Powerpoint Templates and Google slides for Deployment And Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Data security it prepare and deploy strong it policies ppt slides deck
Data security it prepare and deploy strong it policies ppt slides deckThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Present the topic in a bit more detail with this Data Security IT Prepare And Deploy Strong IT Policies Ppt Slides Deck. Use it as a tool for discussion and navigation on Build Strong, IT Policies, Required Security Software, Content Sharing, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
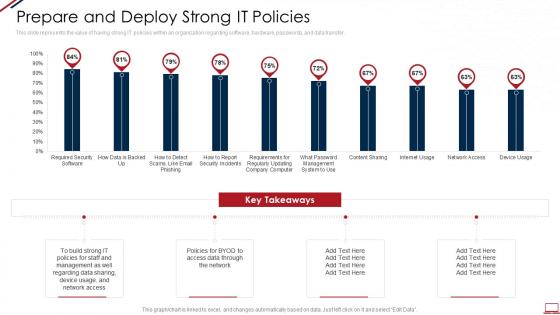 Computer system security prepare and deploy strong it policies
Computer system security prepare and deploy strong it policiesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Present the topic in a bit more detail with this Computer System Security Prepare And Deploy Strong It Policies. Use it as a tool for discussion and navigation on Prepare And Deploy Strong IT Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Firewall Network Security Global Firewall Market Segmentation By Deployment And Solution
Firewall Network Security Global Firewall Market Segmentation By Deployment And SolutionThis slide provides an overview of global firewall market categorization based on deployment and solution type. The purpose of this slide is to showcase the firewall market share based on deployment types and solution type, such as software and hardware services. Deliver an outstanding presentation on the topic using this Firewall Network Security Global Firewall Market Segmentation By Deployment And Solution Dispense information and present a thorough explanation of Oragnisation Size Segment Overview, Regional Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Risk Assessment And Technology Deployment Plan To Improve Organizations
Cyber Security Risk Assessment And Technology Deployment Plan To Improve OrganizationsThis slide represents the assessment of vulnerability and consequences of the cyber security incidents on the operations of the company. It includes details related to threat, vulnerability, consequences, risk and solution Deliver an outstanding presentation on the topic using this Cyber Security Risk Assessment And Technology Deployment Plan To Improve Organizations. Dispense information and present a thorough explanation of Consequences, Vulnerability, Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And Working
Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And WorkingThis slide describes the overview of the forward proxy deployment mode of the CASB model, including its working. The purpose of this slide is to showcase the working of proxy-based CASB deployment and the main components include user or clients, forward proxy, internet and origin server. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And Working. Use it as a tool for discussion and navigation on Deployment Overview And Working, Web Servers They Visit, Forward Proxy Method Is A Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SS
Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SSThis slide exhibits key activities and tools for monitoring and diagnostics of IoT device security. It includes activities such as continuous monitoring, anomaly detection, vulnerability scanning, auditing and reporting, etc. Present the topic in a bit more detail with this Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Vulnerability Scanning, Auditing Reporting, Anomaly Detection . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Advantages And Disadvantages Of Proxy Based Deployment CASB Cloud Security
Advantages And Disadvantages Of Proxy Based Deployment CASB Cloud SecurityThis slide represents the benefits and drawbacks of proxy-based CASB deployment. The purpose of this slide is to showcase the various pros and cons of proxy-based cloud access security brokers and the advantages cover flexibility, secure SaaS applications, and so on. Increase audience engagement and knowledge by dispensing information using Advantages And Disadvantages Of Proxy Based Deployment CASB Cloud Security. This template helps you present information on two stages. You can also present information on Proxy Based Cloud Access Security, Advantages Cover Flexibility, Proxy Based Deployment, Encrypted Connections Or Networks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Forward Proxy Deployment Overview And Working CASB Cloud Security
Forward Proxy Deployment Overview And Working CASB Cloud SecurityThis slide describes the overview of the forward proxy deployment mode of the CASB model, including its working. The purpose of this slide is to showcase the working of proxy-based CASB deployment and the main components include user or clients, forward proxy, internet and origin server. Increase audience engagement and knowledge by dispensing information using Forward Proxy Deployment Overview And Working CASB Cloud Security. This template helps you present information on eight stages. You can also present information on Forward Proxy Deployment, Internet And Origin Server, According To The Internet Server using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Pros And Cons Of Api Scanning CASB Deployment CASB Cloud Security
Pros And Cons Of Api Scanning CASB Deployment CASB Cloud SecurityThis slide outlines the advantages and disadvantages of the API scanning cloud access security broker deployment model. This slide aims to highlight the pros and cons of the API scanning deployment model and the benefits include no impact on user experience, taking only a few hours to configure, etc. Introducing Pros And Cons Of Api Scanning CASB Deployment CASB Cloud Security to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Scanning Cloud Access Security, Broker Deployment Model, Scanning Deployment Model, using this template. Grab it now to reap its full benefits.
-
 Concerns And Solution For Application Security Deployment
Concerns And Solution For Application Security DeploymentThis slide outlines the problems and relevant solutions of application security deployment to ensure smooth functioning. Present the topic in a bit more detail with this Concerns And Solution For Application Security Deployment. Use it as a tool for discussion and navigation on Implement Strict Input Validation, Employ Bot Detection Mechanisms, Application Security Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Create Continuous Update And Deployment Mechanisms Internet Of Things IoT Security Cybersecurity SS
Create Continuous Update And Deployment Mechanisms Internet Of Things IoT Security Cybersecurity SSThis slide showcases comparative analysis for internet of things IoT security tools. It provides details about secure cryptographic key provisioning, identity, access and relationship management, IoT device provisioning, etc. Introducing Create Continuous Update And Deployment Mechanisms Internet Of Things IoT Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Secure Deployment, Cryptographic Protocols, Automated Security Update Deployment, Monitoring And Response Mechanisms, using this template. Grab it now to reap its full benefits.
-
 Deploy Security Auditing And Monitoring Mechanisms Internet Of Things IoT Security Cybersecurity SS
Deploy Security Auditing And Monitoring Mechanisms Internet Of Things IoT Security Cybersecurity SSThis slide showcases application of auditing and monitoring for internet of things IoT devices, referable for businesses in developing mitigation process. It provides details about response plan, etc. Increase audience engagement and knowledge by dispensing information using Deploy Security Auditing And Monitoring Mechanisms Internet Of Things IoT Security Cybersecurity SS. This template helps you present information on three stages. You can also present information on Auditing And Reporting, Incident Response Planning, Record Of Security Actions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Security Prepare And Deploy Strong It Policies
Information Security Prepare And Deploy Strong It PoliciesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Present the topic in a bit more detail with this Information Security Prepare And Deploy Strong It Policies. Use it as a tool for discussion and navigation on Prepare And Deploy Strong IT Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Network Security Prepare And Deploy Strong It Policies
Network Security Prepare And Deploy Strong It PoliciesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Deliver an outstanding presentation on the topic using this Network Security Prepare And Deploy Strong It Policies. Dispense information and present a thorough explanation of Prepare And Deploy Strong It Policies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Technology Security Prepare And Deploy Strong It Policies
Information Technology Security Prepare And Deploy Strong It PoliciesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Deliver an outstanding presentation on the topic using this Information Technology Security Prepare And Deploy Strong It Policies. Dispense information and present a thorough explanation of Prepare And Deploy Strong IT Policies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ensuring Checklist For Mobile Security Deployment Management And Monitoring
Ensuring Checklist For Mobile Security Deployment Management And MonitoringThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Introducing Ensuring Checklist For Mobile Security Deployment Management And Monitoring to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Ensuring Checklist, Mobile Security Deployment, using this template. Grab it now to reap its full benefits.
-
 Kpi for security risks total revenue policy deployment and adoption ppt slide
Kpi for security risks total revenue policy deployment and adoption ppt slidePresenting kpi for security risks total revenue policy deployment and adoption ppt slide. This presentation slide shows three Key Performance Indicators or KPIs in a Dashboard style design. The first KPI that can be shown is Number of Information Security Related Risks. The second KPI is Information Security Costs as a Proportion of Total Revenue or it Budget and the third is Information Security Policy Deployment and Adoption. These KPI Powerpoint graphics are all data driven,and the shape automatically adjusts according to your data. Just right click on the KPI graphic,enter the right value and the shape will adjust automatically. Make a visual impact with our KPI slides.
-
 Security information and event management traditional siem deployment
Security information and event management traditional siem deploymentThis slide covers the traditional in house SIEM model wherein the client take care of all the security incident and event management process on its own. Present the topic in a bit more detail with this Security Information And Event Management Traditional SIEM Deployment. Use it as a tool for discussion and navigation on Visualization, Collection, Aggregation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementation Add Roles And Enable Security Customer Relationship Management Deployment Strategy
Implementation Add Roles And Enable Security Customer Relationship Management Deployment StrategyThis slide highlights the setting roles of new users and assigning roles, also highlights the enable security with field level and integration of lead generation with emails for contact management.Deliver an outstanding presentation on the topic using this Implementation Add Roles And Enable Security Customer Relationship Management Deployment Strategy Dispense information and present a thorough explanation of Restrictions Enabling, Double Authentication, Prevent Unauthorized using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Importance Of Secure Ecommerce Payment Systems Analysis And Deployment Of Efficient Ecommerce
Importance Of Secure Ecommerce Payment Systems Analysis And Deployment Of Efficient EcommerceThis slide represents the importance of payment gateways in facilitating systemized payment methods and providing consumers with fast and flexible way for making payments. It includes benefits of ecommerce payment systems such as meets digital needs, customer retention, security etc. Increase audience engagement and knowledge by dispensing information using Importance Of Secure Ecommerce Payment Systems Analysis And Deployment Of Efficient Ecommerce. This template helps you present information on one stages. You can also present information on Meets Digital Needs, Customer Retention, Multiple Payment Modes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB Advantages And Disadvantages Proxy Based Deployment
Cloud Access Security Broker CASB Advantages And Disadvantages Proxy Based DeploymentThis slide represents the benefits and drawbacks of proxy based CASB deployment. The purpose of this slide is to showcase the various pros and cons of proxy based cloud access security brokers and the advantages cover flexibility, secure SaaS applications, and so on. Introducing Cloud Access Security Broker CASB Advantages And Disadvantages Proxy Based Deployment. to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Advantages, Disadvantages, Based Deployment, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB Forward Proxy Deployment Overview And Working
Cloud Access Security Broker CASB Forward Proxy Deployment Overview And WorkingThis slide describes the overview of the forward proxy deployment mode of the CASB model, including its working. The purpose of this slide is to showcase the working of proxy based CASB deployment and the main components include user or clients, forward proxy, internet and origin server. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB Forward Proxy Deployment Overview And Working. Dispense information and present a thorough explanation of Overview, Forward Proxy, Internet using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Micro services defining scheduling deployment and service security
Micro services defining scheduling deployment and service securityPresenting this set of slides with name - Micro Services Defining Scheduling Deployment And Service Security. This is a five stage process. The stages in this process are Micro Services, Software Development, Service Oriented Architecture.
-
 Technology platform showing deployment and security model
Technology platform showing deployment and security modelPresenting technology platform showing deployment and security model. This is a technology platform showing deployment and security model. This is a nine stage process. The stages in this process are technology platform, software development, software architecture.
-
 Steps to design and deploy security feature in website
Steps to design and deploy security feature in websitePresenting this set of slides with name Steps To Design And Deploy Security Feature In Website. This is a six stage process. The stages in this process are Development, Real World, Deployment, Design, Requirements. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cyber security it prepare and deploy strong it policies ppt powerpoint show topics
Cyber security it prepare and deploy strong it policies ppt powerpoint show topicsThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Deliver an outstanding presentation on the topic using this Cyber Security IT Prepare And Deploy Strong IT Policies Ppt Powerpoint Show Topics. Dispense information and present a thorough explanation of It Policies, Management, Access, Policies, Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Firewall Implementation For Cyber Security Global Firewall Market Segmentation By Deployment And Solution
Firewall Implementation For Cyber Security Global Firewall Market Segmentation By Deployment And SolutionThis slide provides an overview of global firewall market categorization based on deployment and solution type. The purpose of this slide is to showcase the firewall market share based on deployment types and solution type, such as software and hardware services. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Global Firewall Market Segmentation By Deployment And Solution. Use it as a tool for discussion and navigation on Global Firewall Market, Software And Hardware Services, Market Segmentation. This template is free to edit as deemed fit for your organization. Therefore download it now.



