Powerpoint Templates and Google slides for Implement Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Security information event management implementation ppt powerpoint formats cpb
Security information event management implementation ppt powerpoint formats cpbPresenting this set of slides with name Security Information Event Management Implementation Ppt Powerpoint Formats Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Security Information Event Management Implementation to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Implementing security ppt powerpoint presentation show graphic tips cpb
Implementing security ppt powerpoint presentation show graphic tips cpbPresenting this set of slides with name Implementing Security Ppt Powerpoint Presentation Show Graphic Tips Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Implementing Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Network security implementation ppt powerpoint presentation icon deck cpb
Network security implementation ppt powerpoint presentation icon deck cpbPresenting this set of slides with name Network Security Implementation Ppt Powerpoint Presentation Icon Deck Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Network Security Implementation to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security operation center concepts implementation ppt powerpoint presentation pictures cpb
Security operation center concepts implementation ppt powerpoint presentation pictures cpbPresenting this set of slides with name Security Operation Center Concepts Implementation Ppt Powerpoint Presentation Pictures Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Security Operation Center Concepts Implementation to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Implement security ppt powerpoint presentation file design ideas cpb
Implement security ppt powerpoint presentation file design ideas cpbPresenting Implement Security Ppt Powerpoint Presentation File Design Ideas Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase two stages that will help you succinctly convey the information. In addition, you can alternate the colour, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Implement Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Enhanced security event management determine focus areas to implement security operations centre ppt tips
Enhanced security event management determine focus areas to implement security operations centre ppt tipsThis slide portrays information regarding the focus areas that are need to be addressed for effective implementation of security operations center. The focus areas are such as digital forensics and control, risk monitoring and management, etc. Introducing Enhanced Security Event Management Determine Focus Areas To Implement Security Operations Centre Ppt Tips to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Digital Forensics And Control, Risk Monitoring And Management, System And Network Administration, using this template. Grab it now to reap its full benefits.
-
 Agenda implementing security management plan reduce threats protect sensitive company data
Agenda implementing security management plan reduce threats protect sensitive company dataIncrease audience engagement and knowledge by dispensing information using Agenda Implementing Security Management Plan Reduce Threats Protect Sensitive Company Data. This template helps you present information on six stages. You can also present information on Management, Security, Plan, Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementing security management plan security access control ppt styles topics
Implementing security management plan security access control ppt styles topicsThis slide provides information about the sixth step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e., Remote Access Control. Introducing Implementing Security Management Plan Security Access Control Ppt Styles Topics to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Control Security, Private Network, Implementation, using this template. Grab it now to reap its full benefits.
-
 Security plan assets implementing security management plan ppt visual aids outline
Security plan assets implementing security management plan ppt visual aids outlineThis slide provides information about the second step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e., Evaluating Information Processing Assets. Increase audience engagement and knowledge by dispensing information using Security Plan Assets Implementing Security Management Plan Ppt Visual Aids Outline. This template helps you present information on three stages. You can also present information on Information, Processing, Conducted using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Complete electronic information security implementation checklist
Complete electronic information security implementation checklistThis slide depicts the cyber security checklist and measures an organization should take to protect data and company assets from cyber attacks or natural disasters. Increase audience engagement and knowledge by dispensing information using Complete Electronic Information Security Implementation Checklist. This template helps you present information on nine stages. You can also present information on Frequent Staff Training, Antivirus Software, Strong Passwords, Recovery Planning, Strong IT Policies, Device Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Building organizational security strategy plan facilities offered by implementation of security centre
Building organizational security strategy plan facilities offered by implementation of security centreThis slide portrays information regarding the various facilities that are offered by successful implementation of security center in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Introducing Building Organizational Security Strategy Plan Facilities Offered By Implementation Of Security Centre to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Implementation, Investigation, Prevention, using this template. Grab it now to reap its full benefits.
-
 Network Security Complete Network Security Implementation Checklist
Network Security Complete Network Security Implementation ChecklistThis slide depicts the network security checklist and measures an organization should take to protect data and company assets from network attacks or natural disasters. Introducing Network Security Complete Network Security Implementation Checklist to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Complete Network Security Implementation Checklist, using this template. Grab it now to reap its full benefits.
-
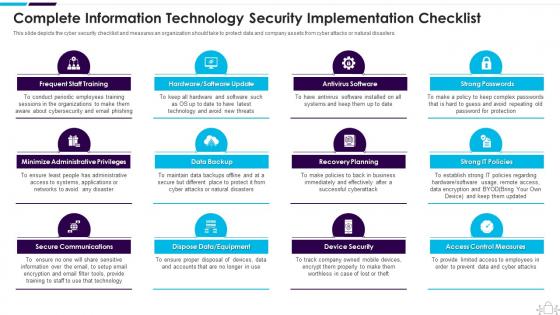 Information Technology Security Complete Information Security Implementation Checklist
Information Technology Security Complete Information Security Implementation ChecklistThis slide depicts the cyber security checklist and measures an organization should take to protect data and company assets from cyber attacks or natural disasters. Introducing Information Technology Security Complete Information Security Implementation Checklist to increase your presentation threshold. Encompassed with twelve stages, this template is a great option to educate and entice your audience. Dispence information on Frequent Staff Training, Administrative Privileges, Data Backup, using this template. Grab it now to reap its full benefits.
-
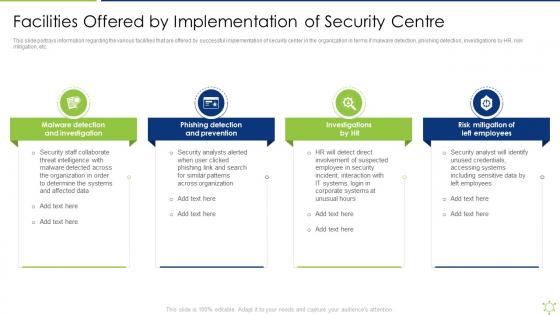 Facilities Offered By Implementation Of Security Centre Enabling It Intelligence Framework
Facilities Offered By Implementation Of Security Centre Enabling It Intelligence FrameworkThis slide portrays information regarding the various facilities that are offered by successful implementation of security center in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc.Introducing Facilities Offered By Implementation Of Security Centre Enabling It Intelligence Framework to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Detection And Prevention, Risk Mitigation Of Left Employees, Malware Detection using this template. Grab it now to reap its full benefits.
-
 Checklist To Implement Cloud Security In Business Cloud Data Protection
Checklist To Implement Cloud Security In Business Cloud Data ProtectionThis slide shows the checklist to implement cloud security in business, including policies and procedures, access control, networking, backup data, security patches, etc. Introducing Checklist To Implement Cloud Security In Business Cloud Data Protection to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispense information on Logging And Monitoring, Networking, Data Encryption, using this template. Grab it now to reap its full benefits.
-
 Keyways To Secure Cloud Infrastructure Strategies To Implement Cloud Computing Infrastructure
Keyways To Secure Cloud Infrastructure Strategies To Implement Cloud Computing InfrastructureMentioned slide provides keyways to secure cloud infrastructure from security threats. It covers encryption services, security design, internet of things and internal security. Introducing Keyways To Secure Cloud Infrastructure Strategies To Implement Cloud Computing Infrastructure to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Encryption Services, Internal Security, Security Design, using this template. Grab it now to reap its full benefits.
-
 Key Benefits Of Cyber Security Awareness Training Implementing Security Awareness Training
Key Benefits Of Cyber Security Awareness Training Implementing Security Awareness TrainingThe purpose of this slide is to delineate several advantages of security awareness training. Driving awareness, reducing data breach threat, prevention of downtime and improving the customer confidence are some of the key benefits which are highlighted in the slide. Introducing Key Benefits Of Cyber Security Awareness Training Implementing Security Awareness Training to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Drive Awareness, Reduce Threat, Improves Customer Confidence, using this template. Grab it now to reap its full benefits.
-
 Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness Training
Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness TrainingThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT based attacks, malware, social engineering attack and business email compromise. Introducing Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness Training to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Password Attack, Cryptojacking, Malware, using this template. Grab it now to reap its full benefits.
-
 Impact Of E Security System Implementation In Organizations
Impact Of E Security System Implementation In OrganizationsThis slide mentions the impact of implementing e-security systems in organizations. The effects include Asset Protection, Security Updates, Conflict Resolution and Automation and Analytics. Presenting our set of slides with name Impact Of E Security System Implementation In Organizations. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Organizations, Automation.
-
 Cyber Security Implementation Approach Conceptual Framework
Cyber Security Implementation Approach Conceptual FrameworkFollowing slide exhibits execution approach for cyber risk management. Purpose of this slide is to assure proper business information or data security. It includes pointers such as current state, evaluation, target state and roadmap. Introducing our premium set of slides with Cyber Security Implementation Approach Conceptual Framework. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Implementation, Approach, Conceptual. So download instantly and tailor it with your information.
-
 Security Architecture Review Of A Cloud Implementation Plan For The Organization
Security Architecture Review Of A Cloud Implementation Plan For The OrganizationThis slide covers the guidelines for creating an actionable implementation plan for the organization with the help of your learnings. Increase audience engagement and knowledge by dispensing information using Security Architecture Review Of A Cloud Implementation Plan For The Organization. This template helps you present information on four stages. You can also present information on Implementation Plan, Analysis Process, Infrastructure Is Progressing, Company Develops using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Facilities Offered By Implementation Of Security Centre Strategic Organizational Security Plan
Facilities Offered By Implementation Of Security Centre Strategic Organizational Security PlanThis slide portrays information regarding the various facilities that are offered by successful implementation of security center in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Introducing Facilities Offered By Implementation Of Security Centre Strategic Organizational Security Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Investigations By Hr, Employees, Phishing Detection, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Incident Response Lifecycle Development And Implementation Of Security Incident Management
Cyber Security Incident Response Lifecycle Development And Implementation Of Security Incident ManagementThis slide represents the lifecycle of incident response which enables organizations to quickly detect and halt attacks, minimize damage and prevent future attacks of same type. It includes four phases of cyber security incident response such as preparation, detection and analysis etc. Introducing Cyber Security Incident Response Lifecycle Development And Implementation Of Security Incident Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Preparation, Detection Analysis, Containment Eradication Recovery, using this template. Grab it now to reap its full benefits.
-
 Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security Incident
Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security IncidentThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc. Introducing Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security Incident to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Assess And Design, Detect And Report, Plan And Prepare, using this template. Grab it now to reap its full benefits.
-
 Ways To Detect Cyber Security Incidents Development And Implementation Of Security Incident Management
Ways To Detect Cyber Security Incidents Development And Implementation Of Security Incident ManagementThis slide represents the activities through which cyber incident management team can effectively and efficiently detect cyber security incidents. It includes various ways of detecting cyber security incidents such as unusual behavior from privileged user accounts etc. Introducing Ways To Detect Cyber Security Incidents Development And Implementation Of Security Incident Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Privileged User Accounts, Unusual Behavior, Network Traffic, using this template. Grab it now to reap its full benefits.
-
 SASE IT Cloud Access Security Broker Implementation Models Ppt Powerpoint Template
SASE IT Cloud Access Security Broker Implementation Models Ppt Powerpoint TemplateThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out-of-band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Introducing SASE IT Cloud Access Security Broker Implementation Models Ppt Powerpoint Template to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on API Scanning, Forward Proxy, Reverse Proxy, using this template. Grab it now to reap its full benefits.
-
 Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SS
Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SSThis slide represents best practices for effective endpoint security. It covers educating users, finding and tracking business owned devices, and installation maintenance of operating systems.Increase audience engagement and knowledge by dispensing information using Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SS. This template helps you present information on three stages. You can also present information on Such Business, Operating System, Frequent Basis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
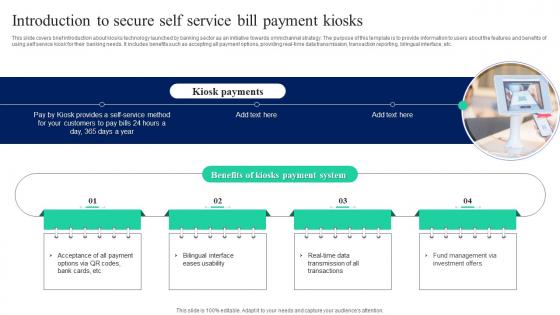 Introduction To Secure Self Service Bill Payment Implementation Of Omnichannel Banking
Introduction To Secure Self Service Bill Payment Implementation Of Omnichannel BankingThis slide covers brief introduction about kiosks technology launched by banking sector as an initiative towards omnichannel strategy. The purpose of this template is to provide information to users about the features and benefits of using self service kiosk for their banking needs. It includes benefits such as accepting all payment options, providing real time data transmission, transaction reporting, bilingual interface, etc. Increase audience engagement and knowledge by dispensing information using Introduction To Secure Self Service Bill Payment Implementation Of Omnichannel Banking. This template helps you present information on four stages. You can also present information on Kiosk Payments, Payment System, Investment Offers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SDN Security IT Implementation Process Of Software Defined Networking SDN
SDN Security IT Implementation Process Of Software Defined Networking SDNThis slide outlines the implementation process of software defined networking that includes creating a use case, forming a multi functional team, testing, and reviewing. The main implementation types of SDN are open SDN, SDN via APIs, and SDN via hypervisor based overlay network. Increase audience engagement and knowledge by dispensing information using SDN Security IT Implementation Process Of Software Defined Networking SDN. This template helps you present information on four stages. You can also present information on Process, Implementation, Software using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps To Implement Enterprise Blockchain Security
Steps To Implement Enterprise Blockchain SecurityThis slide conveys steps to implement blockchain security for enterprises aimed at increasing data trust, transparency and traceability across a business network. It covers choosing platform, experimenting, scalability and security, build framework, gamification and modelling ecosystems. Introducing our premium set of slides with Steps To Implement Enterprise Blockchain Security. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Choose Platform, Scalability And Security, Gamification, Build Framework. So download instantly and tailor it with your information.
-
 Analyzing Multiple Sales Tactics For Securing New Leads Implementation Guidelines For Sales MKT SS V
Analyzing Multiple Sales Tactics For Securing New Leads Implementation Guidelines For Sales MKT SS VThis slide provides glimpse about employing different techniques that can help the business in new lead generation. It includes techniques such as social media marketing, cold calling, email marketing, their impact, etc. Introducing Analyzing Multiple Sales Tactics For Securing New Leads Implementation Guidelines For Sales MKT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Multiple, Analyzing, Sales, using this template. Grab it now to reap its full benefits.
-
 Reasons To Implement Security In Organizational Communication Plan
Reasons To Implement Security In Organizational Communication PlanThis slide showcases reasons for securing organizational networks. This template focuses on encrypting communication to safeguard business, employees clients. It includes information related to advanced privacy, protecting cyber attacks, etc.Introducing our premium set of slides with Reasons To Implement Security In Organizational Communication Plan. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Improves Customer Confidence, Protects Intellectual Property, Builds Consumer. So download instantly and tailor it with your information.
-
 Blockchain Hashing Sha 256 Implementing Blockchain Security Solutions
Blockchain Hashing Sha 256 Implementing Blockchain Security SolutionsThis slide talks about the hashing SHA256 algorithm used in blockchain technology, including its properties. The purpose of this slide is to give an overview of hashing and its properties, such as collision resistance, deterministic, quick, and irreversible.Introducing Blockchain Hashing Sha 256 Implementing Blockchain Security Solutions to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Collision Resistance, Protecting Integrity, Completely Different, using this template. Grab it now to reap its full benefits.
-
 Disadvantages Of Blockchain Implementing Blockchain Security Solutions
Disadvantages Of Blockchain Implementing Blockchain Security SolutionsThis slide defines the various disadvantages of blockchain technology based on speed, energy, cost, scalability, maturity, and integration.Introducing Disadvantages Of Blockchain Implementing Blockchain Security Solutions to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Energy Consumption, Difficult Scale, Self Maintenance, using this template. Grab it now to reap its full benefits.
-
 How Blockchain Prevents Fraud And Implementing Blockchain Security Solutions
How Blockchain Prevents Fraud And Implementing Blockchain Security SolutionsThis slide describes the different methods used by blockchain technology to prevent data from fraud and stealing. The purpose of this slide is to showcase the various techniques and technologies used in blockchain technology to prevent fraud and data theft.Increase audience engagement and knowledge by dispensing information using How Blockchain Prevents Fraud And Implementing Blockchain Security Solutions. This template helps you present information on four stages. You can also present information on Extremely Difficult, Blockchain Incorporates, Techniques Such using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Major Security Concerns For Implementing Blockchain Security Solutions
Major Security Concerns For Implementing Blockchain Security SolutionsThis slide outlines the critical security concerns related to blockchain networks. The purpose of this slide is to showcase the major risks associated with blockchain technology, including confidentiality, integrity, nonrepudiation, and authentication.Introducing Major Security Concerns For Implementing Blockchain Security Solutions to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Unauthorized, Safeguarding Sensitive, Prevent Unauthorized, using this template. Grab it now to reap its full benefits.
-
 Phases To Perform Blockchain Implementing Blockchain Security Solutions
Phases To Perform Blockchain Implementing Blockchain Security SolutionsThis slide highlights the main phases of blockchain penetration testing. The purpose of this slide is to showcase the different stages of penetration testing, including information gathering and threat modeling, testing and discovery, and exploitation.Increase audience engagement and knowledge by dispensing information using Phases To Perform Blockchain Implementing Blockchain Security Solutions. This template helps you present information on three stages. You can also present information on Information Gathering, Functionality Assess, Retrieving Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risks Involved In Public Blockchain Implementing Blockchain Security Solutions
Risks Involved In Public Blockchain Implementing Blockchain Security SolutionsThis slide represents the challenges involved in public blockchains classified as basic risks, implementation risks, security risks, and legal risks.Introducing Risks Involved In Public Blockchain Implementing Blockchain Security Solutions to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Integrate Standards, Lack Standardization, Vendor Challenges, using this template. Grab it now to reap its full benefits.
-
 Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation
Stages Of Implementing Cyber Security Strategies Cyber Attack Risks MitigationThe following slide highlights major stages of executing cyber security techniques to ensure effective implementation. It includes elements such as plan, analyze, upgrade, continuous improvement etc. Increase audience engagement and knowledge by dispensing information using Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Plan Strategy, Implement Strategy, Analyse Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Precaution Implemented In Powerpoint And Google Slides Cpb
Security Precaution Implemented In Powerpoint And Google Slides CpbPresenting our Security Precaution Implemented In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Security Precaution Implemented. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Budget Distribution For Mobile Security Implementation Mobile Device Security Cybersecurity SS
Budget Distribution For Mobile Security Implementation Mobile Device Security Cybersecurity SSThis slide showcases budget distribution that can help to implement mobile security solutions. Its key elements are biometric solution, virtual private network, employee training, data encryption etc. Introducing Budget Distribution For Mobile Security Implementation Mobile Device Security Cybersecurity SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Biometric Solution, Virtual Private Network, Employee Training using this template. Grab it now to reap its full benefits.
-
 Process To Implement Mobile Vpn In Organization Mobile Device Security Cybersecurity SS
Process To Implement Mobile Vpn In Organization Mobile Device Security Cybersecurity SSThis slide showcases procedure that can help organization to implement VPN for mobile security. Its key steps are assessment, VPN technology selection, infrastructure setup etc. Introducing Process To Implement Mobile Vpn In Organization Mobile Device Security Cybersecurity SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Rating, Ideal, Softwares using this template. Grab it now to reap its full benefits.
-
 Incorporating Secure Multi Party Computation To Boost Data Implementing Digital Transformation And Ai DT SS
Incorporating Secure Multi Party Computation To Boost Data Implementing Digital Transformation And Ai DT SSThis slide provides glimpse about utilizing secure multi party computation SMPC approach that can help businesses in boosting data confidentiality. It includes stages such as input sharing, secure computation, output reconstruction, etc. Increase audience engagement and knowledge by dispensing information using Incorporating Secure Multi Party Computation To Boost Data Implementing Digital Transformation And Ai DT SS. This template helps you present information on three stages. You can also present information on Increase Security Against Attacks, Boost Data Confidentiality, Input Sharing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps To Implement Digital Authentication With IAM Securing Systems With Identity
Steps To Implement Digital Authentication With IAM Securing Systems With IdentityThis slide discusses the IAM implementing digital authentication. The purpose of this slide is to highlight the various types of digital authentication done by IAM, which are unique passwords, pre-shared keys, Behavioral authentication, and biometrics. Increase audience engagement and knowledge by dispensing information using Steps To Implement Digital Authentication With IAM Securing Systems With Identity This template helps you present information on Five stages. You can also present information on Unique Passwords, Biometrics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps To Implement Identity And Access Management Securing Systems With Identity
Steps To Implement Identity And Access Management Securing Systems With IdentityThis slide discusses the Identity and Access Management implementing program. The purpose of this slide is to highlight the implementation process of IAM, including scope identification, evaluating the right IAM approach, finding the best solution, and so on. Increase audience engagement and knowledge by dispensing information using Steps To Implement Identity And Access Management Securing Systems With Identity This template helps you present information on Six stages. You can also present information on Scope Identification, Define A Strategy, Assess Cost Factors using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Timeline To Implement Identity And Access Management Plan Securing Systems With Identity
Timeline To Implement Identity And Access Management Plan Securing Systems With IdentityThis slide shows the timeline for implementing the Identity and Access Management plan. The key steps include defining the project objective, identifying key stakeholders, determining compliance, integrating IAM with the existing system, etc. Introducing Timeline To Implement Identity And Access Management Plan Securing Systems With Identity to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Applications And Data, Public Cloud Platforms using this template. Grab it now to reap its full benefits.
-
 Best Practices To Implement NIDS For Maintaining Effective Cyber Security
Best Practices To Implement NIDS For Maintaining Effective Cyber SecurityThis Slide Represents Effective Strategies For Employing NIDS. It Aims To Help Organizations Implement NIDS To Detect, Respond And Mitigate Cyber Threats Within Networks. Introducing Our Premium Set Of Slides With Best Practices To Implement NIDS For Maintaining Effective Cyber Security. Ellicudate The Three Stages And Present Information Using This PPT Slide. This Is A Completely Adaptable Powerpoint Template Design That Can Be Used To Interpret Topics Like Proper Network Segmentation, Thorough Traffic Analysis, Signature Database Upgradation. So Download Instantly And Tailor It With Your Information.
-
 Budget Allocation For Mobile Security Implementation Mobile Security
Budget Allocation For Mobile Security Implementation Mobile SecurityThis slide represents the estimated and actual cost of implementing mobile security in an organization based on categories like training and security update. Increase audience engagement and knowledge by dispensing information using Budget Allocation For Mobile Security Implementation Mobile Security This template helps you present information on Three stages. You can also present information on Data Exposure Risks, Encryption Vulnerabilities, Authorization Weaknesses using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Penetration Testing Implementation Plan Stages Of Penetration Testing In Cyber Security
Penetration Testing Implementation Plan Stages Of Penetration Testing In Cyber SecurityThis slide represents the process included in penetration testing. The purpose of this slide is to showcase the different steps of penetration testing, such as planning the penetration test, gathering information, scanning for vulnerabilities, and so on. Increase audience engagement and knowledge by dispensing information using Penetration Testing Implementation Plan Stages Of Penetration Testing In Cyber Security. This template helps you present information on Six stages. You can also present information on Plan The Penetration Test, Gather Information, Scan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Features Of Implementing Web Security Solution
Key Features Of Implementing Web Security SolutionThis slide highlights the main objectives of implementing web security in an organization which include security, password control, etc. Introducing Key Features Of Implementing Web Security Solution to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Secure Socket Layer, Password Control, Security, Firewall, using this template. Grab it now to reap its full benefits.
-
 A247 Best Practices For Web Security Implementation
A247 Best Practices For Web Security ImplementationThe purpose of this slide is to highlight the best practices for web security such as inclusive security practices, cybersecurity adoption, etc. Introducing A247 Best Practices For Web Security Implementation to increase your presentation threshold. Encompassed with Seven stages, this template is a great option to educate and entice your audience. Dispence information on Inclusive Security Practices, Diverse Security Measures, Security Exercises, using this template. Grab it now to reap its full benefits.
-
 Security Measures To Implement In Automated Messaging
Security Measures To Implement In Automated MessagingThe purpose of this slide is to outline security measures to be implemented in automated messaging systems such as opting for a reliable SMS provider, SMS verification, etc., for ensuring data protection, encryption, etc. Introducing our premium set of slides with Security Measures To Implement In Automated Messaging. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Reliable SMS Provider, SMS Verification, Otps Keywords. So download instantly and tailor it with your information.
-
 Web Security Upgradation Project Summary For Implementing Web Security
Web Security Upgradation Project Summary For Implementing Web SecurityThe purpose of this slide is to represent the summary of the web security project providing information regarding problems faced, recommended solution, etc. Introducing Web Security Upgradation Project Summary For Implementing Web Security to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Problems, Solutions, Estimated Cost, Estimated Timeline, using this template. Grab it now to reap its full benefits.
-
 Web Security Upgradation Steps For Implementing Vulnerability Scanning In Web Security
Web Security Upgradation Steps For Implementing Vulnerability Scanning In Web SecurityThis slide highlights the process phases for implementing vulnerability scanning which include creating asset inventory, scanning the attack surface, etc. Introducing Web Security Upgradation Steps For Implementing Vulnerability Scanning In Web Security to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Information Regarding Vulnerabilities Discovered, Creates Asset Inventory, using this template. Grab it now to reap its full benefits.
-
 Essential Features For Ecommerce Fraud Prevention Implementing E Commerce Security Measures
Essential Features For Ecommerce Fraud Prevention Implementing E Commerce Security MeasuresThe slide covers features that e-commerce businesses should prioritize when selecting fraud prevention software. It include feature such as machine learning, bot detection, chargeback protection etc.Introducing Essential Features For Ecommerce Fraud Prevention Implementing E Commerce Security Measures to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Chargeback Protection, Risk Scoring, Application Programming Interfaces, using this template. Grab it now to reap its full benefits.
-
 Fraud Prevention Training Program For Different Implementing E Commerce Security Measures
Fraud Prevention Training Program For Different Implementing E Commerce Security MeasuresThe slide represent ecommerce fraud prevention training program designed for various departments. It covers team such as fulfilment, marketing, IT and also training focus and action items. Increase audience engagement and knowledge by dispensing information using Fraud Prevention Training Program For Different Implementing E Commerce Security Measures. This template helps you present information on three stages. You can also present information on Training Purpose, Department, Action Items using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Roles And Responsibilities Fraud Prevention Team Implementing E Commerce Security Measures
Roles And Responsibilities Fraud Prevention Team Implementing E Commerce Security MeasuresThe slide outlines roles and responsibilities for ecommerce fraud detection team. It includes details about chief information security officer, security operations manger, incident response manager, and risk compliance manager.Increase audience engagement and knowledge by dispensing information using Roles And Responsibilities Fraud Prevention Team Implementing E Commerce Security Measures. This template helps you present information on five stages. You can also present information on Security Operations Manager, Incident Response Manager, Security Architecture Manager using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security Measures
Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security MeasuresThe slide depicts secure sockets layer SSL process to encrypt sensitive information between a webs browser and server. It include client web browser, websiteserver, SSL certificate etc. Introducing Ssl Certificate Process To Secure Payment Gateway Implementing E Commerce Security Measures to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Client Check Certificate, Impact, Delivers Encrypted Content, using this template. Grab it now to reap its full benefits.
-
 Steps To Implement Biometric Authentication For User Implementing E Commerce Security Measures
Steps To Implement Biometric Authentication For User Implementing E Commerce Security MeasuresThe slide highlights steps to implement biometric authentication systems effectively for buisness. Key steps include biometric assessment, integration, data security, user enrollment, testing and fallback mechanism etc. Increase audience engagement and knowledge by dispensing information using Steps To Implement Biometric Authentication For User Implementing E Commerce Security Measures. This template helps you present information on six stages. You can also present information on Choose Biometric Method, Fallback Mechanism, User Enrollment, Testing And Evaluation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 United Nations And Cyber Security Initiatives Strategic Guide To Implement Strategy SS
United Nations And Cyber Security Initiatives Strategic Guide To Implement Strategy SSThis slide showcases the United nations and cyber security initiatives. It includes initiatives such as UN general assembly resolutions, UNODA, UNIDIR, CTC and UNODC.Increase audience engagement and knowledge by dispensing information using United Nations And Cyber Security Initiatives Strategic Guide To Implement Strategy SS. This template helps you present information on five stages. You can also present information on General Assembly Resolutions, Disarmament Affairs, Disarmament Research using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.




