Powerpoint Templates and Google slides for Implementing Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Bi design and implementation security ppt powerpoint presentation picture
Bi design and implementation security ppt powerpoint presentation picturePresenting this set of slides with name BI Design And Implementation Security Ppt Powerpoint Presentation Picture. This is a four stage process. The stages in this process are Web Based, Architecture, Scalability, Security. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Business security implementation ppt powerpoint presentation pictures background cpb
Business security implementation ppt powerpoint presentation pictures background cpbPresenting this set of slides with name Business Security Implementation Ppt Powerpoint Presentation Pictures Background Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Business Security Implementation to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Implement enterprise security ppt powerpoint presentation outline format ideas cpb
Implement enterprise security ppt powerpoint presentation outline format ideas cpbPresenting this set of slides with name Implement Enterprise Security Ppt Powerpoint Presentation Outline Format Ideas Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Implement Enterprise Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Icons slide for e mail security industry overview and implementation report ppt powerpoint slides
Icons slide for e mail security industry overview and implementation report ppt powerpoint slidesPresenting this set of slides containing editable icons for topic Icons Slide For E Mail Security Industry Overview And Implementation Report Ppt Powerpoint Slides. All icons in this slide are 100 percent editable. You can replace icons in your deck with any of these icons. Download now and impress your audience.
-
 Network security implementation ppt powerpoint presentation icon deck cpb
Network security implementation ppt powerpoint presentation icon deck cpbPresenting this set of slides with name Network Security Implementation Ppt Powerpoint Presentation Icon Deck Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Network Security Implementation to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security operation center concepts implementation ppt powerpoint presentation pictures cpb
Security operation center concepts implementation ppt powerpoint presentation pictures cpbPresenting this set of slides with name Security Operation Center Concepts Implementation Ppt Powerpoint Presentation Pictures Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Security Operation Center Concepts Implementation to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security implementation ppt powerpoint presentation infographic template outfit cpb
Security implementation ppt powerpoint presentation infographic template outfit cpbPresenting this set of slides with name Security Implementation Ppt Powerpoint Presentation Infographic Template Outfit Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Security Implementation to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Steps for developing and implementing it security controls
Steps for developing and implementing it security controlsIntroducing our premium set of slides with Steps For Developing And Implementing IT Security Controls. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access, Eventuality, Training. So download instantly and tailor it with your information.
-
 Implement security system ppt powerpoint presentation gallery inspiration cpb
Implement security system ppt powerpoint presentation gallery inspiration cpbPresenting our Implement Security System Ppt Powerpoint Presentation Gallery Inspiration Cpbs PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Implement Security System This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Information security governance management implementation model
Information security governance management implementation modelPresenting our set of slides with name Information Security Governance Management Implementation Model. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Organizational Structure, Strategic Planning For Risk Mitigation, Security Management, Roles And Responsibilities.
-
 Enhanced security event management current challenges faced by firm while implementing secops ppt skills
Enhanced security event management current challenges faced by firm while implementing secops ppt skillsThis slide portrays information regarding the present challenges faced by firm while implementing SecOps system including budget constraint, absence of pool of talent and expertise and lack of essential tools. Introducing Enhanced Security Event Management Current Challenges Faced By Firm While Implementing Secops Ppt Skills to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Budget Tools, Pool Of Talent And Expertise, using this template. Grab it now to reap its full benefits.
-
 Enhanced security event management facilities offered by successful implementation ppt images
Enhanced security event management facilities offered by successful implementation ppt imagesThis slide portrays information regarding the various facilities that are offered by successful implementation of SecOps in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Introducing Enhanced Security Event Management Facilities Offered By Successful Implementation Ppt Images to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Malware Detection And Investigation, Phishing Detection And Prevention, Investigations By Hr, Risk Mitigation Of Left Employees, using this template. Grab it now to reap its full benefits.
-
 Cost estimation for strategy implementation overcome the it security
Cost estimation for strategy implementation overcome the it securityThe slide shows the estimation of major cost involved in the next four years 2021 to 2025 for implementing the strategies. The strategies are implementing Data Encryption, Increase Employee Awareness, Restricting Access to Physical Devices etc.Present the topic in a bit more detail with this Cost Estimation For Strategy Implementation Overcome The It Security. Use it as a tool for discussion and navigation on Market Research, Software Installation, Software Upgradation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementing Cyber Security Awareness Raising Cyber Security Awareness In Organizations
Implementing Cyber Security Awareness Raising Cyber Security Awareness In OrganizationsThe purpose of this slide is to delineate a comprehensive security awareness training program that can assist corporates to mitigate cyber attacks and reduce downtime. Information covered in this slide is related to training goals, major topics to cover and projected result. Introducing Implementing Cyber Security Awareness Raising Cyber Security Awareness In Organizations to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Training Objective, Topics To Cover, Expected Result, using this template. Grab it now to reap its full benefits.
-
 Implementation Process Of Network Infra Security
Implementation Process Of Network Infra SecurityThe following slide showcases process to implement network infra security to ensure that underlying infrastructure remains protected. It presents information related to segmentation networks, validation of hardware, etc. Introducing Implementation Process Of Network Infra Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Segmentation, Hardware, Software, using this template. Grab it now to reap its full benefits.
-
 Various Key Levels In Implementing Infrastructure Security
Various Key Levels In Implementing Infrastructure SecurityThe following slide showcases different levels of infra security which aims to boost safety measures and minimize downtime. It presents information related to physical, network, application and data level. Introducing Various Key Levels In Implementing Infrastructure Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Physical, Network, Application, using this template. Grab it now to reap its full benefits.
-
 Case Study On Security Improvement Through Secops Implementation
Case Study On Security Improvement Through Secops ImplementationThis slide exhibits a case study of the SecOps application in a pharmaceutical company. It includes information about the firm, challenges, solutions, and benefits to a business. Introducing our premium set of slides with Case Study On Security Improvement Through Secops Implementation. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Challenges, Solution, Benefit To Business. So download instantly and tailor it with your information.
-
 Steps To Implement Cyber Security Automation In Secops
Steps To Implement Cyber Security Automation In SecopsThis slide outline the security operations automation process that enables to ease of the burden of cybersecurity organizations by automating repetitive tasks. It includes determine standard operating procedures SOPs , analyse tools, verify existing API connectors, etc. Presenting our set of slides with Steps To Implement Cyber Security Automation In Secops. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Analyse Tools, Progressive Automation, Enhance Processes.
-
 Cyber Security Implementation Approach Conceptual Framework
Cyber Security Implementation Approach Conceptual FrameworkFollowing slide exhibits execution approach for cyber risk management. Purpose of this slide is to assure proper business information or data security. It includes pointers such as current state, evaluation, target state and roadmap. Introducing our premium set of slides with Cyber Security Implementation Approach Conceptual Framework. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Implementation, Approach, Conceptual. So download instantly and tailor it with your information.
-
 Cyber Security Attacks Response Plan Benefits Of Implementing Web Application Firewall
Cyber Security Attacks Response Plan Benefits Of Implementing Web Application FirewallThis slide represents the advantages of implementing a software which protects web applications from variety of application layer attacks. It includes key benefits of implementing web application firewall such as defense, fights vulnerabilities etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Benefits Of Implementing Web Application Firewall. Use it as a tool for discussion and navigation on Fights Vulnerabilities, Application Firewall, Confidential Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Parameters To Select Cyber Security Containment Strategy Development And Implementation Of Security
Key Parameters To Select Cyber Security Containment Strategy Development And Implementation Of SecurityThis slide represents the various parameters to look for before choosing an effective and efficient cyber security containment strategy. It includes key parameters such as higher potential damages and theft of organizational resources etc. Introducing Key Parameters To Select Cyber Security Containment Strategy Development And Implementation Of Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Organizational Resources, Potential Damages, Strategy, using this template. Grab it now to reap its full benefits.
-
 Strategies To Analyze Cyber Security Incidents Development And Implementation Of Security Incident Management
Strategies To Analyze Cyber Security Incidents Development And Implementation Of Security Incident ManagementThis slide represents the techniques to be used by the organizations to analyze the impact of cyber security incidents on business operations. It includes strategies for analyzing cyber incidents such as profile network and systems etc. Increase audience engagement and knowledge by dispensing information using Strategies To Analyze Cyber Security Incidents Development And Implementation Of Security Incident Management. This template helps you present information on two stages. You can also present information on Profile Network And Systems, Understand Normal Behaviors, Perform Event Correlation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Various Cyber Security Incidents Detected By It Department Development And Implementation Of Security
Various Cyber Security Incidents Detected By It Department Development And Implementation Of SecurityThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Increase audience engagement and knowledge by dispensing information using Various Cyber Security Incidents Detected By It Department Development And Implementation Of Security. This template helps you present information on five stages. You can also present information on Insider Threat, Phishing Attack, Malware Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ways To Detect Cyber Security Incidents Development And Implementation Of Security Incident Management
Ways To Detect Cyber Security Incidents Development And Implementation Of Security Incident ManagementThis slide represents the activities through which cyber incident management team can effectively and efficiently detect cyber security incidents. It includes various ways of detecting cyber security incidents such as unusual behavior from privileged user accounts etc. Introducing Ways To Detect Cyber Security Incidents Development And Implementation Of Security Incident Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Privileged User Accounts, Unusual Behavior, Network Traffic, using this template. Grab it now to reap its full benefits.
-
 Benefits Of Implementing Web Application Firewall Deploying Computer Security Incident
Benefits Of Implementing Web Application Firewall Deploying Computer Security IncidentThis slide represents the advantages of implementing a software which protects web applications from variety of application layer attacks. It includes key benefits of implementing web application firewall such as defense, fights vulnerabilities etc.Present the topic in a bit more detail with this Benefits Of Implementing Web Application Firewall Deploying Computer Security Incident. Use it as a tool for discussion and navigation on Provides Signature, Protects Against, Fights Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Development And Implementation Of Security Key Issues Faced By Organization Due To Cybersecurity Incidents
Development And Implementation Of Security Key Issues Faced By Organization Due To Cybersecurity IncidentsThis slide shows the challenges faced by enterprise due to increase in cyber attacks. It includes cyber security incidents experienced by the organization such as cloud computing issues, theft of sensitive information, ransomware attacks etc. Introducing Development And Implementation Of Security Key Issues Faced By Organization Due To Cybersecurity Incidents to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Privacy, Compliance, Security, using this template. Grab it now to reap its full benefits.
-
 Development And Implementation Of Security Key Lessons Learned By Organization From Cyber Security Incident
Development And Implementation Of Security Key Lessons Learned By Organization From Cyber Security IncidentThis slide represents the key takeaways for the cyber security incident management team after they effectively respond to and manage the cyber attacks experienced by the organization. It includes key lessons learned by organization such as ransomware is here to stay etc. Increase audience engagement and knowledge by dispensing information using Development And Implementation Of Security Key Lessons Learned By Organization From Cyber Security Incident. This template helps you present information on three stages. You can also present information on Active, Probably Stay, No Signs Reduction Ransomware Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Development And Implementation User Awareness Training Program To Prevent Cyber Security Incidents
Development And Implementation User Awareness Training Program To Prevent Cyber Security IncidentsThis slide represents the training program conducted by the incident management team for end users to help them identify and mitigate the cyber security incidents before they occur. It includes details related to training topic, method, date, trainer and budget. Deliver an outstanding presentation on the topic using this Development And Implementation User Awareness Training Program To Prevent Cyber Security Incidents. Dispense information and present a thorough explanation of Password Security, Cloud And Internet Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SS
Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SSThis slide represents best practices for effective endpoint security. It covers educating users, finding and tracking business owned devices, and installation maintenance of operating systems.Increase audience engagement and knowledge by dispensing information using Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SS. This template helps you present information on three stages. You can also present information on Such Business, Operating System, Frequent Basis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Access Security Control Models Implementation Of ICT Strategic Plan Strategy SS
Key Access Security Control Models Implementation Of ICT Strategic Plan Strategy SSThis slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role based access control and attributes based access control.Deliver an outstanding presentation on the topic using this Key Access Security Control Models Implementation Of ICT Strategic Plan Strategy SS. Dispense information and present a thorough explanation of Discretionary Access, Mandatory Access, Access Granted using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SDN Security IT Implementation Process Of Software Defined Networking SDN
SDN Security IT Implementation Process Of Software Defined Networking SDNThis slide outlines the implementation process of software defined networking that includes creating a use case, forming a multi functional team, testing, and reviewing. The main implementation types of SDN are open SDN, SDN via APIs, and SDN via hypervisor based overlay network. Increase audience engagement and knowledge by dispensing information using SDN Security IT Implementation Process Of Software Defined Networking SDN. This template helps you present information on four stages. You can also present information on Process, Implementation, Software using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SDN Security IT Roadmap For Software Defined Network Implementation
SDN Security IT Roadmap For Software Defined Network ImplementationThis slide outlines the roadmap for software defined network implementation, including the steps to be performed, such as defining the use case, creating a cross functional team, testing, and reviewing. Increase audience engagement and knowledge by dispensing information using SDN Security IT Roadmap For Software Defined Network Implementation. This template helps you present information on four stages. You can also present information on Roadmap, Software, Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
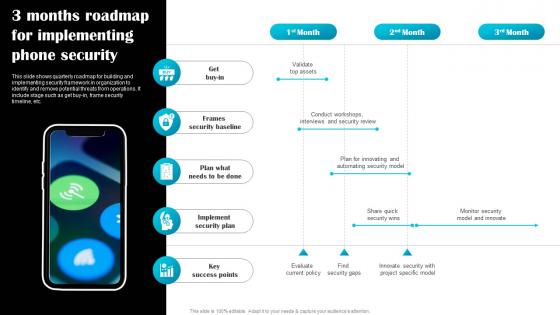 3 Months Roadmap For Implementing Phone Security
3 Months Roadmap For Implementing Phone SecurityThis slide shows quarterly roadmap for building and implementing security framework in organization to identify and remove potential threats from operations. It include stage such as get buy in, frame security timeline, etc. Presenting our set of slides with 3 Months Roadmap For Implementing Phone Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Frames Security Baseline, Implement Security Plan.
-
 Implement Automated Generating Security Awareness Among Employees To Reduce
Implement Automated Generating Security Awareness Among Employees To ReduceThe following slide showcases the automated patch management process to fix software vulnerabilities and ensure smooth functioning of systems. It includes activities such as scanning of systems, requesting to take back up etc. Deliver an outstanding presentation on the topic using this Implement Automated Generating Security Awareness Among Employees To Reduce Dispense information and present a thorough explanation of Vulnerability Assessment, Request Cancelled using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Principles Of Enterprise Blockchain Security Implementation
Principles Of Enterprise Blockchain Security ImplementationThis slide highlights principles for blockchain security implementation aimed at implementing technology to strengthen platform by aligning with current trends. It covers open source, permissioning, governance, security and standards. Introducing our premium set of slides with Principles Of Enterprise Blockchain Security Implementation. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Permissioning, Security, Open Source, Governance. So download instantly and tailor it with your information.
-
 Security Practices For Enterprise Blockchain Implementation
Security Practices For Enterprise Blockchain ImplementationThis slide presents security practices for blockchain implementation aimed at optimizing security and mitigation practices to improve cybersecurity technology. It covers permissioned blockchain, case analysis, create governance structure and file storage. Presenting our set of slides with Security Practices For Enterprise Blockchain Implementation. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Permissioned Blockchain, Create Governance Structure, Case Analysis, File Storage.
-
 Addressing Compliance Classes In IOT Security Internet Of Things IOT Implementation At Workplace
Addressing Compliance Classes In IOT Security Internet Of Things IOT Implementation At WorkplaceThis slide provides information regarding different compliance classes in IoT security framework catering different security objective. Present the topic in a bit more detail with this Addressing Compliance Classes In IOT Security Internet Of Things IOT Implementation At Workplace Use it as a tool for discussion and navigation on Confidentiality, Integrity, Availability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determine IOT Security Compliance Framework Internet Of Things IOT Implementation At Workplace
Determine IOT Security Compliance Framework Internet Of Things IOT Implementation At WorkplaceThis slide provides information regarding IoT security compliance framework addressing key security issues such as governance of management, security engineering, etc. Present the topic in a bit more detail with this Determine IOT Security Compliance Framework Internet Of Things IOT Implementation At Workplace. Use it as a tool for discussion and navigation on Governance Of Management, Security Engineering This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Analyzing Multiple Sales Tactics For Securing New Leads Implementation Guidelines For Sales MKT SS V
Analyzing Multiple Sales Tactics For Securing New Leads Implementation Guidelines For Sales MKT SS VThis slide provides glimpse about employing different techniques that can help the business in new lead generation. It includes techniques such as social media marketing, cold calling, email marketing, their impact, etc. Introducing Analyzing Multiple Sales Tactics For Securing New Leads Implementation Guidelines For Sales MKT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Multiple, Analyzing, Sales, using this template. Grab it now to reap its full benefits.
-
 Reasons To Implement Security In Organizational Communication Plan
Reasons To Implement Security In Organizational Communication PlanThis slide showcases reasons for securing organizational networks. This template focuses on encrypting communication to safeguard business, employees clients. It includes information related to advanced privacy, protecting cyber attacks, etc.Introducing our premium set of slides with Reasons To Implement Security In Organizational Communication Plan. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Improves Customer Confidence, Protects Intellectual Property, Builds Consumer. So download instantly and tailor it with your information.
-
 Implementation Of Cyber Security Risk Management Action Plan
Implementation Of Cyber Security Risk Management Action PlanThis slide represents implementation process of cyber security risk management action plan. It further includes steps such as evaluate cyber security risks, prioritize cyber risks Presenting our well structured Implementation Of Cyber Security Risk Management Action Plan. The topics discussed in this slide are Security, Management, Plan. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Advantages Of Blockchain Implementing Blockchain Security Solutions
Advantages Of Blockchain Implementing Blockchain Security SolutionsThis slide represents the various advantages of blockchain technology based on information security, digital freedom, privacy, and lower transaction fees.Introducing Advantages Of Blockchain Implementing Blockchain Security Solutions to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Immutable Information, Anonymity Privacy, No Intermediaries, using this template. Grab it now to reap its full benefits.
-
 Bitcoin Vs Blockchain Technology Implementing Blockchain Security Solutions
Bitcoin Vs Blockchain Technology Implementing Blockchain Security SolutionsThis slide defines the difference between bitcoin and blockchain technology based on goal, trade, scope, strategy and status.Increase audience engagement and knowledge by dispensing information using Bitcoin Vs Blockchain Technology Implementing Blockchain Security Solutions. This template helps you present information on five stages. You can also present information on Efficiently Government Restrictions, Numerical Sequence, Property Currency using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain Hashing Sha 256 Implementing Blockchain Security Solutions
Blockchain Hashing Sha 256 Implementing Blockchain Security SolutionsThis slide talks about the hashing SHA256 algorithm used in blockchain technology, including its properties. The purpose of this slide is to give an overview of hashing and its properties, such as collision resistance, deterministic, quick, and irreversible.Introducing Blockchain Hashing Sha 256 Implementing Blockchain Security Solutions to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Collision Resistance, Protecting Integrity, Completely Different, using this template. Grab it now to reap its full benefits.
-
 Checklist To Build Secure Blockchain Implementing Blockchain Security Solutions
Checklist To Build Secure Blockchain Implementing Blockchain Security SolutionsThis slide represents the best practices for businesses to develop secure blockchain solutions. The purpose of this slide is to showcase the different steps that should be considered for building secure blockchain solutions.Deliver an outstanding presentation on the topic using this Checklist To Build Secure Blockchain Implementing Blockchain Security Solutions. Dispense information and present a thorough explanation of Blockchain Penetration Testing, Protection Personal, Penetration Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyberattacks And Fraud Incidents Implementing Blockchain Security Solutions
Cyberattacks And Fraud Incidents Implementing Blockchain Security SolutionsThis slide outlines a few cyber attacks and fraud incidents that happened in the blockchain infrastructure. The purpose of this slide is to showcase the cyberattacks and fraud that occurred in the past, including code exploitation, stolen keys and employee computer hacking.Present the topic in a bit more detail with this Cyberattacks And Fraud Incidents Implementing Blockchain Security Solutions. Use it as a tool for discussion and navigation on Resulting In Substantial Financial, Bitcoins Belonging, Gain Unauthorized. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Disadvantages Of Blockchain Implementing Blockchain Security Solutions
Disadvantages Of Blockchain Implementing Blockchain Security SolutionsThis slide defines the various disadvantages of blockchain technology based on speed, energy, cost, scalability, maturity, and integration.Introducing Disadvantages Of Blockchain Implementing Blockchain Security Solutions to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Energy Consumption, Difficult Scale, Self Maintenance, using this template. Grab it now to reap its full benefits.
-
 How Blockchain Prevents Fraud And Implementing Blockchain Security Solutions
How Blockchain Prevents Fraud And Implementing Blockchain Security SolutionsThis slide describes the different methods used by blockchain technology to prevent data from fraud and stealing. The purpose of this slide is to showcase the various techniques and technologies used in blockchain technology to prevent fraud and data theft.Increase audience engagement and knowledge by dispensing information using How Blockchain Prevents Fraud And Implementing Blockchain Security Solutions. This template helps you present information on four stages. You can also present information on Extremely Difficult, Blockchain Incorporates, Techniques Such using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How Ddos Attack Works In Implementing Blockchain Security Solutions
How Ddos Attack Works In Implementing Blockchain Security SolutionsThis slide represents the overview of distributed denialofservice DDOS attacks in blockchain technology. This slide aims to showcase how distributed denialofservice DDOS works to exploit a blockchain network by generating multiple requests from a single source.Present the topic in a bit more detail with this How Ddos Attack Works In Implementing Blockchain Security Solutions. Use it as a tool for discussion and navigation on Network Resource Unavailable, Mitigation Strategies, Distinguishing Malicious. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 How Fraudsters Attack Implementing Blockchain Security Solutions
How Fraudsters Attack Implementing Blockchain Security SolutionsThis slide describes the primary attacks that hackers can use to exploit blockchain technology networks. The purpose of this slide is to showcase some basic threats that hackers can use to manipulate a blockchain network, such as phishing attacks, routing attacks, sybil, and 51 precent.Increase audience engagement and knowledge by dispensing information using How Fraudsters Attack Implementing Blockchain Security Solutions. This template helps you present information on four stages. You can also present information on Phishing Attacks, Routing Attacks, Sybil Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How Organizations Maintaining Implementing Blockchain Security Solutions
How Organizations Maintaining Implementing Blockchain Security SolutionsThis slide represents the various organizations that are taking security measures to prevent cyberattacks on blockchain network. The purpose of this slide is to highlight the various steps taken by US based organizations to prevent blockchain from cyber attacks and frauds.Deliver an outstanding presentation on the topic using this How Organizations Maintaining Implementing Blockchain Security Solutions. Dispense information and present a thorough explanation of Comprehensive Background, Healthcare Organizations, Credibility Influence using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Major Security Concerns For Implementing Blockchain Security Solutions
Major Security Concerns For Implementing Blockchain Security SolutionsThis slide outlines the critical security concerns related to blockchain networks. The purpose of this slide is to showcase the major risks associated with blockchain technology, including confidentiality, integrity, nonrepudiation, and authentication.Introducing Major Security Concerns For Implementing Blockchain Security Solutions to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Unauthorized, Safeguarding Sensitive, Prevent Unauthorized, using this template. Grab it now to reap its full benefits.
-
 Overview Of Sybil Attack In Implementing Blockchain Security Solutions
Overview Of Sybil Attack In Implementing Blockchain Security SolutionsThis slide gives an overview of the sybil attack in the blockchain network. The purpose of this slide is to showcase the use case of a sybil attack, also known as eclipse attack, and how the sybil attack works to manipulate a blockchain network.Deliver an outstanding presentation on the topic using this Overview Of Sybil Attack In Implementing Blockchain Security Solutions. Dispense information and present a thorough explanation of Hindering Communication, Potential Application, Fake Identities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Phases To Perform Blockchain Implementing Blockchain Security Solutions
Phases To Perform Blockchain Implementing Blockchain Security SolutionsThis slide highlights the main phases of blockchain penetration testing. The purpose of this slide is to showcase the different stages of penetration testing, including information gathering and threat modeling, testing and discovery, and exploitation.Increase audience engagement and knowledge by dispensing information using Phases To Perform Blockchain Implementing Blockchain Security Solutions. This template helps you present information on three stages. You can also present information on Information Gathering, Functionality Assess, Retrieving Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Preventive Measures Against Implementing Blockchain Security Solutions
Preventive Measures Against Implementing Blockchain Security SolutionsThis slide represents the steps to prevent distributed daniel of service attacks in blockchain technology. The purpose of this slide is to showcase the different security measures against ddos attacks, including implementing traffic filtering, employing load balancing, utilizing rate limiting and so on..Present the topic in a bit more detail with this Preventive Measures Against Implementing Blockchain Security Solutions. Use it as a tool for discussion and navigation on Collaborate Communicate, Decentralized Network, Implement Traffic Filtering. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Primary Security Attributes Of Implementing Blockchain Security Solutions
Primary Security Attributes Of Implementing Blockchain Security SolutionsThis slide outlines the main attributes of blockchain network security. The purpose of this slide is to highlight the security attributes of blockchain technology, including transaction integrity, tamper resistance, consistency, access to network and data, confidentiality of transactions, and so on.Deliver an outstanding presentation on the topic using this Primary Security Attributes Of Implementing Blockchain Security Solutions. Dispense information and present a thorough explanation of Transaction Integrity, Confidentiality Transactions, Resistance Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Blockchain Penetration Testing Implementing Blockchain Security Solutions
Blockchain Penetration Testing Implementing Blockchain Security SolutionsThis slide gives an overview of blockchain penetration testing and its primary goal. The purpose of this slide is to highlight the benefits of penetration testing in blockchain technology and its objectives, such as finding vulnerabilities, security loopholes, and misconfiguration errors within the solution.Present the topic in a bit more detail with this Blockchain Penetration Testing Implementing Blockchain Security Solutions. Use it as a tool for discussion and navigation on Deployment Procedure, Assessment Examine, Specialists Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risks Involved In Public Blockchain Implementing Blockchain Security Solutions
Risks Involved In Public Blockchain Implementing Blockchain Security SolutionsThis slide represents the challenges involved in public blockchains classified as basic risks, implementation risks, security risks, and legal risks.Introducing Risks Involved In Public Blockchain Implementing Blockchain Security Solutions to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Integrate Standards, Lack Standardization, Vendor Challenges, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Implementing Blockchain Security Solutions
Table Of Contents For Implementing Blockchain Security SolutionsPresent the topic in a bit more detail with this Table Of Contents For Implementing Blockchain Security Solutions. Use it as a tool for discussion and navigation on Risks Involved, Public Blockchain, Attack Blockchain Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Understanding 51 Precent Attack Implementing Blockchain Security Solutions
Understanding 51 Precent Attack Implementing Blockchain Security SolutionsThis slide outlines the overview of 51 precent attack in blockchain technology. The purpose of this slide is to showcase how malicious miners possess control over 51 precent of blockchain blocks, including a before and after use case.Deliver an outstanding presentation on the topic using this Understanding 51 Precent Attack Implementing Blockchain Security Solutions. Dispense information and present a thorough explanation of Chain Simultaneously, Attacker Controls, Mining Protocol using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.




