Powerpoint Templates and Google slides for How
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 0614 learning styles howard gardner new powerpoint presentation slide template
0614 learning styles howard gardner new powerpoint presentation slide templateAdjust PowerPoint image slides font, text, color and design as per your performance. Appropriate for entrepreneurs and large business organization. This PPT theme wholly supported with Google slides. Formats can easily be changed into other software’s applications like PDF and JPEG. Simple to input company logo, brand name or name. The quality of presentation slide does not blur even when your project it on wide screen.
-
 How Quality Assurance Works In Agile Approach Ppt Powerpoint Icons
How Quality Assurance Works In Agile Approach Ppt Powerpoint IconsThis slide shows the role of Quality Assurance model in Agile methodology and how Quality Assurance make work easy between different processes. Introducing How Quality Assurance Works In Agile Approach Ppt Powerpoint Icons to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Daily Scrum Meetings, Communication, Developers, Meetings, using this template. Grab it now to reap its full benefits.
-
 How Does Cloud Security Work Data Security Cloud Information Security
How Does Cloud Security Work Data Security Cloud Information SecurityThis slide represents the data security under the cloud security work process, and it also shows the various factors that cover data security.Introducing How Does Cloud Security Work Data Security Cloud Information Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Accessibility, Knowledge, Organized Documented using this template. Grab it now to reap its full benefits.
-
 Multi Cloud It Environments After Implementing How A Cloud Architecture Review
Multi Cloud It Environments After Implementing How A Cloud Architecture ReviewThis slide covers the running all the workloads on a variety of clouds including public cloud, third party public clouds, hosted private clouds, and colocation servers while managing them. Introducing Multi Cloud It Environments After Implementing How A Cloud Architecture Review to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Migration Services, Managed Services, Security Services, using this template. Grab it now to reap its full benefits.
-
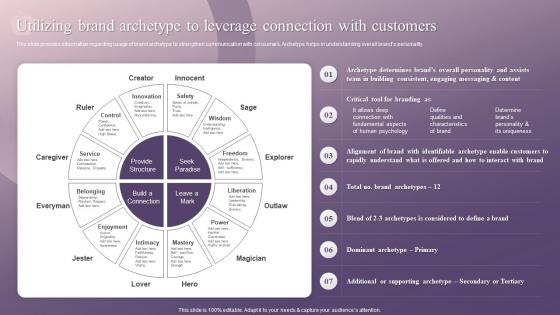 Utilizing Brand Archetype To Leverage Connection With Customers How Apple Has Emerged As Innovative
Utilizing Brand Archetype To Leverage Connection With Customers How Apple Has Emerged As InnovativeThis slide provides information regarding usage of brand archetype to strengthen communication with consumers.Archetype helps in understanding overall brands personality.Increase audience engagement and knowledge by dispensing information using Utilizing Brand Archetype To Leverage Connection With Customers How Apple Has Emerged As Innovative.This template helps you present information on seven stages.You can also present information on Identifiable Archetype, Rapidly Understand, Brand Archetypes using this PPT design.This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ultimate Guide For Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS
Ultimate Guide For Blockchain How Does Phishing Attack Works On Blockchain Network BCT SSThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS This template helps you present information on Seven stages. You can also present information on Phishing Email, Attacker, Internet Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How A Stellar Blockchain Network Platform Works Comprehensive Evaluation BCT SS
How A Stellar Blockchain Network Platform Works Comprehensive Evaluation BCT SSThis slide covers process of how Stellar blockchain technology platform operates for facilitating crypto transactions. It includes steps from sending money to receiver for a business transaction, conversations into XLM cryptocurrency, approval of bank along with deducting money from senders account, etc. Introducing How A Stellar Blockchain Network Platform Works Comprehensive Evaluation BCT SS to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Stellar Blockchain, Network Platform Works, Stellar Network using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity How Does Phishing Attack Works On Blockchain Network BCT SS V
Blockchain And Cybersecurity How Does Phishing Attack Works On Blockchain Network BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity How Does Phishing Attack Works On Blockchain Network BCT SS V This template helps you present information on Seven stages. You can also present information on Phishing Email, Internet Network, Dispense Email using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Challenges Of Performing Prompt Engineering Prompt Engineering How To Communicate With Ai AI SS
Challenges Of Performing Prompt Engineering Prompt Engineering How To Communicate With Ai AI SSThis slide showcases challenges of performing prompt engineering with large language models LLMs, making developers aware about potential issues. It provides information about required results, controlling level, etc. Increase audience engagement and knowledge by dispensing information using Challenges Of Performing Prompt Engineering Prompt Engineering How To Communicate With Ai AI SS. This template helps you present information on seven stages. You can also present information on Engineering, Innovativeness, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS V
Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS V This template helps you present information on Seven stages. You can also present information on Steals Data From User System, Obtains Information From System using this PPT design. This layout is completely editable so personaize it now


