Powerpoint Templates and Google slides for Encryption Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Encryption For Data Security Powerpoint Presentation Slides Cybersecurity CD
Encryption For Data Security Powerpoint Presentation Slides Cybersecurity CDDitch the Dull templates and opt for our engaging Encryption For Data Security Powerpoint Presentation Slides Cybersecurity CD deck to attract your audience. Our visually striking design effortlessly combines creativity with functionality, ensuring your content shines through. Compatible with Microsoft versions and Google Slides, it offers seamless integration of presentation. Save time and effort with our pre-designed PPT layout, while still having the freedom to customize fonts, colors, and everything you ask for. With the ability to download in various formats like JPG, JPEG, and PNG, sharing your slides has never been easier. From boardroom meetings to client pitches, this deck can be the secret weapon to leaving a lasting impression.
-
 Lack Of Encryption As An Information Security Threat Training Ppt
Lack Of Encryption As An Information Security Threat Training PptPresenting Lack of Encryption as an Information Security Threat. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Encryption As A Type Of Application Security Training Ppt
Encryption As A Type Of Application Security Training PptPresenting Encryption as a Type of Application Security. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Firewall Enterprise Protection Security Installation Encryption
Firewall Enterprise Protection Security Installation EncryptionIntroduce your topic and host expert discussion sessions with this Firewall Enterprise Protection Security Installation Encryption. This template is designed using high-quality visuals, images, graphics, etc, that can be used to showcase your expertise. Different topics can be tackled using the twelve slides included in this template. You can present each topic on a different slide to help your audience interpret the information more effectively. Apart from this, this PPT slideshow is available in two screen sizes, standard and widescreen making its delivery more impactful. This will not only help in presenting a birds-eye view of the topic but also keep your audience engaged. Since this PPT slideshow utilizes well-researched content, it induces strategic thinking and helps you convey your message in the best possible manner. The biggest feature of this design is that it comes with a host of editable features like color, font, background, etc. So, grab it now to deliver a unique presentation every time.
-
 Blockchain icon symbol circle computers encryption security technology
Blockchain icon symbol circle computers encryption security technologyEngage buyer personas and boost brand awareness by pitching yourself using this prefabricated set. This Blockchain Icon Symbol Circle Computers Encryption Security Technology is a great tool to connect with your audience as it contains high-quality content and graphics. This helps in conveying your thoughts in a well-structured manner. It also helps you attain a competitive advantage because of its unique design and aesthetics. In addition to this, you can use this PPT design to portray information and educate your audience on various topics. With twelve slides, this is a great design to use for your upcoming presentations. Not only is it cost-effective but also easily pliable depending on your needs and requirements. As such color, font, or any other design component can be altered. It is also available for immediate download in different formats such as PNG, JPG, etc. So, without any further ado, download it now.
-
 Statistics Of Cloud Data Security Attacks In Organization Cloud Data Encryption
Statistics Of Cloud Data Security Attacks In Organization Cloud Data EncryptionThis slide summarizes data security attacks across different organizational departments, such as sales, IT department, finance, marketing, operations, etc. The outlined attacks are data interception, unauthorized access, data breaches, etc. Deliver an outstanding presentation on the topic using this Statistics Of Cloud Data Security Attacks In Organization Cloud Data Encryption. Dispense information and present a thorough explanation of Data Interception, Unauthorized Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
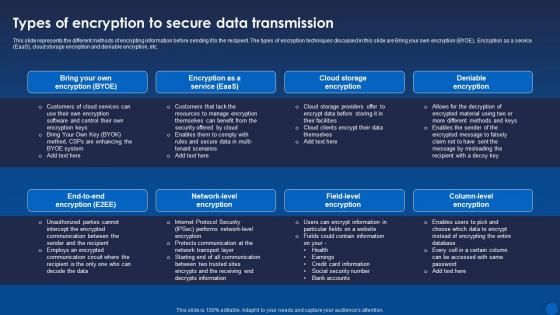 Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age It
Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age ItThis slide represents the different methods of encrypting information before sending it to the recipient. The types of encryption techniques discussed in this slide are Bring your own encryption BYOE, Encryption as a service EaaS, cloud storage encryption and deniable encryption, etc. Present the topic in a bit more detail with this Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Data Transmission, Encryption, Deniable Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption For Data Encrypted Email Practices For Secure Messaging Cybersecurity SS
Encryption For Data Encrypted Email Practices For Secure Messaging Cybersecurity SSThis slide showcases public key cryptography deployment which can help employees increased speed and user experience of their platforms. It provides details about private key, key generation, decryption, etc. Present the topic in a bit more detail with this Encryption For Data Encrypted Email Practices For Secure Messaging Cybersecurity SS. Use it as a tool for discussion and navigation on Reduced Data Breaches, Reduced Email Compromises, Create Strong Passwords. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption For Data Major Types Of Encryption For Data Security Cybersecurity SS
Encryption For Data Major Types Of Encryption For Data Security Cybersecurity SSThis slide major types of encryption technology, focused on improving data privacy and security of todays business. It provides details about symmetric, asymmetric, RSA, data encryption standard, etc. Introducing Encryption For Data Major Types Of Encryption For Data Security Cybersecurity SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Symmetric Encryption, Asymmetric Encryption, RSA Encryption, using this template. Grab it now to reap its full benefits.
-
 Encryption For Data SSL Protocol Deployment For Secure Communication Cybersecurity SS
Encryption For Data SSL Protocol Deployment For Secure Communication Cybersecurity SSThis slide showcases secure socket layer SSL deployment which can help employees perform secure communication within businesses. It provides details about certificate authority, webmaster, etc. Present the topic in a bit more detail with this Encryption For Data SSL Protocol Deployment For Secure Communication Cybersecurity SS. Use it as a tool for discussion and navigation on Reduced Message Forgery, Reduced Data Theft, Less Eavesdropping. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 WIFI Encryption Security Device Colored Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Encryption Security Device Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis PowerPoint icon features a colourful illustration of a lock, symbolizing the security of a wireless network. It is perfect for presentations on WIFI security, data protection, and cyber safety. Use this icon to emphasize the importance of secure networks and data privacy.
-
 WIFI Encryption Security Device Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Encryption Security Device Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon is perfect for any presentation on WIFI security. It features a classic black and white design with a laptop and a router, making it ideal for any modern business presentation. It is easy to use and can be used to illustrate the importance of secure WIFI connections.
-
 Password Security Authentication Encryption Illustration
Password Security Authentication Encryption IllustrationThis coloured powerpoint icon is a visual representation of password security. It features a padlock with a keyhole, a shield, and a key. It is perfect for illustrating the importance of secure passwords in presentations.
-
 Data Security Encryption Technology Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Security Encryption Technology Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Data Security Encryption Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Security Encryption Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V
Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Present the topic in a bit more detail with this Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V. Use it as a tool for discussion and navigation on Backup Repository, Encrypted Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Techniques Icon For Securing Big Data Analytics
Encryption Techniques Icon For Securing Big Data AnalyticsIntroducing our Encryption Techniques Icon For Securing Big Data Analytics set of slides. The topics discussed in these slides are Encryption Techniques, Securing Big Data Analytics. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Types Of Encryption For Securing Big Data Analytics
Types Of Encryption For Securing Big Data AnalyticsThis slide highlights the various types of encryption techniques utilized for protecting big data analytics. The purpose of this slide is to help the business safeguard sensitive information for preventing data breaches and information thefts. It includes quantum proof encryption, homomorphic encryption, etc. Introducing our premium set of slides with Types Of Encryption For Securing Big Data Analytics. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Homomorphic Encryption, Differential Privacy. So download instantly and tailor it with your information.
-
 Impact Of Encryption Implementation On Cloud Security Cloud Data Encryption
Impact Of Encryption Implementation On Cloud Security Cloud Data EncryptionThis slide represents the various factors that showcase the improvement of application security after adopting encryption. The parameters discussed are unauthorized access, data breaches, malware and ransomware, phishing attacks, etc. Deliver an outstanding presentation on the topic using this Impact Of Encryption Implementation On Cloud Security Cloud Data Encryption. Dispense information and present a thorough explanation of Unauthorized Access, Data Breaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Timeline For Cloud Data Security Implementation Cloud Data Encryption
Timeline For Cloud Data Security Implementation Cloud Data EncryptionThis slide represents the timeline to implement cloud data encryption in an organization. The main components included are determine sensitive data and required encryption technique, choose a cloud service provider, implement encryption solution in cloud, etc. Introducing Timeline For Cloud Data Security Implementation Cloud Data Encryption to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Test Encryption Solutions, Implement Encryptions Solution, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 And Encryption Ppt Gallery Design Templates
Cloud Access Security Broker CASB V2 And Encryption Ppt Gallery Design TemplatesThis slide describes the improved encryption with CASB version 2.0. The purpose of this slide is to showcase the various encryption features of Cloud Access Security Broker version 2.0, including security that follows the data, content access that can be revoked at any time, and multi-platform compatibility. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 And Encryption Ppt Gallery Design Templates. Dispense information and present a thorough explanation of Detecting Sensitive Information, Personally Identifiable Information, Personal Health Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Best Practices To Implement Suitable Security Protocol Into Network
Encryption Implementation Strategies Best Practices To Implement Suitable Security Protocol Into NetworkThe purpose of this slide is to outline the steps involved in implementing a security protocol into a network. These are access network requirements, plan and design, select the right protocol, prepare the network infrastructure, configure devices, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Best Practices To Implement Suitable Security Protocol Into Network. Dispense information and present a thorough explanation of Assess Network Requirements, Implement User Authentication, Suitable Security Protocol using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use
Encryption Implementation Strategies Data Protection Technologies To Secure Information In UseThis slide compares different data in use protection methods, and their working and associated cost. These methods are IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use. Use it as a tool for discussion and navigation on Identity Management Tools, Digital Rights Protection, Data Protection Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Data Security Concerns Faced By Company
Encryption Implementation Strategies Data Security Concerns Faced By CompanyThis slide discusses the security issues faced by the organization due to a lack of encryption and data protection technologies. These concerns are unauthorized access, data breaches, insider threats, malware and ransomware, phishing attacks, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Data Security Concerns Faced By Company. Dispense information and present a thorough explanation of Data Security Concerns, Phishing Attacks, Data Protection Technologies, Compliance And Regulations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Database Encryption Methods For Business Security
Encryption Implementation Strategies Database Encryption Methods For Business SecurityThis slide discusses the database encryption methods used to encrypt the data of different departments, such as finance, sales, and human resources. The database encryption levels are application-level encryption, plug-in method, TDE, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Database Encryption Methods For Business Security. Use it as a tool for discussion and navigation on Database Encryption Methods, Business Security, Sales And Human Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest
Encryption Implementation Strategies Encryption Technologies To Secure Data At RestThis slide compares different data protection methods, highlighting their advantages and limitations. These methods are full disk encryption, file-level encryption, database encryption, information rights management IRM, data leak prevention DLP,etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Full Disk Encryption, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Impact Of Encryption Implementation On Application Security
Encryption Implementation Strategies Impact Of Encryption Implementation On Application SecurityThis slide represents the various factors which showcase the improvement of application security after adopting encryption. The parameters discussed are data privacy, confidentiality, authentication, compliance, trust and reputation, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Impact Of Encryption Implementation On Application Security. Dispense information and present a thorough explanation of Confidentiality, Data Privacy, Trust And Reputation, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Key Components Of Internet Protocol Security
Encryption Implementation Strategies Key Components Of Internet Protocol SecurityThe purpose of this slide is to discuss the main components of internet protocol security IPsec architecture. These three components are encapsulating security payload ESP, authentication header AH, and internet key exchange IKE. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Key Components Of Internet Protocol Security. Dispense information and present a thorough explanation of Data Integrity, Encryption, Anti Replay, Payload Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Organizational Compliance Regulations For Information Security
Encryption Implementation Strategies Organizational Compliance Regulations For Information SecurityThe purpose of this slide is to summarize the most common regulations that organizations need to comply with, and their requirements. These regulations are HIPAA Health Insurance Portability and Accountability Act, SOX, PCI DSS, breach laws in all US states, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Organizational Compliance Regulations For Information Security. Use it as a tool for discussion and navigation on Health Insurance Portability, Accountability Act, Payment Card Industry, Data Security Standard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use
Encryption Implementation Strategies Overview Of Encryption For Securing Data In UseThe purpose of this slide is to outline the different possible ways of protecting data in use. The methods include IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use. Dispense information and present a thorough explanation of Information Rights Management, Encryption For Securing Data, Role Based Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Secure Socket Layer SSL Security Technology
Encryption Implementation Strategies Secure Socket Layer SSL Security TechnologyThe purpose of this slide is to explain the role of HTTPS and the secure sockets layer SSL protocol for secure connections. This slide also discusses the incorporation of symmetric and asymmetric encryption during the SSL handshake process. Present the topic in a bit more detail with this Encryption Implementation Strategies Secure Socket Layer SSL Security Technology. Use it as a tool for discussion and navigation on Secure Socket Layer, Security Technology, Symmetric And Asymmetric Encryption, Protocol For Secure Connections. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Secure Socket Shell Encryption Protocol
Encryption Implementation Strategies Secure Socket Shell Encryption ProtocolThis slide represents the working process of SSH Secure Socket Shell protocol to secure data sharing between unsecured networks. This slide also illustrates the before and after scenario of using SSH protocol for data encryption. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Secure Socket Shell Encryption Protocol. Dispense information and present a thorough explanation of Secure Socket Shell, Encryption Protocol, Unsecured Networks, Protocol For Data Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Security Protocols Required According To Type Of Network
Encryption Implementation Strategies Security Protocols Required According To Type Of NetworkThe purpose of this slide is to outline different security protocols used in various types of networks, and their specific applications. These network types are wired, wireless networks, Local Area Networks LANs, Wide Area Networks WANs, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Security Protocols Required According To Type Of Network. Use it as a tool for discussion and navigation on Local Area Networks, Wide Area Networks, Wired Networks, Wireless Networks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Steps Followed By Internet Protocol Security Connections
Encryption Implementation Strategies Steps Followed By Internet Protocol Security ConnectionsThe purpose of this slide is to outline the working steps of internet protocol security connections. These are key exchange, packet headers and trailers, packet authentication, encryption, data transmission and decryption of data packets. Present the topic in a bit more detail with this Encryption Implementation Strategies Steps Followed By Internet Protocol Security Connections. Use it as a tool for discussion and navigation on Protocol Security Connections, Packet Authentication, Encryption, Data Transmission, Decryption Of Data Packets. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Transport Layer Security Implementation Using Handshake
Encryption Implementation Strategies Transport Layer Security Implementation Using HandshakeThis slide discusses a cryptographic system known as transport layer security TLS. The purpose of this slide is to explain how TLS enables safe communication over computer networks using handshake protocol and record protocol. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Transport Layer Security Implementation Using Handshake. This template helps you present information on two stages. You can also present information on Transport Layer Security Implementation, Handshake And Record Protocol, Computer Networks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies
Encryption Technologies To Secure Data In Transit Encryption Implementation StrategiesThis slide compares different data in transit protection methods, including their working and associated cost. These methods are email encryption, Managed File Transfer MFT, Data Leak Prevention DLP, Cloud Access Security Brokers CASB, etc. Deliver an outstanding presentation on the topic using this Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Managed File Transfer, Cloud Access Security Brokers, Email Encryption, Encryption Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies
Overview Of Encryption For Securing Data At Rest Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data at rest. The storage methods include file servers, network shares, document management systems, external storage, databases, endpoint devices, mobile devices, cloud storage, etc. Present the topic in a bit more detail with this Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies. Use it as a tool for discussion and navigation on Database Encryption, Information Rights Management, Data Leak Prevention, Mobile Device Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies
Overview Of Encryption For Securing Data In Transit Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data in transit. The methods include email encryption, MFT Managed File Transfer, IRM Information Rights Management, CASB Cloud Access Security Brokers, and DLP Data Leak Prevention. Deliver an outstanding presentation on the topic using this Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Issues Internet Things Encryption In Powerpoint And Google Slides Cpb
Security Issues Internet Things Encryption In Powerpoint And Google Slides CpbPresenting Security Issues Internet Things Encryption In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Issues Internet Things Encryption. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS V
Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Present the topic in a bit more detail with this Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS V Use it as a tool for discussion and navigation on Employee Headcount, Average Employee Age, Gender Diversity Ratio This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Encryption Secure Computer Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Encryption Secure Computer Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is a visual representation of secure computer. It is a modern, vibrant and eye catching icon that will help to create an impactful presentation. It is a great way to emphasize the importance of data security and safety.
-
 Data Encryption Secure Computer Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Encryption Secure Computer Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for presentations on secure computer systems. It features a black and white design depicting a computer with a padlock, symbolizing the safety of your data. Use this icon to emphasize the importance of secure computing.
-
 Cloud Access Security Broker And Encryption Next Generation CASB
Cloud Access Security Broker And Encryption Next Generation CASBThis slide describes the improved encryption with CASB version 2.0. The purpose of this slide is to showcase the various encryption features of cloud access security broker version 2.0, including security that follows the data, content access that can be revoked at any time, and multi-platform compatibility. Present the topic in a bit more detail with this Cloud Access Security Broker And Encryption Next Generation CASB Use it as a tool for discussion and navigation on Security That Tracks Data, Terminated Moment, Content Access This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Encryption Algorithms Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Security Encryption Algorithms Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is a great visual aid for representing folder password protection. It is a modern and vibrant design that will add a professional touch to any presentation. The icon is easy to use and can be used to quickly and effectively communicate the importance of password security.
-
 Cyber Security Encryption Algorithms Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Security Encryption Algorithms Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Folder Password is a simple yet effective way to protect your confidential data. It is easy to use and provides a secure encryption for your files. It is an ideal solution for those who want to keep their documents safe and secure.
-
 About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It
About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the role and functionality of IPsec Internet Protocol Security in securing connections between devices. This slide also outlines the uses of IPsec such as protecting data during transmission over open networks, use in building VPNs, etc. Deliver an outstanding presentation on the topic using this About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Overview, Protocol Security, Destination using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of utilizing Hypertext Transfer Protocol Secure HTTPS for website encryption. The advantages discussed in this slide are secure interaction, data integrity, privacy and security, better performance, user experience, etc. Introducing Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Interaction, Data Integrity, Better Performance, using this template. Grab it now to reap its full benefits.
-
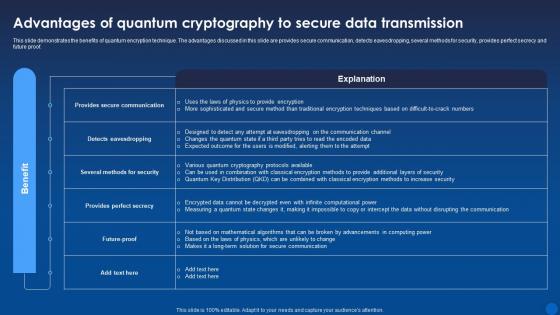 Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It
Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age ItThis slide demonstrates the benefits of quantum encryption technique. The advantages discussed in this slide are provides secure communication, detects eavesdropping, several methods for security, provides perfect secrecy and future proof. Present the topic in a bit more detail with this Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Quantum, Cryptography, Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Applications Secure Email Content Encryption For Data Privacy In Digital Age It
Applications Secure Email Content Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss the importance of email encryption in protecting the privacy and security of email communications. The key components of secure email transfer are public key, private key, encryption, decryption, etc. Present the topic in a bit more detail with this Applications Secure Email Content Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Applications, Encryption, Decryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages and disadvantages of Internet protocol Security IPsec technology. The various benefits explained in this slide are strong security, broad compatibility, flexibility, scalability and efficient network performance. Deliver an outstanding presentation on the topic using this Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Key Management, Performance Impact, Compatibility Issues using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It
Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various features of Internet Protocol Security IPsec mechanism. The properties of IPsec include authentication, privacy, integrity, key management, tunnelling, flexibility and interoperability. Introducing Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Key Management, Interoperability, using this template. Grab it now to reap its full benefits.
-
 Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age It
Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age ItThis slide describes the cloud cryptography trends. The purpose of this slide is to highlight the emerging trends in the field of cloud encryption. These include homomorphic encryption, quantum-safe cryptography, secure multi-party computation, etc. Introducing Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Homomorphic Encryption, Quantum Safe Cryptography, Secure Multi Party Computation, using this template. Grab it now to reap its full benefits.
-
 Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age It
Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age ItThis slide discusses about the increasing adoption of encryption to solve current cyber security issues. The key points discussed are more use of cloud encryption in banking sector, introduction of homomorphic encryption, increase in BYOE adoption, etc. Increase audience engagement and knowledge by dispensing information using Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age It. This template helps you present information on five stages. You can also present information on Homomorphic, Encryption, Introduction using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 End To End Encryption To Secure Digital Ecosystems Encryption For Data Privacy In Digital Age It
End To End Encryption To Secure Digital Ecosystems Encryption For Data Privacy In Digital Age ItThis slide discusses about the end to end encryption methodology. It secures the communication between sender and receiver. The purpose of this slide is to show the data flow between two users using end to end encryption technique. Present the topic in a bit more detail with this End To End Encryption To Secure Digital Ecosystems Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Digital Ecosystems, Communication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age It
Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the various misconceptions and mistakes of organization while integrating cryptographic solutions into cloud. These include dependence on low-level encryption, reliance on cloud service providers for data protection, poor key management, etc. Introducing Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Data Protection, Poor Key Management, Software Engineers, using this template. Grab it now to reap its full benefits.
-
 Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age It
Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age ItThis slide demonstrates the working of Internet Protocol Security. The main components of IPsec architecture are ESP protocol, AH protocol, encryption algorithm, authentication algorithm, key management, etc. Present the topic in a bit more detail with this Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Protocol Security, Architecture, Encryption Algorithm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide talks about the Hypertext Transfer Protocol Secure HTTPS, which is an advance version of HTTP. The purpose of this slide is to discuss the importance of using HTTPS to encrypt communication between browser and server. Present the topic in a bit more detail with this Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Introduction, Overview, Protocol Secure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss the main components of Internet Protocol Security IPsec architecture. These three components are Encapsulating Security Payload ESP, Authentication Header AH, and Internet Key Exchange IKE. Deliver an outstanding presentation on the topic using this Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Authentication Header, Internet Key Exchange, Encapsulating Security Payload using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age It
Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age ItThis slide talks about the challenges of Hypertext Transfer Protocol Secure HTTPS and their possible solutions. These challenges are lack of end-to-end encryption, certificate authority vulnerabilities, difficulty in detecting malicious content, and complexity and cost of certificate management. Present the topic in a bit more detail with this Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Limitations, Solutions, Description. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age It
Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to highlight the benefits and capabilities of Hardware Security Modules HSMs. The key components included are cloud server, private key, encrypted request, encrypted data, HSM isolated environment, etc. Deliver an outstanding presentation on the topic using this Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Relationship, Hardware, Cryptographic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.




