Powerpoint Templates and Google slides for Implement Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cloud Access Security Broker Implementation Roadmap
Cloud Access Security Broker Implementation RoadmapThis slide outlines the roadmap for deploying a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to implement the cloud access security broker model. The steps include starting with the most critical cloud application in the portfolio, looking for suitable CASB, etc. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Implementation Roadmap. This template helps you present information on six stages. You can also present information on Security Profile, Determine Whether, Sso Systems using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
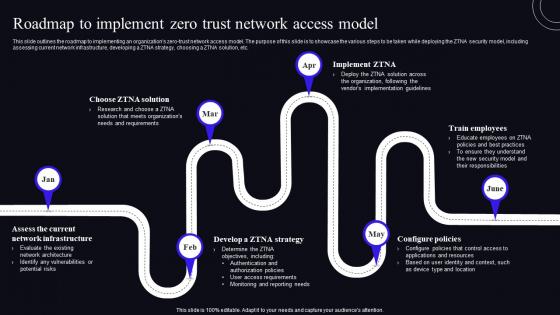 Roadmap To Implement Zero Trust Network Access Model Zero Trust Security Model
Roadmap To Implement Zero Trust Network Access Model Zero Trust Security ModelThis Slide Outlines The Roadmap To Implementing An Organizations Zero-Trust Network Access Model. The Purpose Of This Slide Is To Showcase The Various Steps To Be Taken While Deploying The ZTNA Security Model, Including Assessing Current Network Infrastructure, Developing A ZTNA Strategy, Choosing A ZTNA Solution, Etc. Increase Audience Engagement And Knowledge By Dispensing Information Using Roadmap To Implement Zero Trust Network Access Model Zero Trust Security Model. This Template Helps You Present Information On Six Stages. You Can Also Present Information On Roadmap, Network Infrastructure, Configure Policies Using This PPT Design. This Layout Is Completely Editable So Personaize It Now To Meet Your Audiences Expectations.
-
 Roadmap To Implement Secure Access Service Edge Secure Access Service Edge Sase
Roadmap To Implement Secure Access Service Edge Secure Access Service Edge SaseThis slide depicts the roadmap to implementing secure access service edge in an organization. The purpose of this slide is to demonstrate all the steps to be taken in the SASE implementation process, covering defining SASE objectives and needs, examining the environment and, discovering gaps, etc. Increase audience engagement and knowledge by dispensing information using Roadmap To Implement Secure Access Service Edge Secure Access Service Edge Sase. This template helps you present information on six stages. You can also present information on Environment, Solutions, Troubleshooting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker Implementation Roadmap Next Generation CASB
Cloud Access Security Broker Implementation Roadmap Next Generation CASBThis slide outlines the roadmap for deploying a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to implement the cloud access security broker model. The steps include starting with the most critical cloud application in the portfolio, looking for suitable CASB, etc. Introducing Cloud Access Security Broker Implementation Roadmap Next Generation CASB to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Portfolio, Cloud Application, Systems using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Timeline To Implementation Tokenization In Data Security
Tokenization For Improved Data Security Timeline To Implementation Tokenization In Data SecurityThis slide outlines the timeline for executing tokenization. The purpose of this slide is to showcase the different steps performed while implementing tokenization, including key management, monitoring, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Timeline To Implementation Tokenization In Data Security. This template helps you present information on six stages. You can also present information on Tokenization Key Management, Monitoring And Auditing, Tokenization Methods, Data Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint Security Roadmap To Implement Effective Endpoint Security
Endpoint Security Roadmap To Implement Effective Endpoint SecurityThis slide outlines the steps to deploy endpoint security which include recognizing known malware, reduce end user access, utilizing application control, etc. Increase audience engagement and knowledge by dispensing information using Endpoint Security Roadmap To Implement Effective Endpoint Security. This template helps you present information on six stages. You can also present information on Utilize Sensible Application Control, Recognize And Avoid Known Malware, Block Dangerous Activity, Effective Endpoint Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker Implementation Roadmap CASB Cloud Security
Cloud Access Security Broker Implementation Roadmap CASB Cloud SecurityThis slide outlines the roadmap for deploying a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to implement the cloud access security broker model. The steps include starting with the most critical cloud application in the portfolio, looking for suitable CASB, etc. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Implementation Roadmap CASB Cloud Security. This template helps you present information on six stages. You can also present information on Cloud Access Security Broker, Cloud Application In The Portfolio, Implementation Roadmap using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


