Powerpoint Templates and Google slides for Implement Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
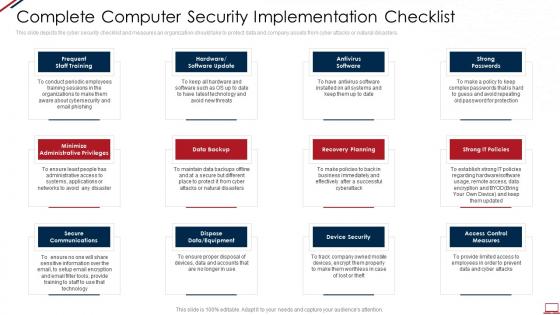 Computer system security complete computer security implementation checklist
Computer system security complete computer security implementation checklistThis slide depicts the cyber security checklist and measures an organization should take to protect data and company assets from cyber attacks or natural disasters. Increase audience engagement and knowledge by dispensing information using Computer System Security Complete Computer Security Implementation Checklist. This template helps you present information on twelve stages. You can also present information on Data Backup, Secure Communications, Recovery Planning, Strong Passwords, Device Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data security it complete data security implementation checklist
Data security it complete data security implementation checklistThis slide depicts the cyber security checklist and measures an organization should take to protect data and company assets from cyber attacks or natural disasters. Introducing Data Security IT Complete Data Security Implementation Checklist to increase your presentation threshold. Encompassed with twelve stages, this template is a great option to educate and entice your audience. Dispence information on Frequent Staff Training, Antivirus Software, Strong Passwords, Minimize Administrative Privileges, Data Backup, Recovery Planning, Strong IT Policies, Secure Communications, Device Security, using this template. Grab it now to reap its full benefits.
-
 Steps To Implement Cryptographic Cloud Security Cloud Cryptography
Steps To Implement Cryptographic Cloud Security Cloud CryptographyThe purpose of this slide is to outline the various steps to be followed while implementing cloud cryptography. These include identify and classify sensitive data, choose the appropriate cryptographic algorithm, use strong encryption keys, manage keys effectively, etc. Increase audience engagement and knowledge by dispensing information using Steps To Implement Cryptographic Cloud Security Cloud Cryptography. This template helps you present information on eight stages. You can also present information on Cryptographic, Appropriate, Implement Access Controls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
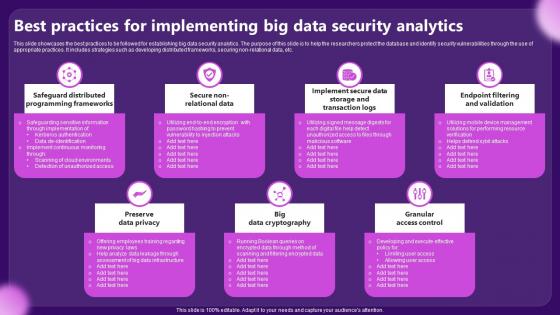 Best Practices For Implementing Big Data Security Analytics
Best Practices For Implementing Big Data Security AnalyticsThis slide showcases the best practices to be followed for establishing big data security analytics. The purpose of this slide is to help the researchers protect the database and identify security vulnerabilities through the use of appropriate practices. It includes strategies such as developing distributed frameworks, securing non relational data, etc. Presenting our set of slides with Best Practices For Implementing Big Data Security Analytics. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Preserve Data Privacy, Granular Access Control.
-
 Implementation Of Information Most Commonly Types Of Ict Securities Used By Strategy SS V
Implementation Of Information Most Commonly Types Of Ict Securities Used By Strategy SS VThis slide represents various types of information and communication technology ICT securities used by businesses. It covers network security, endpoint security, access security, and data encryption. Introducing Implementation Of Information Most Commonly Types Of Ict Securities Used By Strategy SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Network Security, Access Security, using this template. Grab it now to reap its full benefits.
-
 Timeline For Cloud Data Security Implementation Cloud Data Encryption
Timeline For Cloud Data Security Implementation Cloud Data EncryptionThis slide represents the timeline to implement cloud data encryption in an organization. The main components included are determine sensitive data and required encryption technique, choose a cloud service provider, implement encryption solution in cloud, etc. Introducing Timeline For Cloud Data Security Implementation Cloud Data Encryption to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Test Encryption Solutions, Implement Encryptions Solution, using this template. Grab it now to reap its full benefits.
-
 Sase Security Secure Edge Implementation Steps Ppt Show Design Inspiration
Sase Security Secure Edge Implementation Steps Ppt Show Design InspirationThis slide outlines the steps to implement a secure service edge in a business. The purpose of this slide is to demonstrate the various guidelines to consider while implementing the SASE model in an organization. The main steps include defining SASE goals and requirements, selecting the SD-WAN backbone, incorporating zero-trust solutions, etc. Introducing Sase Security Secure Edge Implementation Steps Ppt Show Design Inspiration to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Incorporate Zero Trust Solutions, Test Troubleshoot, Optimize SASE Setup, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Broker Implementation Models Secure Access Service Edge Sase
Cloud Security Broker Implementation Models Secure Access Service Edge SaseThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out-of-band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Increase audience engagement and knowledge by dispensing information using Cloud Security Broker Implementation Models Secure Access Service Edge Sase. This template helps you present information on three stages. You can also present information on Implementation, Applications, Inline Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Access Edge Implementation Steps Secure Access Service Edge Sase
Secure Access Edge Implementation Steps Secure Access Service Edge SaseThis slide outlines the steps to implement a secure service edge in a business. The purpose of this slide is to demonstrate the various guidelines to consider while implementing the SASE model in an organization. The main steps include defining SASE goals and requirements, selecting the SD-WAN backbone, incorporating zero-trust solutions, etc. Introducing Secure Access Edge Implementation Steps Secure Access Service Edge Sase to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Incorporate Zero Trust Solutions, Optimize SASE Setup, Service, using this template. Grab it now to reap its full benefits.
-
 Strategic Plan To Implement Most Commonly Types Of Ict Securities Used By Businesses Strategy SS V
Strategic Plan To Implement Most Commonly Types Of Ict Securities Used By Businesses Strategy SS VThis slide represents various types of information and communication technology ICT securities used by businesses. It covers network security, endpoint security, access security, and data encryption. Introducing Strategic Plan To Implement Most Commonly Types Of Ict Securities Used By Businesses Strategy SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on IT Governance, Visualization, Resource Management using this template. Grab it now to reap its full benefits.
-
 Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS V
Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Incident Management, Request Fulfillment using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker Implementation Models Cloud Security Model
Cloud Access Security Broker Implementation Models Cloud Security ModelThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out of band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Implementation Models Cloud Security Model. This template helps you present information on three stages. You can also present information on Scanning, Forward, Reverse using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Access Service Edge Implementation Steps Cloud Security Model
Secure Access Service Edge Implementation Steps Cloud Security ModelThis slide outlines the steps to implement a secure service edge in a business. The purpose of this slide is to demonstrate the various guidelines to consider while implementing the SASE model in an organization. The main steps include defining SASE goals and requirements, selecting the SD WAN backbone, incorporating zero trust solutions, etc. Introducing Secure Access Service Edge Implementation Steps Cloud Security Model to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Requirements, Solutions, Optimize, using this template. Grab it now to reap its full benefits.
-
 Implementation Roadmap For ERP Security Management
Implementation Roadmap For ERP Security ManagementThis slide showcases the implementation of roadmap security management in ERP. Its objective is to formulate a team and figure out the configuration level. This slide includes training, hardware evaluation, scenario training, protocol, etc. Presenting our set of slides with Implementation Roadmap For ERP Security Management. This exhibits information on Seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Resolution Protocol, Figure Out Configuration, Testing Scenario.
-
 Cloud Access Security Broker Implementation Models SASE Network Security
Cloud Access Security Broker Implementation Models SASE Network SecurityThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out of band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Introducing Cloud Access Security Broker Implementation Models SASE Network Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Scanning, Forward, Reverse, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure Enabling Devsecops Implementation Through Process
Devsecops Best Practices For Secure Enabling Devsecops Implementation Through ProcessThis slide explains the process involved in DevSecOps implementation. The purpose of his slide is to discuss the process involving automate dev. and production environments, automate software testing, automate software deployment, automate monitoring and alerting, and so on. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Enabling Devsecops Implementation Through Process. This template helps you present information on eight stages. You can also present information on Devsecops Implementation, Production Environments, Automate Software Testing, Automate Software Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Devsecops Best Practices For Secure Key Elements Of Successful Devsecops Implementation
Devsecops Best Practices For Secure Key Elements Of Successful Devsecops ImplementationThe slide discusses the critical elements for the successful implementation of DevSecOps. The purpose of this slide is to explain the various features that are integrated automated testing into a pipeline, automated deployment, infrastructure as code, etc. Introducing Devsecops Best Practices For Secure Key Elements Of Successful Devsecops Implementation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Infrastructure As Code, Integrate Security Testing Into Workflows, Automated Deployment, Devsecops Implementation, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure Roadmap For Devsecops Implementation Strategy
Devsecops Best Practices For Secure Roadmap For Devsecops Implementation StrategyThis slide highlights the project roadmap to implement the DevSecOps plan in an organization. The purpose of this slide is to showcase the different phases of the DevSecOps implementation plan, such as foundation and preparation, tool selection and integration, etc. Introducing Devsecops Best Practices For Secure Roadmap For Devsecops Implementation Strategy to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Tool Selection And Integration, Compliance And Governance, Foundation And Preparation, Security As Code, using this template. Grab it now to reap its full benefits.
-
 Sase Model Cloud Access Security Broker Implementation Models
Sase Model Cloud Access Security Broker Implementation ModelsThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out-of-band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Introducing Sase Model Cloud Access Security Broker Implementation Models to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Scanning, Forward Proxy, Reverse Proxy, using this template. Grab it now to reap its full benefits.
-
 Sase Model Secure Access Service Edge Implementation Steps
Sase Model Secure Access Service Edge Implementation StepsThis slide outlines the steps to implement a secure service edge in a business. The purpose of this slide is to demonstrate the various guidelines to consider while implementing the SASE model in an organization. The main steps include defining SASE goals and requirements, selecting the SD-WAN backbone, incorporating zero-trust solutions, etc. Increase audience engagement and knowledge by dispensing information using Sase Model Secure Access Service Edge Implementation Steps. This template helps you present information on five stages. You can also present information on Goals And Requirements, Incorporate Zero Trust Solutions, Test And Troubleshoot using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SD WAN Model Cloud Access Security Broker Implementation Models
SD WAN Model Cloud Access Security Broker Implementation ModelsThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out-of-band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Increase audience engagement and knowledge by dispensing information using SD WAN Model Cloud Access Security Broker Implementation Models. This template helps you present information on three stages. You can also present information on Cloud Access Security Broker, Api Scanning, Forward Proxy, Reverse Proxy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SD WAN Model Secure Access Service Edge Implementation Steps
SD WAN Model Secure Access Service Edge Implementation StepsThis slide outlines the steps to implement a secure service edge in a business. The purpose of this slide is to demonstrate the various guidelines to consider while implementing the SASE model in an organization. The main steps include defining SASE goals and requirements, selecting the SD-WAN backbone, incorporating zero-trust solutions, etc. Increase audience engagement and knowledge by dispensing information using SD WAN Model Secure Access Service Edge Implementation Steps. This template helps you present information on five stages. You can also present information on Incorporate Zero Trust Solutions, Test And Troubleshoot, Secure Access Service Edge, Infrastructure Gaps using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Practices To Maintain Digital Wallet Security Implementation Of Cashless Payment
Best Practices To Maintain Digital Wallet Security Implementation Of Cashless PaymentMentioned slide exhibits various best practices which can be implemented by followed by businesses to secure e wallets. It includes best practices such as enable passwords, secure network connections, install reliable applications, secure login credentials, and keep personal data private.Increase audience engagement and knowledge by dispensing information using Best Practices To Maintain Digital Wallet Security Implementation Of Cashless Payment This template helps you present information on five stages. You can also present information on Responsible Managers, Segregate Duties, Bank Statements using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security Threats
Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti virus, preventing to open suspicious emails, keeping systems up to date etc. Introducing Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Leverage Firewalls, Prevent Opening Suspicious Emails using this template. Grab it now to reap its full benefits.
-
 Global Cyber Security Trend Analysis Implementing Strategies To Mitigate Cyber Security Threats
Global Cyber Security Trend Analysis Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the key statistics about cyber security trends to project future performance. It mainly includes elements such as increase in ransomware attacks, average data breach costs, approximate number of businesses prone to cyber attacks etc. Increase audience engagement and knowledge by dispensing information using Global Cyber Security Trend Analysis Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on six stages. You can also present information on Attack, Data Breaches, Cyber Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security Threats
Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates some practices to ensure strong password management and restrict access to data. It includes activities such as avoiding weak passwords, encryption, multi factor authentication, conducting test etc. Introducing Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Conduct Password Test, Password Encryption, Multi Factor Authentication using this template. Grab it now to reap its full benefits.
-
 Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security Threats
Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the various types of cyber attacks faced by staff to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service tec. Introducing Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Ransomware, Phishing using this template. Grab it now to reap its full benefits.
-
 Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness Among
Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness AmongThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Introducing Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness Among to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Email Attachments, Systems, Employees using this template. Grab it now to reap its full benefits.
-
 Best Practices Of QR Code Implementation Enhancing Transaction Security With E Payment
Best Practices Of QR Code Implementation Enhancing Transaction Security With E PaymentMentioned slide provides information about best practices which can be implemented by businesses to increase sales. It includes best practices such as Include call to action, personalize QR code, check code scannability, update content regularly. Introducing Best Practices Of QR Code Implementation Enhancing Transaction Security With E Payment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Include Call To Action, Personalize QR Code, Check Code Scannability using this template. Grab it now to reap its full benefits.
-
 Best Practices For Implementing Mobile Security
Best Practices For Implementing Mobile SecurityThis slide talks about the best practices for an organization to practice mobile security device which includes minimizing public wi-fi usage, public Wi-Fi, etc. Introducing our premium set of slides with name Best Practices For Implementing Mobile Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ensuring Robust Password Protection, Security Training And Education, Enforcing Transparent Policies. So download instantly and tailor it with your information.
-
 Security Methods For Implementing Email Encryption
Security Methods For Implementing Email EncryptionThis slide outlines the security methods for implementing email encryption which includes encrypted PDFs secure attachments, web portal encryption, etc. Introducing our premium set of slides with Security Methods For Implementing Email Encryption. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Secure Attachments, Web Portal, Gateway Software. So download instantly and tailor it with your information.
-
 Best Practices For Implementing Application Security
Best Practices For Implementing Application SecurityThis slide discusses the best approaches for application security deployment which include assess threats, shift security left, control rights, etc. Increase audience engagement and knowledge by dispensing information using Best Practices For Implementing Application Security. This template helps you present information on five stages. You can also present information on Shift Security Left, Track Application Security Outcomes, Assess Threats, Application Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Timeline For Implementing Efficient Application Security
Timeline For Implementing Efficient Application SecurityThis slide outlines the different steps performed while deploying application security, including planning phase, requirement gathering, etc. Introducing Timeline For Implementing Efficient Application Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Patch Management, Incident Response Planning, Planning Phase, Education And Training, using this template. Grab it now to reap its full benefits.
-
 Implementing Effective Tokenization Steps To Implement Security Tokenization Strategy
Implementing Effective Tokenization Steps To Implement Security Tokenization StrategyThis slide represents the different phases of deploying security tokenization which include identifying sensitive data, implementing tokenization, etc. Increase audience engagement and knowledge by dispensing information using Implementing Effective Tokenization Steps To Implement Security Tokenization Strategy. This template helps you present information on seven stages. You can also present information on Implement Security Tokenization, Identify Sensitive Data, Secure Storage Of Tokens using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategies For Implementing AI Powered Global Technology In Cyber Security
Strategies For Implementing AI Powered Global Technology In Cyber SecurityThis slide shows strategic approaches for implementing AI in cyber security. The purpose of this slide is to strengthen organizations defence against potential cyber attacks to maximize effectiveness of global technological solutions. It covers strategies such as resource allocation, training data, internal processes, etc. Presenting our set of slides with Strategies For Implementing AI Powered Global Technology In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Resource Allocation, Training Data, Internal Processes.
-
 Application Security Implementation Plan Authorization Deployment Steps For Application Security
Application Security Implementation Plan Authorization Deployment Steps For Application SecurityThis slide discusses the process phases for implementing effective authorization which include assessment, planning, defining access control policies, etc. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Authorization Deployment Steps For Application Security. This template helps you present information on seven stages. You can also present information on Technology Selection, Assessment And Planning, Training And Awareness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Application Security Implementation Plan Implementing Effective Security Testing In Organization
Application Security Implementation Plan Implementing Effective Security Testing In OrganizationThis slide showcases the deployment process of security testing parallel to Software Development Testing Lifecycle SDLC stages. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Implementing Effective Security Testing In Organization. This template helps you present information on seven stages. You can also present information on System Testing, Implementation System Testing, Integration Testing, Requirement using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Application Security Implementation Plan Performance Gap Analysis For Implementing Application Security
Application Security Implementation Plan Performance Gap Analysis For Implementing Application SecurityThe purpose of this slide is to indicate the performance analysis of the organizations current security infrastructure. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Performance Gap Analysis For Implementing Application Security. This template helps you present information on four stages. You can also present information on Proper Functioning, Implement Robust Encryption Protocols, Lack Of Ideal Security Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Application Security Implementation Plan Process Of Implementing Cloud Native Application Security
Application Security Implementation Plan Process Of Implementing Cloud Native Application SecurityThis slide highlights the steps for deploying cloud-native application security which include understanding principles, risk assessment, etc. Introducing Application Security Implementation Plan Process Of Implementing Cloud Native Application Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Risk Assessment, Continuous Monitoring, Container Security, Implement Strong Access Controls, using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Steps For Deploying Application Security Testing
Application Security Implementation Plan Steps For Deploying Application Security TestingThis slide showcases the steps for deploying effective application security testing which include establishing test case, including security exam, etc. Introducing Application Security Implementation Plan Steps For Deploying Application Security Testing to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Execute Security Exam, Examine Outcomes, Include Security Exam, Stablish Working Test Case, using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Steps For Effective Encryption Method Deployment
Application Security Implementation Plan Steps For Effective Encryption Method DeploymentThis slide highlights the steps for deploying effective encryption which include selecting appropriate algorithm, choosing correct key size, etc. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Steps For Effective Encryption Method Deployment. This template helps you present information on six stages. You can also present information on Select Appropriate Algorithm, Select Appropriate Program, Maintain Key Security, Encryption Method Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Application Security Implementation Plan Steps To Deploy Efficient Access Control
Application Security Implementation Plan Steps To Deploy Efficient Access ControlThis slide discusses the process phases of implementing access control which include taking inventory of systems, examining staffs, etc. Introducing Application Security Implementation Plan Steps To Deploy Efficient Access Control to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Establish Roles, Resist Sporadic Adjustments, Examine The Staff, Take Inventory Of Systems, using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Timeline For Deploying Efficient Application Security
Application Security Implementation Plan Timeline For Deploying Efficient Application SecurityThis slide outlines the different steps performed while deploying application security, including planning phase, requirement gathering, etc. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Timeline For Deploying Efficient Application Security. This template helps you present information on six stages. You can also present information on Education And Training, Patch Management, Incident Response Planning, Establish Security Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Application Security Implementation Plan Working Process Of Effective Logging Implementation
Application Security Implementation Plan Working Process Of Effective Logging ImplementationThis slide outlines the steps for deploying effective logging which include assess requirements, select logging tool, defining logging standards, etc. Introducing Application Security Implementation Plan Working Process Of Effective Logging Implementation to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Ensure Security, Centralize Log Management, Define Logging Standards, Select Logging Tools, using this template. Grab it now to reap its full benefits.
-
 Endpoint Security Approaches To Implement Effective Endpoint Security
Endpoint Security Approaches To Implement Effective Endpoint SecurityThis slide showcases the techniques of deploying effective endpoint security which include on-location, cloud, hybrid endpoint security, etc. Introducing Endpoint Security Approaches To Implement Effective Endpoint Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Agent Based Security, Remote Device Connection, Effective Endpoint Security, using this template. Grab it now to reap its full benefits.
-
 Endpoint Security Timeline For Implementing Efficient Endpoint Security
Endpoint Security Timeline For Implementing Efficient Endpoint SecurityThis slide outlines the different steps performed while deploying endpoint security, including planning phase, solution selection, etc. Introducing Endpoint Security Timeline For Implementing Efficient Endpoint Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Testing And Optimization, Solution Selection, Deployment, Endpoint Security, using this template. Grab it now to reap its full benefits.
-
 Best Practices For Web Security Implementation
Best Practices For Web Security ImplementationThe purpose of this slide is to highlight the best practices for web security such as inclusive security practices, cybersecurity adoption, etc. Introducing our premium set of slides with name Best Practices For Web Security Implementation. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cybersecurity Framework Adoption, Automation Of Security Tools, Diverse Security Measures, Web Security Implementation. So download instantly and tailor it with your information.
-
 Internet Gateway Security IT Swg Implementation Methodology Span Switched
Internet Gateway Security IT Swg Implementation Methodology Span SwitchedThis slide talks about the SPAN scenario of Secure Web Gateway implementation. The purpose of this slide is to demonstrate the concept of SPAN SWG deployment technique with the help of a diagram. This slide also outlines the benefits of this method. Introducing Internet Gateway Security IT Swg Implementation Methodology Span Switched to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Internet Gateway Rules, Deployment, Monitoring, Transparent Modes, using this template. Grab it now to reap its full benefits.
-
 Implementation Steps Of Physical Security In Company
Implementation Steps Of Physical Security In CompanyThis slide showcases process of physical security that includes conducting risk assessment, reviewing operations, obtaining approval, implementing policies and following best practices. Presenting our set of slides with Implementation Steps Of Physical Security In Company. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Conduct Risk Assessment, Review Operations, Obtain Approval.
-
 Roadmap To Implement Robust OT Cyber Security
Roadmap To Implement Robust OT Cyber SecurityThis slide represents roadmap that guides companies to implement strong operational technology cybersecurity model for enhancing information protection. It includes various steps such as conducting OT threat assessment, know network and assets, etc. Presenting our set of slides with Roadmap To Implement Robust OT Cyber Security This exhibits information on Seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Conduct OT Threat Assessment, Know Network And Assets, Publish OT Security Policy
-
 Key Parameters Of IAM Implementation Process Securing Systems With Identity
Key Parameters Of IAM Implementation Process Securing Systems With IdentityThis slide highlights the key function of the Identity and Access Management implementation process. The purpose of this slide is to explain the various parameters of IAM implementation these include identity lifecycle management, access control, authentication, and so on. Introducing Key Parameters Of IAM Implementation Process Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Authorization, Identity Governance using this template. Grab it now to reap its full benefits.
-
 Roadmap For Identity And Access Management Implementation Securing Systems With Identity
Roadmap For Identity And Access Management Implementation Securing Systems With IdentityThis slide highlights the project roadmap to implement the Identity and Access Management process. The purpose of this slide is to showcase the different phases of the IAM implementation plan, such as implementing emerging IAM technologies, BYOI adoption, etc. Increase audience engagement and knowledge by dispensing information using Roadmap For Identity And Access Management Implementation Securing Systems With Identity This template helps you present information on Four stages. You can also present information on Iam Technologies, Byoi Adoption, Testing And Security Assurance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps To Implement Digital Authentication With IAM Securing Systems With Identity
Steps To Implement Digital Authentication With IAM Securing Systems With IdentityThis slide discusses the IAM implementing digital authentication. The purpose of this slide is to highlight the various types of digital authentication done by IAM, which are unique passwords, pre-shared keys, Behavioral authentication, and biometrics. Increase audience engagement and knowledge by dispensing information using Steps To Implement Digital Authentication With IAM Securing Systems With Identity This template helps you present information on Five stages. You can also present information on Unique Passwords, Biometrics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps To Implement Identity And Access Management Securing Systems With Identity
Steps To Implement Identity And Access Management Securing Systems With IdentityThis slide discusses the Identity and Access Management implementing program. The purpose of this slide is to highlight the implementation process of IAM, including scope identification, evaluating the right IAM approach, finding the best solution, and so on. Increase audience engagement and knowledge by dispensing information using Steps To Implement Identity And Access Management Securing Systems With Identity This template helps you present information on Six stages. You can also present information on Scope Identification, Define A Strategy, Assess Cost Factors using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Timeline To Implement Identity And Access Management Plan Securing Systems With Identity
Timeline To Implement Identity And Access Management Plan Securing Systems With IdentityThis slide shows the timeline for implementing the Identity and Access Management plan. The key steps include defining the project objective, identifying key stakeholders, determining compliance, integrating IAM with the existing system, etc. Introducing Timeline To Implement Identity And Access Management Plan Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Applications And Data, Public Cloud Platforms using this template. Grab it now to reap its full benefits.
-
 Budget Allocation For Mobile Security Implementation Mobile Security
Budget Allocation For Mobile Security Implementation Mobile SecurityThis slide represents the estimated and actual cost of implementing mobile security in an organization based on categories like training and security update. Increase audience engagement and knowledge by dispensing information using Budget Allocation For Mobile Security Implementation Mobile Security This template helps you present information on Three stages. You can also present information on Data Exposure Risks, Encryption Vulnerabilities, Authorization Weaknesses using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Web Security Upgradation Project Summary For Implementing Web Security
Web Security Upgradation Project Summary For Implementing Web SecurityThe purpose of this slide is to represent the summary of the web security project providing information regarding problems faced, recommended solution, etc. Introducing Web Security Upgradation Project Summary For Implementing Web Security to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Problems, Solutions, Estimated Cost, Estimated Timeline, using this template. Grab it now to reap its full benefits.
-
 Roles And Responsibilities Fraud Prevention Team Implementing E Commerce Security Measures
Roles And Responsibilities Fraud Prevention Team Implementing E Commerce Security MeasuresThe slide outlines roles and responsibilities for ecommerce fraud detection team. It includes details about chief information security officer, security operations manger, incident response manager, and risk compliance manager.Increase audience engagement and knowledge by dispensing information using Roles And Responsibilities Fraud Prevention Team Implementing E Commerce Security Measures. This template helps you present information on five stages. You can also present information on Security Operations Manager, Incident Response Manager, Security Architecture Manager using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security Measures
Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security MeasuresThe slide depicts secure sockets layer SSL process to encrypt sensitive information between a webs browser and server. It include client web browser, websiteserver, SSL certificate etc. Introducing Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security Measures to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Client Check Certificate, Impact, Delivers Encrypted Content, using this template. Grab it now to reap its full benefits.
-
 Steps To Train Employees For Fraud Prevention Implementing E Commerce Security Measures
Steps To Train Employees For Fraud Prevention Implementing E Commerce Security MeasuresThe slide portrays a stepwise process to train employees for fraud prevention. Key steps include identification, education, proactive measures, regular updates and evaluation. Introducing Steps To Train Employees For Fraud Prevention Implementing E Commerce Security Measures to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Proactive Measures, Evaluate Performance, Update Employees, Identify Fraud Risk, using this template. Grab it now to reap its full benefits.



