response, security controls and maintain security. Presenting our set of slides with Implementing Security System In Organization. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Maintain Security, Managed Security, Security Controls.
-
 SASE Network Security Secure Access Service Edge Implementation Steps
SASE Network Security Secure Access Service Edge Implementation StepsThis slide outlines the steps to implement a secure service edge in a business. The purpose of this slide is to demonstrate the various guidelines to consider while implementing the SASE model in an organization. The main steps include defining SASE goals and requirements, selecting the SD WAN backbone, incorporating zero trust solutions, etc. Introducing SASE Network Security Secure Access Service Edge Implementation Steps to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Requirements, Solutions, Service, using this template. Grab it now to reap its full benefits.
-
 Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process
Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management ProcessThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Increase audience engagement and knowledge by dispensing information using Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process. This template helps you present information on five stages. You can also present information on Malware Infection, Systems With Passwords, Employees Feels, Allow Official Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Global Cyber Security Trend Analysis Implementing Cyber Risk Management Process
Global Cyber Security Trend Analysis Implementing Cyber Risk Management ProcessThe following slide depicts the key statistics about cyber security trends to project future performance. It mainly includes elements such as increase in ransomware attacks, average data breach costs, approximate number of businesses prone to cyber-attacks etc. Introducing Global Cyber Security Trend Analysis Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Businesses Targeted, Ransomware Attack, Cyber Attacks, using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Major Impact Of Application Security On Business
Application Security Implementation Plan Major Impact Of Application Security On BusinessThis slide showcases the after application security impact on business along with factors that have improved the overall performance. Introducing Application Security Implementation Plan Major Impact Of Application Security On Business to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Threats Surge, Security Increase, Reduced Attacks On Applications, using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Process Phases For Effective Authentication Implementation
Application Security Implementation Plan Process Phases For Effective Authentication ImplementationThis slide showcases the steps for deploying effective authentication which include defining requirements, selecting authentication method, etc. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Process Phases For Effective Authentication Implementation. This template helps you present information on seven stages. You can also present information on Implement Login Mechanism, Choose Authentication Method, Secure Storage Of Credentials using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint Security Implementation Process Of Endpoint Security Solutions
Endpoint Security Implementation Process Of Endpoint Security SolutionsThis slide highlights the process stages of endpoint security which include information gathering, choosing security solutions, etc. Increase audience engagement and knowledge by dispensing information using Endpoint Security Implementation Process Of Endpoint Security Solutions. This template helps you present information on three stages. You can also present information on Gather Information, Deploy Selected Solutions, Select Security Solutions, Endpoint Security Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Six Steps For Implementing Visualization Security
Six Steps For Implementing Visualization SecurityThis slide showcases process of implementing visualization security. The main purpose of this template is to showcase various steps of data visualization in business. This includes data assessment, access control policies, train employees, etc. Introducing our premium set of slides with Six Steps For Implementing Visualization Security. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Regular Security, Train Employee, Data Encryption. So download instantly and tailor it with your information.
-
 Roadmap For Implementing Effective Web Security
Roadmap For Implementing Effective Web SecurityThis slide outlines the steps that an organization should take while conducting web security such as education, infrastructure security, etc. Presenting our set of slides with name Roadmap For Implementing Effective Web Security. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Monitoring, Application Security, Incident Response, Assessment And Planning.
-
 Key Considerations Before Implementing Cyber Security Mesh
Key Considerations Before Implementing Cyber Security MeshThe following slide emphasizes essential factors like connecting to VMs, developing tooling, observability, multi-cluster security, and mesh capabilities in pre-implementation considerations for cybersecurity mesh. This aids in preparing a robust strategy for successful cyber mesh integration. Presenting our set of slides with Key Considerations Before Implementing Cyber Security Mesh This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Deployment Tooling, Exposing Mesh Capabilities, Observability
-
 Implementing Security Gap Visualization In System
Implementing Security Gap Visualization In SystemThis slide showcases process of implementing visualization security. The main purpose of this template is to showcase various steps of data visualization in business. This includes data assessment, access control policies, train employees, etc. Presenting our set of slides with name Implementing Security Gap Visualization In System. This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Assessment, Select Secure Visualization Tools, Establish Access Control Policies, Regular Security Monitoring.
-
 Shift Left Testing Security Implementation Methods
Shift Left Testing Security Implementation MethodsThis slide showcases the tools for shift left testing.Its aim is to deploy and reinforce security code base and increase security.This slide includes static application system testing, dynamic application security.Presenting our set of slides with Shift Left Testing Security Implementation Methods This exhibits information on four stages of the process.This is an easy to edit and innovatively designed PowerPoint template.So download immediately and highlight information on Remediate Seamlessly, Immediate Remediation, Environment.
-
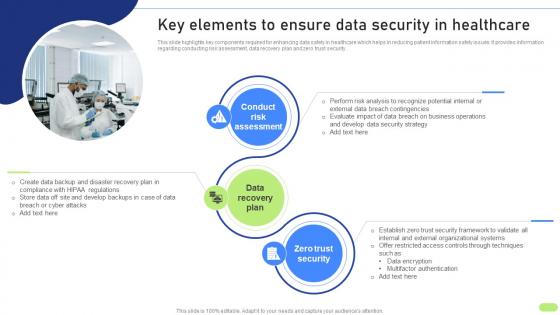 Key Elements To Ensure Data Security Definitive Guide To Implement Data Analytics SS
Key Elements To Ensure Data Security Definitive Guide To Implement Data Analytics SSThis slide highlights key components required for enhancing data safety in healthcare which helps in reducing patient information safety issues. It provides information regarding conducting risk assessment, data recovery plan and zero trust security. Introducing Key Elements To Ensure Data Security Definitive Guide To Implement Data Analytics SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Conduct Risk Assessment, Data Recovery Plan, Zero Trust Security, using this template. Grab it now to reap its full benefits.
-
 Adopting Homomorphic Encryption To Secure Cloud Computing Implementing Digital Transformation And Ai DT SS
Adopting Homomorphic Encryption To Secure Cloud Computing Implementing Digital Transformation And Ai DT SSThis slide provides glimpse about utilizing homomorphic encryption approach that can help businesses in privacy preservation. It includes stages such as encryption, computation, decryption, etc. Increase audience engagement and knowledge by dispensing information using Adopting Homomorphic Encryption To Secure Cloud Computing Implementing Digital Transformation And Ai DT SS. This template helps you present information on three stages. You can also present information on Privacy Preservation, Secure Cloud Computing, Model Owner using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Business Plan Implementation Roadmap Business Recovery Plan To Overcome Cyber Security Threat
Business Plan Implementation Roadmap Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about business cyber security attack recovery plan. It includes key steps such as setting time based recovery goals, impact and risk assessment, build recovery team, communication plan, recovery strategies implementation, etc. Introducing Business Plan Implementation Roadmap Business Recovery Plan To Overcome Cyber Security Threat to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Assessment, Communication Plan, Recovery Strategies Implementation, using this template. Grab it now to reap its full benefits.
-
 Business Benefits Of Implementing Web Security Solution
Business Benefits Of Implementing Web Security SolutionThis slide outlines the pros of web security in business which include safeguarding sensitive data, securing private information, etc. Introducing Business Benefits Of Implementing Web Security Solution to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Safeguard Sensitive Data, Secure Private Information, Prevent Costly Service Disruptions, using this template. Grab it now to reap its full benefits.
-
 Security Measures To Implement In Automated Messaging
Security Measures To Implement In Automated MessagingThe purpose of this slide is to outline security measures to be implemented in automated messaging systems such as opting for a reliable SMS provider, SMS verification, etc., for ensuring data protection, encryption, etc. Introducing our premium set of slides with Security Measures To Implement In Automated Messaging. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Reliable SMS Provider, SMS Verification, Otps Keywords. So download instantly and tailor it with your information.
-
 Gamification Implementation In Cyber Security Recruitment Best Practices
Gamification Implementation In Cyber Security Recruitment Best PracticesThe purpose of this slide is to ensure that gamified components are consistent with organizations culture and values and create fun and competitive atmosphere for applicants including best practices such as aligning gamification with company culture and values, promoting diversity and inclusion, etc. Introducing our premium set of slides with name Gamification Implementation In Cyber Security Recruitment Best Practices. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Design Meaningful Challenges, Make Process Enjoyable, Promote Diversity And Inclusion, Cyber Security Recruitment. So download instantly and tailor it with your information.
-
 Process To Implement Gamified Cyber Security Training
Process To Implement Gamified Cyber Security TrainingThe purpose of this slide is to create a gamified cybersecurity training program that captures attention of users also achieves specific, measurable improvements in cybersecurity awareness and skills including steps such as identifying learning objectives, structuring activities and challenges, etc. Introducing our premium set of slides with name Process To Implement Gamified Cyber Security Training. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Learning Objectives, Structure Activities And Challenges, Cyber Security Training. So download instantly and tailor it with your information.
-
 Potential Solutions To Prevent Ecommerce Fraud Implementing E Commerce Security Measures
Potential Solutions To Prevent Ecommerce Fraud Implementing E Commerce Security MeasuresThe slide highlights potential measures to mitigate ecommerce fraud. It include Authentication solution, Transaction monitoring, employee training and technology integration. Introducing Potential Solutions To Prevent Ecommerce Fraud Implementing E Commerce Security Measures to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Authentication Solution, Employee Training, Transaction Monitoring, Technology Integration, using this template. Grab it now to reap its full benefits.


