Powerpoint Templates and Google slides for Implement Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Bi design and implementation security ppt powerpoint presentation picture
Bi design and implementation security ppt powerpoint presentation picturePresenting this set of slides with name BI Design And Implementation Security Ppt Powerpoint Presentation Picture. This is a four stage process. The stages in this process are Web Based, Architecture, Scalability, Security. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Automated security awareness platform and cost implementing security awareness program ppt tips
Automated security awareness platform and cost implementing security awareness program ppt tipsThis slide covers the Automated training programs for security awareness that will help educate workers to act appropriately, even when introduced to entirely new risks. Increase audience engagement and knowledge by dispensing information using Automated Security Awareness Platform And Cost Implementing Security Awareness Program Ppt Tips. This template helps you present information on one stage. You can also present information on Automated Security Awareness Platform And Cost using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Communication plan general format implementing security awareness program ppt formats
Communication plan general format implementing security awareness program ppt formatsThis slide covers the schedule communication plan for security awareness program including brief description, frequency and audience. Introducing Communication Plan General Format Implementing Security Awareness Program Ppt Formats to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Communication, Description, Frequency, using this template. Grab it now to reap its full benefits.
-
 Where is the gap in security programs implementing security awareness program ppt grid
Where is the gap in security programs implementing security awareness program ppt gridThis slide covers the problems in the organization regarding security awareness training along with the gap and solution to overcome those gaps. Increase audience engagement and knowledge by dispensing information using Where Is The Gap In Security Programs Implementing Security Awareness Program Ppt Grid. This template helps you present information on three stages. You can also present information on Where Is The Gap In Security Programs using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 It security operations impact of successful implementation of secops system ppt inspiration
It security operations impact of successful implementation of secops system ppt inspirationThis slide portrays information regarding the impact of successful implementation of SecOps system in terms alert fatigue reduction, threat hunting improvement, etc. Introducing IT Security Operations Impact Of Successful Implementation Of Secops System Ppt Inspiration to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Security, Analyst, Improvement, Reduction, using this template. Grab it now to reap its full benefits.
-
 Enhanced security event management current challenges faced by firm while implementing secops ppt skills
Enhanced security event management current challenges faced by firm while implementing secops ppt skillsThis slide portrays information regarding the present challenges faced by firm while implementing SecOps system including budget constraint, absence of pool of talent and expertise and lack of essential tools. Introducing Enhanced Security Event Management Current Challenges Faced By Firm While Implementing Secops Ppt Skills to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Budget Tools, Pool Of Talent And Expertise, using this template. Grab it now to reap its full benefits.
-
 Enhanced security event management impact of successful implementation of secops system ppt icon
Enhanced security event management impact of successful implementation of secops system ppt iconThis slide portrays information regarding the impact of successful implementation of SecOps system in terms alert fatigue reduction, threat hunting improvement, etc. Introducing Enhanced Security Event Management Impact Of Successful Implementation Of Secops System Ppt Icon to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Security, Analyst, Improvement, Reduction, using this template. Grab it now to reap its full benefits.
-
 Enhanced security event management prerequisites for effective secops implementation ppt styles
Enhanced security event management prerequisites for effective secops implementation ppt stylesThis slide portrays information regarding the prerequisites that essential for effective implementation of SecOps in terms of development and operations team, etc. Increase audience engagement and knowledge by dispensing information using Enhanced Security Event Management Prerequisites For Effective Secops Implementation Ppt Styles. This template helps you present information on six stages. You can also present information on Development, Data Available, Security With Compliance, Operations Team using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementing security management plan security plan monitoring ppt ideas show
Implementing security management plan security plan monitoring ppt ideas showThis slide provides information about the ninth and the last step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e., System Maintenance and Monitoring. Introducing Implementing Security Management Plan Security Plan Monitoring Ppt Ideas Show to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on System Monitoring, Installation, Security Monitoring, using this template. Grab it now to reap its full benefits.
-
 Implementing security management plan security recovery plan ppt slides templates
Implementing security management plan security recovery plan ppt slides templatesThis slide provides information about the eighth step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e., Data Backup and Data Loss Recovery Plan. Increase audience engagement and knowledge by dispensing information using Implementing Security Management Plan Security Recovery Plan Ppt Slides Templates. This template helps you present information on three stages. You can also present information on Location, Backup, Schedule, Restoration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Way management challenges implementing security management plan
Way management challenges implementing security management planThis slide provides information about the way that the company and IT security manager must choose in order to solve the challenge problem related to Potential Insider Threats. the solution is to set up an advanced security management plan in place with the help of a set series of steps mentioned in the slide. Increase audience engagement and knowledge by dispensing information using Way Management Challenges Implementing Security Management Plan. This template helps you present information on ten stages. You can also present information on Objectives, Assessment, Access Controls, Competencies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enhancing overall project security it facilities rendered by security centre implementation
Enhancing overall project security it facilities rendered by security centre implementationThis slide provides information regarding the various facilities that are offered by successful implementation of security center in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Introducing Enhancing Overall Project Security It Facilities Rendered By Security Centre Implementation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Implementation, Investigation, Prevention, using this template. Grab it now to reap its full benefits.
-
 Timeline For Cyber Security Implementation In Company
Timeline For Cyber Security Implementation In CompanyIntroducing our premium set of slides with name Timeline For Cyber Security Implementation In Company. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Timeline For Cyber Security, Implementation In Company. So download instantly and tailor it with your information.
-
 6 Stage Process For Implementation Of Risk Management In Cyber Security Project
6 Stage Process For Implementation Of Risk Management In Cyber Security ProjectThis This slide signifies the six step process for successful implementation of risk assessment in cyber security project. It covers information about stages like identify, analyse, evaluate, prioritize, treat and monitor. Presenting our set of slides with name 6 Stage Process For Implementation Of Risk Management In Cyber Security Project. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Analyse, Evaluate, Prioritize, Treat.
-
 Benefits Of Implementing Web Application Firewall Implementing Cyber Security Ppt Structure
Benefits Of Implementing Web Application Firewall Implementing Cyber Security Ppt StructureThis slide represents the advantages of implementing a software which protects web applications from variety of application layer attacks. It includes key benefits of implementing web application firewall such as defense, fights vulnerabilities etc. Increase audience engagement and knowledge by dispensing information using Benefits Of Implementing Web Application Firewall Implementing Cyber Security Ppt Structure. This template helps you present information on one stage. You can also present information on Fights Vulnerabilities, Implementing, Application Firewall using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementing Cyber Security Strategies To Analyze Cyber Security Incidents Ppt Elements
Implementing Cyber Security Strategies To Analyze Cyber Security Incidents Ppt ElementsThis slide represents the techniques to be used by the organizations to analyze the impact of cyber security incidents on business operations. It includes strategies for analyzing cyber incidents such as profile network and systems etc. Increase audience engagement and knowledge by dispensing information using Implementing Cyber Security Strategies To Analyze Cyber Security Incidents Ppt Elements. This template helps you present information on two stages. You can also present information on Profile Network And Systems, Understand Normal Behaviors, Perform Event Correlation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness Training
Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness TrainingThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness Training. This template helps you present information on four stages. You can also present information on Describes Spam, Cyberbullying, Protect The Confidential Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Awareness Trends In 2023 Implementing Security Awareness Training
Cyber Security Awareness Trends In 2023 Implementing Security Awareness TrainingThe purpose of this slide is to showcase security awareness trends which the organization has to look out for in 2023. Increase malware and ransomware attack, more employees will be targeted by mobile malware attack and advancement of phishing attack are some of the major trends mentioned in the slide. Introducing Cyber Security Awareness Trends In 2023 Implementing Security Awareness Training to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware Attack, Malware Attack, Phishing Attack, using this template. Grab it now to reap its full benefits.
-
 G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks
G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Current Assessment, Organization, Cyber Security, using this template. Grab it now to reap its full benefits.
-
 General Outlook Of Ransomware Attack Implementing Security Awareness Training
General Outlook Of Ransomware Attack Implementing Security Awareness TrainingThe purpose of this slide is to outline an example of ransomware attack. The slide provides information about the working of ransomware attack work and how it can encrypts the victims data. Increase audience engagement and knowledge by dispensing information using General Outlook Of Ransomware Attack Implementing Security Awareness Training. This template helps you present information on four stages. You can also present information on Programme, General Outlook, Ransomware Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Outlook Of Social Engineering Attack Implementing Security Awareness Training
Outlook Of Social Engineering Attack Implementing Security Awareness TrainingThe purpose of this slide is to showcase an example of social engineering attack. It also covers information about how the social engineering attack work and spread malware. Introducing Outlook Of Social Engineering Attack Implementing Security Awareness Training to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Engineering Attack, Completion Of A Survey, Social Engineering Attack, using this template. Grab it now to reap its full benefits.
-
 Overview Of Business Email Compromise Attack Implementing Security Awareness Training
Overview Of Business Email Compromise Attack Implementing Security Awareness TrainingThe purpose of this slide is to delineate an example of business email compromise attack. Information covered in this slide is related to the working of this attack and how it can result in loss of company reputation. Increase audience engagement and knowledge by dispensing information using Overview Of Business Email Compromise Attack Implementing Security Awareness Training. This template helps you present information on four stages. You can also present information on Business, Compromise Attack, Risk Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Running Cyber Security Awareness Campaign Implementing Security Awareness Training
Running Cyber Security Awareness Campaign Implementing Security Awareness TrainingThe purpose of this slide is to provide an overview of cyber security awareness campaign which can be used to educate staff members. The campaign covers information about the objectives, security awareness topics to cover and various activities which will be covered. Increase audience engagement and knowledge by dispensing information using Running Cyber Security Awareness Campaign Implementing Security Awareness Training. This template helps you present information on two stages. You can also present information on Campaign Objectives, Security Awareness, Various Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Awareness Training Program Challenges Implementing Security Awareness Training
Security Awareness Training Program Challenges Implementing Security Awareness TrainingThe purpose of this slide is to exhibit biggest cyber security awareness challenges which is faced by the organization. Outdated content, burden on administrators, low employee participation rate and employees losing interest are some of the key challenges which are highlighted in the slide. Introducing Security Awareness Training Program Challenges Implementing Security Awareness Training to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Outdated Content, Burden On Administrators, Employees Lose Interest, using this template. Grab it now to reap its full benefits.
-
 Understanding The Frequency And Weightage Implementing Security Awareness Training
Understanding The Frequency And Weightage Implementing Security Awareness TrainingThe purpose of this slide is to showcase the frequency and weightage of different cyber attacks on multiple departments. The major departments mentioned in the slide are financial, marketing, information technology IT and human resource HR. Introducing Understanding The Frequency And Weightage Implementing Security Awareness Training to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Financial Department, Marketing Team, It Department, using this template. Grab it now to reap its full benefits.
-
 Various Techniques To Successfully Prevent Business Implementing Security Awareness Training
Various Techniques To Successfully Prevent Business Implementing Security Awareness TrainingThe purpose of this slide is to outline different techniques which can be used to protect organization from business email compromise attack. The techniques covered in the slide are sender policy framework SPF, using strong password policy and process for wire transfers. Increase audience engagement and knowledge by dispensing information using Various Techniques To Successfully Prevent Business Implementing Security Awareness Training. This template helps you present information on one stage. You can also present information on Sender Policy Framework, Strong Process For Wire Transfers, Strong Password Policy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Case Study On Security Improvement Through Secops Implementation
Case Study On Security Improvement Through Secops ImplementationThis slide exhibits a case study of the SecOps application in a pharmaceutical company. It includes information about the firm, challenges, solutions, and benefits to a business. Introducing our premium set of slides with Case Study On Security Improvement Through Secops Implementation. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Challenges, Solution, Benefit To Business. So download instantly and tailor it with your information.
-
 SASE IT Secure Access Service Edge Implementation Steps Ppt Powerpoint Guidelines
SASE IT Secure Access Service Edge Implementation Steps Ppt Powerpoint GuidelinesThis slide outlines the steps to implement a secure service edge in a business. The purpose of this slide is to demonstrate the various guidelines to consider while implementing the SASE model in an organization. The main steps include defining SASE goals and requirements, selecting the SD-WAN backbone, incorporating zero-trust solutions, etc. Increase audience engagement and knowledge by dispensing information using SASE IT Secure Access Service Edge Implementation Steps Ppt Powerpoint Guidelines. This template helps you present information on five stages. You can also present information on SASE Goals And Requirements, Select SD-WAN Backbone, Incorporate Zero Trust Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SDN Security IT Timeline For Software Defined Network Implementation
SDN Security IT Timeline For Software Defined Network ImplementationThis slide talks about the timeline for software defined network implementation, including the steps to be performed, such as defining the use case, creating a cross functional team, testing, and reviewing. Introducing SDN Security IT Timeline For Software Defined Network Implementation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Timeline, Software, Network, using this template. Grab it now to reap its full benefits.
-
 Security Practices For Enterprise Blockchain Implementation
Security Practices For Enterprise Blockchain ImplementationThis slide presents security practices for blockchain implementation aimed at optimizing security and mitigation practices to improve cybersecurity technology. It covers permissioned blockchain, case analysis, create governance structure and file storage. Presenting our set of slides with Security Practices For Enterprise Blockchain Implementation. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Permissioned Blockchain, Create Governance Structure, Case Analysis, File Storage.
-
 Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks Management
Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks ManagementThe following slide illustrates some best practices to execute preventive actions for cyber attacks. It includes elements such as train employees, updating systems and software, developing incident response plan, backing up data, maintaining compliance etc. Increase audience engagement and knowledge by dispensing information using Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks Management. This template helps you present information on six stages. You can also present information on Train Employees, Maintain Compliance, Develop Incident Response Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
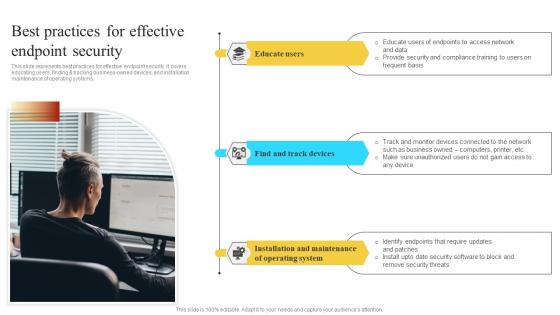 Implementation Of Information Best Practices For Effective Endpoint Security Strategy SS V
Implementation Of Information Best Practices For Effective Endpoint Security Strategy SS VThis slide represents best practices for effective endpoint security. It covers educating users finding and tracking business owned devices and installation maintenance of operating systems. Increase audience engagement and knowledge by dispensing information using Implementation Of Information Best Practices For Effective Endpoint Security Strategy SS V. This template helps you present information on three stages. You can also present information on Educate Users, Installation Maintenance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
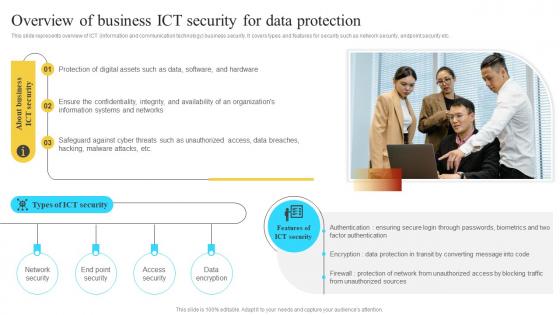 Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V
Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Protection Of Digital, Safeguard Against Cyber, using this template. Grab it now to reap its full benefits.
-
 Icon For Implementation Of Cyber Security Strategy Action Plan
Icon For Implementation Of Cyber Security Strategy Action PlanPresenting our set of slides with Icon For Implementation Of Cyber Security Strategy Action Plan. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Strategy, Security.
-
 Need To Implement IoT Cyber Security Improving IoT Device Cybersecurity IoT SS
Need To Implement IoT Cyber Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit need to implement Internet of Things IoT security in order to avoid cyber attack and minimize losses. The slide covers information about data protection of users, adhering to regulatory standards, limited security of IoT devices, etc. Introducing Need To Implement IoT Cyber Security Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Required, Companies, Potential, using this template. Grab it now to reap its full benefits.
-
 Kpis For ERP Security Management Implementation
Kpis For ERP Security Management ImplementationThis slide showcases the important KPIs for implementation of ERP security management. Its objective is to check the key metrics and identify the problems. This slide includes inventory turnover, project margins, demand forecasting, business productivity, employee satisfaction, etc. Introducing our premium set of slides with Kpis For ERP Security Management Implementation. Ellicudate the Nine stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Inventory Turnover, Business Productivity, Customer Experience. So download instantly and tailor it with your information.
-
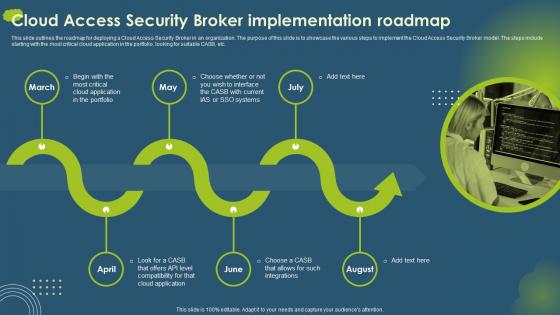 Cloud Access Security Broker CASB V2 Implementation Roadmap Ppt Gallery Portrait
Cloud Access Security Broker CASB V2 Implementation Roadmap Ppt Gallery PortraitThis slide outlines the roadmap for deploying a Cloud Access Security Broker in an organization. The purpose of this slide is to showcase the various steps to implement the Cloud Access Security Broker model. The steps include starting with the most critical cloud application in the portfolio, looking for suitable CASB, etc. Introducing Cloud Access Security Broker CASB V2 Implementation Roadmap Ppt Gallery Portrait to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Critical Cloud Application, Compatibility, using this template. Grab it now to reap its full benefits.
-
 Implementing Virtual Infrastructure Security Integration Roadmap
Implementing Virtual Infrastructure Security Integration RoadmapThis slide showcases timeline that assist businesses to implement virtual infrastructure to enhance data security integration and management. It includes carious phases such as resource virtualization, application virtualization, internal cloud and hybrid cloud. Introducing our premium set of slides with Implementing Virtual Infrastructure Security Integration Roadmap. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Trusted Platform Incorporation, Zero Data Loss, Trusted Security. So download instantly and tailor it with your information.
-
 Implementing Byod Policy To Enhance Develop Security Policies For Data Protection
Implementing Byod Policy To Enhance Develop Security Policies For Data ProtectionThis slide shows major data protection policies for handling sensitive data of corporate. It include policies such as device security, network and data handling, etc. Introducing Implementing Byod Policy To Enhance Develop Security Policies For Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Network Security, Data Handling, Device Security, Data Protection, using this template. Grab it now to reap its full benefits.
-
 Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy
Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod PolicyThis slide shows essential considerations for protecting crucial data of company in organization. It include security areas such as device security, network security and software updates, etc. Increase audience engagement and knowledge by dispensing information using Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy. This template helps you present information on five stages. You can also present information on Device Security, Mobile Device Management, Network Security, Malware Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda Implementing Strategies To Mitigate Cyber Security Threats
Agenda Implementing Strategies To Mitigate Cyber Security ThreatsIntroducing Agenda Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Security Awareness, Risk Management Process, Cyber Risk using this template. Grab it now to reap its full benefits.
-
 Cyber Security Awareness Facts And Statistics Implementing Strategies To Mitigate Cyber Security Threats
Cyber Security Awareness Facts And Statistics Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases some facts and figures to generate awareness about cyber crimes. It includes elements such as hike in ransomware attacks, more employees are expected to be target of malware attacks, increasing cost of data breaches etc Introducing Cyber Security Awareness Facts And Statistics Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Malware Attacks, Employees, Social Engineering Attacks using this template. Grab it now to reap its full benefits.
-
 Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security Threats
Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the negative impact of cyber crimes on business to build control actions and strategies. It includes key elements such as rising costs, reputational damage, operational disruption, loss of revenue etc. Introducing Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Rising Cost, Reputational Damage, Operational Disruption using this template. Grab it now to reap its full benefits.
-
 Steps To Implement Cost Effective Information Security Program
Steps To Implement Cost Effective Information Security ProgramThis template shows cost effective key steps for information security program which helps to create program by utilizing some automated tools. It further includes steps such as identify assets and related threats ,identify and prioritize tasks . Introducing our premium set of slides with Steps To Implement Cost Effective Information Security Program Ellicudate the Six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Assets And Related Threats, Identify And Prioritize Risks, Information Security Controls. So download instantly and tailor it with your information.
-
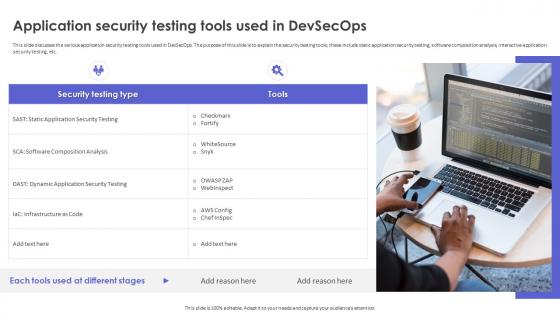 Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOps
Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOpsThis slide discusses the various application security testing tools used in DevSecOps. The purpose of this slide is to explain the security testing tools these include static application security testing, software composition analysis, interactive application security testing, etc. Increase audience engagement and knowledge by dispensing information using Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOps. This template helps you present information on one stages. You can also present information on Application Security Testing, Software Composition Analysis, Interactive Application Security Testing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Advantages Of Implementing Network Infrastructure Security
Key Advantages Of Implementing Network Infrastructure SecurityThe following slide emphasizes advantages like resource sharing, site licenses, productivity, and security benefits, supporting organizations in understanding the value of network infrastructure security implementation. Presenting our set of slides with Key Advantages Of Implementing Network Infrastructure Security This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Improved Resource Sharing, Shared Site Licenses, Data Protection
-
 Survey Statistics Highlighting Need For Employee Implementing Organizational Security Training
Survey Statistics Highlighting Need For Employee Implementing Organizational Security TrainingThe slide highlights the need for employee security awareness in organizations to eliminate or easily detect cyber attacks and cloud security issues. It includes malware infection, social engineering, etc. Increase audience engagement and knowledge by dispensing information using Survey Statistics Highlighting Need For Employee Implementing Organizational Security Training. This template helps you present information on four stages. You can also present information on Identify Cyber Attacks, Social Engineering, Malware Infection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ai Technology Implementation Icon For Robust OT Cyber Security
Ai Technology Implementation Icon For Robust OT Cyber SecurityPresenting our set of slides with Ai Technology Implementation Icon For Robust OT Cyber Security This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on AI Technology Implementation Icon, Robust OT Cyber Security
-
 Post Implementation Measures To Enhance Ecommerce Security
Post Implementation Measures To Enhance Ecommerce SecurityThis slide shows the three step process of implementing successful ecommerce security to defend against the cyber attacks. The steps are testing, training and continued monitoring Presenting our set of slides with Post Implementation Measures To Enhance Ecommerce Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Measures, Continued Monitoring.
-
 Least Privilege Implementation For Segregation Building Next Generation Endpoint Security Cybersecurity SS
Least Privilege Implementation For Segregation Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases implementation of least privilege principle for segregation of duties. It provides details about time limits, certain access, etc.Introducing Least Privilege Implementation For Segregation Building Next Generation Endpoint Security Cybersecurity SS to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Action Steps, Real Problem Solved, Financial Data, using this template. Grab it now to reap its full benefits.
-
 Timeline For Implementing IT Security Awareness Training Modules Cybersecurity SS
Timeline For Implementing IT Security Awareness Training Modules Cybersecurity SSThis slide represents timeline for implementing training program for organizational employees to effectively understand, prevent and mitigate cyber security risks. Increase audience engagement and knowledge by dispensing information using Timeline For Implementing IT Security Awareness Training Modules Cybersecurity SS. This template helps you present information on six stages. You can also present information on Ransomware Awareness Program, Passwords And Authentication, Social Engineering, Insider Threats Awareness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 User Based Security Training Model Strategic Guide To Implement Strategy SS
User Based Security Training Model Strategic Guide To Implement Strategy SSIntroducing User Based Security Training Model Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Compromised System, Compromised Network, Critical Assets, Exfiltrate Sensitive Data, using this template. Grab it now to reap its full benefits.


